Understanding the Impact of Cybersecurity Breaches on Gaming Industry: A Deep Dive [2025]
Last week, Rockstar Games made headlines when it announced that a recent cybersecurity breach would have 'no impact' on its operations. While this may sound reassuring, the incident raises significant questions about the security measures within the gaming industry and the potential implications of such breaches.
TL; DR
- Cybersecurity breaches in the gaming industry can lead to data leaks, financial loss, and brand damage. According to emerging cybersecurity threats, these incidents are becoming more sophisticated and costly.
- Rockstar Games claims their recent breach will have 'no impact', highlighting the importance of strong security protocols. As reported by Kotaku, the company's swift response and robust infrastructure played a key role in mitigating potential damage.
- Developers must implement end-to-end encryption and regular audits to mitigate risks, as emphasized in recent studies on cybersecurity.
- Users should practice safe gaming habits to protect personal data, as suggested by the Delaware Gazette.
- The future of gaming security will rely heavily on AI and machine learning to predict and prevent attacks, a trend highlighted by the Atlantic Council.

Investing in cybersecurity and leveraging AI are rated highest in impact for gaming companies' security. (Estimated data)
Introduction
The gaming industry, a multi-billion dollar market, is increasingly becoming a target for cybercriminals. With massive user bases and valuable intellectual property, gaming companies are prime targets for hackers. The recent breach at Rockstar Games is a stark reminder of the vulnerabilities that exist within this digital landscape, as discussed in Industrial Cyber.

The Anatomy of a Cybersecurity Breach
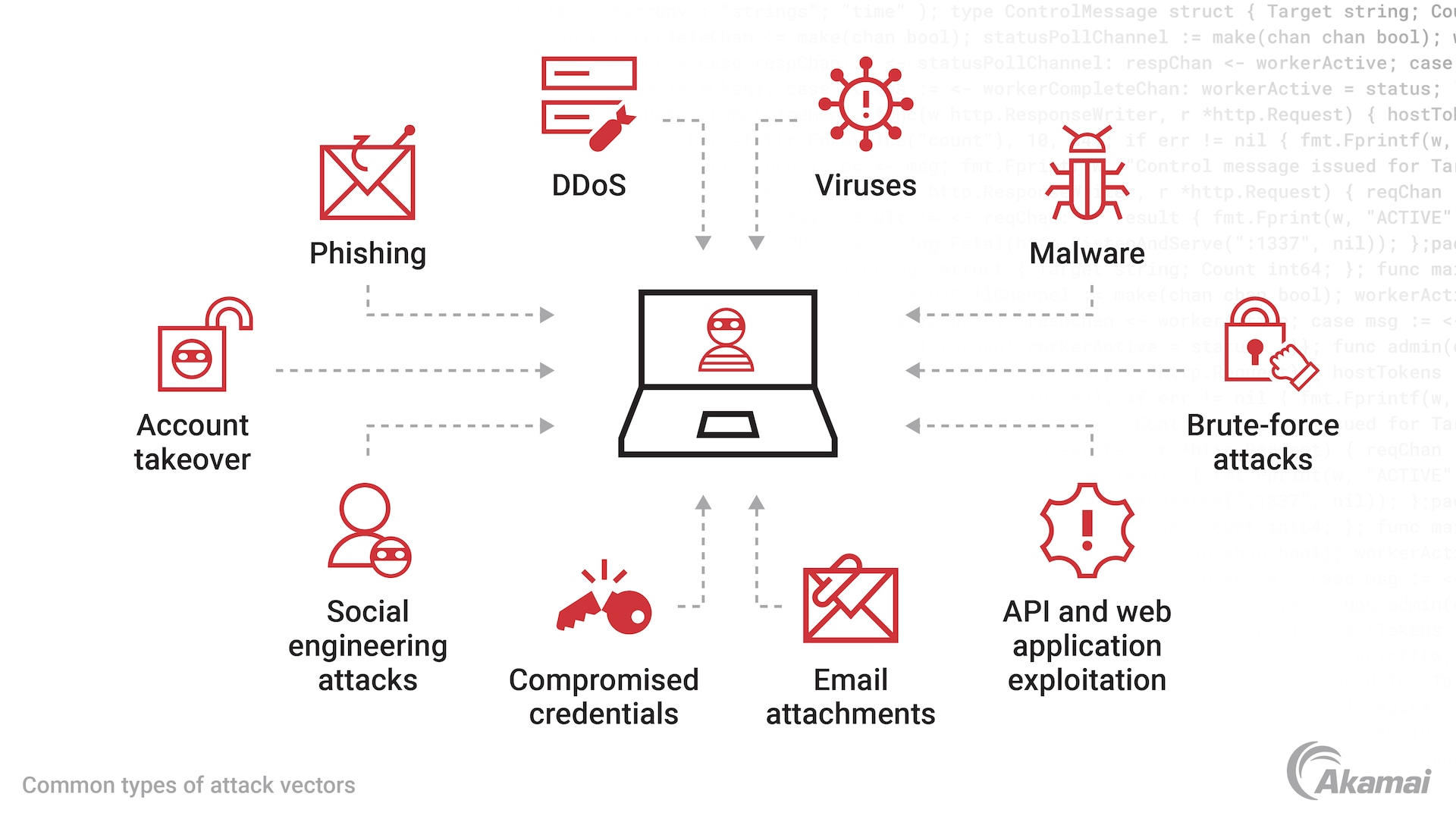
Understanding how cybersecurity breaches occur is crucial for both prevention and recovery. Typically, breaches involve unauthorized access to a company's systems, where hackers can steal data, disrupt services, or cause reputational damage, as outlined by the New York Times.
Common Attack Vectors
- Phishing Attacks: Deceptive emails or messages trick users into revealing sensitive information.
- Malware: Malicious software designed to damage or gain unauthorized access to systems.
- Distributed Denial of Service (DDoS): Overwhelms a network with traffic, causing service disruptions.
- Exploiting Vulnerabilities: Taking advantage of weaknesses in software or hardware.

Financial loss is often the most severe consequence of a cybersecurity breach, followed closely by data leaks. (Estimated data)
The Impact on Gaming Companies
Cybersecurity breaches can have a devastating impact on gaming companies. Beyond the immediate financial loss, there are several other consequences to consider:
- Data Leaks: Compromised personal and financial information can lead to identity theft and fraud, as noted by White & Case.
- Reputation Damage: Loss of consumer trust can result in decreased sales and long-term brand damage.
- Legal Consequences: Failure to protect user data can lead to lawsuits and regulatory fines.

Rockstar Games: A Case Study
Rockstar Games' recent breach is a notable example of a company facing a cybersecurity threat. However, their ability to claim 'no impact' suggests they have robust security measures in place, as reported by Yahoo Sports.
What They Did Right
- Rapid Response: Quick identification and containment of the breach minimized damage.
- Transparency: Communicating with stakeholders about the breach built trust.
- Robust Security Infrastructure: Implementation of advanced cybersecurity technologies likely mitigated the impact.
Best Practices for Developers
Developers play a critical role in preventing cybersecurity breaches. Here are some best practices they should follow:
- Implement Encryption: Use end-to-end encryption to protect data in transit and at rest.
- Regular Security Audits: Conduct frequent audits to identify and fix vulnerabilities.
- User Authentication: Employ multi-factor authentication to add an extra layer of security.
- Secure Coding Practices: Write code that is resilient against common vulnerabilities.

Cybersecurity breaches impact gaming companies through financial loss (30%), reputation damage (25%), legal consequences (20%), and data leaks (25%). Estimated data.
Practical Implementation Guides
For developers looking to bolster their security measures, here are some practical steps:
- Set Up a Firewall: Protect networks from unauthorized access by configuring firewalls properly.
- Update Software Regularly: Implement automatic updates to patch known vulnerabilities.
- Conduct Penetration Testing: Simulate attacks to test the effectiveness of security measures.
- Train Employees: Regular training sessions can help employees recognize and avoid phishing attacks.

Common Pitfalls and Solutions
Even with the best intentions, mistakes can happen. Here are some common pitfalls and how to avoid them:
- Ignoring Security Alerts: Pay attention to alerts and investigate them promptly.
- Inadequate Backup: Regularly back up data to secure locations to prevent data loss.
- Poor Incident Response Plan: Develop a comprehensive incident response plan and update it regularly.
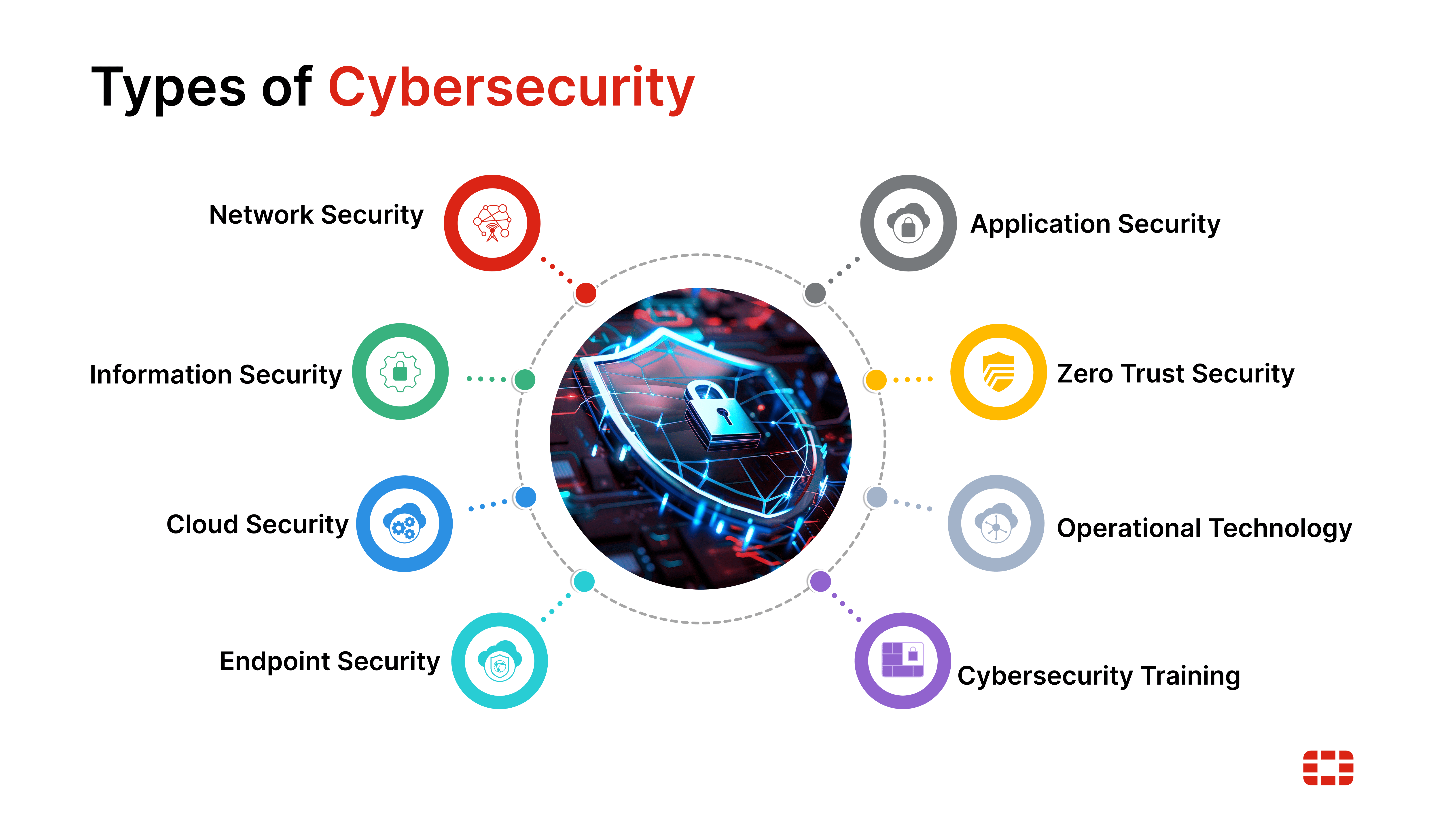
Future Trends in Gaming Security
The evolution of technology brings both new opportunities and challenges for cybersecurity in the gaming industry. Here are some trends to watch:
- AI and Machine Learning: These technologies will play a significant role in detecting and preventing cyber threats, as explored by the Atlantic Council.
- Cloud Gaming: As cloud gaming grows, so too will the need for securing cloud-based infrastructure.
- Blockchain: This technology offers secure and transparent transactions, potentially reducing fraud.
Recommendations
To stay ahead of cyber threats, gaming companies should:
- Invest in Cybersecurity: Allocate resources to build and maintain robust security infrastructures.
- Collaborate with Experts: Partner with cybersecurity firms to stay updated on the latest threats and solutions.
- Engage the Community: Encourage responsible disclosure of vulnerabilities by working with the gaming community.

Conclusion
Cybersecurity breaches are an ever-present threat to the gaming industry. By understanding the risks and implementing best practices, both developers and users can protect themselves and ensure the continued growth and success of the gaming sector.
FAQ
What is a cybersecurity breach?
A cybersecurity breach is an incident where unauthorized individuals gain access to systems or data, often resulting in data theft, service disruption, or financial loss.
How can developers prevent breaches?
Developers can prevent breaches by implementing encryption, conducting regular security audits, employing multi-factor authentication, and following secure coding practices.
What are the consequences of a breach?
Breaches can lead to data leaks, reputation damage, financial loss, and legal consequences for companies.
How does AI help in cybersecurity?
AI and machine learning can analyze patterns and detect anomalies, helping to predict and prevent potential cyber threats.
What role does the gaming community play in security?
The gaming community can contribute by reporting vulnerabilities, participating in bug bounty programs, and promoting safe gaming practices.
How can users protect themselves?
Users should practice safe gaming habits, such as using strong passwords, enabling two-factor authentication, and staying informed about potential threats.
Key Takeaways
- Cybersecurity breaches can have severe consequences, including data leaks and reputation damage.
- Rockstar Games claims their breach will have 'no impact', highlighting effective security measures.
- Developers should adopt best practices such as encryption and regular audits.
- AI and machine learning are critical for future cybersecurity strategies.
- Users must remain vigilant and practice safe gaming habits.
- Collaboration with experts can enhance a company's security posture.
- Investing in cybersecurity is essential for the growth and success of gaming companies.
Related Articles
- Rockstar Games and the Third-Party Data Breach: Understanding the Fallout [2025]
- Marauding Minotaurs, More CloverPit, and Indie Game Gems to Explore [2025]
- No, Elon Musk Doesn't Want to Give You a $5,000 Tax Refund — It's a Scam [2025]
- Reimagining FISA Section 702: Closing Surveillance Loopholes [2025]
- Unlock the Future of Tech: Last Chance to Save $500 on Your Disrupt 2026 Pass [2025]
- Understanding AI: A Simple Guide to Common Terms and Concepts [2025]
![Understanding the Impact of Cybersecurity Breaches on Gaming Industry: A Deep Dive [2025]](https://tryrunable.com/blog/understanding-the-impact-of-cybersecurity-breaches-on-gaming/image-1-1776015229601.jpg)



