Why Passkeys Are the Future of Authentication [2025]
In a groundbreaking move, the UK's National Cyber Security Centre has officially declared passkeys superior to traditional passwords, recommending them as the first choice for authentication. This declaration marks a pivotal shift in cybersecurity practices, emphasizing the need for more secure and user-friendly authentication methods. In this comprehensive guide, we'll explore why passkeys are becoming the go-to solution for secure authentication, how they work, and what the future holds for this technology.
TL; DR
- Passkeys offer superior security by eliminating common vulnerabilities associated with traditional passwords.
- Ease of use: Passkeys streamline the login process, reducing the need for users to remember complex passwords.
- Enhanced user experience: Passkeys integrate seamlessly with devices, providing a frictionless authentication experience.
- Future-proofing your security: As technology evolves, passkeys are poised to become the standard for authentication.
- Bottom Line: For enhanced security and convenience, adopt passkeys as your primary authentication method.
Passkey authentication involves equal roles of public and private keys, biometric authentication, and server challenges. (Estimated data)
The Evolution of Authentication
Authentication has long been a cornerstone of cybersecurity, with passwords being the traditional method of choice. However, as cyber threats have evolved, the limitations of passwords have become increasingly apparent. Weak passwords, password reuse, and phishing attacks are just a few of the challenges that have plagued the security landscape.
The Rise of Passkeys
Passkeys, also known as passwordless authentication, offer a compelling alternative. They leverage cryptographic keys stored on a user's device, providing a secure and convenient way to authenticate. This approach eliminates many of the vulnerabilities associated with passwords, making it an attractive option for both individuals and organizations. According to a recent report, 87% of companies are deploying passkeys as passwords near their end of life.
Choosing the right passkey solution is crucial, rated highest in importance. Educating the team, while important, is slightly less critical compared to other technical steps. (Estimated data)
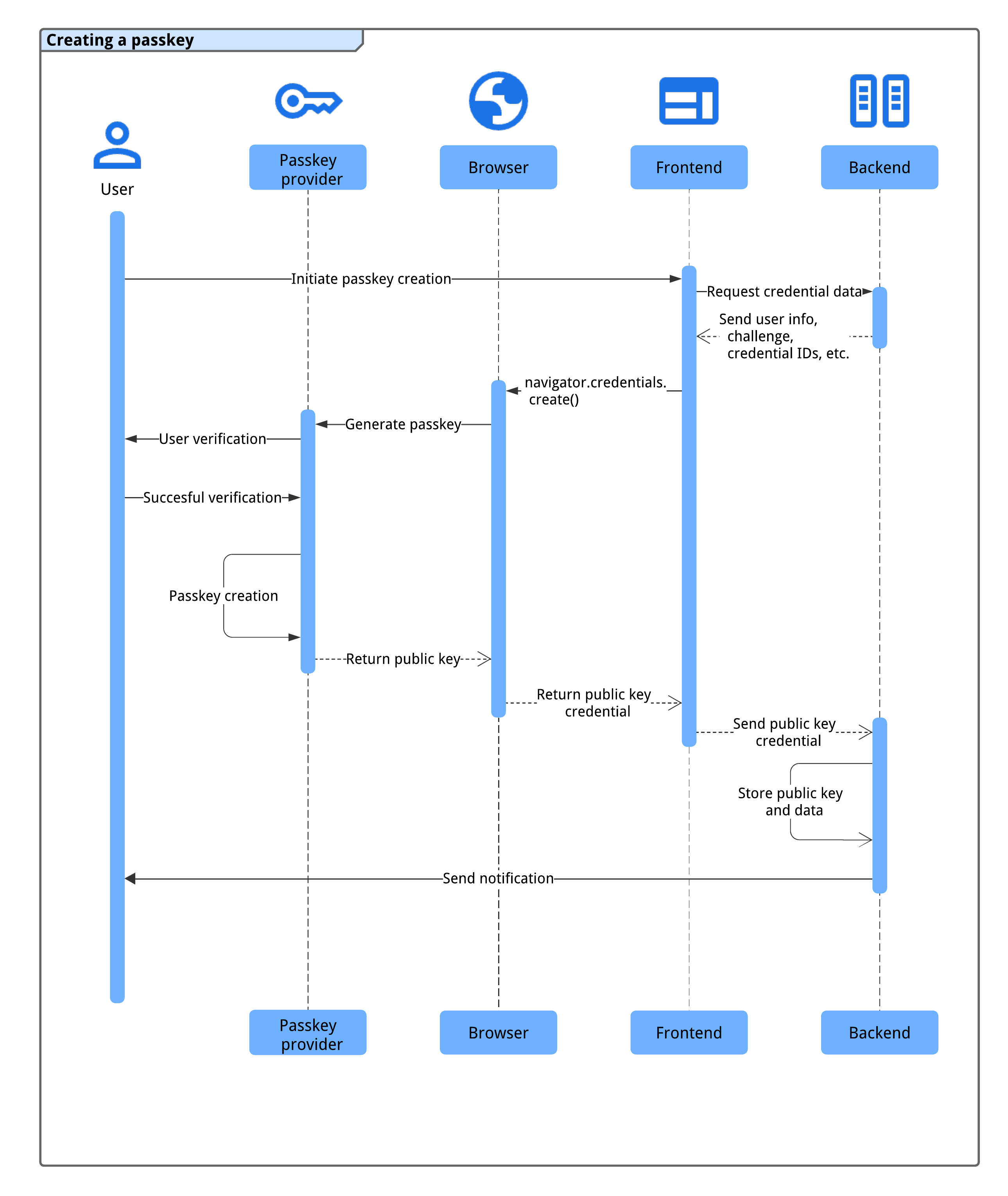
How Passkeys Work
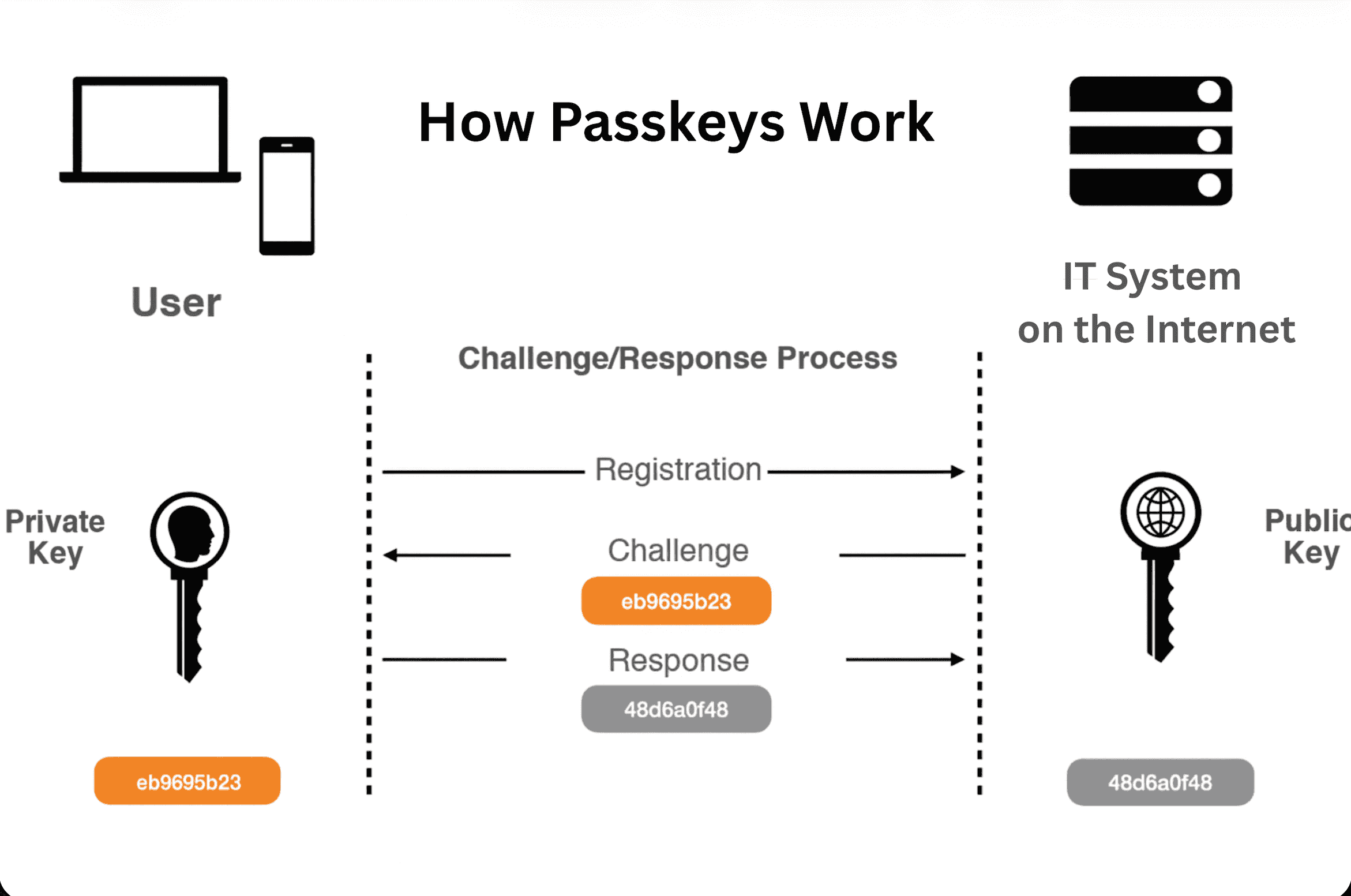
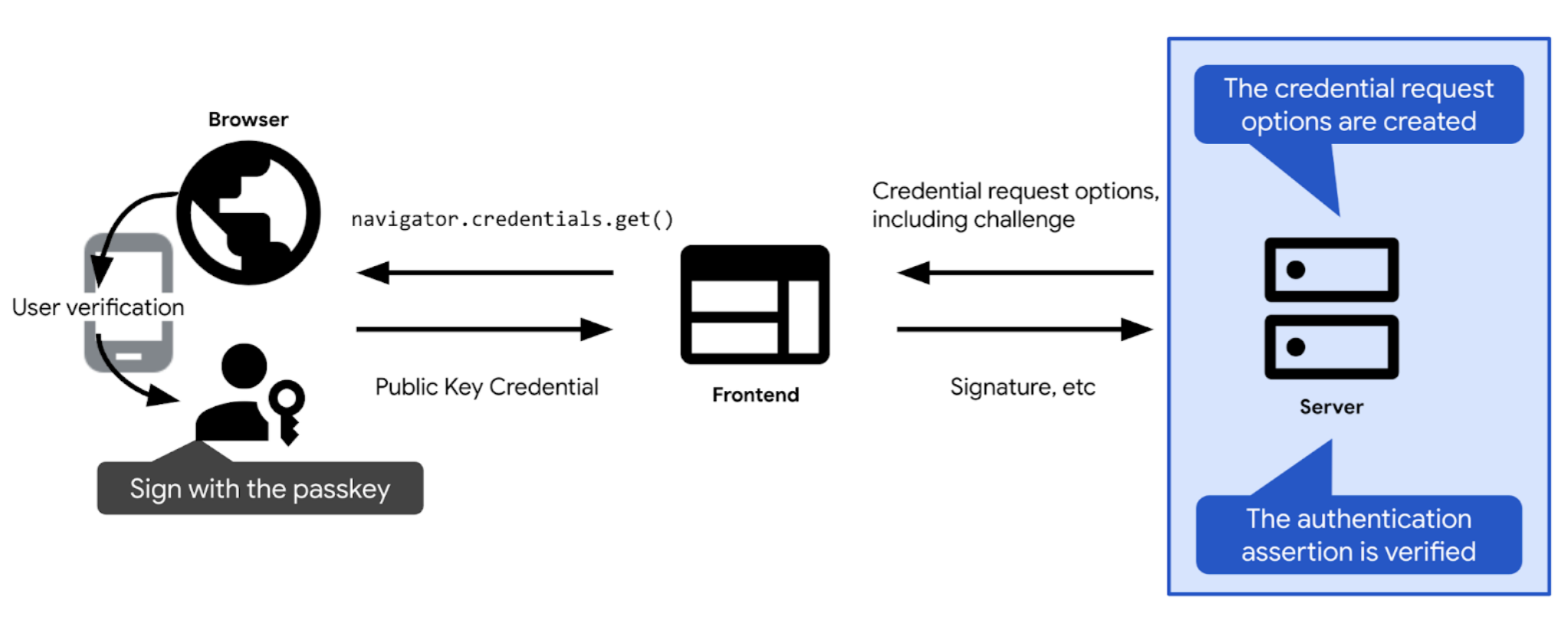
Passkeys operate by using a pair of cryptographic keys: a public key and a private key. The public key is stored on the server, while the private key remains on the user's device. When a user attempts to log in, the server sends a challenge to the device, which is signed using the private key. The server then verifies the signature using the public key, granting access if the signature is valid. This method is detailed in enterprise passkey deployment guides.
Example Use Case
Consider a scenario where a user wants to access their online banking account. Instead of entering a password, the user simply authenticates using their device's biometric features, such as fingerprint or facial recognition. The device then uses the private key to sign the authentication challenge, allowing the user to access their account securely.
Benefits of Passkeys
The advantages of passkeys over traditional passwords are numerous:
- Enhanced Security: Passkeys are immune to phishing attacks and password breaches, as highlighted by IBM's multi-factor authentication insights.
- User Convenience: No need to remember complex passwords or change them regularly.
- Faster Authentication: Reduced login times with seamless integration of biometric authentication.
- Compatibility: Works across multiple devices and platforms, enabling a consistent user experience.

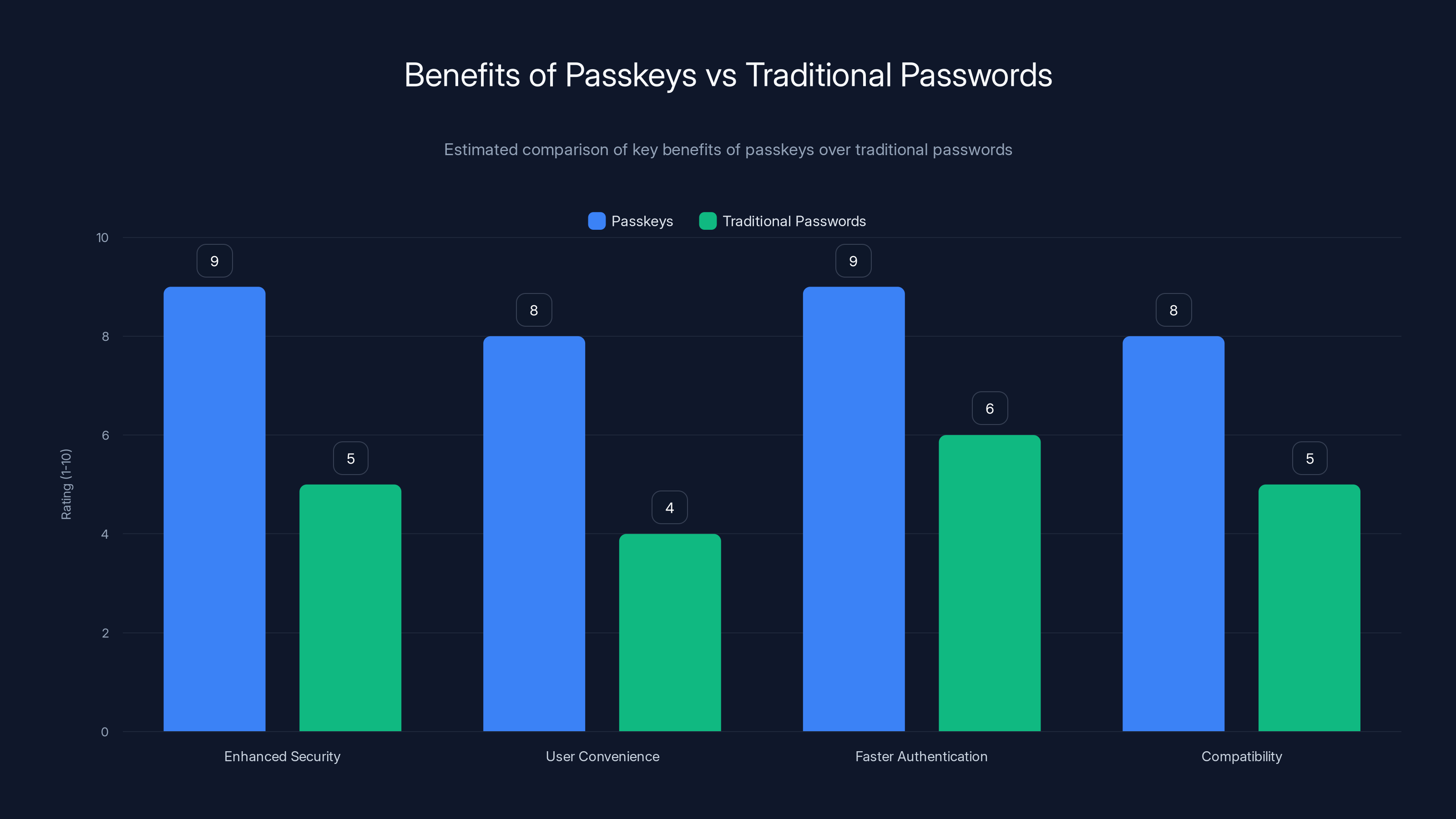
Passkeys significantly outperform traditional passwords in terms of security, user convenience, authentication speed, and compatibility. Estimated data.
Implementing Passkeys in Your Organization
Transitioning to passkeys requires careful planning and execution. Here are the key steps to consider:
- Evaluate Your Current Infrastructure: Assess your existing authentication systems and identify areas for improvement.
- Choose the Right Passkey Solution: Select a solution that aligns with your organization's needs and supports the devices and platforms used by your employees. Resources like MSSP Alert provide insights on choosing the right security solutions.
- Educate Your Team: Provide training and resources to help employees understand the benefits and functionality of passkeys.
- Integrate Passkeys with Existing Systems: Ensure compatibility with your current applications and services to facilitate a smooth transition.
- Monitor and Optimize: Continuously assess the effectiveness of your passkey implementation and make adjustments as needed.
Common Pitfalls and Solutions
While passkeys offer numerous benefits, there are potential challenges to be aware of:
- Device Dependency: Users may face difficulties if they lose access to their device. Solution: Implement backup authentication methods, such as security questions or backup codes.
- Compatibility Issues: Some legacy systems may not support passkeys. Solution: Gradually phase out outdated systems and prioritize compatibility in future technology investments.
- User Resistance: Some users may be hesitant to adopt new authentication methods. Solution: Communicate the benefits clearly and provide ample support during the transition.

Future Trends in Authentication
As cybersecurity threats continue to evolve, passkeys are poised to become the standard for authentication. Here are some trends to watch for:
- Increased Adoption: More organizations will adopt passkeys as awareness of their benefits grows, as seen in Microsoft's password manager updates.
- Integration with IoT Devices: Passkeys will extend to Internet of Things (IoT) devices, enhancing security in smart homes and workplaces.
- Advanced Biometrics: The use of advanced biometrics, such as voice recognition and behavioral biometrics, will enhance passkey authentication, as discussed in BizTech Magazine.
- Regulatory Support: Governments and regulatory bodies will increasingly endorse passkeys as a secure authentication method.

Conclusion
The UK's endorsement of passkeys as a superior alternative to passwords marks a significant milestone in the evolution of authentication. By embracing passkeys, individuals and organizations can enhance their security posture while enjoying a more convenient and user-friendly experience. As technology continues to advance, passkeys are set to become an integral part of the cybersecurity landscape, offering a future-proof solution to the challenges of digital authentication.
FAQ
What are passkeys?
Passkeys are a secure authentication method that uses cryptographic keys stored on a user's device to verify identity without traditional passwords.
How do passkeys enhance security?
Passkeys eliminate vulnerabilities such as phishing attacks and password breaches by using device-stored cryptographic keys for authentication.
What are the benefits of using passkeys?
Passkeys offer enhanced security, user convenience, faster authentication, and compatibility across multiple devices and platforms.
How can I implement passkeys in my organization?
Evaluate your current infrastructure, choose a suitable passkey solution, educate your team, integrate with existing systems, and monitor the implementation.
What are some common pitfalls when using passkeys?
Device dependency, compatibility issues, and user resistance are common challenges, but they can be mitigated with proper planning and communication.
What future trends should we expect in passkey authentication?
Expect increased adoption, integration with IoT devices, advanced biometric technologies, and regulatory support for passkey authentication.
Key Takeaways
- Passkeys provide enhanced security by eliminating vulnerabilities associated with passwords.
- Passkeys offer a seamless user experience with faster authentication.
- Organizations can implement passkeys by evaluating infrastructure and educating teams.
- Device dependency and compatibility are common challenges in passkey adoption.
- Future trends include IoT integration and advanced biometric technologies.
Related Articles
- AI Overcrowding the Smartphone: Embracing Simplicity for Wider Adoption [2025]
- The Silent Legacy of FTP Servers: Still Running and Still Vital [2025]
- The Hidden Risks of AI-Generated Passwords [2025]
- The Intersection of Reality and AI: Understanding the Complex Case of Iranian Women 'Saved' from Execution [2025]
- Crypto Scam Lures Ships into Strait of Hormuz: Navigating the Digital Threat [2025]
- Revolutionizing Naval Defense: The $5 Laser Solution Against Drone Threats [2025]
![Why Passkeys Are the Future of Authentication [2025]](https://tryrunable.com/blog/why-passkeys-are-the-future-of-authentication-2025/image-1-1776942262186.jpg)



