Crypto Scam Lures Ships into Strait of Hormuz: Navigating the Digital Threat [2025]
The murky waters of digital crime have once again converged with the high seas, this time in one of the world's most strategic maritime corridors—the Strait of Hormuz. Recent reports have unveiled a concerning trend where cybercriminals are exploiting the chaotic geopolitical environment and the anonymity of cryptocurrency to orchestrate scams aimed at shipping companies. This article dives deep into how these scams operate, their implications, and how stakeholders can protect themselves against such sophisticated threats.
TL; DR
- Crypto scams target ships: Cybercriminals exploit geopolitical tensions in the Strait of Hormuz, luring ships into a false sense of security, as detailed in Ars Technica's report.
- Digital deception: Scammers pose as Iranian authorities, demanding cryptocurrency payments for 'safe passage.'
- High stakes: The Strait of Hormuz is crucial for global oil and gas supply, making security breaches catastrophic, as highlighted by the New York Times.
- Tech vulnerabilities: Exploits target maritime communication systems, highlighting the need for robust cybersecurity.
- Future trends: Increased reliance on blockchain and AI for maritime security is anticipated.


Estimated data showing the distribution of tactics used in maritime crypto scams, highlighting the reliance on impersonation and technological exploits.
Navigating the Strait of Hormuz: A Maritime Chokepoint
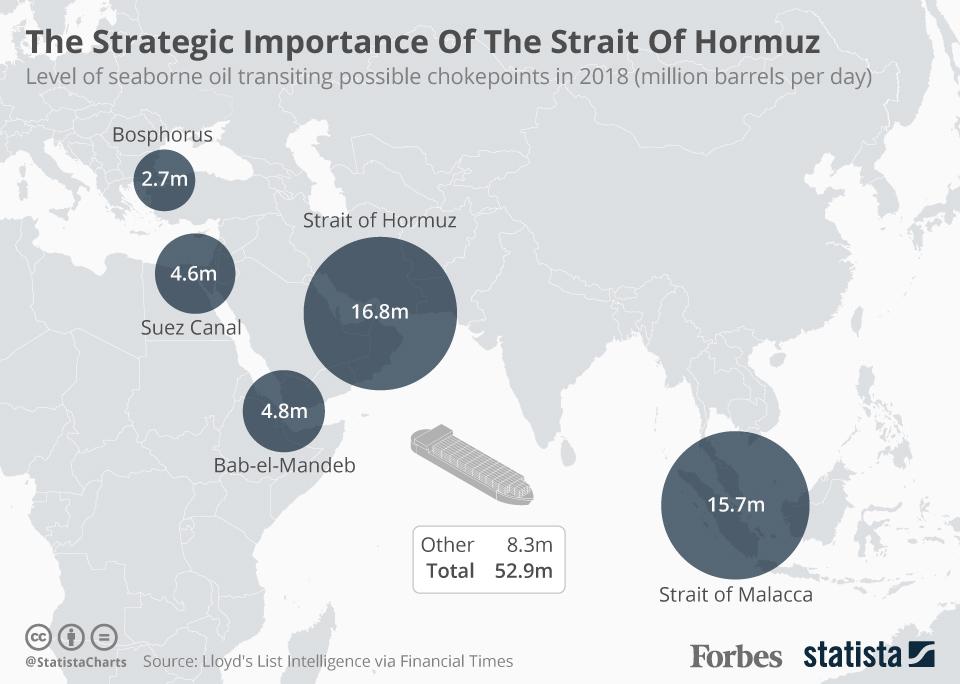
The Strait of Hormuz is a vital artery for global trade, particularly oil and liquefied natural gas. Approximately 20% of the world's petroleum passes through this narrow waterway, making it a focal point for geopolitical tensions and, increasingly, cyber threats. Understanding the strait's strategic importance is key to grasping why it has become a target for such scams, as noted by the World Economic Forum.
The Geopolitical Context
Located between Iran and Oman, the Strait of Hormuz connects the Persian Gulf with the Gulf of Oman and the Arabian Sea. Its strategic importance cannot be overstated: control over the strait equates to control over a significant portion of the world's oil supply. This has historically made it a flashpoint for international tensions, as reported by the BBC.
Iran has periodically asserted control over the strait, which can create confusion and vulnerability among shipping companies. This geopolitical uncertainty provides fertile ground for scammers.
The Rise of Digital Maritime Threats
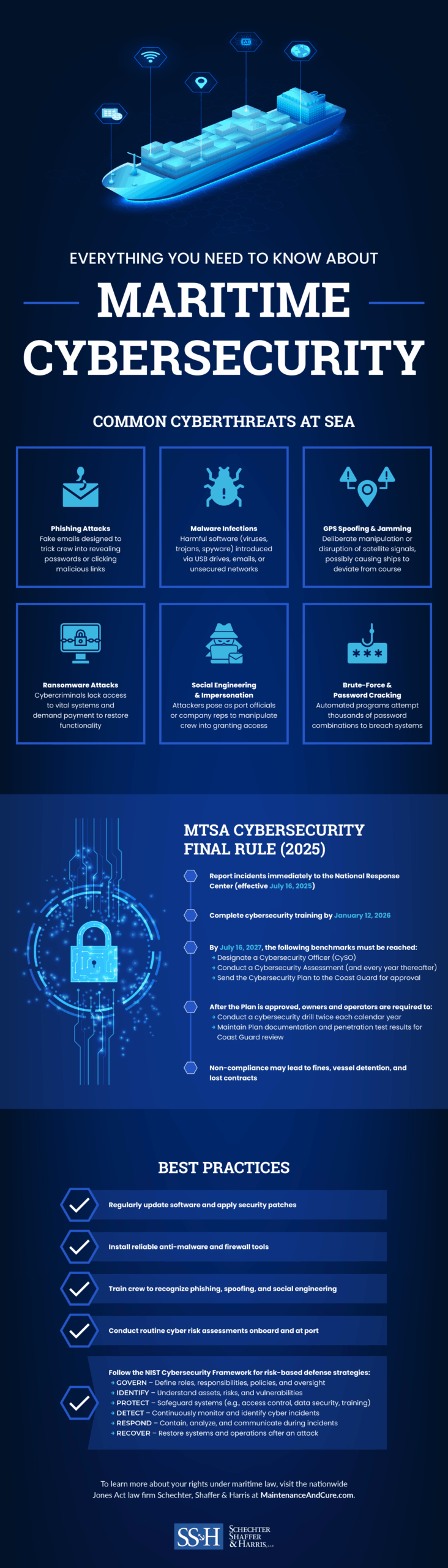
In recent years, the maritime industry has become increasingly reliant on digital technologies for navigation, communication, and operations. This digital transformation, while improving efficiency, also opens up new avenues for cyber threats. The intersection of physical and digital realms in maritime operations makes them susceptible to unique security challenges, as discussed in Honeywell's analysis.
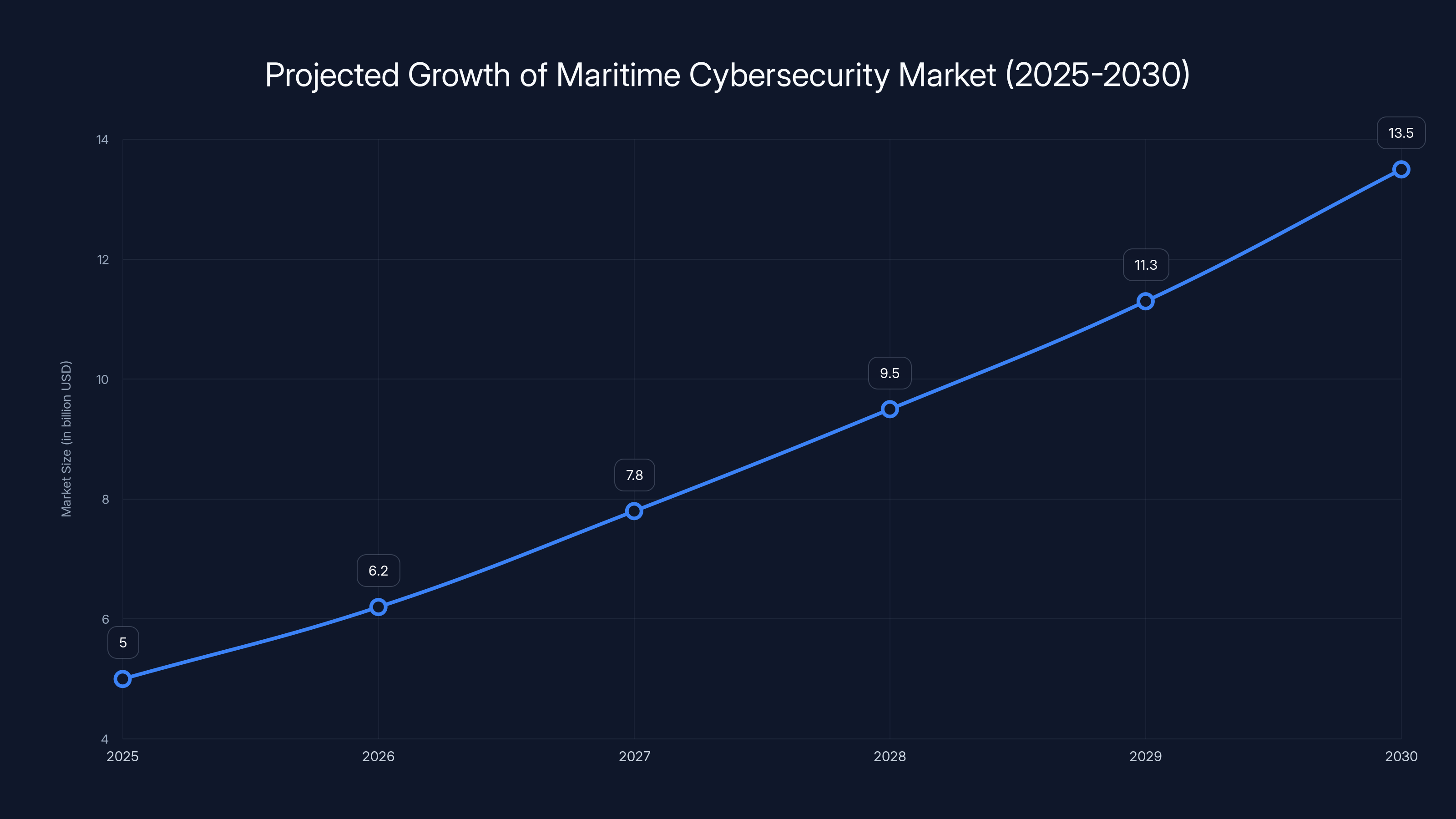
The maritime cybersecurity market is projected to grow significantly from 2025 to 2030, driven by advancements in blockchain, AI, and integrated security solutions. (Estimated data)
Anatomy of a Crypto Scam: How Ships Are Deceived
The recent scam targeting ships in the Strait of Hormuz involved criminals posing as Iranian authorities. They contacted shipping companies, demanding payment in cryptocurrency for safe passage through the strait. Let's dissect how these scams are orchestrated and their implications.
Step-by-Step Breakdown
-
Impersonation of Authorities: Scammers use phishing techniques to impersonate Iranian maritime authorities, leveraging official-looking communication channels to gain trust, as noted in the Ars Technica report.
-
Demand for Cryptocurrency: They demand payments in cryptocurrencies like Bitcoin or Tether, exploiting the anonymity and irreversibility of these transactions.
-
Exploitation of Geopolitical Tensions: The ongoing geopolitical tensions in the region make the fake claims of needing to pay for safe passage more believable.
-
Technological Exploits: Using sophisticated technology, scammers may hack into maritime communication systems to intercept and alter navigational messages.
Real World Consequences
The consequences of falling for such scams are dire. In one reported case, a ship that believed it had secured safe passage was attacked by Iranian forces—a stark reminder of the potential physical dangers stemming from digital deception. Beyond physical threats, the financial losses incurred from such scams can be substantial, impacting company operations and bottom lines, as highlighted by Yahoo Finance.
Cybersecurity in the Maritime Industry: Current Practices and Gaps
The maritime industry is at a precarious intersection of traditional naval operations and modern digital technology. While there are efforts to bolster cybersecurity, significant gaps remain that could be exploited by malicious actors.
Current Cybersecurity Measures
-
AIS Systems: The Automatic Identification System (AIS) is used for identifying and locating vessels. However, AIS data can be spoofed, leading to potential security breaches, as discussed in ABB's guidelines.
-
Maritime Cybersecurity Frameworks: Organizations like the International Maritime Organization (IMO) have established guidelines for cybersecurity management on ships.
-
Training and Awareness Programs: Regular training for crew members on identifying phishing attempts and suspicious activities is crucial.
Gaps and Vulnerabilities
-
Outdated Technology: Many ships still rely on legacy systems that are not designed to withstand modern cyber threats, as noted by GlobeNewswire.
-
Lack of Standardization: There is a disparity in cybersecurity practices across different regions and shipping companies, leading to inconsistent protection levels.
-
Human Error: As with many industries, human error remains a significant vulnerability, often exploited by phishing attacks.
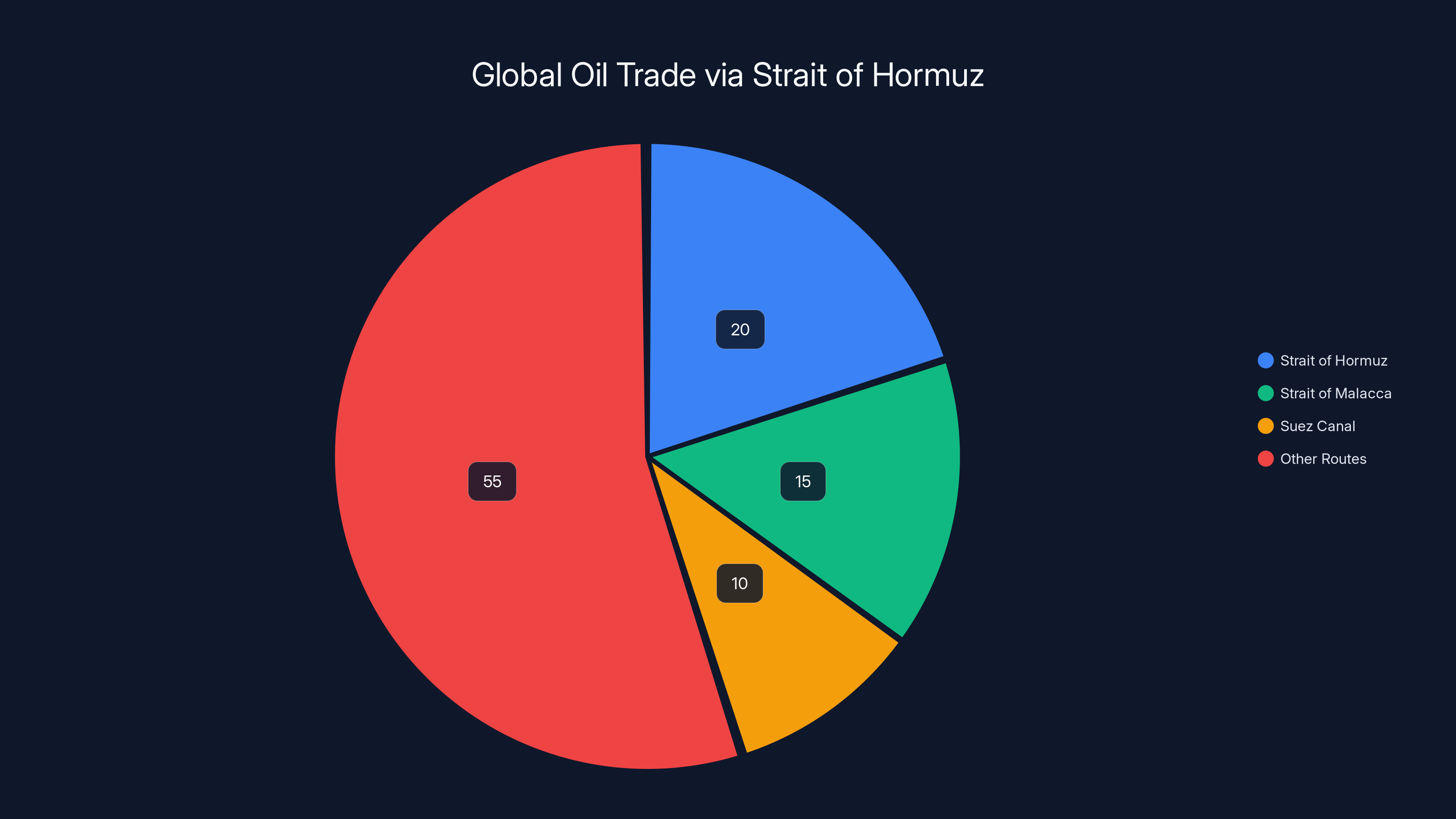
The Strait of Hormuz accounts for approximately 20% of the world's petroleum trade, highlighting its strategic importance. Estimated data based on typical distribution.
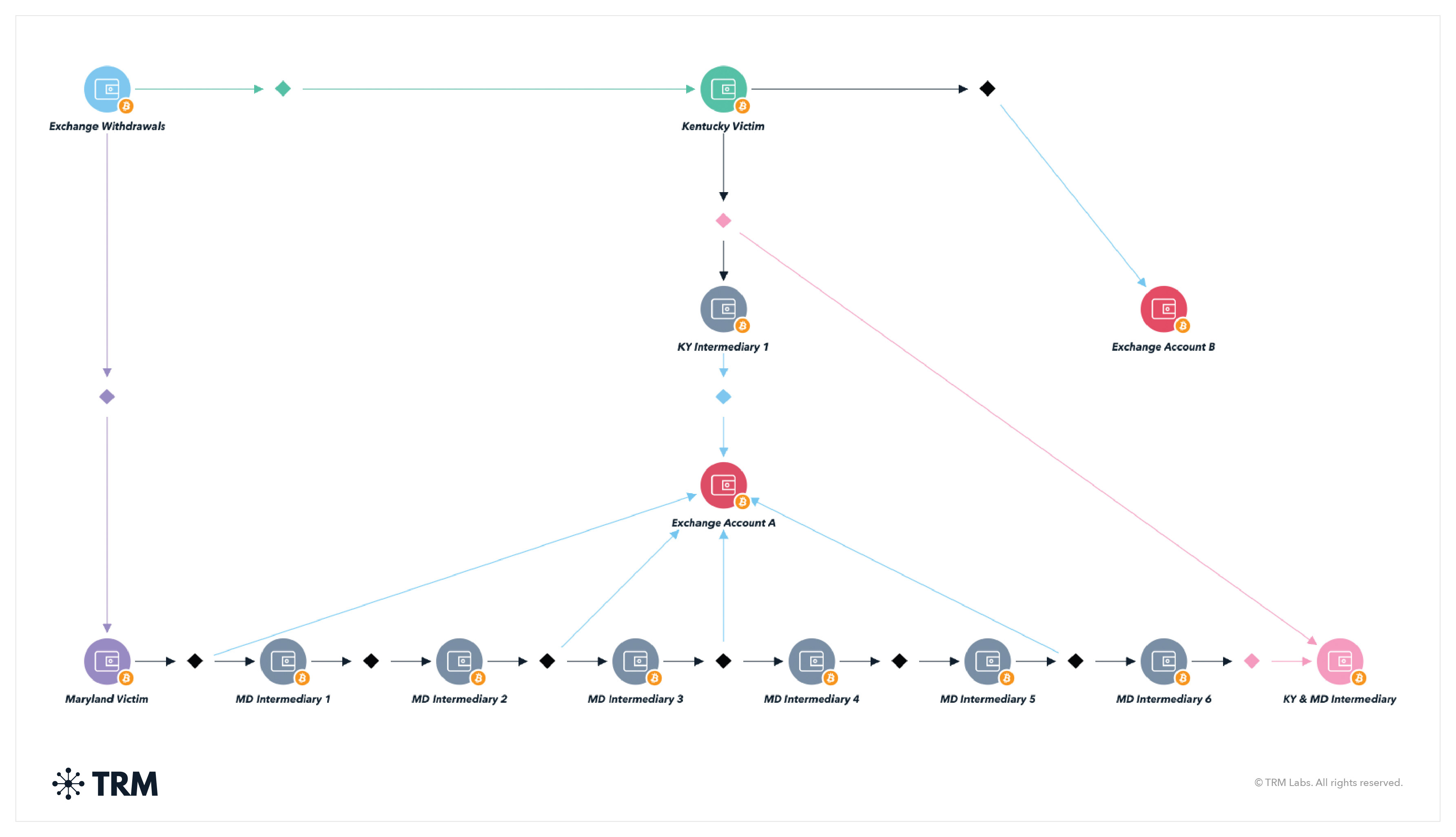
The Role of Cryptocurrency: Anonymity and Irreversibility
Cryptocurrency plays a pivotal role in these scams due to its inherent characteristics. Understanding these attributes can help stakeholders develop more robust defense mechanisms.
Why Cryptocurrency?
-
Anonymity: Cryptocurrencies offer a level of anonymity that traditional financial transactions do not, making it difficult to trace payments.
-
Irreversibility: Once a cryptocurrency transaction is completed, it cannot be reversed, a feature that scammers exploit to ensure their demands are met without recourse.
Implications for Maritime Security
The use of cryptocurrency in scams highlights the need for shipping companies to not only focus on physical security but also on financial transaction security. Robust verification processes and secure communication channels are essential, as emphasized by Yahoo Finance UK.
Implementing Best Practices: Protecting Ships from Crypto Scams
Proactive measures are essential to guard against the evolving threat landscape in maritime security. Here are some practical steps that companies can take to protect their vessels and crews.
Best Practices for Shipping Companies
-
Enhanced Verification Protocols: Implement multi-factor authentication for all communications related to financial transactions.
-
Regular Cybersecurity Audits: Conduct frequent audits to identify vulnerabilities in onboard systems and shore-based operations.
-
Incident Response Plan: Develop a comprehensive incident response plan that includes protocols for potential cyber-attacks and scams.
-
Collaboration with Authorities: Establish direct communication lines with legitimate authorities to verify any claims or demands made by third parties.

Phishing scams are the most prevalent, accounting for 35% of crypto scams targeting shipping companies in the Strait of Hormuz. Estimated data.
Future Trends: The Evolution of Maritime Cybersecurity
As cyber threats continue to evolve, so too must the strategies employed by the maritime industry to combat them. Here are some trends to watch.
Increasing Use of Blockchain Technology
Blockchain technology offers a secure and transparent way to handle transactions and data, which could significantly reduce the risk of scams and cyber attacks, as discussed in The Detroit Bureau.
AI-Powered Threat Detection
Artificial Intelligence (AI) can be leveraged to detect anomalies in communication patterns and identify potential threats before they materialize.
Integrated Security Solutions
Future cybersecurity solutions will need to integrate both physical and digital security measures to provide comprehensive protection.
Geopolitical Developments
Ongoing geopolitical tensions will continue to influence the security landscape, necessitating adaptive and resilient strategies, as highlighted by the World Economic Forum.
Conclusion: Navigating the New Maritime Reality
The intersection of digital and maritime threats presents a complex challenge for the shipping industry. As cybercriminals become more sophisticated, it's imperative that shipping companies and maritime authorities stay ahead with robust cybersecurity measures. While the current situation in the Strait of Hormuz is a stark reminder of the vulnerabilities that exist, it also serves as a call to action for enhanced vigilance and innovation in maritime security.
By embracing new technologies, fostering international cooperation, and prioritizing cybersecurity, the maritime industry can navigate these threats and ensure the safe passage of ships through one of the world's most critical waterways.
FAQ
What makes the Strait of Hormuz a target for cyber scams?
The Strait of Hormuz is a strategic chokepoint for global oil and gas trade, making it a high-value target for geopolitical tensions and, consequently, cyber scams that exploit these vulnerabilities.
How do cryptocurrency scams exploit maritime operations?
Scammers impersonate authorities to demand cryptocurrency payments for 'safe passage,' exploiting the anonymity and irreversibility of digital currencies.
What are the key cybersecurity vulnerabilities in the maritime industry?
Key vulnerabilities include outdated technology, lack of standardization in cybersecurity practices, and human error, which can all be exploited by cybercriminals.
How can shipping companies protect themselves from these scams?
Shipping companies can enhance verification protocols, conduct regular cybersecurity audits, develop comprehensive incident response plans, and collaborate with legitimate authorities.
What role does blockchain play in enhancing maritime security?
Blockchain technology provides secure, transparent, and tamper-proof transaction verification, which can significantly reduce the risk of scams and cyber attacks.
How is AI being used to combat maritime cyber threats?
AI can detect anomalies in communication patterns and identify potential threats, enabling proactive defense measures against cyber attacks.

Key Takeaways
- Crypto scams exploit geopolitical tensions in the Strait of Hormuz.
- Scammers impersonate authorities to demand cryptocurrency payments.
- The maritime industry faces unique cybersecurity challenges.
- Outdated technology and human error are key vulnerabilities.
- Blockchain and AI offer promising solutions for maritime security.
- International cooperation is crucial for navigating these threats.
Related Articles
- France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]
- Understanding Apple's iPhone Bug Fix: Protecting Deleted Messages [2025]
- AI Models: The New Generation of Scammers [2025]
- How AI Tools Empower North Korean Hackers to Steal Millions [2025]
- Understanding New York's Ban on Insider Trading in Prediction Markets [2025]
- Understanding the Rising Threat of Hacktivist Attacks in the UK [2025]
![Crypto Scam Lures Ships into Strait of Hormuz: Navigating the Digital Threat [2025]](https://tryrunable.com/blog/crypto-scam-lures-ships-into-strait-of-hormuz-navigating-the/image-1-1776897358640.jpg)



