Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
Phishing attacks have evolved significantly over the years, with cybercriminals employing increasingly sophisticated methods to deceive their targets. One of the latest tactics involves exploiting Google Tasks, a legitimate tool used by millions to manage tasks and projects. In this article, we'll dive deep into how hackers abuse Google Tasks to deliver phishing emails, explore the technical details of these scams, and provide practical steps to protect your workplace from falling victim.
TL; DR
- Hackers Exploit Google Tasks: Cybercriminals use Google Tasks to send phishing emails that bypass spam filters by leveraging legitimate notifications, as noted by Kaspersky.
- Technical Breakdown: Fake tasks are created and assigned to users, triggering Google notifications that appear authentic.
- Best Practices: Implement security measures like email filtering, employee training, and multi-factor authentication to mitigate risks, as recommended by Cybersecurity Ventures.
- Common Pitfalls: Over-reliance on automated spam filters can lead to complacency and increased vulnerability, as highlighted by Simplilearn.
- Future Trends: Expect phishing tactics to become more sophisticated, targeting other legitimate tools and services.
- Bottom Line: Stay vigilant and proactive in your cybersecurity approach to protect your workplace from evolving threats.

Multi-Factor Authentication and AI-Powered Filters are estimated to be the most effective measures in reducing security threats. Estimated data based on typical industry assessments.
Understanding the Google Tasks Scam
Google Tasks is part of Google Workspace, providing users with a simple way to manage their to-do lists, integrate with Gmail and Google Calendar, and more. However, cybercriminals have found a way to exploit this legitimate service to deliver phishing attacks.
How the Scam Works
Hackers create fake tasks and assign them to unsuspecting users by adding their email addresses. This action triggers a legitimate Google notification, which is typically trusted by recipients. These notifications bypass traditional spam filters because they originate from a legitimate source—Google itself, as explained by TechRadar.
Once the target receives the notification, they might click on the included links, thinking they are legitimate. These links often lead to phishing sites designed to steal sensitive information such as login credentials or personal data.
Why This Method is Effective
- Legitimate Source: Notifications come from Google, a trusted entity, making them less likely to be flagged as spam.
- Bypassing Spam Filters: Traditional email filters may not catch these notifications as they appear to be legitimate.
- User Trust: Users are more likely to trust and engage with notifications from well-known services.
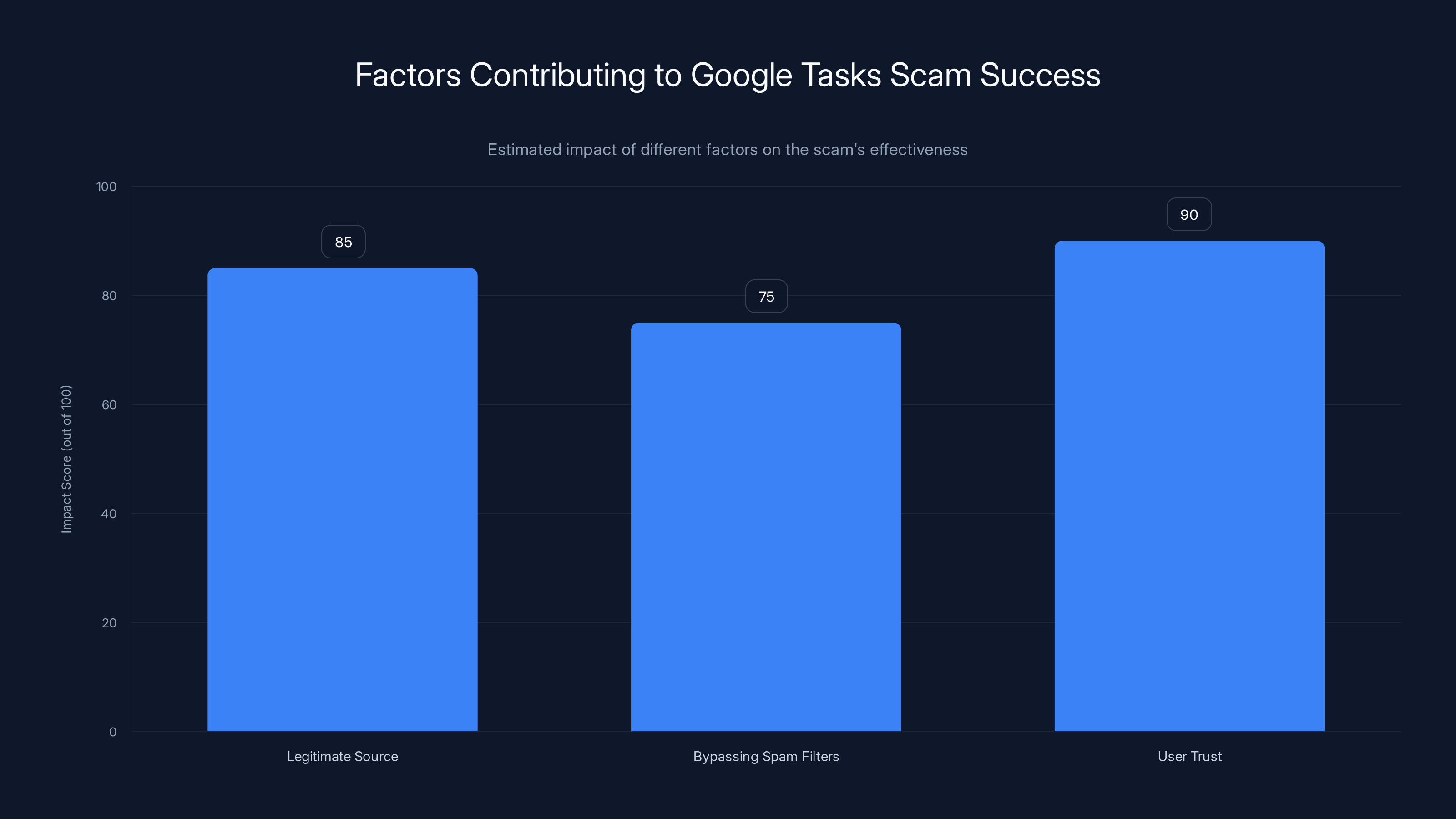
User trust and the legitimate source of notifications are key factors making the Google Tasks scam effective. Estimated data.
Practical Implementation Guides
Step 1: Enhance Email Filtering
Implement advanced email filtering solutions that can detect and block suspicious activity even from legitimate sources like Google. These solutions should be capable of analyzing the content and context of emails, rather than just their origin.
- Use AI-Powered Filters: AI can analyze patterns and detect anomalies that traditional filters might miss, as discussed in Microsoft's security blog.
- Regularly Update Filters: Ensure your email filtering solutions are regularly updated to recognize new threats.
Step 2: Employee Training
Educate your employees about the risks associated with phishing scams, including those exploiting Google Tasks. Regular training sessions can help employees recognize and report suspicious activities.
- Conduct Phishing Simulations: Simulate phishing attacks to test employee awareness and improve their response.
- Provide Clear Reporting Channels: Make it easy for employees to report suspicious emails without fear of repercussion.
Step 3: Implement Multi-Factor Authentication (MFA)
Require MFA for all employee accounts to add an extra layer of security. MFA can prevent unauthorized access even if login credentials are compromised.
- Use App-Based MFA: Encourage the use of authenticator apps rather than SMS-based MFA, which can be vulnerable to SIM swapping attacks.
- Educate Employees on MFA Benefits: Ensure employees understand the importance and effectiveness of MFA in protecting their accounts.

Common Pitfalls and Solutions
Pitfall 1: Over-Reliance on Automated Solutions
Relying solely on automated spam filters can lead to complacency. While these solutions are powerful, they are not infallible.
- Solution: Combine automated solutions with human oversight. Regularly review and update security protocols, as suggested by MEXC.
Pitfall 2: Inadequate Employee Training
Employees are often the weakest link in cybersecurity. Without proper training, they may fall victim to sophisticated phishing attacks.
- Solution: Implement ongoing training programs that adapt to new threats. Encourage a culture of security awareness.
Pitfall 3: Neglecting MFA Implementation
Not all organizations prioritize MFA, leaving them vulnerable to account takeovers.
- Solution: Make MFA mandatory for all employees and regularly review its implementation.

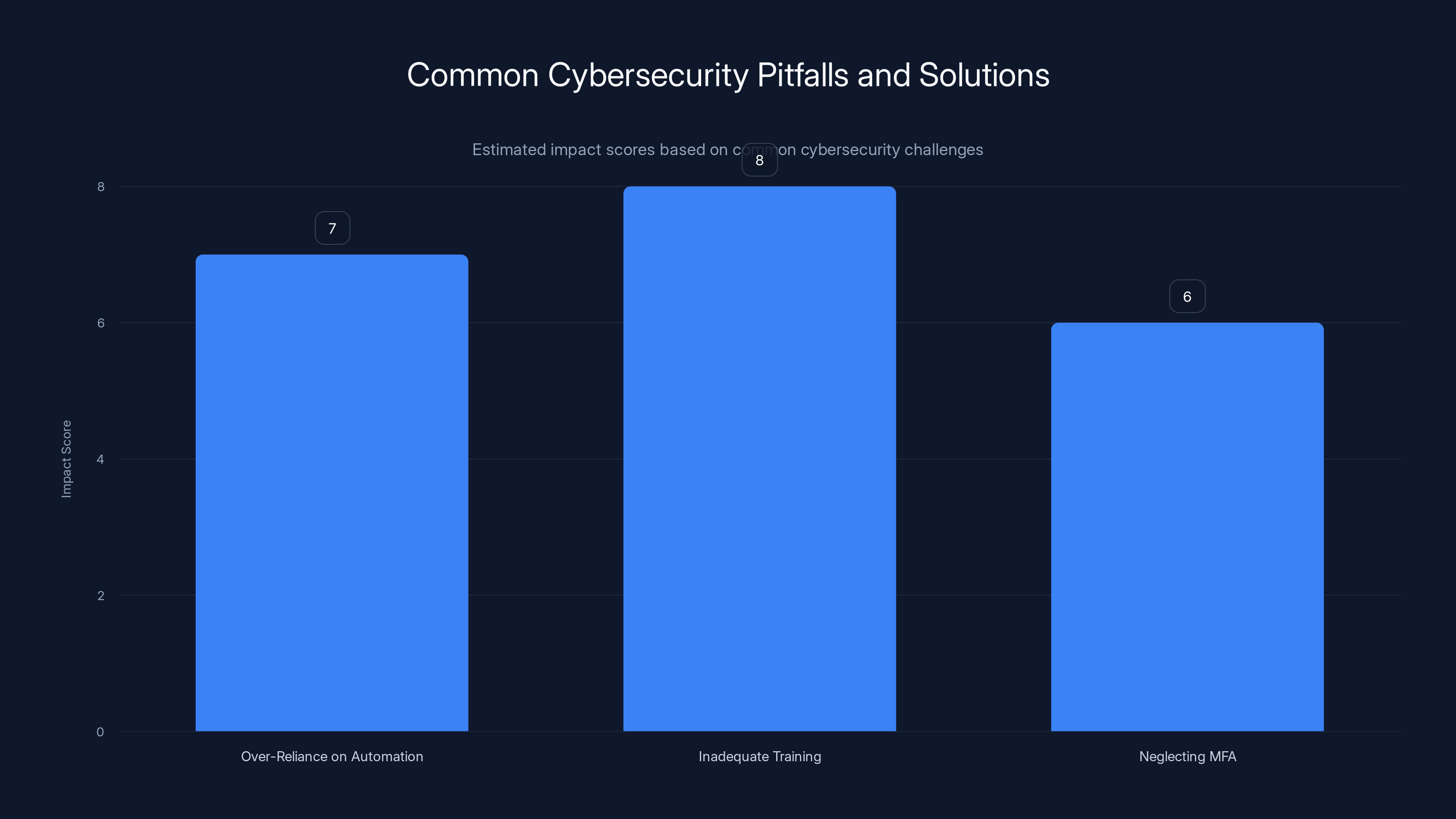
Estimated data shows that inadequate employee training has the highest impact score, highlighting the need for comprehensive training programs.
Future Trends and Recommendations
Trend 1: Increasing Sophistication of Phishing Tactics
Phishing tactics will continue to evolve, targeting other legitimate tools and services. Cybercriminals will likely exploit new vulnerabilities as they emerge, as noted by TechAfrica News.
- Recommendation: Stay informed about the latest phishing trends and update your security measures accordingly.
Trend 2: Greater Emphasis on Employee Education
As phishing attacks become more sophisticated, organizations will place a greater emphasis on employee education and training.
- Recommendation: Develop comprehensive training programs that cover a wide range of cyber threats.
Trend 3: Integration of AI in Cybersecurity
AI and machine learning will play an increasingly important role in detecting and preventing phishing attacks.
- Recommendation: Invest in AI-powered cybersecurity solutions to enhance your organization's ability to detect and respond to threats.

Conclusion
Phishing attacks exploiting Google Tasks represent a growing threat to organizations worldwide. By understanding how these scams work and implementing robust security measures, you can protect your workplace from falling victim to these sophisticated attacks. Stay proactive, educate your employees, and leverage advanced technologies to stay one step ahead of cybercriminals.
FAQ
What is a phishing attack?
A phishing attack is a type of cybercrime where attackers impersonate legitimate organizations to steal sensitive information from individuals, such as login credentials or financial information.
How do hackers exploit Google Tasks for phishing?
Hackers create fake tasks and assign them to users, triggering legitimate Google notifications that bypass spam filters, making it easier to deceive recipients.
What are the signs of a phishing email?
Common signs include unexpected requests for personal information, urgent language, unknown senders, and suspicious links. Always verify the sender's identity and the legitimacy of the request.
How can I protect my workplace from phishing attacks?
Implement advanced email filtering, conduct regular employee training, require multi-factor authentication, and encourage a culture of security awareness.
Why is multi-factor authentication important?
MFA adds an extra layer of security by requiring users to verify their identity through multiple methods, reducing the risk of unauthorized access.
Key Takeaways
- Hackers exploit Google Tasks to send phishing emails that bypass spam filters.
- Fake tasks trigger legitimate Google notifications, deceiving recipients.
- Implement email filtering, employee training, and MFA to mitigate risks.
- Over-reliance on automated solutions can lead to increased vulnerability.
- Phishing tactics will continue to evolve, targeting new vulnerabilities.
Related Articles
- Ransomware Payments Plummet Even as Attacks Surge: Insights and Strategies [2025]
- Safeguarding AI Agents: How IronCurtain Prevents Rogue Behavior [2025]
- AI vs. the Pentagon: Killer Robots, Mass Surveillance, and Red Lines [2025]
- AI-Driven Workforce Transformation: Embracing Smaller Teams for Efficiency [2025]
- Understanding and Mitigating Critical Security Flaws in Windows Systems [2025]
- MWC 2026: The Future Unveiled in Barcelona – Phones, Gadgets, and Innovations
![Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]](https://tryrunable.com/blog/beware-of-google-tasks-scams-protect-your-workplace-from-phi/image-1-1772215519124.jpg)



