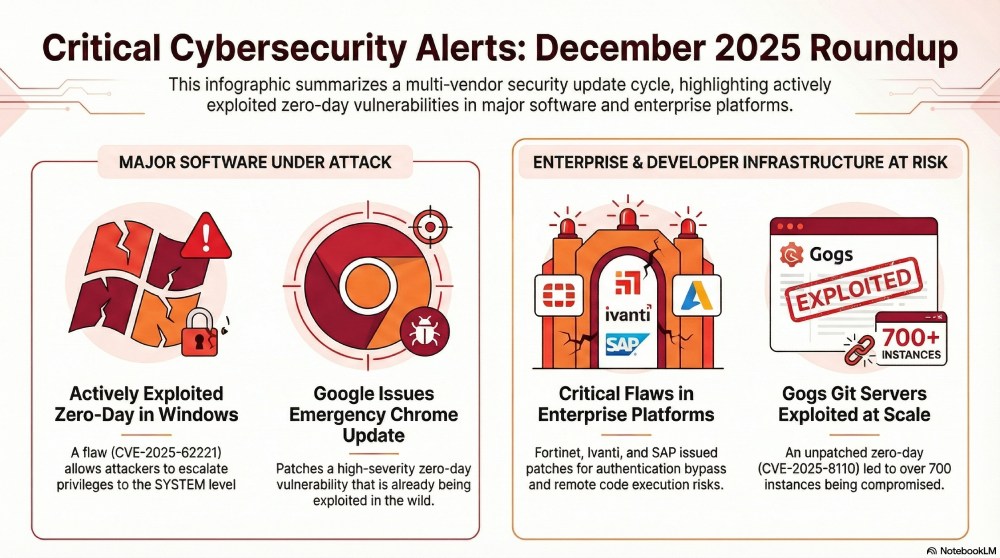
Understanding and Mitigating Critical Security Flaws in Windows Systems [2025]
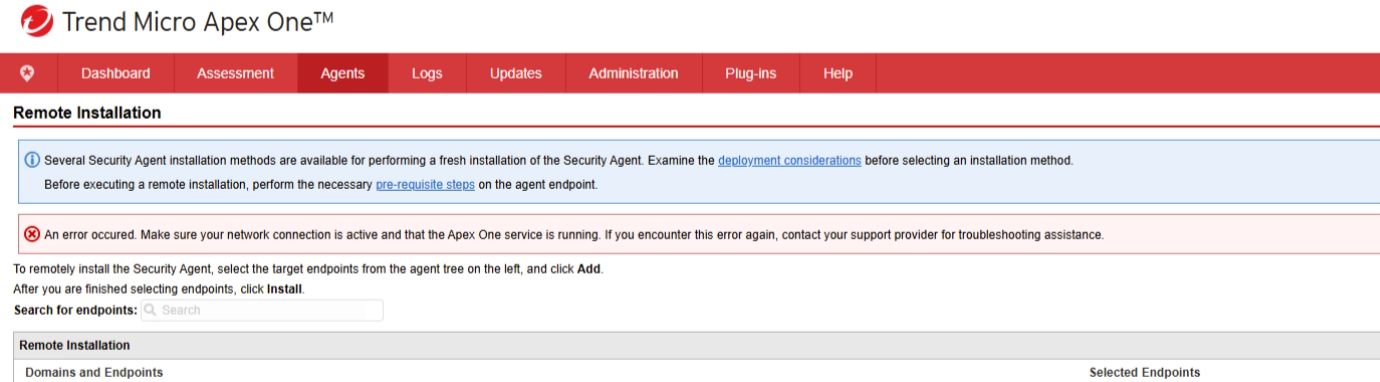
Security flaws in software systems can pose significant risks to any organization, especially when those vulnerabilities allow for complete system takeover. Trend Micro recently highlighted such critical vulnerabilities in their Apex One management console, emphasizing the urgency for users to update their systems. In this comprehensive guide, we'll dive into the nature of these vulnerabilities, their potential impacts, and the best practices for mitigation.
TL; DR
- Critical Flaws: Two vulnerabilities in Trend Micro's Apex One console scored 9.8/10 in severity, as reported by CyberPress.
- Immediate Action Required: On-premises users must apply the patch immediately.
- Exploitation Risk: Requires console access; SaaS versions are already patched, according to BleepingComputer.
- Path Traversal Explained: Allows unauthorized access to system resources.
- Future Trends: Emphasis on zero-trust architectures and automatic patching.
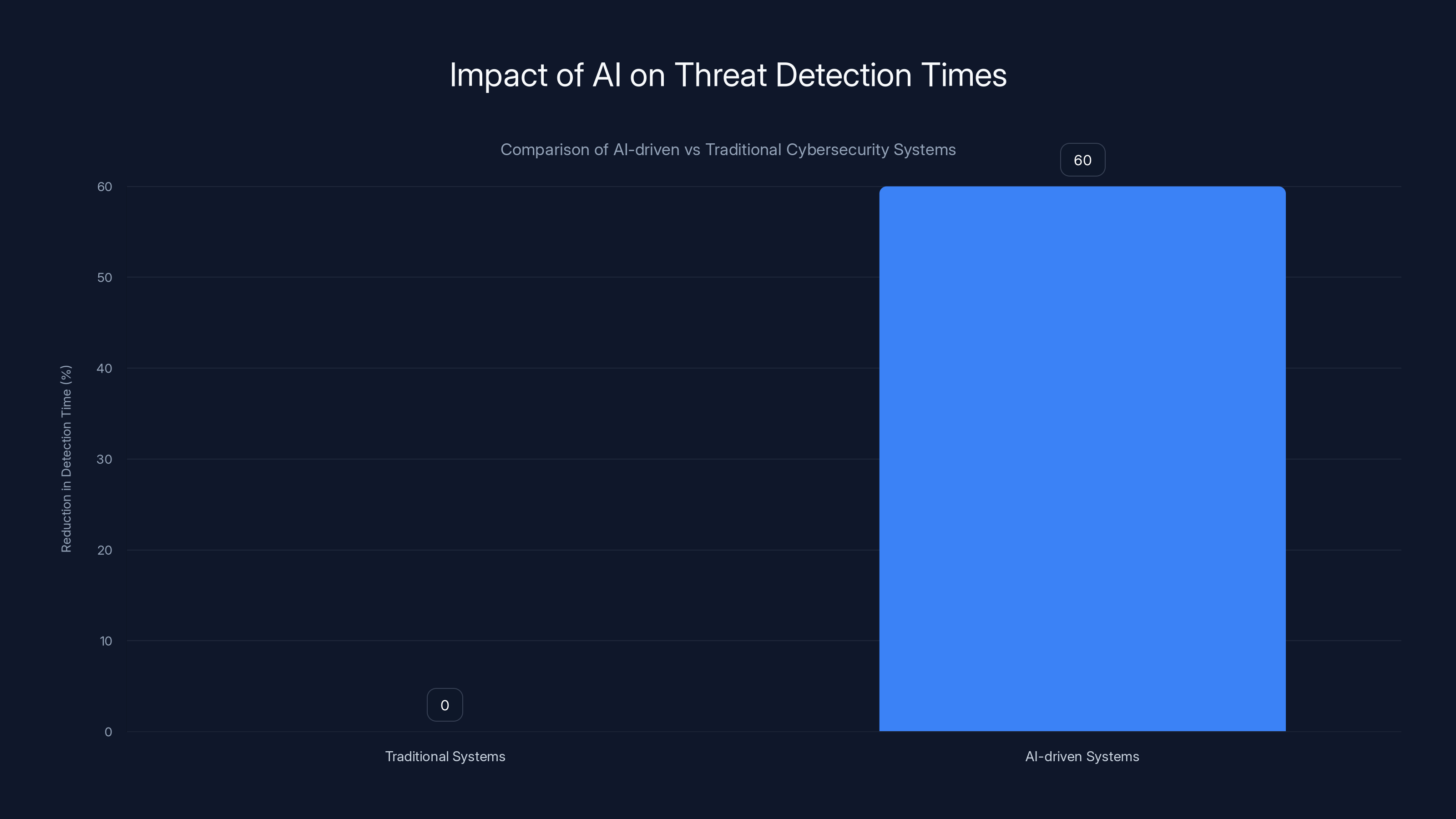
AI-driven cybersecurity systems are projected to reduce threat detection times by over 60% compared to traditional methods by 2025. Estimated data.
The Critical Security Vulnerabilities
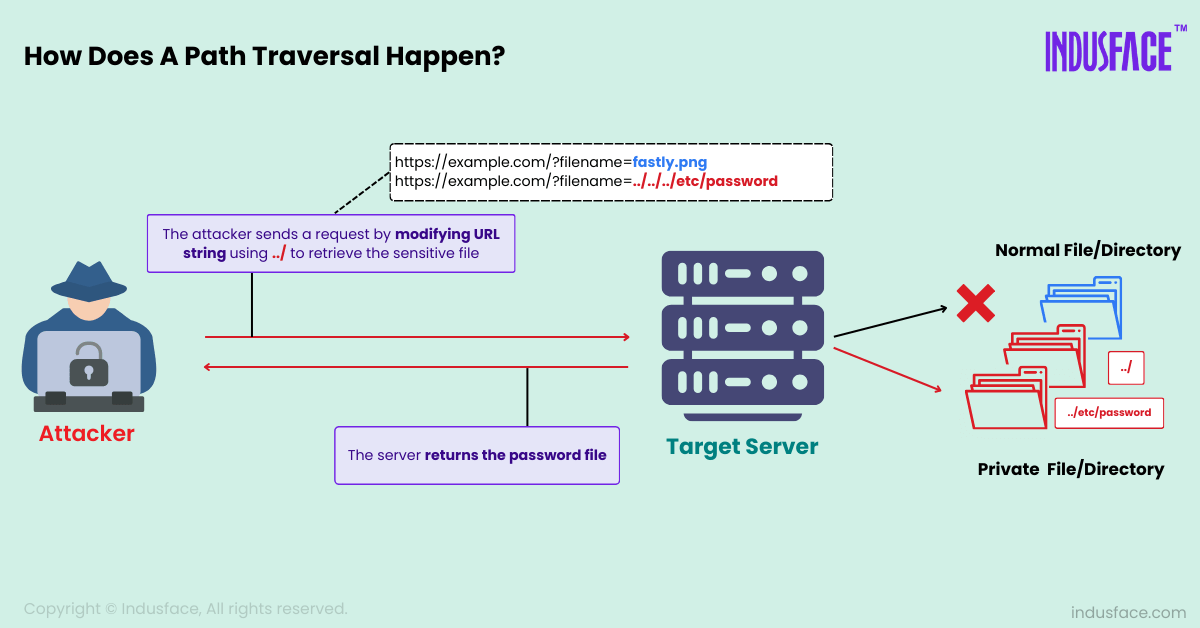
What Are Path Traversal Vulnerabilities?
Path traversal vulnerabilities occur when an application improperly sanitizes user input, allowing an attacker to access files and directories that reside outside the web root folder. These flaws can lead to unauthorized access to sensitive system files, potentially allowing attackers to execute arbitrary code.
The CVE-2025-71210 and CVE-2025-71211
These specific vulnerabilities were discovered in Trend Micro's Apex One management console. They scored a critical severity due to their potential to allow attackers to completely take over the affected systems. Both vulnerabilities are path traversal flaws, which exploit improper input validation, as detailed by Rescana.
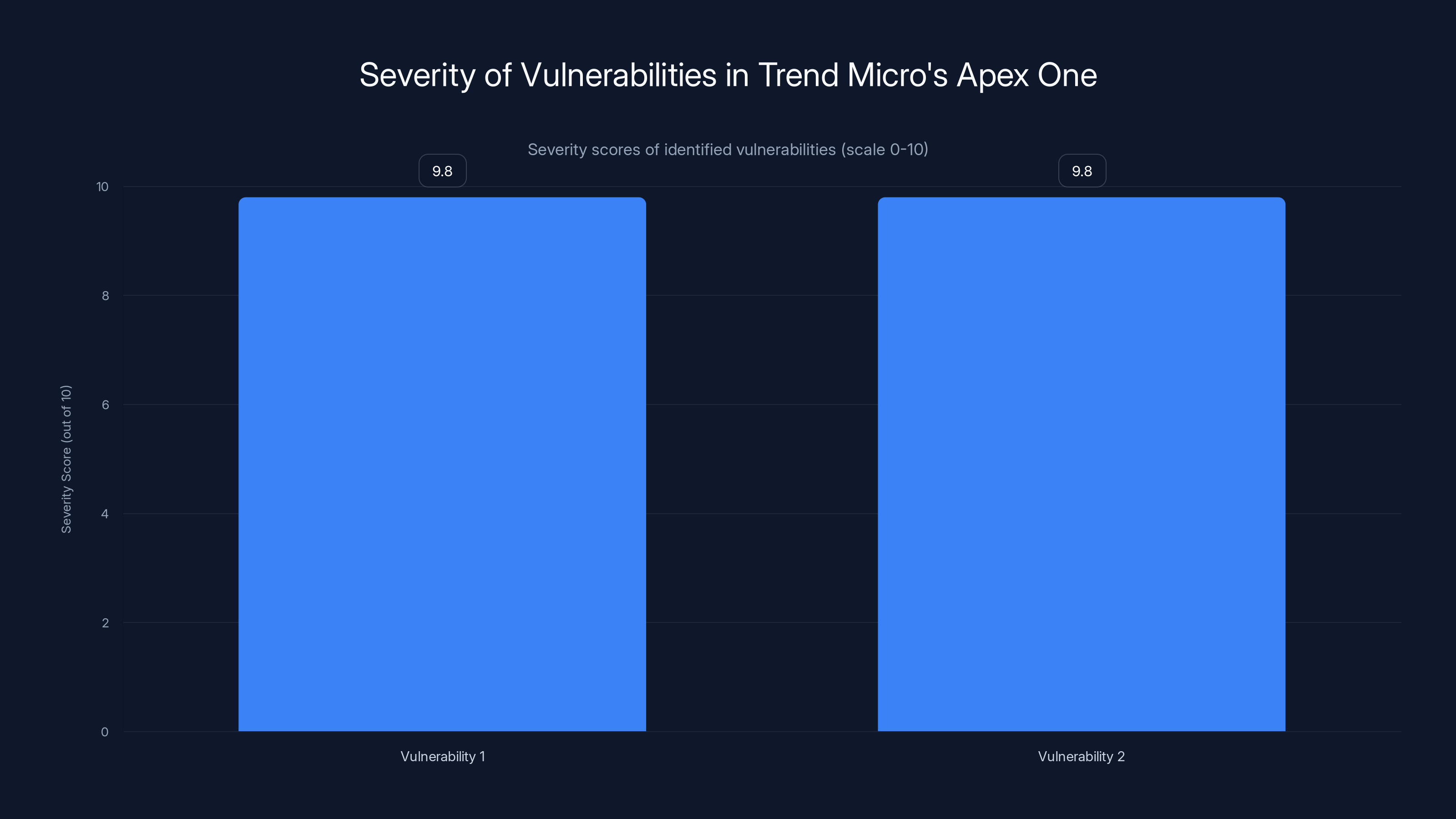
Both vulnerabilities in Trend Micro's Apex One console have a critical severity score of 9.8 out of 10, highlighting the urgent need for patching.
The Risks of Unpatched Systems
Full System Takeover
When exploited, these vulnerabilities could allow an attacker to gain full control over the affected Windows system. This includes the ability to execute arbitrary code, access sensitive data, and potentially use the system as a launchpad for further attacks within the network.
Data Breach and Compliance Issues
A successful exploit could lead to significant data breaches, exposing sensitive information and leading to compliance violations. Organizations can face hefty fines and reputational damage as a result, as noted by HIPAA Journal.

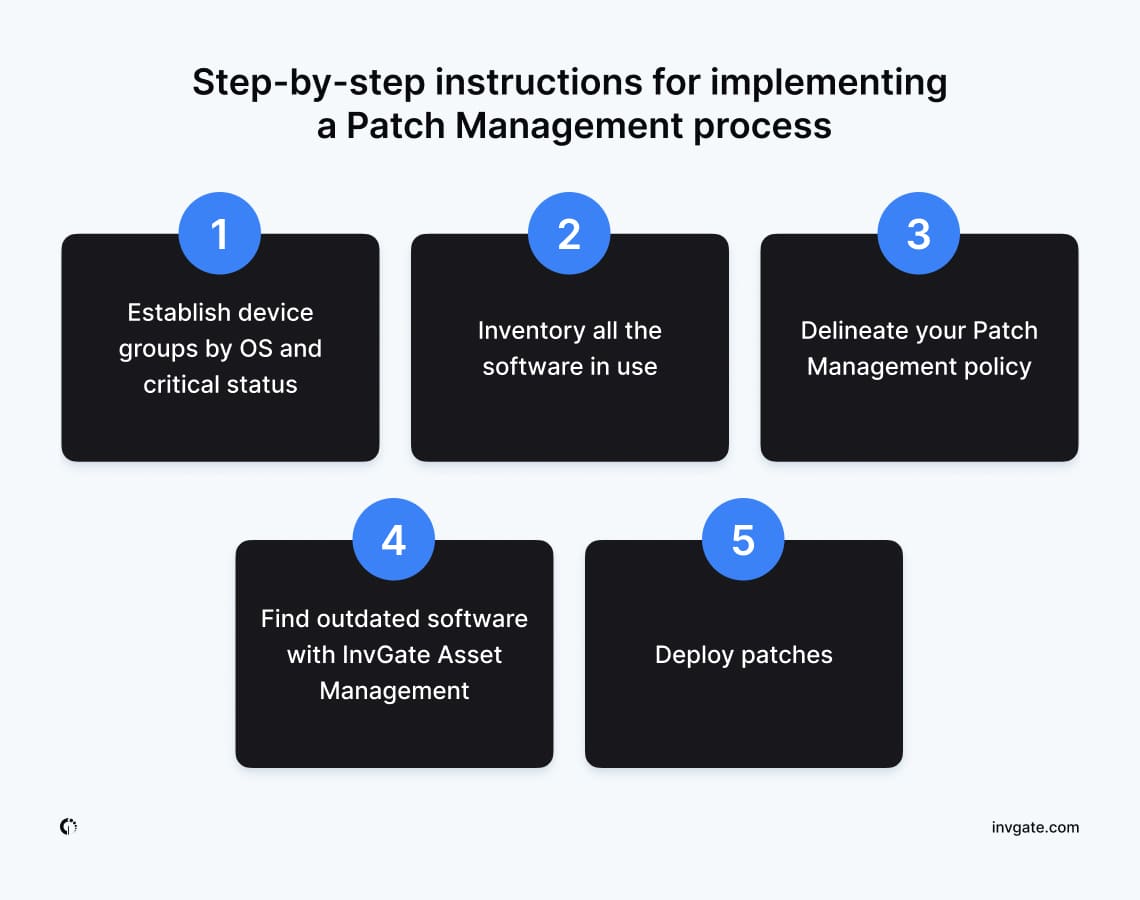
Implementing Security Patches
Steps for Patching On-Premises Systems
- Backup Critical Data: Ensure that all critical data is backed up before applying patches.
- Download the Patch: Obtain the latest patch from Trend Micro’s official site.
- Test the Patch: Apply the patch in a test environment first to ensure it does not disrupt operations.
- Deploy the Patch: Apply the patch to production systems during a scheduled maintenance window.
- Verify the Update: Check the system to ensure the patch was applied successfully.
SaaS Solutions
For users of Trend Micro’s SaaS version, the patches are applied automatically. However, it's crucial to verify that the system is updated by checking the version number against the latest release, as advised by CyberPress.
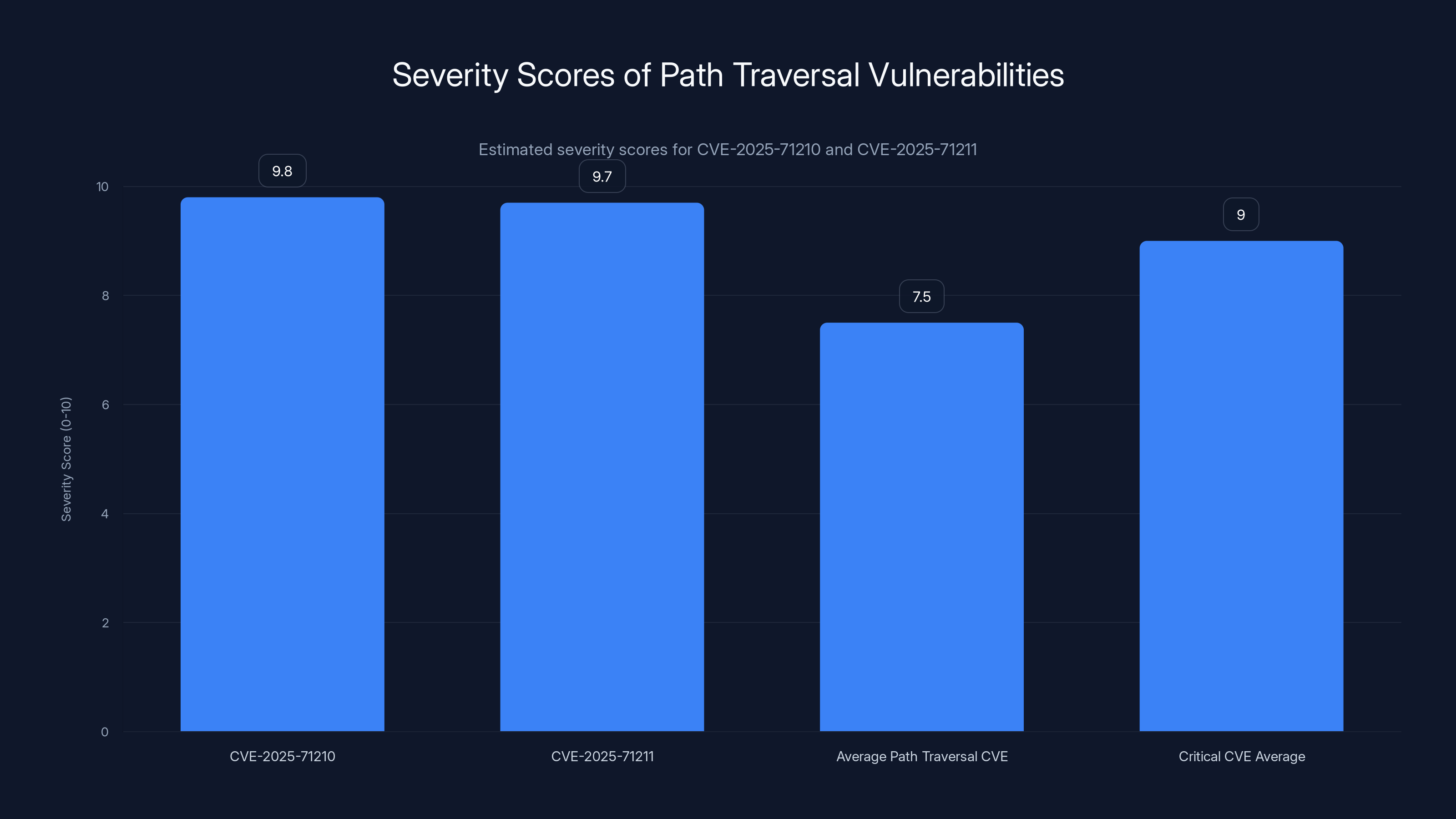
The CVE-2025-71210 and CVE-2025-71211 have high severity scores of 9.8 and 9.7 respectively, indicating their critical impact compared to average path traversal vulnerabilities. Estimated data.
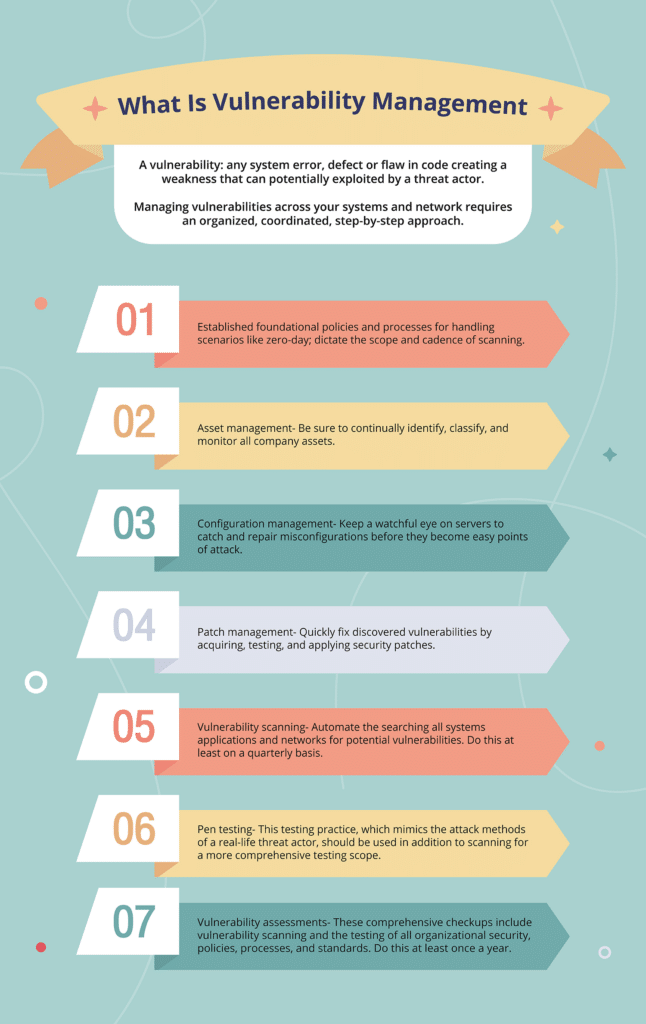
Best Practices for Vulnerability Management
Regular System Updates
Ensure that all systems and software are regularly updated. Enable automatic updates where possible to minimize the window of exposure to new vulnerabilities.
Implementing a Zero-Trust Architecture
Adopt a zero-trust security model that assumes breaches will occur. This involves verifying each request as though it originates from an open network, regardless of where the request comes from, as explained by Wiz.io.
Conducting Regular Security Audits
Perform regular security audits and vulnerability assessments to identify and mitigate potential risks. Use both automated tools and manual reviews to cover all bases.
Common Pitfalls and Solutions
Ignoring Test Environments
One common mistake is failing to test patches in a controlled environment before deployment. This can result in unexpected downtime or system failures.
Solution: Always apply patches in a test environment first, and monitor the system’s behavior closely.
Delayed Patch Application
Delays in applying patches can leave systems vulnerable to exploits.
Solution: Establish a clear patch management policy, prioritizing critical patches and setting defined timelines for application.

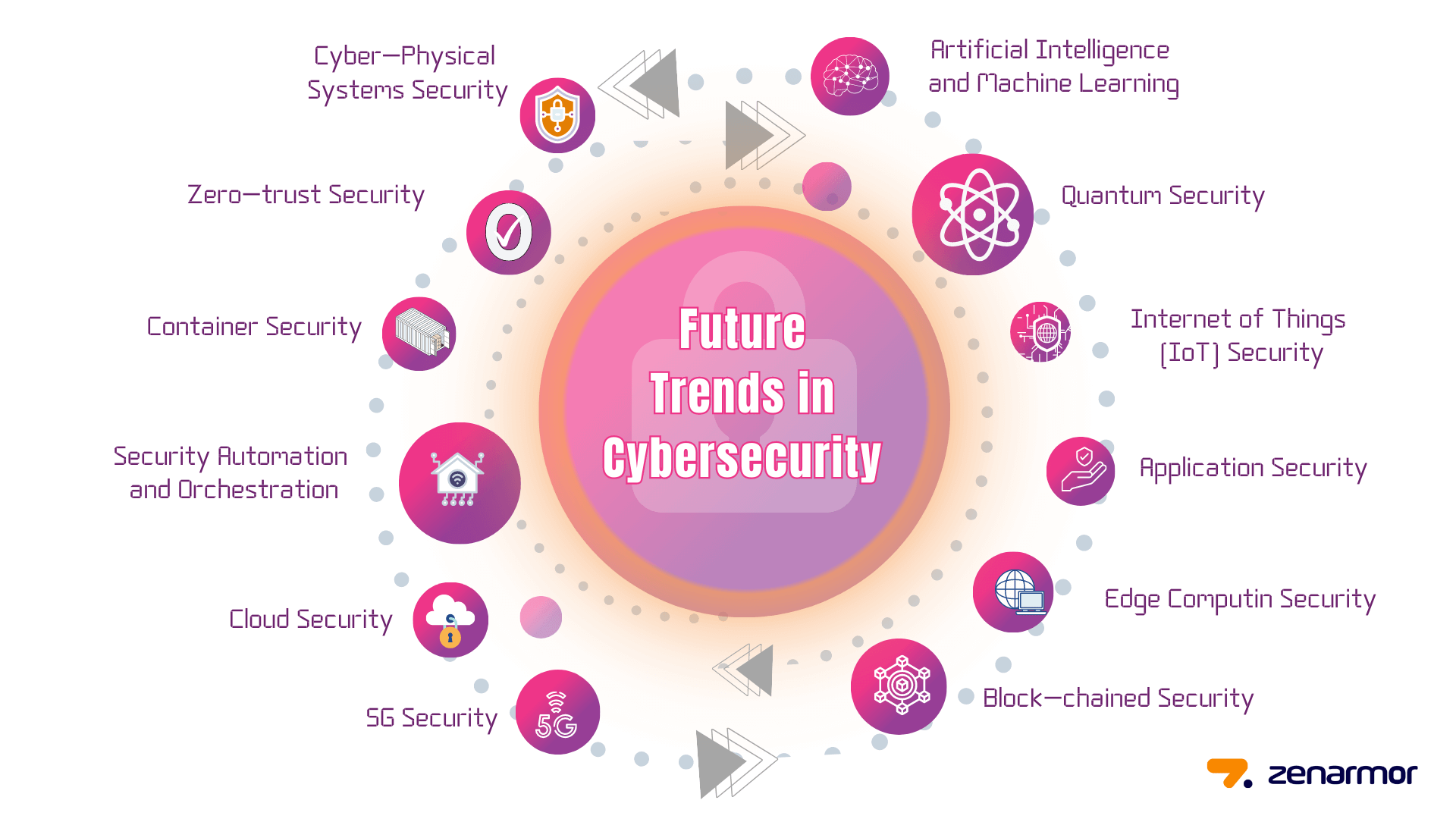
Future Trends in Cybersecurity
Emphasis on Automation
Automation will play a significant role in future cybersecurity strategies, helping to streamline patch management and vulnerability assessments.
AI and Machine Learning
Leveraging AI and machine learning will enhance threat detection capabilities, allowing for faster identification and response to emerging threats, as noted by Cybersecurity Ventures.
The Rise of DevSecOps
Integrating security into the DevOps process ensures that security considerations are included from the start, reducing vulnerabilities in production environments.
Conclusion
Addressing security vulnerabilities promptly is crucial for maintaining system integrity and protecting sensitive data. By understanding the nature of these critical flaws and implementing robust patch management strategies, organizations can significantly reduce the risk of exploitation.
FAQ
What are path traversal vulnerabilities?
Path traversal vulnerabilities allow unauthorized access to files and directories outside the intended web root folder, potentially leading to arbitrary code execution.
How can I protect my systems from these vulnerabilities?
Apply security patches promptly, conduct regular security audits, and adopt a zero-trust architecture to minimize risk.
Why is it important to test patches before deployment?
Testing patches in a controlled environment helps identify potential issues and prevents unexpected system downtime.
How does automation help in cybersecurity?
Automation streamlines processes like patch management and threat detection, reducing the time and effort required to maintain security.
What is DevSecOps?
DevSecOps integrates security into the DevOps process, ensuring security measures are considered from the start of development, reducing vulnerabilities in production.
Key Takeaways
- Path traversal vulnerabilities can lead to full system takeover.
- Immediate patching is crucial to protect systems.
- Automation and zero-trust models enhance security.
- Testing patches in a safe environment prevents downtime.
- Regular audits help identify potential security risks.
Related Articles
- Safeguarding AI Agents: How IronCurtain Prevents Rogue Behavior [2025]
- Navigating the Complex World of Anti-Bot Systems: The OpenClaw Dilemma [2025]
- Debunking the Top Five Myths About Sovereign Cloud [2025]
- Understanding the Impact of Data Broker Breaches on Identity Theft [2025]
- Are You 'Agentic' Enough for the AI Era? [2025]
- Understanding and Mitigating the Cisco Catalyst SD-WAN Vulnerability [2025]
![Understanding and Mitigating Critical Security Flaws in Windows Systems [2025]](https://tryrunable.com/blog/understanding-and-mitigating-critical-security-flaws-in-wind/image-1-1772195681875.jpg)



