Care Cloud Data Breach: Details, Solutions, and Future Safeguards [2025]
Last month, the healthcare tech firm Care Cloud made headlines for a significant data breach. Hackers accessed sensitive patient information, raising alarms across the industry. This incident not only underscores the vulnerabilities inherent in electronic health records (EHR) systems but also highlights the urgent need for robust cybersecurity measures. In this article, we'll delve into the specifics of the breach, discuss the broader implications for the healthcare industry, and explore best practices that can safeguard sensitive data in the future.
TL; DR
- Care Cloud Hack: Exposed sensitive patient information, compromising trust, as detailed in the HIPAA Journal.
- Security Gaps: Highlighted the need for improved cybersecurity in healthcare, according to SecurityWeek.
- Proactive Measures: Regular audits, encryption, and staff training are crucial.
- Future Trends: AI and machine learning to play a pivotal role in threat detection.
- Industry Impact: Calls for stricter regulations and compliance standards.

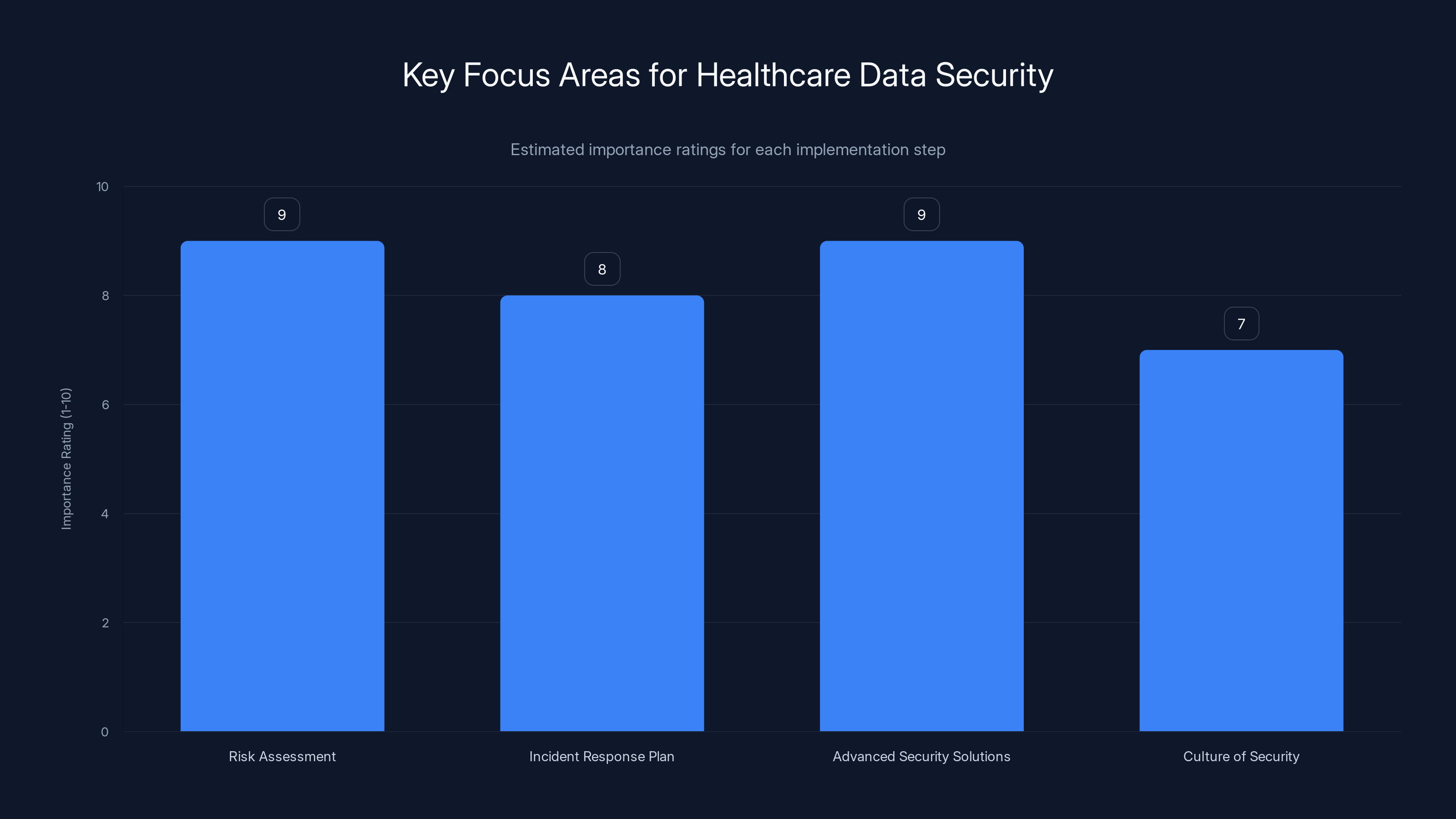
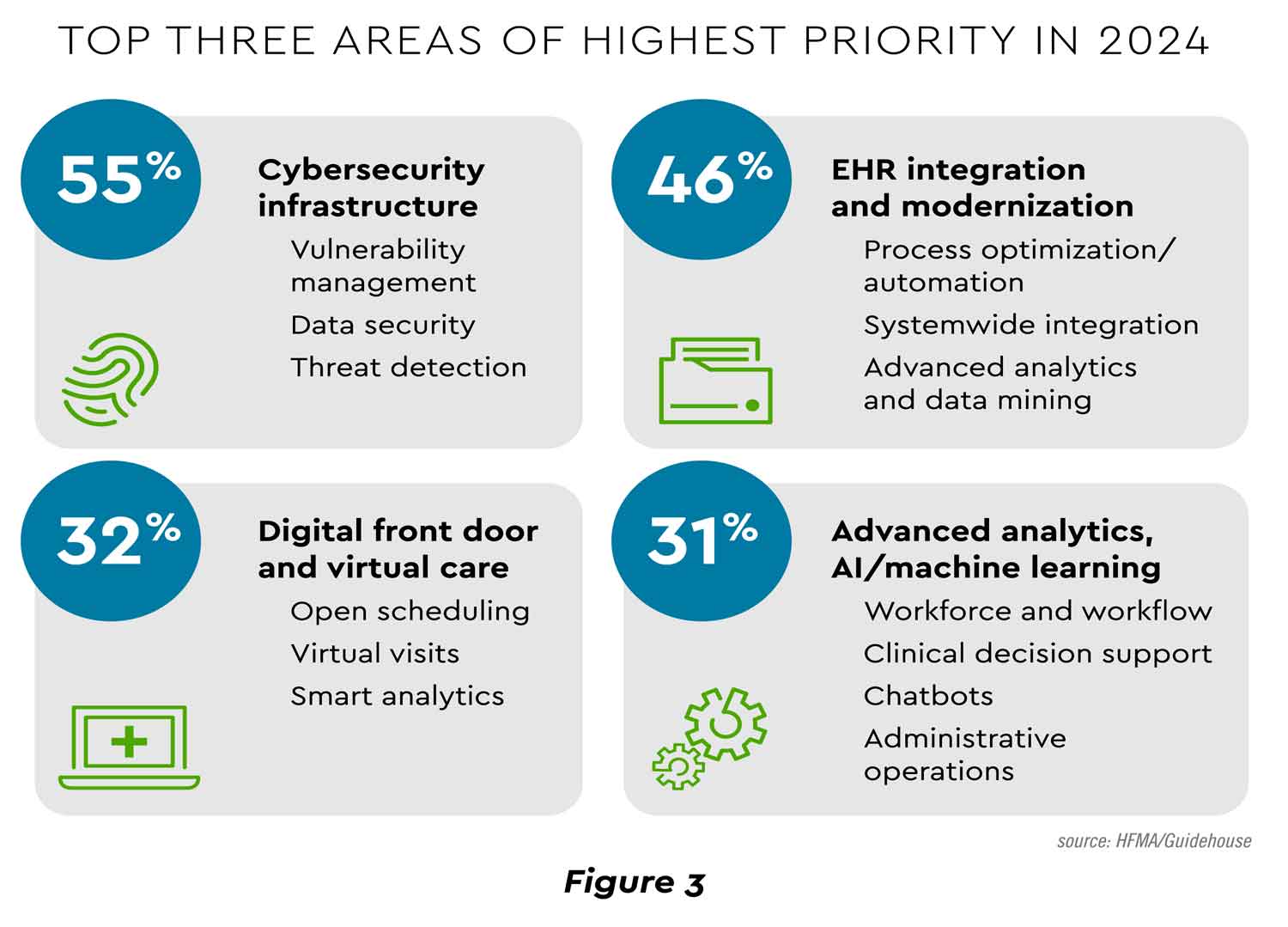
Risk assessment and investing in advanced security solutions are rated highest in importance for safeguarding patient data. (Estimated data)
Understanding the Breach
Care Cloud's recent breach affected one of its EHR environments, disrupting operations for approximately eight hours. During this period, hackers gained unauthorized access to sensitive data. While the company is still investigating the extent of the breach, initial reports suggest that patient information, including personal and medical data, may have been exposed, as reported by CyberPress.
What Went Wrong?
The breach appears to have been facilitated by a combination of factors, including outdated security protocols and insufficient monitoring of network activity. Such vulnerabilities are not uncommon in the healthcare sector, where legacy systems often coexist with newer technologies, creating potential entry points for cybercriminals, as noted in The Record.
Key Vulnerabilities Identified:
- Lack of Real-Time Monitoring: Many systems failed to detect unusual activity promptly.
- Outdated Encryption Standards: Data was not adequately protected during transmission.
- Inadequate Employee Training: Staff were not fully aware of phishing and other social engineering tactics.
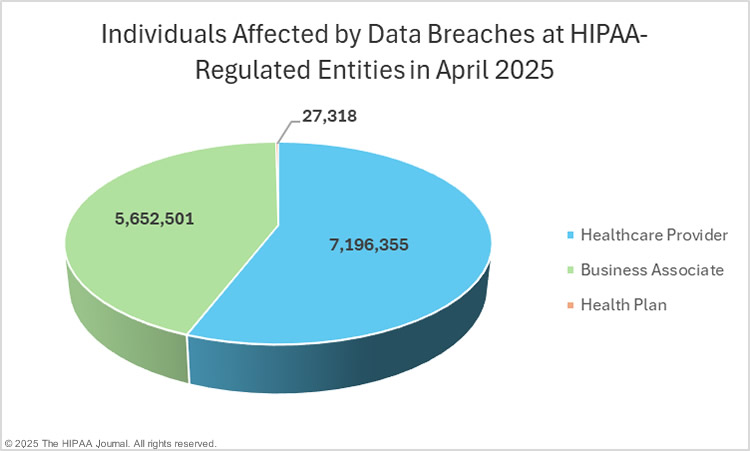
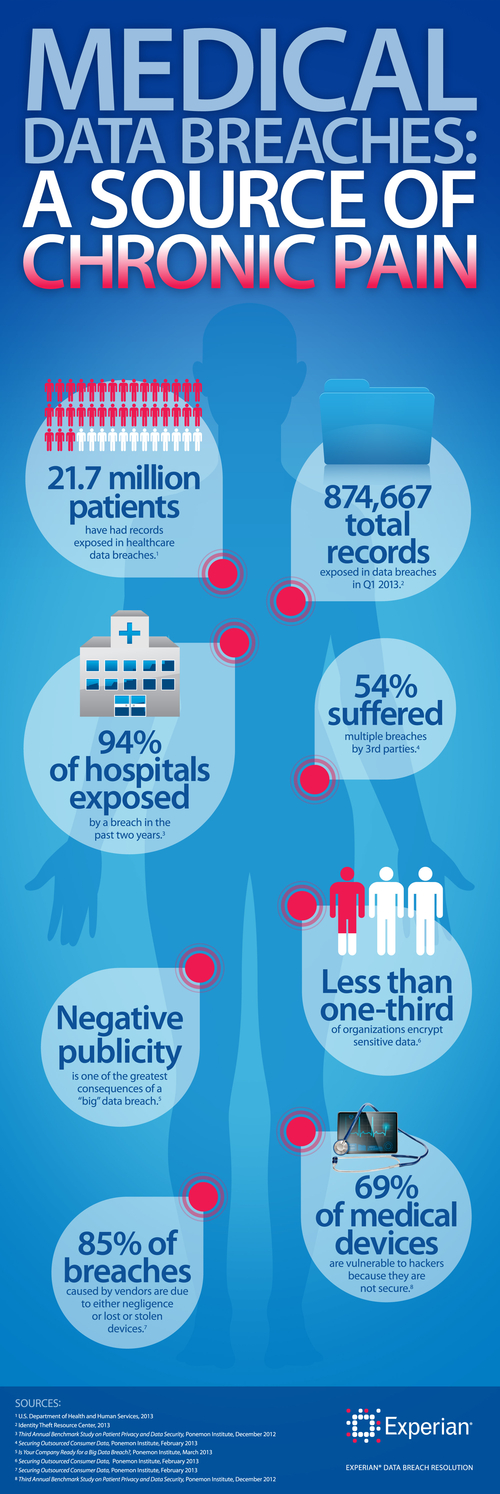
The Impact on Patients and Healthcare Providers
The consequences of data breaches in healthcare can be severe, affecting not only the privacy of millions of patients but also the operational integrity of healthcare providers. In Care Cloud's case, the breach could lead to significant financial penalties and loss of consumer trust, as highlighted by HIPAA Journal.
Patient Information at Risk
Sensitive data, such as medical histories, treatment plans, and personal identifiers, are highly sought after by cybercriminals. This information can be used for identity theft, insurance fraud, and even blackmail, according to The Register.
Operational Disruption
The eight-hour outage experienced by Care Cloud highlights the operational risks associated with data breaches. Such disruptions can delay patient care, impact clinical outcomes, and strain healthcare resources, as reported by CyberPress.

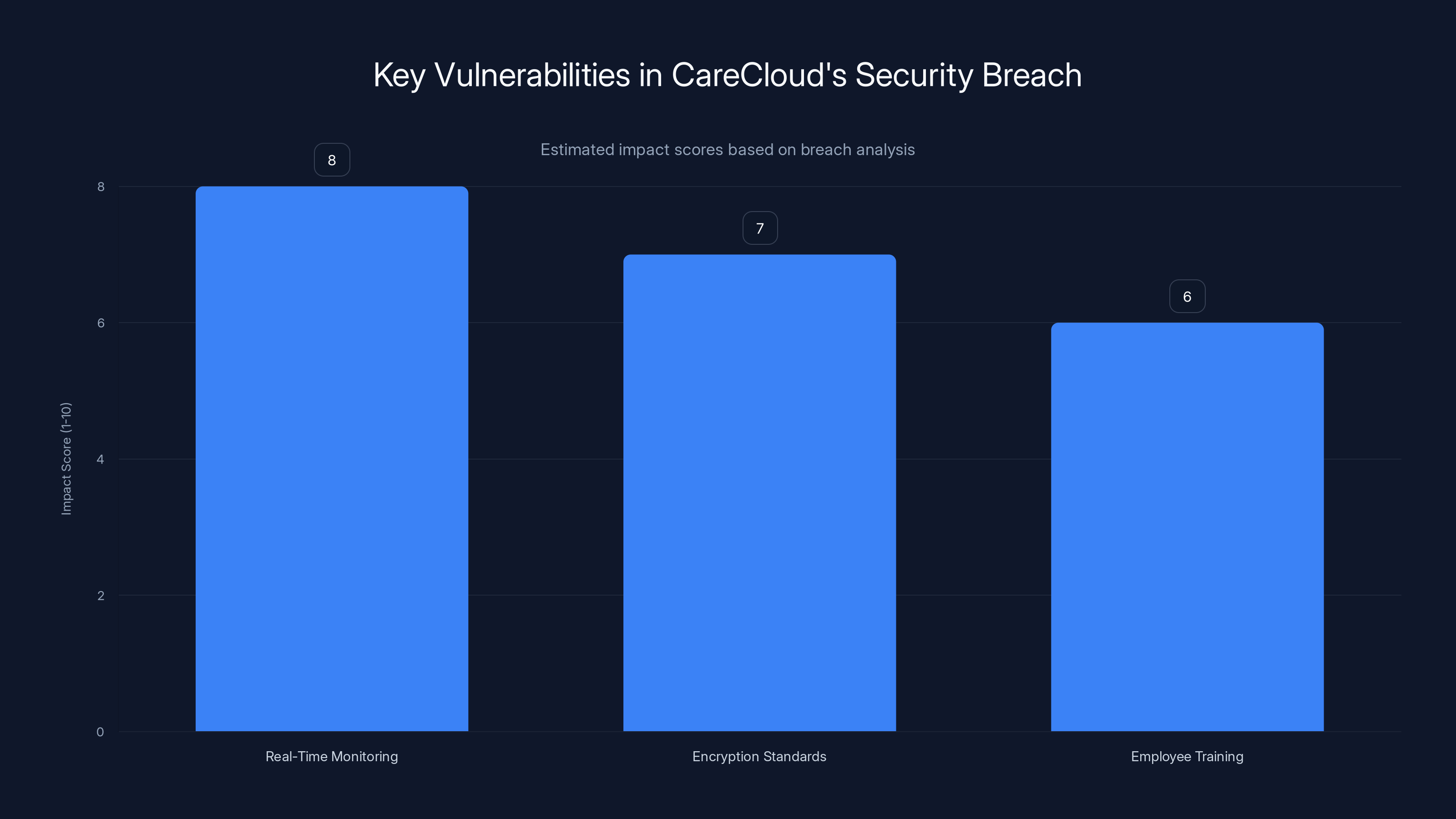
The breach was primarily due to lack of real-time monitoring, outdated encryption, and inadequate employee training. Estimated data.
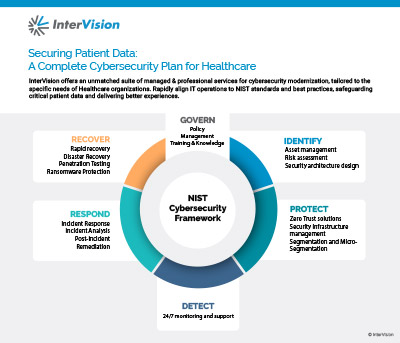
Enhancing Cybersecurity in Healthcare
Given the increasing frequency of cyberattacks, healthcare organizations must adopt a proactive approach to cybersecurity. Here are some best practices that can help mitigate risks:
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities before they are exploited. Audits should include penetration testing, vulnerability scanning, and security assessments, as recommended by South Florida Hospital News.
Advanced Encryption Techniques
Data encryption is a critical line of defense against data breaches. Healthcare organizations should implement advanced encryption standards to protect sensitive information both in transit and at rest, as advised by Oracle.
Employee Training and Awareness
Human error remains a leading cause of data breaches. Regular training sessions can help employees recognize phishing attempts and understand the importance of cybersecurity protocols, as noted by Crowell & Moring.
Implementing Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to verify their identity through multiple methods. This can significantly reduce the risk of unauthorized access, as highlighted by HIPAA Journal.
The Role of Technology in Cybersecurity
As cyber threats become more sophisticated, technology will play a crucial role in enhancing cybersecurity measures. Artificial intelligence (AI) and machine learning are particularly promising in this regard.
AI-Powered Threat Detection
AI can analyze vast amounts of data in real-time to identify patterns and anomalies that may indicate a cyberattack. Machine learning algorithms can also adapt to new threats, providing a dynamic defense strategy, as discussed in UCF News.
Blockchain for Secure Data Management
Blockchain technology can enhance data security by providing a decentralized and immutable ledger. This can prevent unauthorized data modifications and ensure data integrity, as explored in Nature.

Future Trends in Healthcare Cybersecurity
The future of healthcare cybersecurity will likely be shaped by several key trends:
Increased Regulation and Compliance Standards
Governments worldwide are likely to impose stricter regulations to protect patient data. Compliance with standards like HIPAA will become even more critical, as noted in Crowell & Moring.
Integration of Cybersecurity into Healthcare IT
Cybersecurity will become a core component of healthcare IT systems, integrated into every layer of the technology stack, as reported by South Florida Hospital News.
Collaboration Across the Industry
Healthcare organizations will increasingly collaborate to share threat intelligence and best practices, creating a united front against cyber threats, as highlighted in Cybersecurity News.
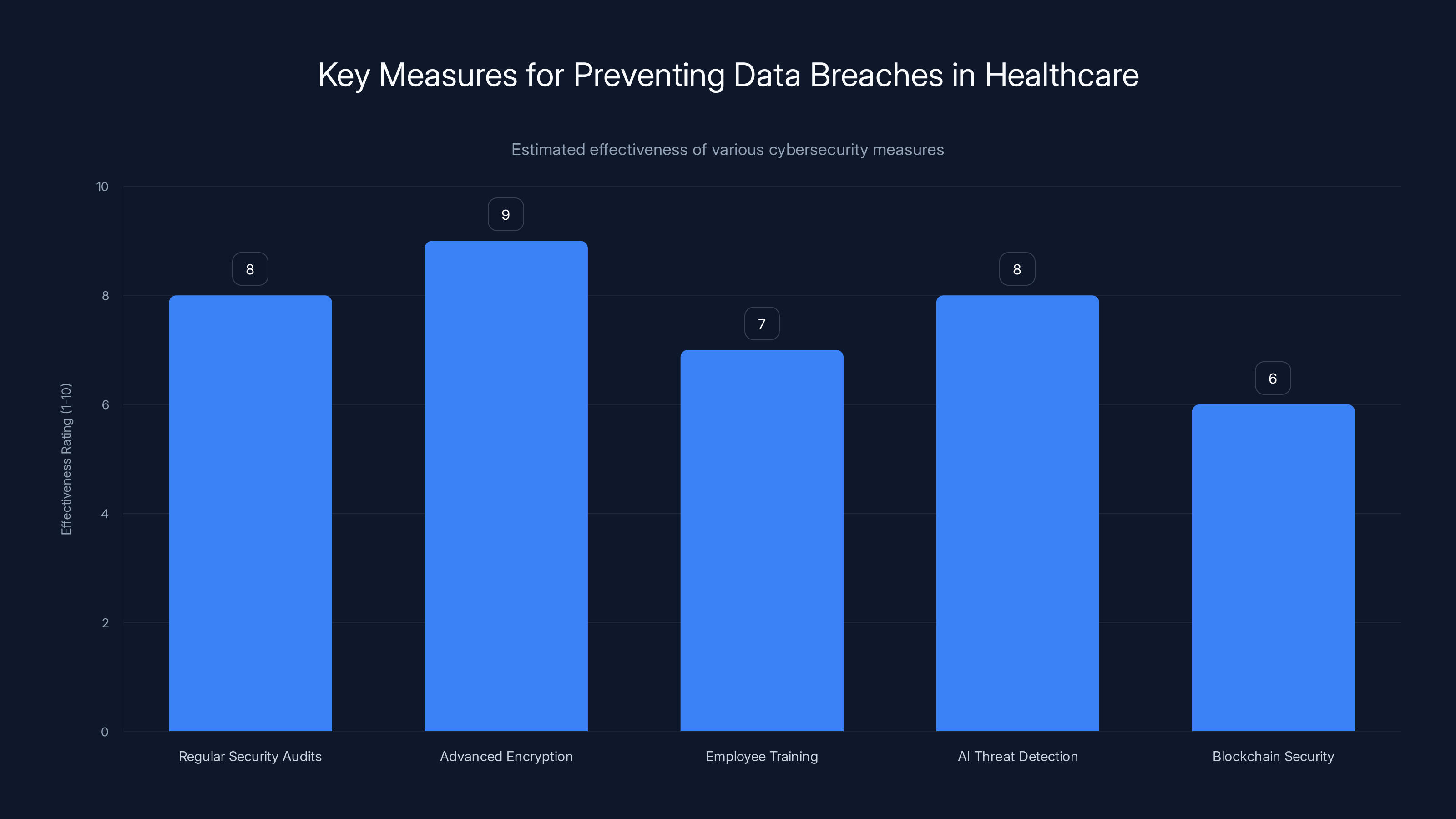
Advanced encryption and regular security audits are rated as the most effective measures for preventing data breaches in healthcare. (Estimated data)
Implementation Guide for Healthcare Providers
To effectively safeguard patient data, healthcare providers should consider the following implementation guide:
- Conduct a Comprehensive Risk Assessment: Identify and evaluate potential risks to patient data.
- Develop an Incident Response Plan: Prepare for potential breaches by outlining roles and responsibilities.
- Invest in Advanced Security Solutions: Utilize AI and machine learning to enhance threat detection.
- Foster a Culture of Security: Encourage all employees to prioritize cybersecurity in their daily operations.
Common Pitfalls and How to Avoid Them
Despite best efforts, healthcare organizations often fall prey to common cybersecurity pitfalls. Here are some strategies to avoid them:
Underestimating the Human Element
Invest in continuous training programs to keep employees informed about the latest threats.
Failing to Update Software Regularly
Regular software updates can patch vulnerabilities and protect against the latest threats.
Neglecting Third-Party Vendor Security
Ensure that all vendors comply with your organization's security standards to prevent supply chain attacks.
Looking Ahead: Preparing for the Next Wave of Cyber Threats
The cybersecurity landscape is constantly evolving, and healthcare organizations must remain vigilant to emerging threats. By adopting a proactive approach and leveraging advanced technologies, the industry can better protect patient data and maintain trust.
Conclusion
The Care Cloud data breach serves as a stark reminder of the vulnerabilities within the healthcare industry. However, by implementing robust cybersecurity measures and staying ahead of emerging threats, healthcare providers can safeguard sensitive information and ensure the privacy of their patients.
Key Takeaways
- Breaches Are Increasing: The frequency of data breaches in healthcare is on the rise.
- Proactive Measures Are Essential: Regular audits and advanced encryption are critical.
- AI and Blockchain Are Game-Changers: These technologies can revolutionize data security.
- Regulations Will Tighten: Stricter compliance standards are expected in the future.
- Collaboration Is Key: Sharing threat intelligence can strengthen defenses.
FAQ
What is a data breach in healthcare?
A data breach in healthcare involves unauthorized access to sensitive patient information, potentially compromising privacy and security.
How can healthcare providers prevent data breaches?
Preventive measures include regular security audits, advanced encryption, and employee training.
What role does AI play in healthcare cybersecurity?
AI can enhance threat detection by analyzing data patterns and identifying anomalies in real-time.
Why is encryption important in healthcare?
Encryption protects sensitive data from unauthorized access during transmission and storage.
How can blockchain improve data security?
Blockchain provides a decentralized ledger, ensuring data integrity and preventing unauthorized modifications.
What are the consequences of a data breach for patients?
Consequences can include identity theft, insurance fraud, and loss of privacy.
What should healthcare providers do after a data breach?
They should implement an incident response plan, notify affected individuals, and take steps to prevent future breaches.
Are there regulations governing healthcare cybersecurity?
Yes, regulations like HIPAA set standards for protecting patient data and ensuring compliance.
Related Articles
- Understanding Banking App Glitches: Lessons from Lloyds and Beyond [2025]
- How Fragmented Promotion Systems Are Eroding Retail Price Trust and Why Integration Alone Isn't Enough [2025]
- Solving Medicine's Data Availability Problem with Digital Twins: The Mantis Biotech Approach [2025]
- Intelligence and Trust in AI: Transforming Work with Smarter Tools [2025]
- European Commission Data Breach: What Happened and How to Respond [2025]
- Your Vape Wants to Know How Old You Are | WIRED
![CareCloud Data Breach: Details, Solutions, and Future Safeguards [2025]](https://tryrunable.com/blog/carecloud-data-breach-details-solutions-and-future-safeguard/image-1-1774975954014.jpg)



