The Hotel Check-In Security Debacle: Lessons from Tabiq's Data Exposure [2025]
Last month, an alarming security breach revealed a major vulnerability in a hotel check-in system, exposing over a million passports and driver's licenses. This incident, involving the Tabiq system developed by Japan-based Reqrea, underscores critical lessons for businesses relying on digital platforms to handle sensitive customer data.
TL; DR
- Data Breach: Tabiq left over 1 million sensitive documents publicly accessible due to a cloud storage misconfiguration.
- Key Vulnerability: The breach was due to a publicly accessible Amazon S3 bucket.
- Security Measures: Implementing proper access controls and routine audits can prevent such incidents.
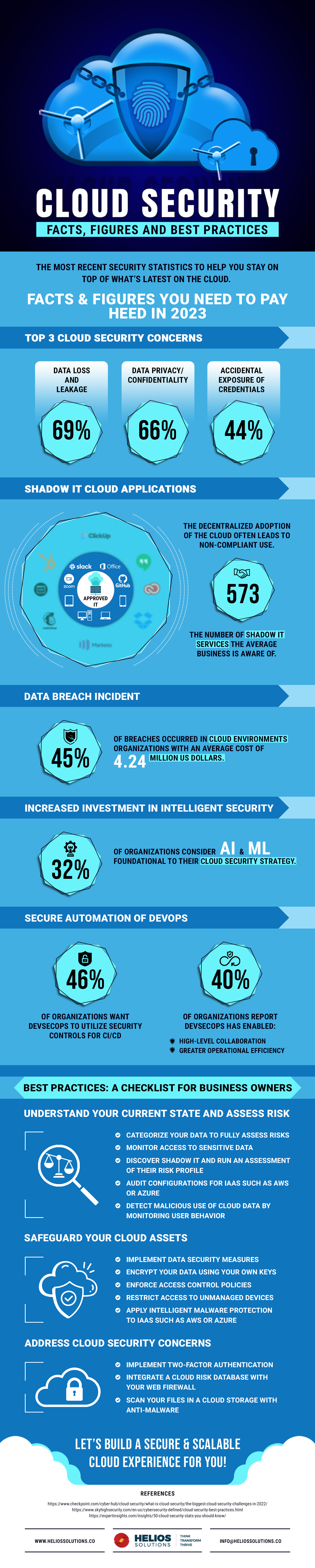
- Future Trends: Increasing reliance on AI-driven security to detect and prevent breaches.
- Industry Impact: Highlights the need for stringent data protection regulations in the hospitality sector.

Understanding the Breach
The Tabiq check-in system, used widely across hotels in Japan, exposed sensitive customer data due to a misconfiguration in their Amazon S3 bucket. This allowed anyone with internet access to view the documents without authentication, simply by knowing the bucket's name.
How It Happened
The root cause was a simple misconfiguration: setting the S3 bucket to public access. This error is surprisingly common and can occur when developers prioritize functionality over security. Here's a breakdown of how such an oversight can happen:
- Default Settings: Developers often use default settings during testing, which may allow public access.
- Lack of Knowledge: Misunderstanding of cloud security settings can lead to incorrect configurations.
- Rush to Deploy: In the race to meet deadlines, security checks are sometimes skipped.
- Insufficient Training: Teams may lack proper training on secure cloud practices.
The Role of Amazon S3
Amazon S3, a popular cloud storage solution, is both powerful and potentially dangerous if not handled correctly. By default, S3 buckets are private, but users can change this setting to allow public access, often unknowingly. Here’s a quick guide on securing S3 buckets:
- Private by Default: Ensure buckets are set to private unless public access is absolutely necessary.
- IAM Policies: Use Identity and Access Management (IAM) policies to control who can access your data.
- Bucket Policies: Define specific access conditions with bucket policies.
- Versioning and Logging: Enable these features to track changes and access attempts.
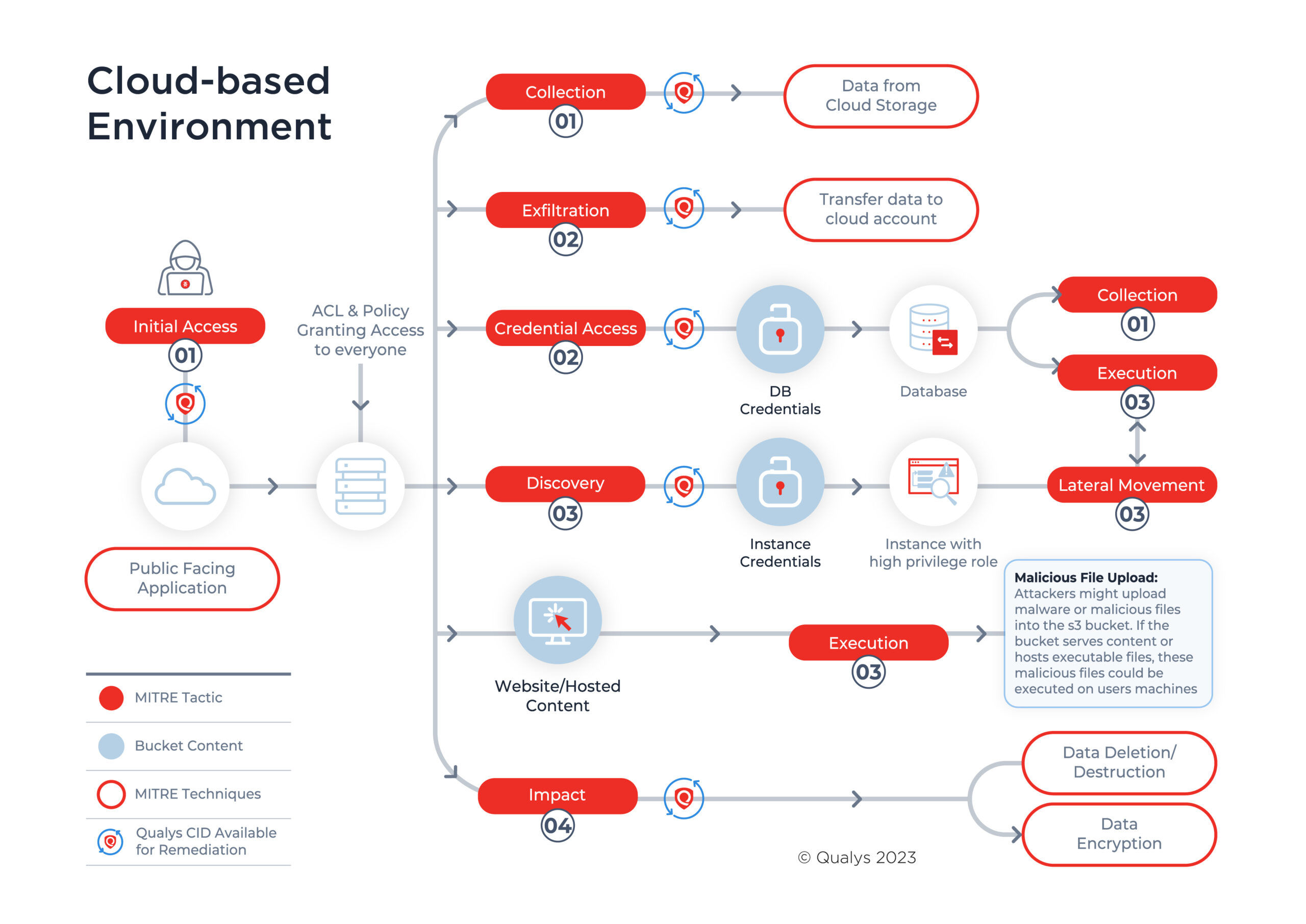
Practical Steps to Secure Data in the Cloud
Securing cloud-based systems requires a multi-layered approach. Here are best practices to prevent data exposure:
1. Implement Strong Access Controls
Access control is your first line of defense against unauthorized access. Ensure that only authenticated users can access sensitive data:
- Role-Based Access Control (RBAC): Assign permissions based on user roles, as highlighted in Oracle's guidance on RBAC.
- Multi-Factor Authentication (MFA): Add an extra layer of security.
- Least Privilege Principle: Users should have the minimum level of access necessary.
2. Regular Audits and Penetration Testing
Routine security audits and penetration tests can identify vulnerabilities before they are exploited.
- Automated Scans: Use tools to regularly scan for misconfigurations.
- Penetration Testing: Simulate attacks to test your defenses.
- Third-Party Reviews: External audits provide an unbiased assessment.
3. Continuous Monitoring
Implement a system to continuously monitor access and changes to your cloud resources:
- Cloud Trail and Cloud Watch: Use these AWS tools to track activity and set alerts for suspicious behavior, as recommended in AWS's security blog.
- Anomaly Detection: AI can help identify unusual patterns indicative of a breach.
4. Data Encryption
Encrypt sensitive data both in transit and at rest to add another layer of security. Use industry-standard encryption protocols to protect data from unauthorized access.
Common Pitfalls in Cloud Security
Even with robust security measures in place, pitfalls can lead to vulnerabilities. Here are common pitfalls and how to avoid them:
- Misconfigurations: Regularly review your configurations to ensure they comply with security policies.
- Human Error: Implement automated tools to minimize the impact of human errors.
- Neglecting Updates: Keep your systems and software up to date with the latest security patches.
- Assuming Compliance Equals Security: Compliance standards are a baseline; going beyond them is essential for security.

Future Trends in Data Security
As data breaches become more sophisticated, so too must our defenses. Here are some trends shaping the future of data security:
AI-Driven Security
Artificial Intelligence (AI) is playing an increasingly vital role in detecting and preventing security threats.
- Behavioral Analytics: AI can analyze user behavior to detect anomalies indicative of a breach.
- Threat Intelligence: Machine learning models can predict and mitigate threats before they occur.
Zero Trust Architecture
The zero trust model assumes that threats could be both external and internal and requires strict identity verification for every person and device trying to access resources on a private network.
- Microsegmentation: Divide networks into small segments, each requiring independent access.
- Identity Verification: Continuous verification to ensure only authorized users access data.
Enhanced Regulatory Frameworks
As breaches like Tabiq's become more prevalent, governments are likely to implement stricter regulations on data protection.
- GDPR and Beyond: Expect more regions to adopt GDPR-like regulations.
- Industry-Specific Standards: Tailored regulations for industries handling sensitive data, such as hospitality.

Recommendations for the Hospitality Industry
The hospitality industry, handling vast amounts of customer data, must prioritize security. Here are some specific recommendations:
- Comprehensive Training: Regularly train staff on data security best practices.
- Data Minimization: Only collect and retain data that is absolutely necessary.
- Secure Vendor Management: Ensure third-party vendors adhere to your security standards.
Conclusion
The Tabiq data exposure incident serves as a stark reminder of the importance of cloud security. By implementing robust security measures, staying informed about emerging threats, and preparing for future trends, businesses can protect themselves and their customers from data breaches.

FAQ
What caused the Tabiq data breach?
The breach was caused by a misconfiguration of an Amazon S3 bucket, which was set to allow public access, exposing sensitive customer documents.
How can I secure my cloud-based systems?
Implement strong access controls, conduct regular audits, use continuous monitoring, and encrypt data both in transit and at rest.
What are the common pitfalls in cloud security?
Common pitfalls include misconfigurations, human error, neglecting updates, and assuming compliance equals security.
How is AI being used in data security?
AI is used for behavioral analytics, threat intelligence, and anomaly detection to predict and prevent security threats.
What is zero trust architecture?
Zero trust architecture requires strict identity verification for every person and device accessing resources, assuming threats could be internal or external.
How should the hospitality industry manage data security?
The industry should focus on comprehensive training, data minimization, and secure vendor management to protect customer data.
What future trends should we expect in data security?
Expect AI-driven security, zero trust architecture, and enhanced regulatory frameworks to become more prevalent in the fight against data breaches.
Key Takeaways
- Over 1 million sensitive documents were exposed due to a cloud storage misconfiguration.
- Strong access controls and regular audits are essential for data security.
- AI and zero trust models are critical for future cybersecurity measures.
- The hospitality industry must prioritize data protection through comprehensive training and secure vendor management.
- Expect stricter regulations and enhanced frameworks for data security compliance.
Related Articles
- Understanding the Mistral AI Breach: Implications for AI Security in 2025
- How Cell Phones Lead to Self-Incrimination: A Deep Dive [2025]
- Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]
- Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
- Confidentiality is Not Security: Bridging the Authorization Gap in AI [2025]
![The Hotel Check-In Security Debacle: Lessons from Tabiq's Data Exposure [2025]](https://tryrunable.com/blog/the-hotel-check-in-security-debacle-lessons-from-tabiq-s-dat/image-1-1778871882185.jpg)



