European Commission Data Breach: What Happened and How to Respond [2025]
In today's interconnected world, data breaches are becoming alarmingly common. Recently, the European Commission fell victim to a significant cyberattack, resulting in the unauthorized extraction of approximately 350GB of sensitive data. This incident has raised concerns about cybersecurity measures and data protection protocols across public sector bodies and beyond.
TL; DR
- Data Breach Incident: Attackers extracted 350GB of data from the European Commission's AWS-hosted infrastructure.
- Vulnerability Exploitation: Likely exploited weak access controls and insufficient monitoring.
- Immediate Response: Prompt notification to authorities and public acknowledgment.
- Long-term Strategies: Emphasizes the need for robust encryption and continuous security assessments.
- Future Trends: Increasing reliance on AI-driven security solutions to preemptively identify threats.

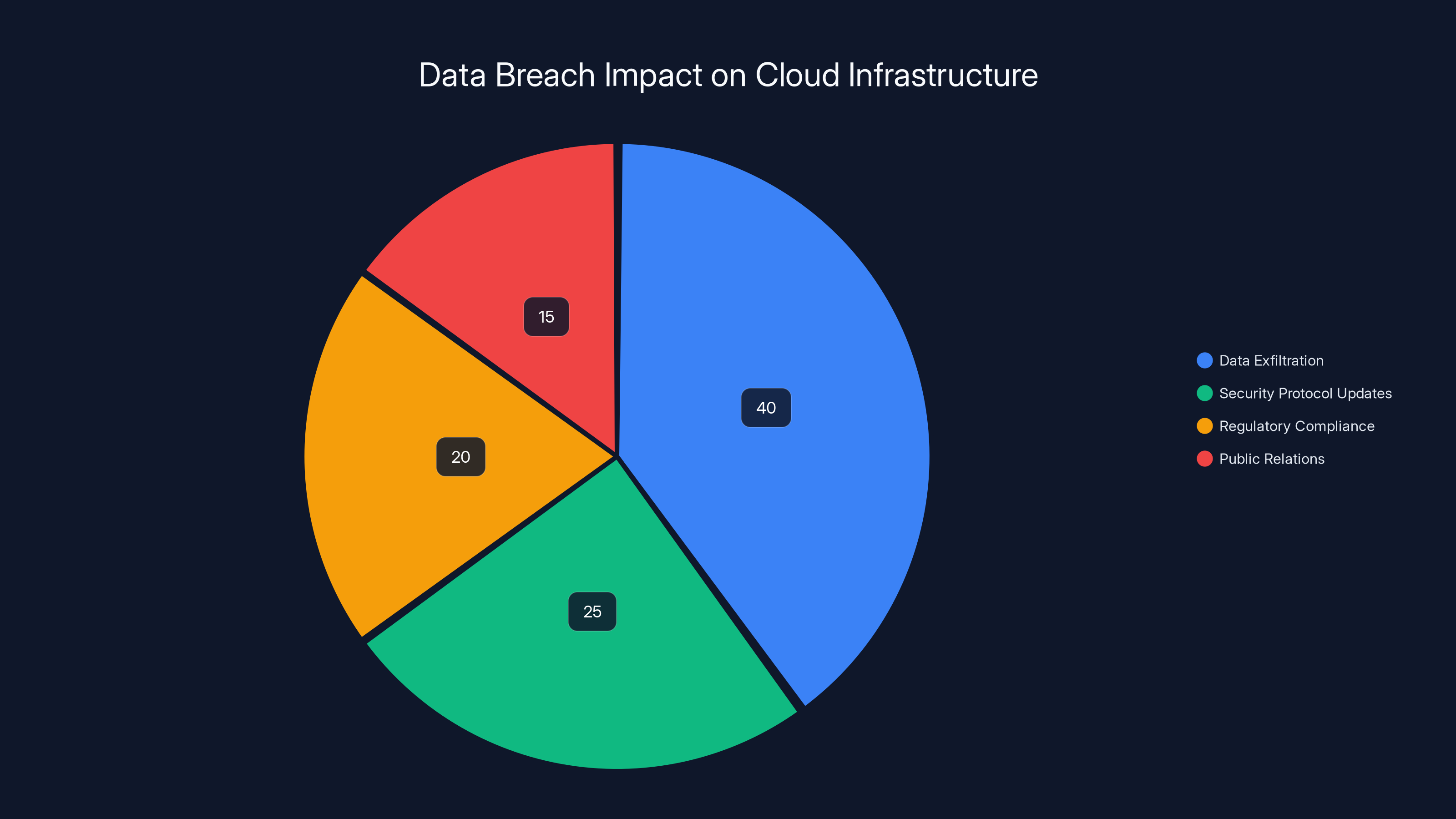
Estimated data shows that data exfiltration is the most significant consequence of the breach, followed by necessary updates to security protocols. Estimated data.
What Happened?
The European Commission recently confirmed a significant breach of its data infrastructure hosted on Amazon Web Services (AWS). Unnamed attackers reportedly exfiltrated approximately 350GB of sensitive organizational data. This breach underscores the vulnerabilities inherent in cloud-based infrastructures and the pressing need for enhanced security measures.
Initial Discovery
The breach was discovered during routine security audits when anomalies in data traffic and unauthorized access attempts were detected. These audits, essential for maintaining cybersecurity hygiene, serve as the first line of defense against potential breaches.
Response and Notification
Upon discovery, the European Commission promptly notified relevant authorities, adhering to the GDPR's breach notification requirements. Public acknowledgment of the breach followed, demonstrating transparency and commitment to addressing the issue.

The corporation saw an estimated 80% reduction in security incidents after implementing enhanced encryption, increased monitoring, and comprehensive training. (Estimated data)
Technical Breakdown of the Breach
Understanding how the breach occurred is crucial for preventing future incidents. While specific technical details remain undisclosed, several factors likely contributed to this incident.
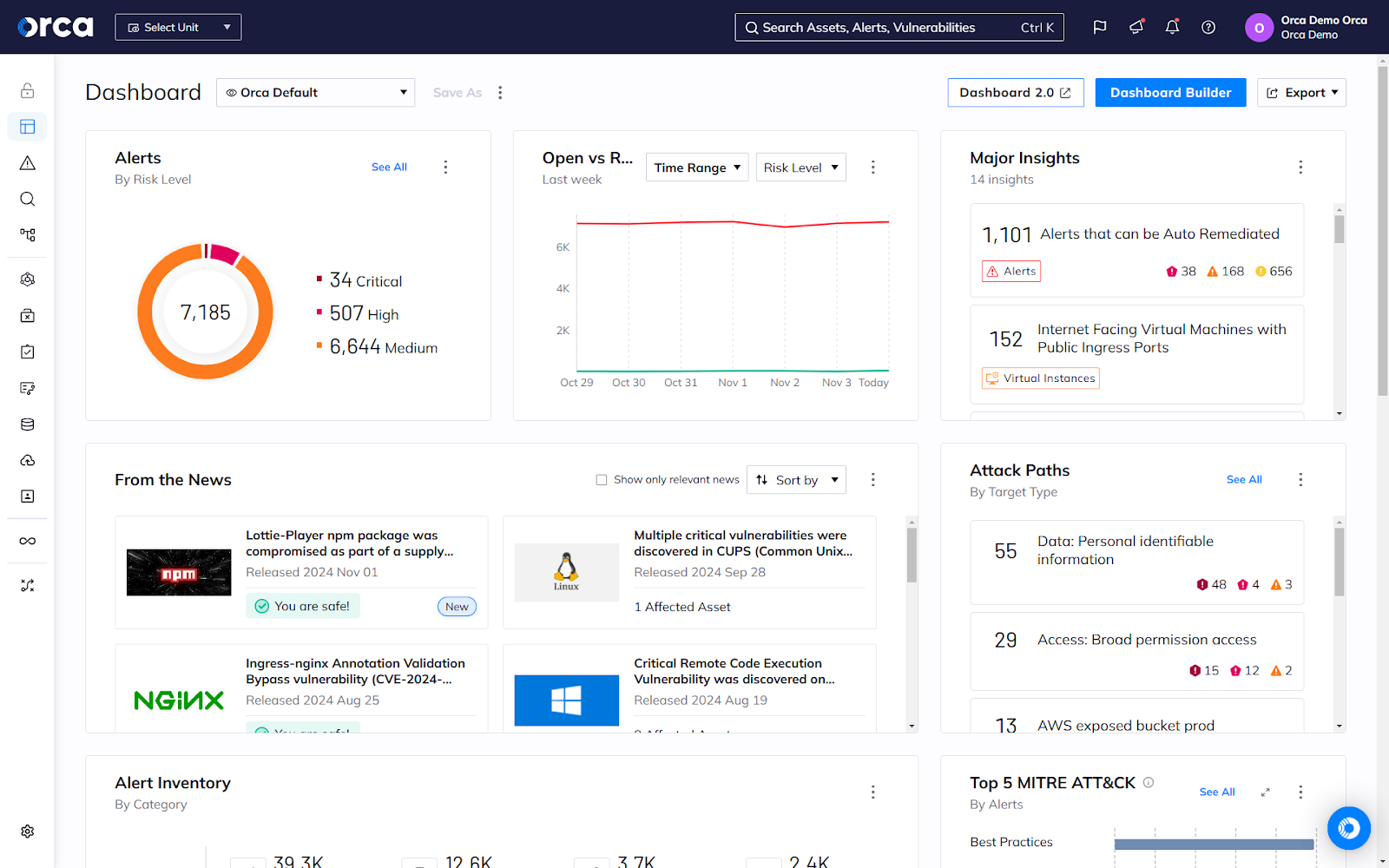
Exploiting AWS Vulnerabilities
AWS provides robust security features, but misconfigurations can expose vulnerabilities. In this case, inadequate access controls and insufficient monitoring might have been exploited.
Key Vulnerabilities
- Misconfigured Permissions: Users often over-provision access rights, granting more privileges than necessary.
- Insufficient Monitoring: Lack of real-time threat detection can allow breaches to go unnoticed for extended periods.
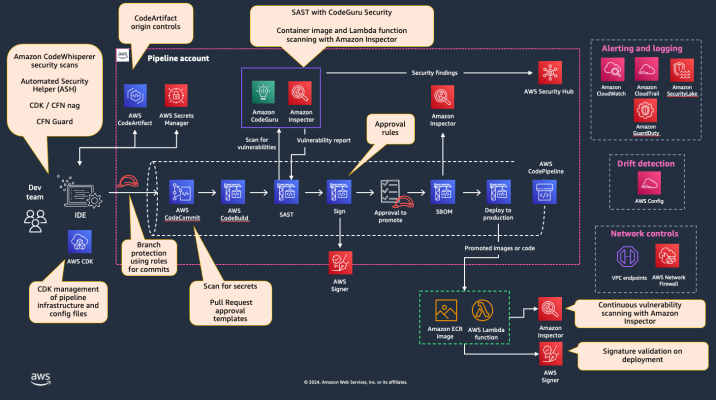
markdown**Best Practices for AWS Security**
1. **Implement Least Privilege Access**: Limit permissions to only those necessary for specific roles.
2. **Enable Multi-Factor Authentication (MFA)**: Strengthen user authentication processes.
3. **Conduct Regular Audits**: Use tools like AWS Cloud Trail to monitor account activity.
4. **Automate Security Checks**: Utilize AWS Config to enforce security compliance.
Immediate and Long-term Response Strategies
Addressing a breach involves both immediate actions and long-term strategies to mitigate future risks.
Immediate Actions
- Contain the Breach: Isolate affected systems to prevent further data loss.
- Assess Impact: Determine the scope and nature of the compromised data.
- Notify Stakeholders: Inform affected parties and regulatory bodies promptly.
Long-term Mitigation Strategies
- Enhance Encryption Protocols: Ensure all sensitive data is encrypted both at rest and in transit.
- Conduct Security Awareness Training: Educate employees about phishing and social engineering attacks.
- Adopt Zero Trust Architecture: Implement a security model that assumes potential threats inside and outside the network.
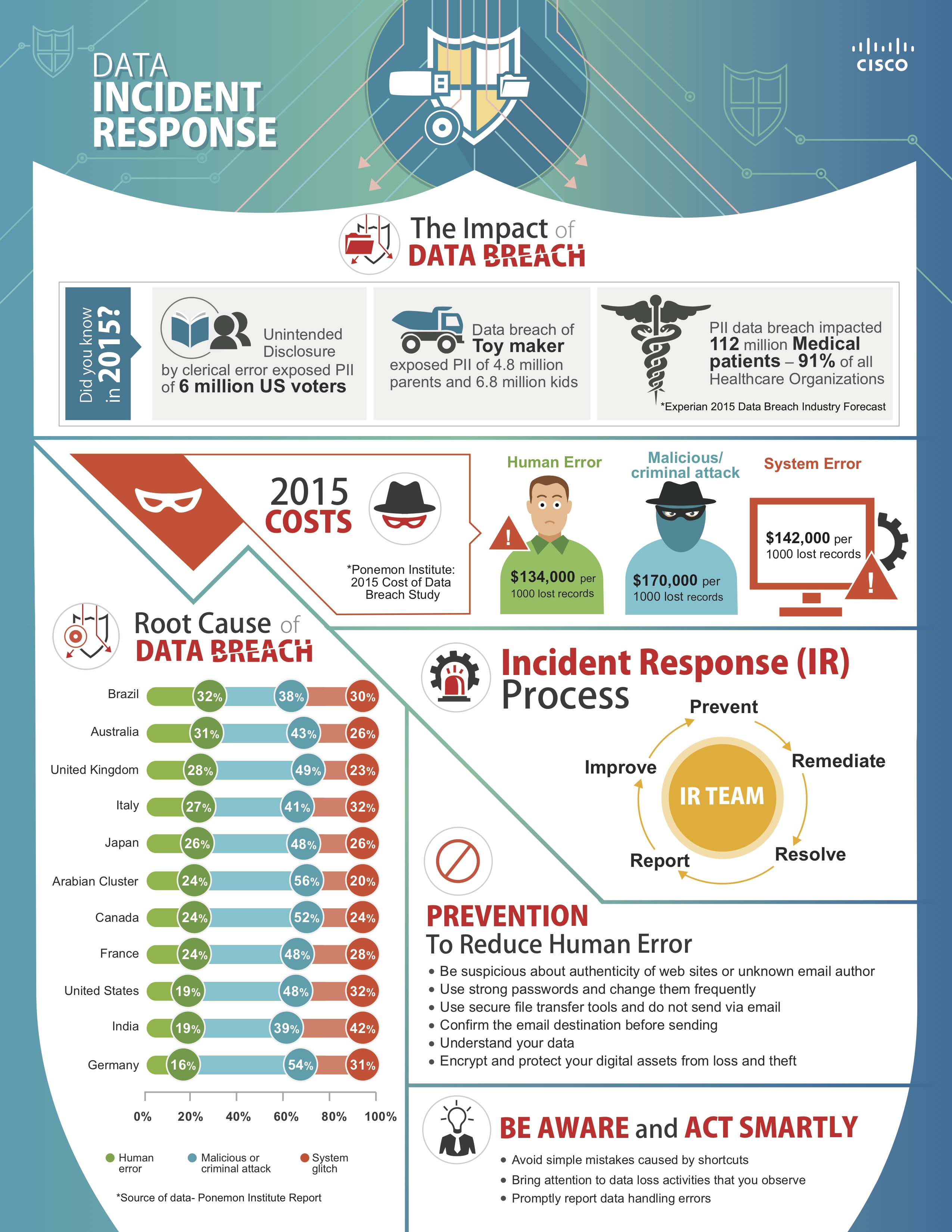

Phishing attacks are estimated to account for 40% of data breaches, making them the most common cause. Estimated data.
Future Trends in Cybersecurity
The landscape of cybersecurity is continually evolving, driven by technological advancements and emerging threats.
AI-Driven Threat Detection
Artificial Intelligence (AI) is revolutionizing cybersecurity by providing predictive analytics that can identify potential threats before they materialize. AI systems analyze vast amounts of data to detect anomalous patterns indicative of cyber threats.
Increased Regulation and Compliance
Following high-profile breaches like this one, regulatory bodies worldwide are likely to strengthen data protection laws, necessitating stricter compliance from organizations.

Common Pitfalls and Solutions
Organizations often fall into common traps that can lead to security breaches. Here are some pitfalls and how to avoid them.
Overlooking Insider Threats
Insider threats, whether malicious or accidental, pose a significant risk. Regular audits and monitoring are essential to mitigate this.
Neglecting Software Updates
Unpatched software can be a gateway for attackers. Implement an automated patch management system to keep software up-to-date.
Inadequate Incident Response Plan
Many organizations lack a comprehensive incident response plan. Develop and regularly test your response strategies to ensure readiness.
Practical Implementation Guides
Step-by-Step Guide to Enhancing Security
- Perform a Security Audit: Identify existing vulnerabilities.
- Implement MFA Across All Services: Strengthen authentication.
- Encrypt Sensitive Data: Use industry-standard encryption algorithms.
- Regularly Update Security Policies: Adapt to new threats and technologies.
- Conduct Employee Training: Ensure all staff are aware of security best practices.
Case Study: Successful Breach Mitigation
Consider a similar scenario faced by a multinational corporation (anonymized for confidentiality). After experiencing a breach, they implemented a series of strategic changes:
- Enhanced Encryption: Migrated to a more secure encryption protocol, reducing the risk of data interception.
- Increased Monitoring: Deployed advanced monitoring tools that provided real-time alerts for suspicious activity.
- Comprehensive Training: Instituted regular security training sessions for all employees, emphasizing the importance of vigilance.
As a result, they experienced a significant reduction in security incidents and improved their overall security posture.
Future Recommendations
To safeguard against future breaches, organizations should consider the following recommendations:
- Invest in AI-Powered Security Tools: These tools can provide early detection and response capabilities.
- Adopt a Culture of Security: Encourage all employees to prioritize security in their daily activities.
- Regularly Update Security Infrastructure: Stay ahead of emerging threats by updating technologies and protocols.
Conclusion
The European Commission's data breach serves as a stark reminder of the ever-present threat of cyberattacks. By implementing robust security measures and fostering a culture of vigilance, organizations can significantly reduce their risk of falling victim to similar incidents. As technology continues to evolve, so too must our strategies for protecting sensitive data.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals gain access to sensitive data, often with malicious intent.
How does a data breach impact organizations?
Breaches can lead to financial losses, reputational damage, and legal consequences.
What are common causes of data breaches?
Misconfigurations, phishing attacks, and insider threats are among the most common causes.
How can organizations prevent data breaches?
Implementing strong security protocols, conducting regular audits, and educating employees are key prevention strategies.
What role does GDPR play in data breaches?
GDPR mandates that organizations report breaches within 72 hours and imposes strict penalties for non-compliance.
How does AI enhance cybersecurity?
AI can analyze large datasets to identify potential threats, providing early warning and response capabilities.
What is the Zero Trust model?
Zero Trust is a security framework that requires all users to be authenticated and authorized before accessing resources.
Why is encryption important?
Encryption protects data by making it unreadable to unauthorized users, ensuring confidentiality.

Key Takeaways
- Data breaches demand immediate containment and assessment.
- Encryption and MFA are baseline security measures.
- AI-driven tools are critical for preemptive threat detection.
- GDPR compliance is essential for breach management.
- Zero Trust models enhance security by assuming threats exist inside and outside the network.
Related Articles
- Understanding Cybersecurity in the EU: Lessons from the European Commission Cyberattack [2025]
- European Commission Confirms Data Breach: Analysis and Implications [2025]
- Why October 1, 2026, Could Be the Day SSL/TLS Certificates 'Break the Internet' [2025]
- Iranian Hackers Breached Kash Patel’s Email—but Not the FBI’s | WIRED
- Mastering Data Protection: A Comprehensive Guide to Acronis True Image [2025]
- Understanding the Risks: Are American VPN Users Facing 'Warrantless' Government Surveillance? [2025]
![European Commission Data Breach: What Happened and How to Respond [2025]](https://tryrunable.com/blog/european-commission-data-breach-what-happened-and-how-to-res/image-1-1774866844687.jpg)



