Citrix Net Scaler Flaw: CISA's Patch Warning and What It Means [2025]
Citrix Net Scaler is a critical component in many enterprise networks, providing essential application delivery, load balancing, and secure remote access. However, a recent vulnerability has come to light, prompting the Cybersecurity and Infrastructure Security Agency (CISA) to issue an urgent patch warning for this flaw. This article delves into the details of the vulnerability, its potential impact, and how organizations can safeguard their systems.
TL; DR
- Critical Flaw Identified: A vulnerability in Citrix Net Scaler threatens enterprise security, requiring immediate attention.
- CISA's Role: CISA has mandated a patch for Federal Civilian Executive Branch (FCEB) agencies, highlighting the flaw's severity.
- Technical Details: The vulnerability, CVE-2026-3055, involves input validation issues which could lead to system compromise.
- Immediate Actions Required: Organizations must patch systems promptly and review security protocols.
- Future Security Trends: Emphasis on proactive vulnerability management and real-time threat intelligence.
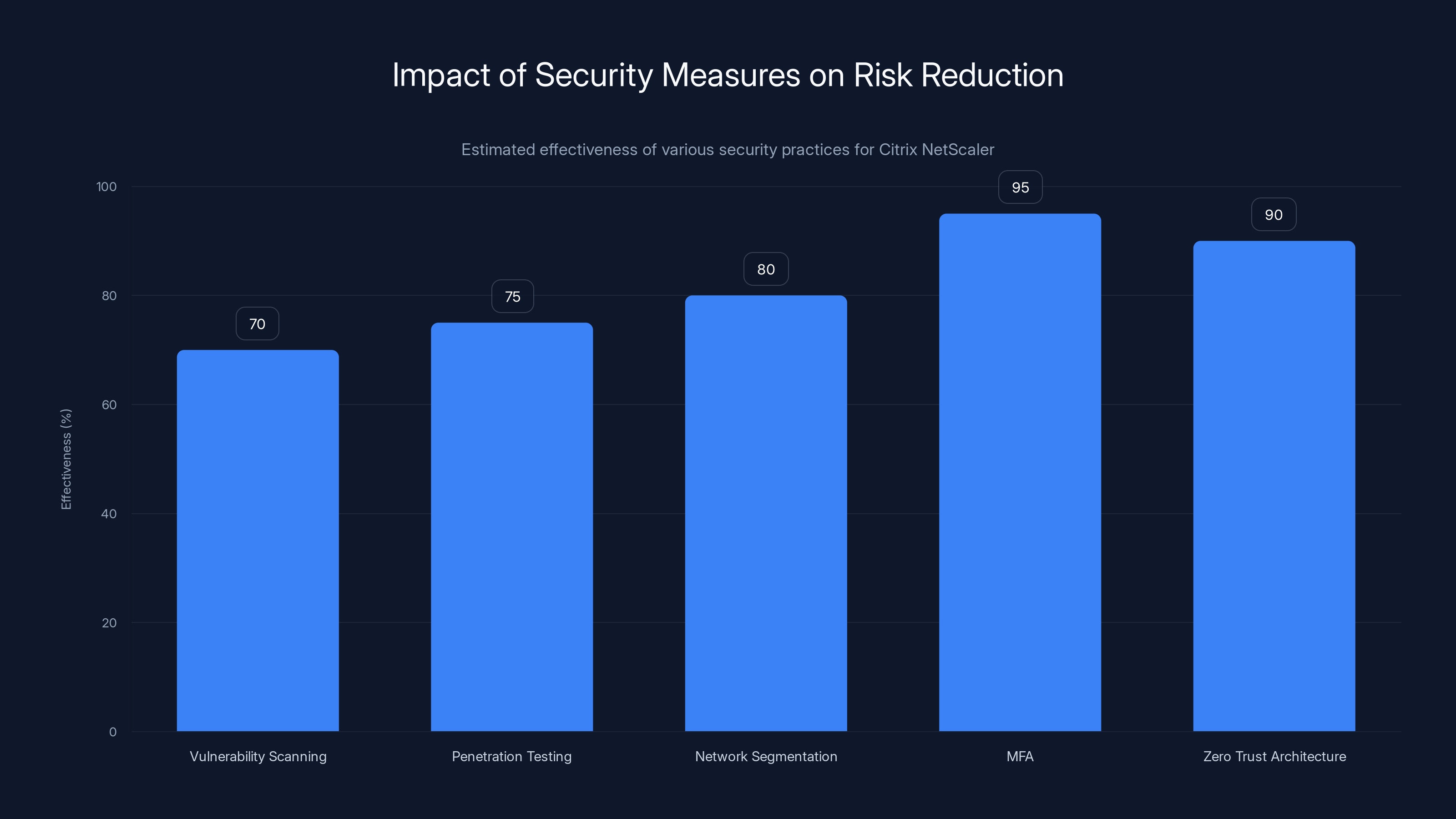
Implementing Multi-Factor Authentication (MFA) and Zero Trust Architecture are highly effective, reducing risks by up to 95% and 90% respectively. Estimated data.
Understanding the Citrix Net Scaler Vulnerability
Citrix Net Scaler, known for its robust capabilities in load balancing and secure application delivery, has been a staple in enterprise infrastructures. Recently, a critical input validation flaw, identified as CVE-2026-3055, was discovered. This flaw involves the Security Assertion Markup Language (SAML) Identity Provider (IDP) within Net Scaler ADC and Gateway systems.
The vulnerability could allow attackers to bypass authentication mechanisms, leading to unauthorized access to sensitive data and systems. Given the potential for widespread exploitation, CISA's addition of this flaw to its Known Exploited Vulnerabilities catalog underscores the urgency of addressing the issue.
How the Vulnerability Works
At its core, CVE-2026-3055 is an input validation flaw. In practical terms, this means the system fails to adequately verify the data input at certain stages of its SAML IDP processes. This oversight can be exploited by attackers to inject malicious data, potentially granting them unauthorized access or control over affected systems.
Example Scenario
Consider a scenario where an enterprise relies on Citrix Net Scaler for managing remote worker access. An attacker, aware of this vulnerability, crafts a malicious SAML assertion that exploits the input validation flaw. Without proper checks in place, Net Scaler accepts the assertion, allowing the attacker to access internal systems as a legitimate user, leading to potential data breaches.
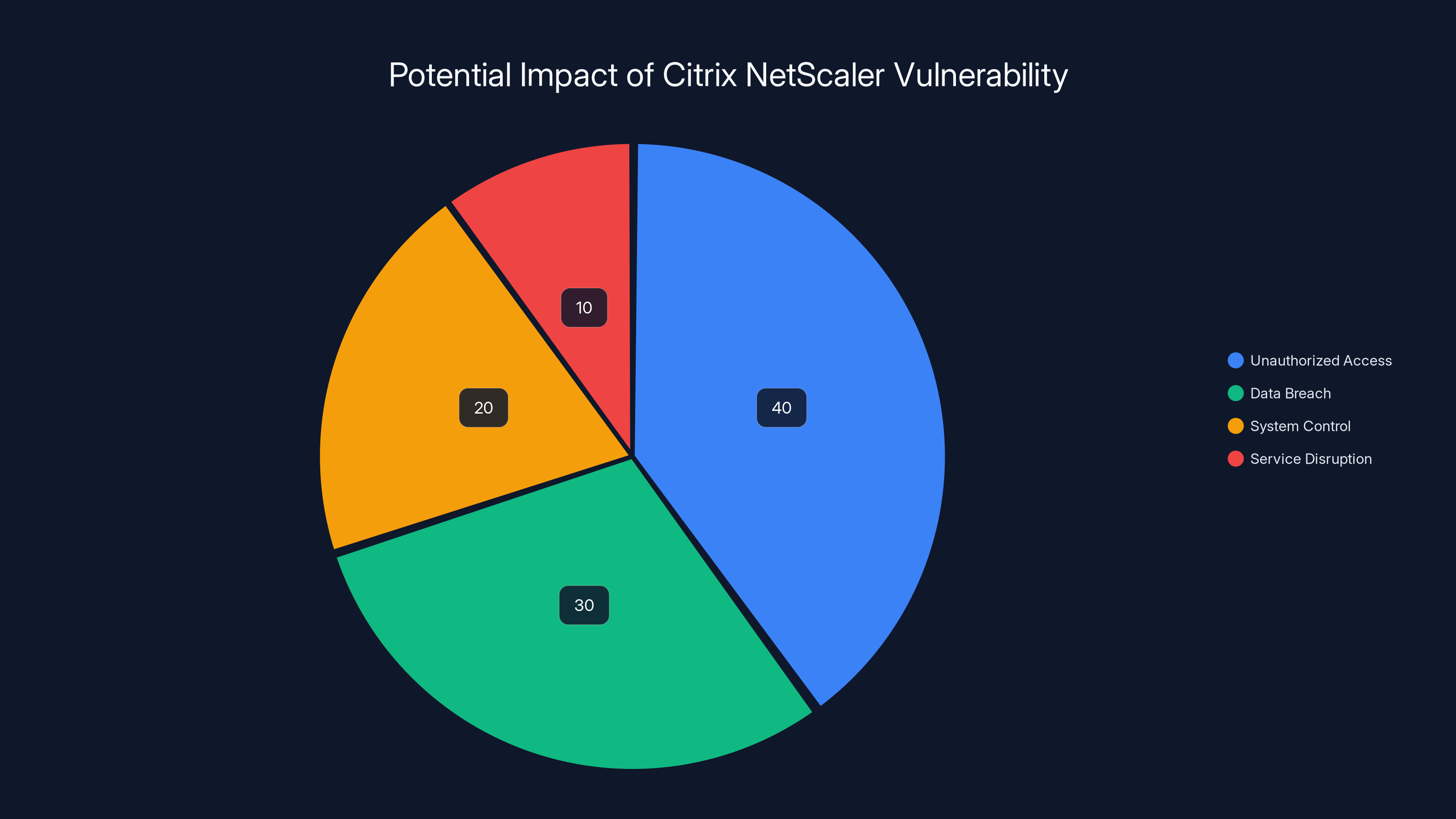
The Citrix NetScaler vulnerability primarily risks unauthorized access (40%) and data breaches (30%), with lesser impacts on system control (20%) and service disruption (10%). Estimated data.
CISA's Involvement and Recommendations
The Cybersecurity and Infrastructure Security Agency (CISA) plays a pivotal role in alerting and guiding organizations on cybersecurity threats. Upon discovering the Citrix Net Scaler vulnerability, CISA promptly issued a directive mandating all Federal Civilian Executive Branch agencies to apply patches by a specific deadline.
The Importance of CISA's Directive
CISA's directive serves as a critical reminder of the necessity for timely patch management. In the fast-evolving landscape of cybersecurity threats, delays in addressing vulnerabilities can lead to significant security breaches, especially in systems as integral as Citrix Net Scaler.

Technical Breakdown: CVE-2026-3055
To effectively mitigate the risks associated with CVE-2026-3055, it's essential to understand the technical specifics of the vulnerability. The flaw lies in the SAML IDP function within Net Scaler, where input data is not sufficiently validated.
Technical Details
- Component Affected: Net Scaler ADC and Gateway's SAML IDP
- Nature of Flaw: Input validation
- Potential Impact: Unauthorized access, data breaches
- Remediation Steps: Apply patches, enhance input validation checks
Implementing the Patch
Applying the patch provided by Citrix is the first step in remediation. Organizations should follow these steps:
- Assess the Environment: Identify all systems running Net Scaler ADC and Gateway.
- Schedule Downtime: Plan for a maintenance window to apply patches without disrupting business operations.
- Apply Patches: Follow Citrix's guidelines to update systems.
- Verify Changes: Conduct post-patch testing to ensure systems function correctly.
- Review Security Policies: Reinforce security protocols and conduct regular audits.
The potential impact of CVE-2026-3055 is high, with unauthorized access and data breaches rated at 4 and 5 respectively. Applying patches is a top priority (rated 5). Estimated data.
Best Practices for Securing Citrix Net Scaler
Securing Citrix Net Scaler goes beyond applying patches. Organizations should adopt a multi-layered security strategy to mitigate the risks of future vulnerabilities.
Regular Security Audits
Conducting regular security audits helps identify potential weaknesses in your systems. These audits should include:
- Vulnerability Scanning: Regularly scan for known vulnerabilities and misconfigurations.
- Penetration Testing: Simulate attack scenarios to test system defenses.
- Configuration Reviews: Ensure systems are configured according to best security practices.
Implementing Network Segmentation
Network segmentation is a crucial security measure that involves dividing a network into smaller, more manageable segments. This strategy limits the movement of attackers within the network, reducing the impact of a potential breach.
Enhancing Authentication Mechanisms
Given the nature of the CVE-2026-3055 vulnerability, strengthening authentication mechanisms is vital. Consider implementing:
- Multi-Factor Authentication (MFA): Add an extra layer of security beyond just passwords.
- Zero Trust Architecture: Continuously verify user permissions and device integrity before granting access.
Common Pitfalls and Their Solutions
While patching and securing systems, organizations often encounter common pitfalls. Understanding these can help avoid them in the future.
Pitfall 1: Delayed Patch Implementation
Solution: Develop a streamlined patch management process that prioritizes critical vulnerabilities. Use automated tools to apply patches quickly and efficiently.
Pitfall 2: Inadequate Testing Post-Patch
Solution: Implement thorough testing protocols to verify that patches do not disrupt system functionality. Engage in both automated and manual testing.
Pitfall 3: Neglecting User Education
Solution: Conduct regular training sessions to educate users about security best practices and the importance of timely updates.
Future Trends in Cybersecurity
As cybersecurity threats evolve, so too must the strategies to combat them. Here are some future trends to watch:
Proactive Threat Intelligence
Organizations will increasingly rely on real-time threat intelligence to stay ahead of potential vulnerabilities. This involves:
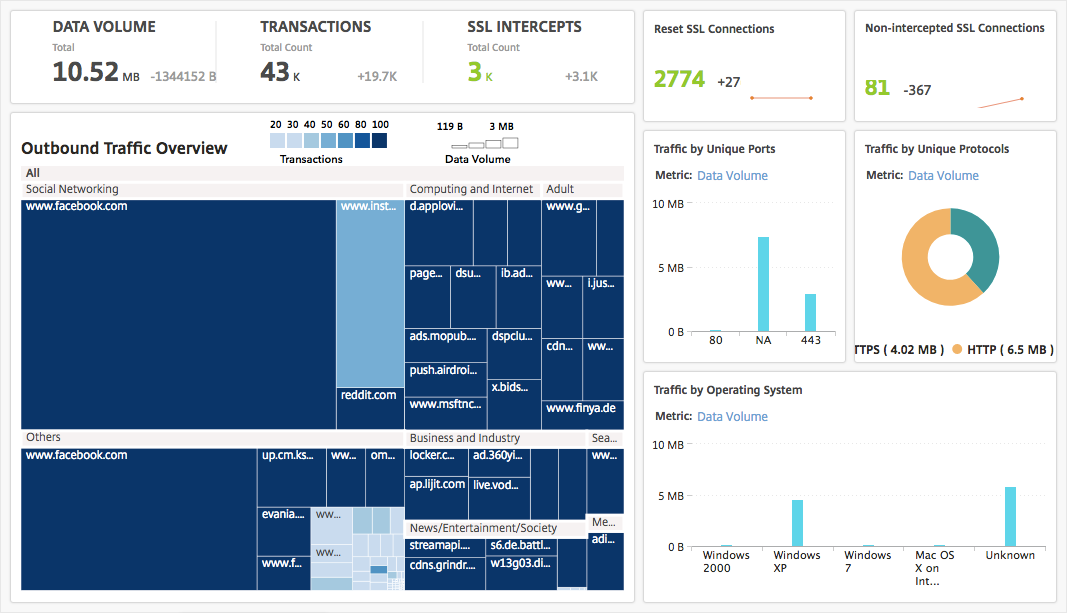
- Continuous Monitoring: Implementing systems that provide ongoing surveillance of network activities.
- AI and Machine Learning: Leveraging these technologies to predict and identify threats faster.
Enhanced Collaboration
There's a growing trend towards enhanced collaboration between organizations and government agencies like CISA. This collaboration aims to:
- Share Information: Exchange threat intelligence and best practices.
- Coordinate Responses: Develop unified responses to emerging threats.
Adoption of Zero Trust Models
Zero Trust is becoming the cornerstone of modern cybersecurity strategies. This model assumes that threats could be internal or external, and therefore, continuous verification is necessary.
Conclusion
The Citrix Net Scaler vulnerability highlights the critical importance of proactive vulnerability management and timely patch application. By understanding the technical aspects of CVE-2026-3055 and implementing best practices, organizations can protect their systems from exploitation.
As cybersecurity threats continue to evolve, staying informed and adopting a layered security approach will be essential in safeguarding sensitive data and maintaining operational integrity.

FAQ
What is the Citrix Net Scaler vulnerability?
The Citrix Net Scaler vulnerability, identified as CVE-2026-3055, is a critical input validation flaw in the SAML IDP function of Net Scaler ADC and Gateway systems, which can lead to unauthorized access.
How does CISA's directive impact organizations?
CISA's directive mandates Federal Civilian Executive Branch agencies to apply the necessary patches to mitigate the vulnerability, emphasizing the importance of timely patch management for all organizations.
What steps should organizations take to secure their systems?
Organizations should apply the Citrix patch, conduct regular security audits, implement network segmentation, and enhance authentication mechanisms such as MFA and Zero Trust.
Why is input validation important in cybersecurity?
Input validation is crucial because it ensures that data processed by applications is secure and free from malicious content, preventing exploits like CVE-2026-3055.
What are the key benefits of adopting a Zero Trust model?
A Zero Trust model enhances security by continuously verifying user access and device integrity, reducing the risk of unauthorized access.
How can organizations stay informed about new vulnerabilities?
Organizations can stay informed by subscribing to CISA alerts, participating in industry forums, and utilizing threat intelligence platforms.
What role do AI and machine learning play in cybersecurity?
AI and machine learning help predict and identify threats more efficiently, enabling organizations to respond proactively to emerging vulnerabilities.
Can regular user training improve cybersecurity?
Yes, regular user training is vital for educating employees about security best practices and the importance of timely updates, thereby reducing human error-related breaches.

Key Takeaways
- Immediate patching required for Citrix NetScaler vulnerability CVE-2026-3055.
- CISA mandates FCEB agencies to address the flaw by a specific deadline.
- Understanding input validation flaws is crucial for securing systems.
- Implementing Zero Trust and MFA enhances organizational security posture.
- Proactive threat intelligence and collaboration are key to future cybersecurity strategies.
Related Articles
- Optimizing Aircraft Cabin Layouts for Efficient Evacuations [2025]
- Aston Martin Valhalla (2026) Review: A $1 Million Plug-In Hybrid Masterpiece [2025]
- Instagram's New Feature: Paying for Anonymous Story Viewing [2025]
- Mastering Health Insights with Samsung Galaxy Watches: Blood Pressure Tracking Unveiled [2025]
- Indoor Cleaning Revolution: The Shark BlastBoss Leaf Blower [2025]
- Why Silence is No Longer a Security Strategy [2025]
![Citrix NetScaler Flaw: CISA's Patch Warning and What It Means [2025]](https://tryrunable.com/blog/citrix-netscaler-flaw-cisa-s-patch-warning-and-what-it-means/image-1-1774975353871.jpg)



