Introduction
For decades, silence was a favored strategy in cybersecurity. The notion was simple: if you don't talk about weaknesses, they won't be exploited. But as cyber threats grow more sophisticated, this approach is no longer viable. Today, transparency, proactive communication, and constant vigilance are essential to safeguarding digital assets.
TL; DR
- Silent strategies are outdated: Transparency is now crucial for robust security.
- Cyber threats are evolving: Attackers use advanced techniques requiring open communication.
- Compliance demands disclosure: Regulatory requirements drive transparency.
- Community intelligence is key: Sharing information improves collective security.
- Proactive measures reduce risk: Early detection and response are critical.
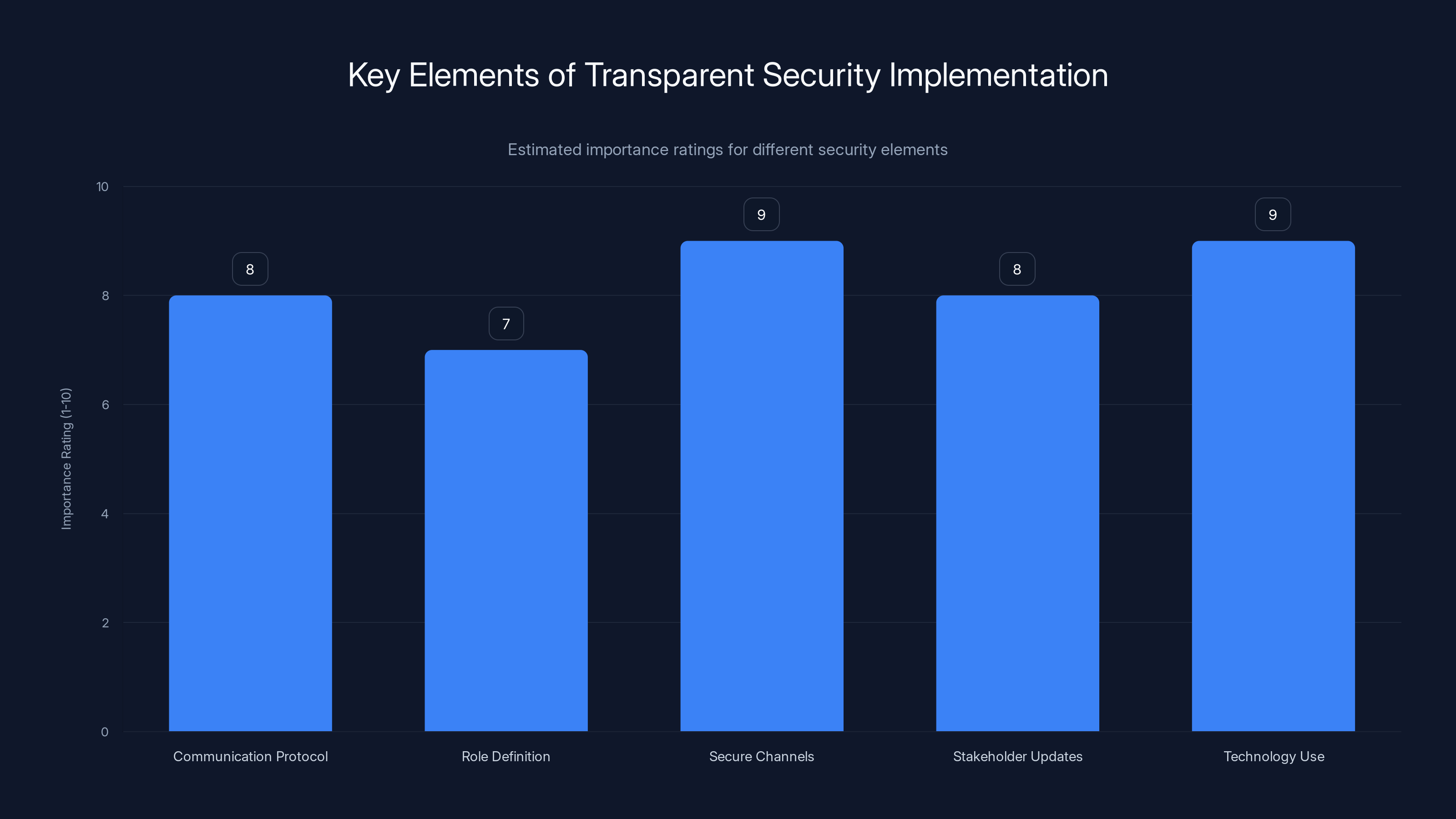
Secure channels and technology use are rated highest in importance for implementing transparent security. Estimated data.
The Fallacy of Silence in Cybersecurity
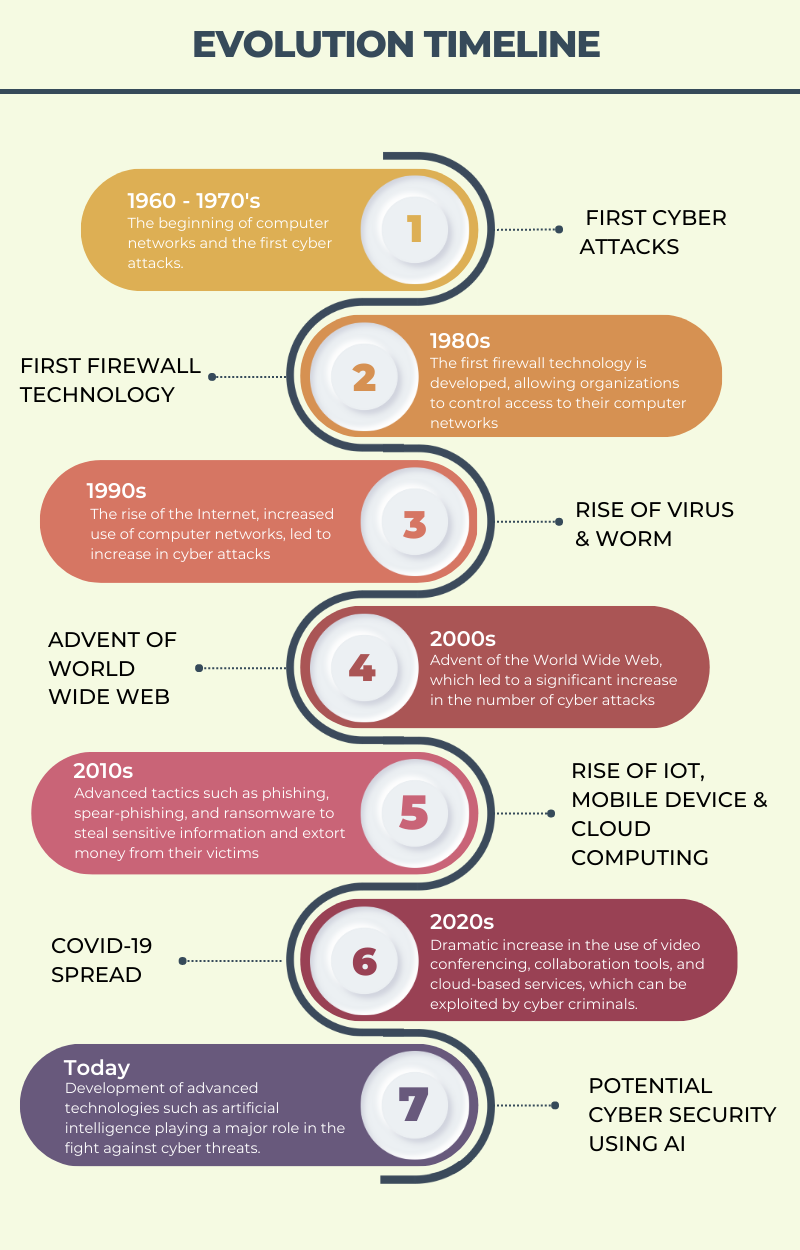
Historical Context
In the early days of digital security, organizations believed that keeping vulnerabilities hidden would protect them from attackers. This strategy was based on the assumption that cybercriminals were less likely to exploit unknown vulnerabilities.
The Evolution of Cyber Threats
Cyber threats have evolved significantly. Attackers now use sophisticated techniques, such as AI-driven malware and zero-day exploits, to breach systems. These methods often bypass traditional security measures, rendering silent strategies ineffective.
Compliance and Regulatory Pressure
Today, regulations like the GDPR and CCPA require organizations to disclose breaches and vulnerabilities. Failure to comply can result in hefty fines and reputational damage. Transparency is not just a good practice; it's a legal obligation.
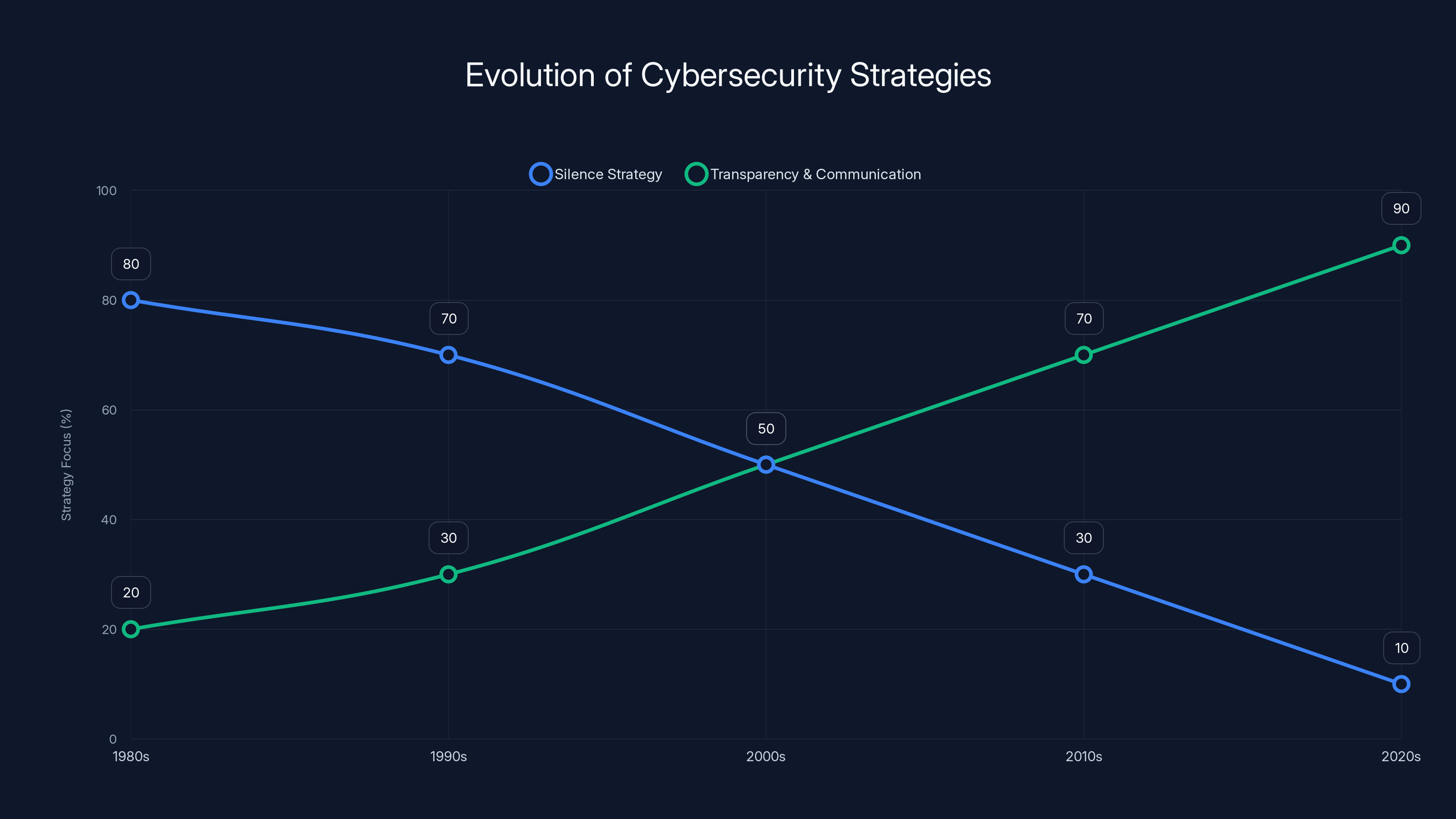
Over the decades, the focus in cybersecurity has shifted from silence to transparency and proactive communication. Estimated data.
The Importance of Transparency
Building Trust with Stakeholders
Transparency fosters trust among stakeholders, including customers, partners, and investors. When organizations communicate openly about their security measures, they demonstrate a commitment to protecting sensitive information.
Enhancing Security Through Collaboration
Sharing information about threats and vulnerabilities enables organizations to learn from each other's experiences. This collective intelligence strengthens overall security and helps prevent widespread attacks.

Practical Implementation of Transparent Security
Establishing a Communication Protocol
Develop a protocol for reporting and communicating about security incidents. This should include guidelines on what to disclose, when to disclose it, and to whom.
- Define Roles and Responsibilities: Ensure everyone knows their part in the communication process.
- Utilize Secure Channels: Use encrypted communication tools to share sensitive information.
- Regularly Update Stakeholders: Keep stakeholders informed about ongoing security efforts and new threats.
Leveraging Technology for Transparency
Tools such as Security Information and Event Management (SIEM) systems can automate the collection and analysis of security data, making it easier to share insights with stakeholders.
Case Study: A Transparent Security Approach
A financial services company implemented a transparent security strategy, publicly disclosing its security protocols and breach incidents. As a result, it gained customer trust and improved its security posture through industry collaboration.

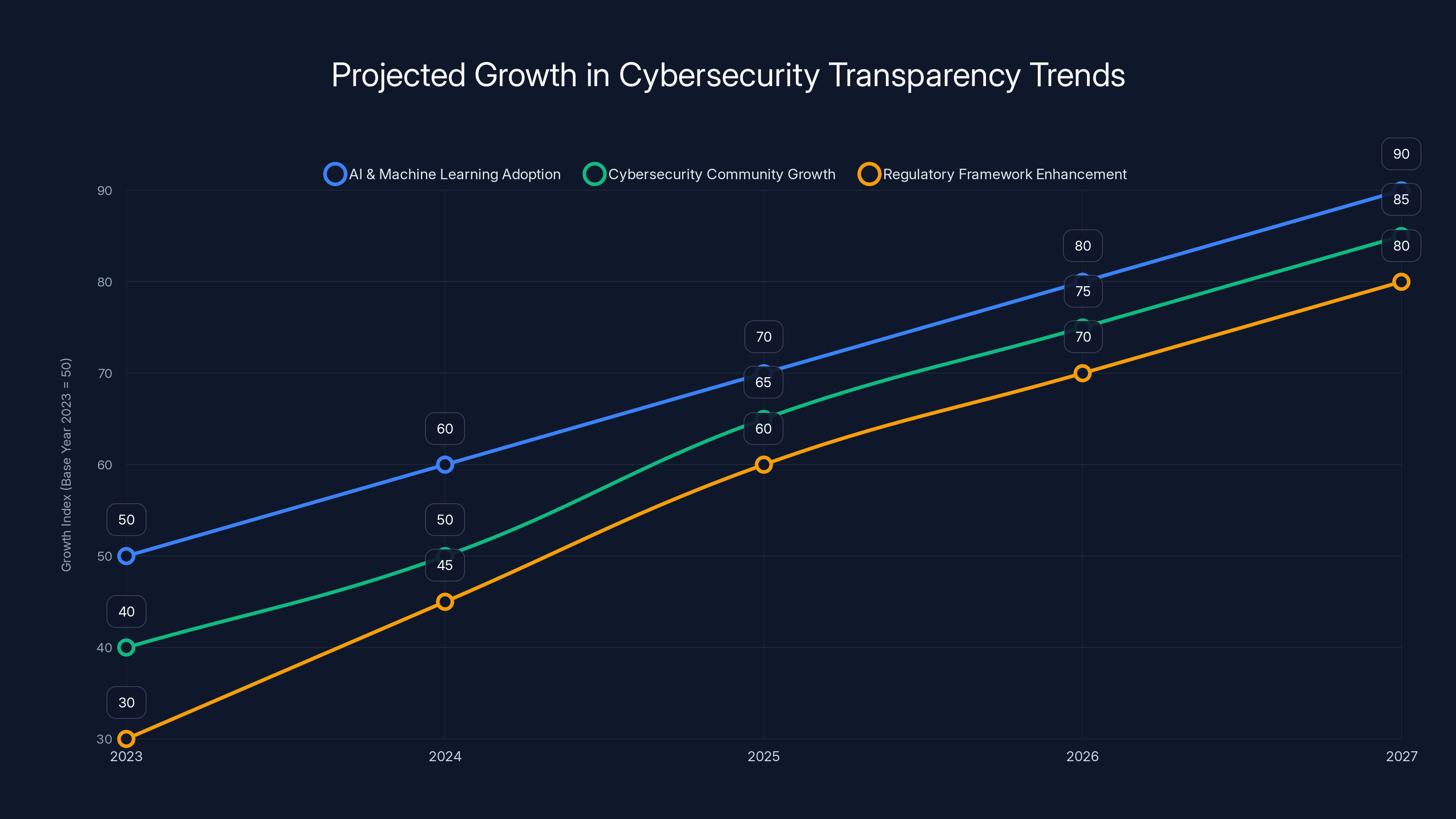
AI and machine learning adoption, cybersecurity community growth, and regulatory enhancements are all projected to significantly increase by 2027. Estimated data based on current trends.
Common Pitfalls and How to Avoid Them
Over-Disclosing Information
While transparency is critical, over-disclosure can lead to unnecessary panic and expose organizations to additional risks.
- Solution: Balance transparency with discretion. Only disclose necessary information to relevant parties.
Failing to Update Communication Protocols
Outdated communication protocols can lead to miscommunication and delayed responses during security incidents.
- Solution: Regularly review and update communication protocols to ensure they align with current threats and technologies.
Future Trends in Cybersecurity Transparency
Increased Use of AI and Machine Learning
AI and machine learning will play a significant role in analyzing and sharing security data, enabling faster and more accurate threat detection.
The Rise of Cybersecurity Communities
Online communities and forums dedicated to cybersecurity will continue to grow, providing platforms for professionals to share information and collaborate on solutions.
Enhanced Regulatory Frameworks
As governments recognize the importance of transparency in cybersecurity, expect more stringent regulations that mandate disclosure of security incidents.
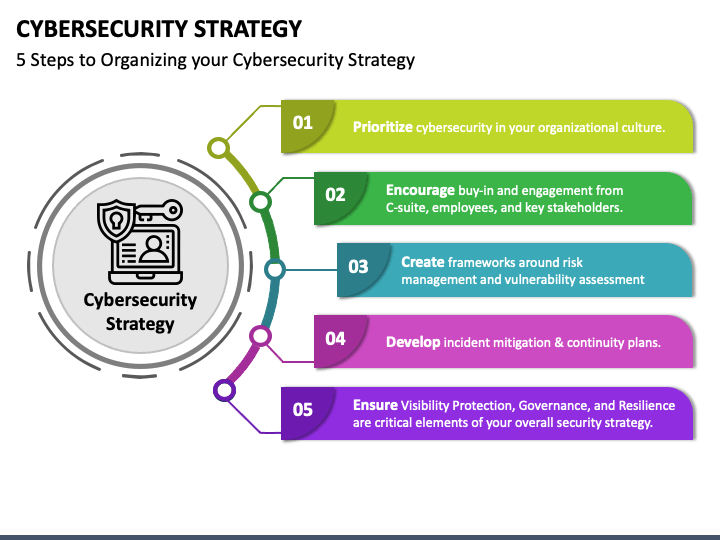
Recommendations for a Transparent Security Strategy
- Adopt a Proactive Mindset: Proactively search for vulnerabilities and address them before they can be exploited.
- Promote a Culture of Security: Educate employees about the importance of security and encourage open communication.
- Invest in Advanced Security Tools: Utilize tools that facilitate transparency and enhance threat detection.
- Collaborate with Industry Peers: Engage with other organizations to share threat intelligence and best practices.

Conclusion
Silence is no longer a viable security strategy in today's digital landscape. By embracing transparency and proactive communication, organizations can build trust, improve security, and stay ahead of evolving threats. The future of cybersecurity depends on our ability to adapt and collaborate, ensuring that we protect our digital assets and maintain the trust of those we serve.

FAQ
What is cybersecurity transparency?
Cybersecurity transparency involves openly communicating about security practices, incidents, and vulnerabilities to build trust and improve collective security.
How can organizations implement transparent security strategies?
Organizations can implement transparent security strategies by establishing clear communication protocols, leveraging technology, and collaborating with industry peers.
Why is silence no longer an effective security strategy?
Silence is ineffective because cyber threats are evolving, and regulatory requirements mandate disclosure of security incidents. Transparency enhances security by fostering collaboration and trust.
What are the benefits of a transparent security approach?
Benefits include improved trust with stakeholders, enhanced threat detection and response, and compliance with regulatory requirements.
How does AI contribute to cybersecurity transparency?
AI contributes by automating threat detection and analysis, enabling faster and more accurate sharing of security insights.
What role do cybersecurity communities play in transparency?
Cybersecurity communities provide platforms for professionals to share information, collaborate on solutions, and improve collective security.
What are the potential challenges of transparency in cybersecurity?
Challenges include balancing transparency with discretion, avoiding over-disclosure, and keeping communication protocols up to date.

Key Takeaways
- Silent strategies are outdated; transparency is crucial.
- Regulations require disclosure of security incidents.
- Collaboration enhances collective security.
- AI and machine learning improve threat detection.
- Proactive communication builds stakeholder trust.
- Balancing transparency with discretion is key.
Related Articles
- The Fluoride Debate: Implications and Insights from Birmingham's Water Utility Decision [2025]
- OkCupid's FTC Settlement: Lessons and Future of Data Privacy [2025]
- WordPress Plugin Security Flaws: Understanding Risks and Protecting Your Site [2025]
- Apple Turns 50: Celebrating Five Decades of Innovation and Influence [2025]
- World Backup Day 2026: Ultimate Guide to Ensuring Data Safety and Security
- European Commission Data Breach: What Happened and How to Respond [2025]
![Why Silence is No Longer a Security Strategy [2025]](https://tryrunable.com/blog/why-silence-is-no-longer-a-security-strategy-2025/image-1-1774955116486.jpg)



