How Technology Tripped Up Cybercriminals: Lessons from the Microsoft Teams Recording Mishap [2025]
Last month, the digital underworld witnessed a rare yet telling blunder. A pair of cybercriminal twins, notorious for their sophisticated phishing schemes, were apprehended after they inadvertently left a Microsoft Teams recording on during a key operation. This incident not only highlights the vulnerabilities that even seasoned hackers face but also underscores the importance of robust cybersecurity practices in our increasingly digital work environments.
TL; DR
- Key Point 1: Cybercriminals left Microsoft Teams recording active, leading to their arrest.
- Key Point 2: Human error remains a significant security vulnerability in digital operations.
- Key Point 3: Implementing proper security protocols can prevent such oversights.
- Key Point 4: Regular security audits and training are crucial for maintaining organizational safety.
- Bottom Line: Vigilance and proper use of security tools are essential in preventing cyber threats.
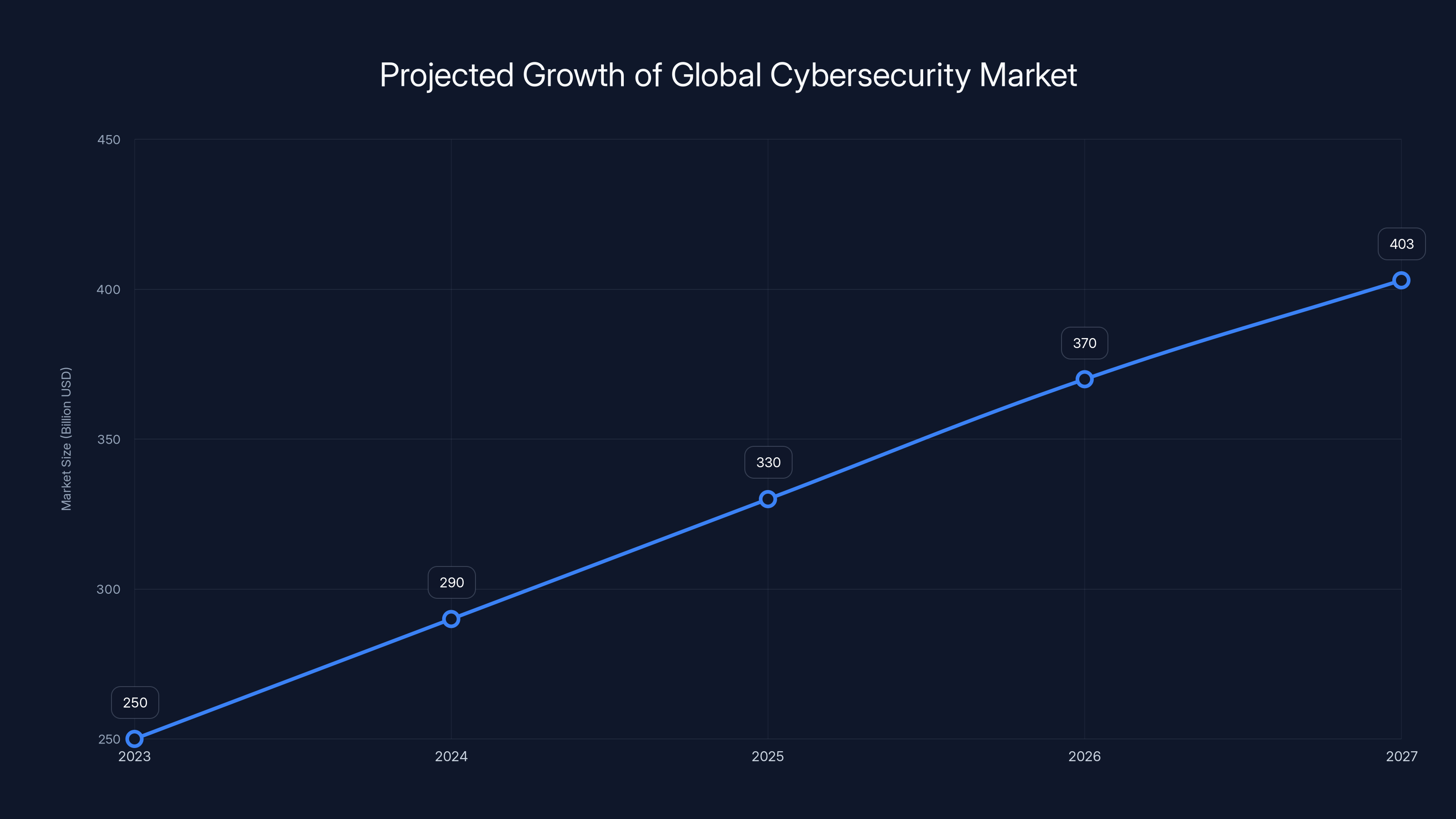
The global cybersecurity market is projected to grow steadily, reaching $403 billion by 2027, driven by increasing cyber threats and technological advancements. Estimated data.
The Incident Unpacked
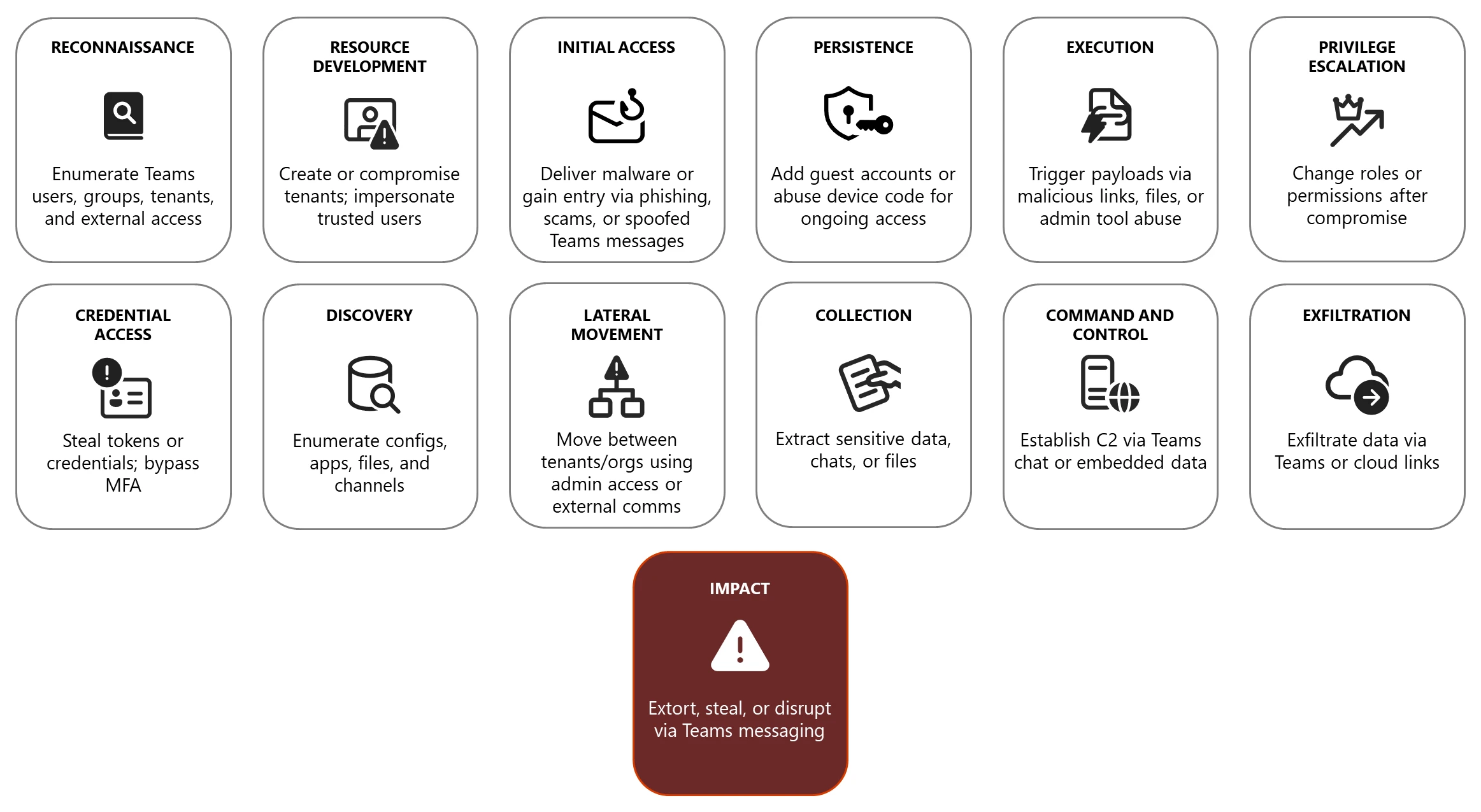
The cybercriminals, operating under the pseudonyms of "The Digital Twins," had orchestrated a series of high-stakes phishing attacks targeting corporate executives. Their modus operandi involved sophisticated spoofing techniques, exploiting vulnerabilities in widely-used platforms to gain unauthorized access to sensitive information.
What Went Wrong?
During a critical planning session on Microsoft Teams, the twins failed to disable the recording feature, inadvertently capturing their entire discussion. The recorded session, which automatically uploaded to their cloud storage, was discovered during a routine security sweep by a vigilant IT team. This mishap led to their identities being exposed and their eventual arrest, as detailed in Wiz's AI Security insights.

Estimated data showing the effectiveness of various security tools, highlighting encryption and multi-factor authentication as top-rated solutions.
Understanding the Technology
Microsoft Teams Recording: How It Works
Microsoft Teams offers a seamless way to record meetings, which can be incredibly useful for documentation and review purposes. However, this feature can also become a liability if not managed correctly.
- Automatic Upload: Recordings are automatically uploaded to the cloud, ensuring easy access but also potential security risks if permissions are not properly set.
- Access Controls: Admins can set who has the ability to start recordings, providing a layer of control to prevent unauthorized recordings, as outlined in Microsoft's Dynamics 365 blog.
- Retention Policies: Organizations can define how long recordings are kept, helping manage storage and security risks.
Security Implications
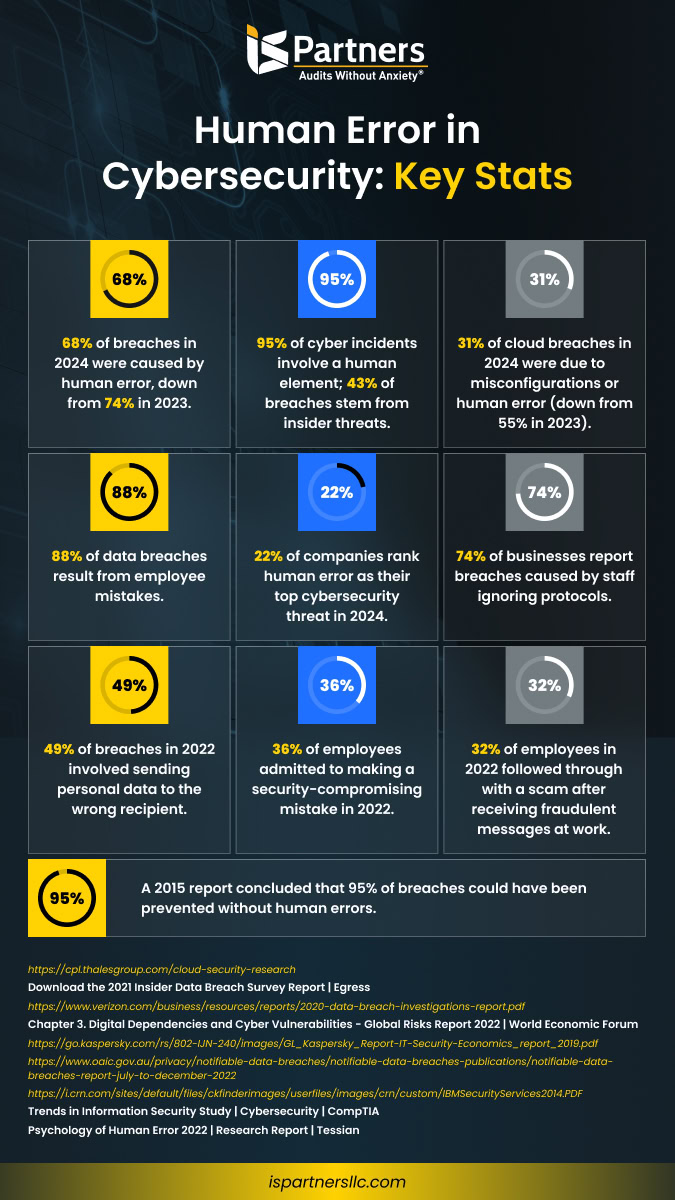
The incident with the twins underscores a critical security lesson: human error can undermine even the most sophisticated systems. In this case, a simple oversight turned a powerful tool into a vulnerability.
- Unintentional Disclosure: As seen, recordings can inadvertently capture sensitive information if not carefully managed.
- Access Permissions: Ensuring only authorized personnel can view and manage recordings is crucial.
- Data Loss Prevention: Implementing DLP policies can help flag and mitigate risks associated with data sharing, as emphasized by Qualys' security governance strategies.
Best Practices for Securing Digital Workspaces
1. Implementing Strict Access Controls
Limiting who can start and access recordings is a foundational step in securing digital communication platforms. Here’s how:
- Role-Based Access: Assign permissions based on roles within the organization.
- Multi-Factor Authentication (MFA): Use MFA to add an extra layer of security for accessing recordings.
- Regular Audits: Conduct regular audits to ensure compliance with access policies, as suggested by Federal News Network's insights on AI risks.
2. Educating Employees
Training employees on security best practices is crucial. Awareness programs should cover:
- Recognizing Phishing Attacks: Teach how to identify and report suspicious emails or messages.
- Handling Sensitive Information: Educate on the importance of securing sensitive data and the risks of oversharing.
- Device Security: Encourage secure device practices, such as regular updates and the use of strong passwords.
3. Leveraging Technology for Security
Utilize advanced security tools to enhance protection:
- AI-Powered Threat Detection: Use AI to monitor and flag unusual activities in real-time.
- Automated Compliance Checks: Implement tools that automatically check for compliance with security policies.
- Encryption: Ensure all communications and stored data are encrypted to prevent unauthorized access, as highlighted in Nomad Lawyer's report on airport security.
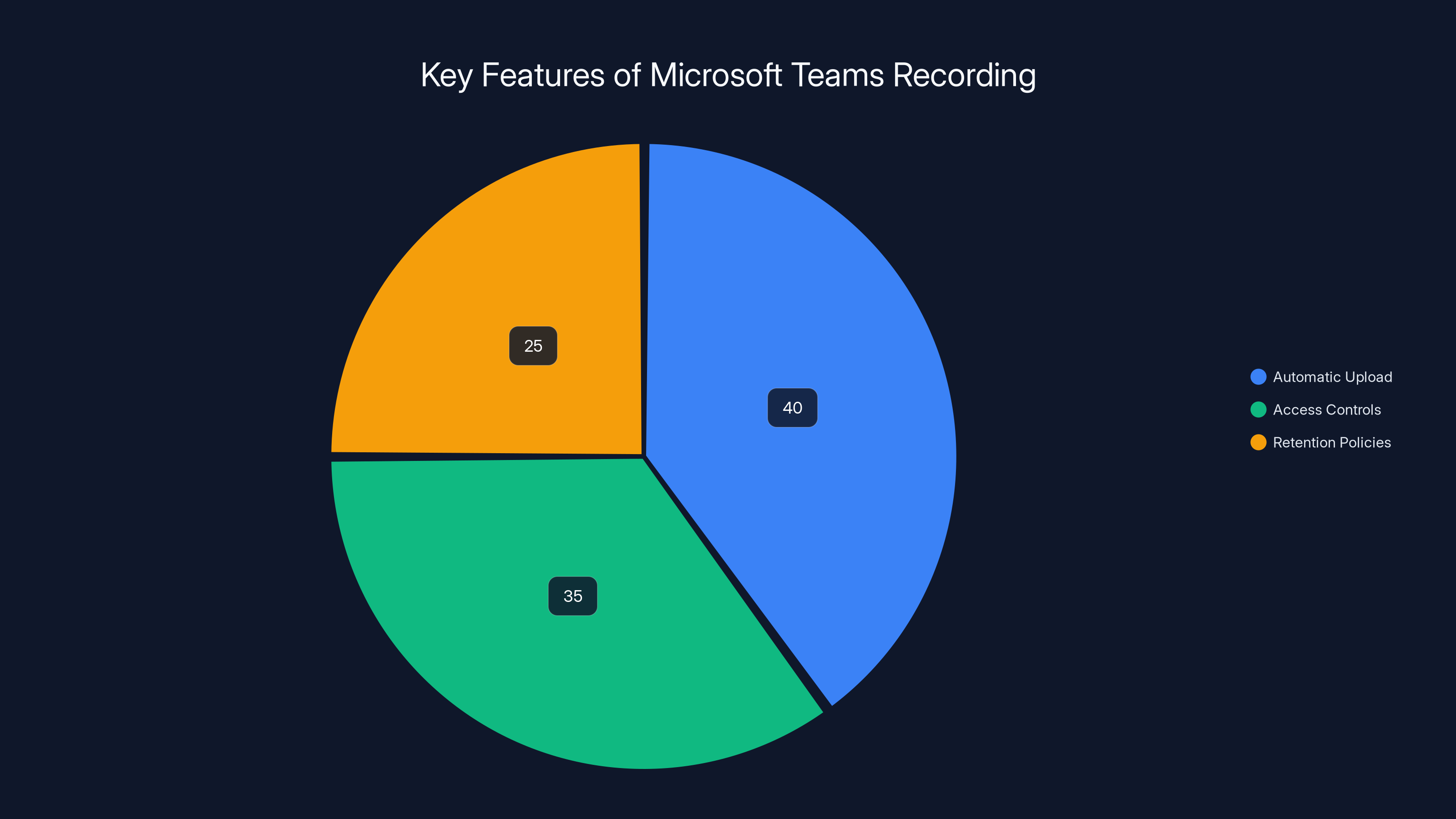
Automatic upload is the most critical feature due to its convenience and potential security risks, followed by access controls and retention policies. Estimated data.
Common Pitfalls and Solutions
Even with the best intentions, organizations can fall prey to common pitfalls that undermine their security efforts. Here are some to watch out for:
Pitfall 1: Overlooking Software Updates
Failing to keep software up-to-date can expose vulnerabilities. To counter this:
- Automatic Updates: Enable automatic updates for critical software to ensure the latest security patches are applied.
- Update Policies: Establish policies that mandate regular updates and maintenance checks.
Pitfall 2: Inadequate Incident Response Plans
Without a solid incident response plan, even minor breaches can escalate. Address this by:
- Developing a Response Plan: Create a detailed plan outlining steps to take in the event of a breach.
- Conducting Drills: Regularly simulate breaches to test and improve your response plan, as recommended by Cyfirma's intelligence reports.
Pitfall 3: Ignoring Insider Threats
Insider threats can be particularly damaging as they often go unnoticed. Mitigate this risk by:
- Monitoring Access Logs: Regularly review logs for unusual access patterns.
- Behavioral Analytics: Use analytics to detect anomalous behavior that could indicate a compromise.
Future Trends in Cybersecurity
As technology evolves, so too do the tactics of cybercriminals. Here are some trends to watch in the coming years:
1. Increased Use of AI in Cyber Defense
AI is becoming a cornerstone of cybersecurity, providing capabilities such as predictive analytics and automated threat detection.
- Predictive Models: AI can anticipate potential threats before they occur, allowing for proactive defense measures.
- Adaptive Learning: Systems that learn from each interaction to improve security protocols over time.
2. Expansion of Zero Trust Models
The Zero Trust security model, which assumes no trust for any user, will continue to gain traction.
- Micro-Segmentation: Dividing networks into smaller, isolated segments to prevent lateral movement of attackers.
- Identity Verification: Continuous verification of user identities at every access point.
3. Cybersecurity as a Service (CaaS)
Organizations are increasingly outsourcing their cybersecurity needs to specialized service providers.
- Scalability: CaaS offers scalable solutions tailored to the needs of the organization.
- Expertise: Access to top-tier security expertise without the overhead of an in-house team.


Encryption and AI-powered threat detection are rated as the most effective measures for securing digital workspaces. Estimated data.
Recommendations for Organizations
Strengthening Security Culture
Fostering a security-conscious culture is essential. Organizations should:
- Leadership Involvement: Encourage leaders to actively participate in security initiatives.
- Open Communication: Promote an environment where employees feel comfortable reporting security concerns.
- Recognition Programs: Implement programs that reward employees for identifying security risks.
Investing in Advanced Tools
Adopt tools that enhance security without compromising usability:
- Unified Threat Management (UTM): Integrate various security functions into a single platform.
- Endpoint Detection and Response (EDR): Use EDR solutions to monitor and respond to threats on individual devices.
Continuous Improvement
Security is not a one-time task but an ongoing process:
- Feedback Loops: Establish mechanisms for continuous feedback on security processes.
- Regular Reviews: Perform frequent reviews of security policies and update them as needed.

Conclusion
The incident involving the cybercriminal twins serves as a stark reminder of the ever-present dangers in the digital world. By understanding the vulnerabilities that exist within our technological tools and implementing robust security measures, organizations can significantly reduce their risk of falling victim to similar blunders.
As we move forward, the integration of advanced technologies like AI and the adoption of comprehensive security frameworks will be critical in safeguarding our digital environments. By fostering a culture of security and vigilance, we can better protect our organizations from the evolving landscape of cyber threats.
FAQ
What is Microsoft Teams recording?
Microsoft Teams recording is a feature that allows meetings to be recorded for later review. These recordings are automatically saved to the cloud, making them easily accessible for authorized users.
How can accidental recordings be prevented?
Accidental recordings can be prevented by implementing strict access controls, training employees to check recording settings before and after meetings, and conducting regular audits to ensure compliance with security policies.
Why is human error a significant security risk?
Human error is a major security risk because it can undermine even the most sophisticated security systems. Errors such as forgetting to turn off a recording feature or clicking on a phishing link can lead to significant data breaches.
What are the benefits of AI in cybersecurity?
AI enhances cybersecurity by providing predictive analytics, automated threat detection, and adaptive learning capabilities. These features enable organizations to anticipate and respond to threats more effectively.
How does the Zero Trust model work?
The Zero Trust model operates on the principle of "never trust, always verify." It requires continuous verification of user identities and limits access based on strict identity verification and micro-segmentation of networks.
What is Cybersecurity as a Service (CaaS)?
CaaS is a model where organizations outsource their cybersecurity needs to specialized service providers. This approach offers scalability, access to expert knowledge, and cost savings compared to maintaining an in-house security team.
How can organizations foster a security-conscious culture?
Organizations can foster a security-conscious culture by involving leadership in security initiatives, promoting open communication, and implementing recognition programs that reward employees for identifying security risks.
What tools are recommended for enhancing organizational security?
Unified Threat Management (UTM) and Endpoint Detection and Response (EDR) solutions are recommended for enhancing organizational security. These tools provide integrated security functions and monitor threats on individual devices, respectively.
How often should security policies be reviewed?
Security policies should be reviewed regularly, ideally quarterly, to ensure they remain effective and up-to-date with the latest threats and technological advancements.
What was the outcome of the Microsoft Teams incident?
The Microsoft Teams incident led to the capture and arrest of the cybercriminal twins, illustrating the critical importance of vigilance and the proper management of digital tools in preventing cyber threats.

Key Takeaways
- Cybercriminals were caught due to a Microsoft Teams recording mistake.
- Human error is a major vulnerability in cybersecurity.
- Strict access controls can prevent unauthorized recordings.
- AI is crucial for modern cybersecurity defenses.
- Zero Trust models enhance network security by assuming no trust.
- Cybersecurity as a Service (CaaS) is growing in popularity.
Related Articles
- The Hotel Check-In Security Debacle: Lessons from Tabiq's Data Exposure [2025]
- Understanding the Mistral AI Breach: Implications for AI Security in 2025
- Understanding the Fragnesia Flaw: How It Threatens Linux Security [2025]
- Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
- Understanding Supply Chain Attacks: Lessons from the OpenAI Data Breach [2025]
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
![How Technology Tripped Up Cybercriminals: Lessons from the Microsoft Teams Recording Mishap [2025]](https://tryrunable.com/blog/how-technology-tripped-up-cybercriminals-lessons-from-the-mi/image-1-1778929435874.jpg)



