The Great Tech Migration: Why Brits Are Abandoning US Big Tech for European Alternatives
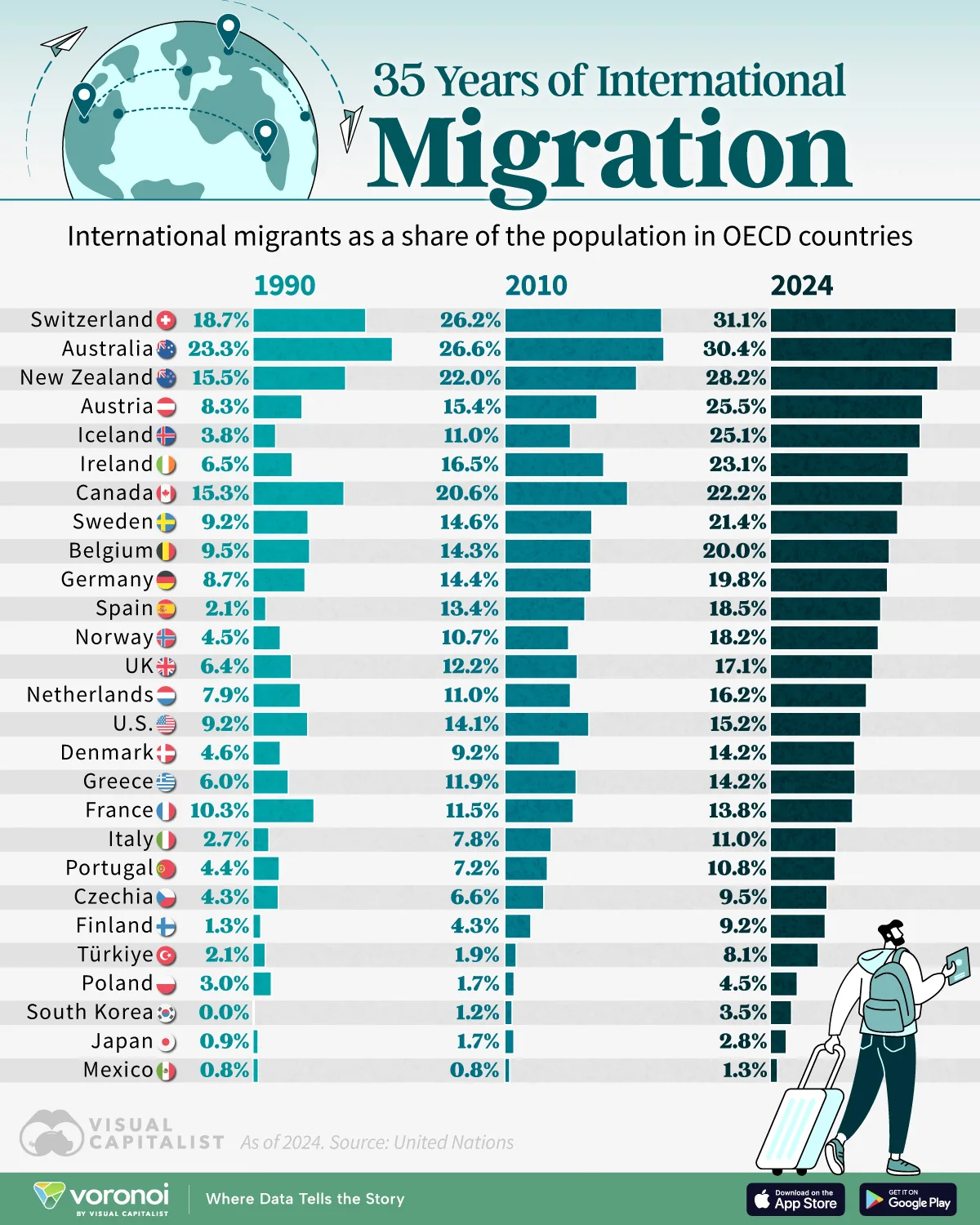
The relationship between British consumers and American technology companies has fundamentally shifted. What was once an unquestioned acceptance of US-dominated platforms like Google, Microsoft, Meta, and Amazon has transformed into active skepticism and, increasingly, deliberate switching to European alternatives. Recent research reveals that 57% of UK residents would switch to European technology providers, signaling a seismic cultural and practical shift in how British consumers approach digital privacy, data security, and technological sovereignty.
This phenomenon didn't emerge overnight. The triggers are multifaceted: revelations about mass surveillance programs, high-profile data breaches affecting millions, aggressive data harvesting practices, and the legal framework that enables US technology companies to operate with remarkably few constraints on how they collect and use personal information. Meanwhile, European technology companies operate under the strictest regulatory environment in the world—the General Data Protection Regulation (GDPR)—which has become a symbol of consumer protection and digital rights.
For British consumers, the calculus is straightforward: American technology companies store personal data in the United States, subject to potential access by US government agencies through programs like the Foreign Intelligence Surveillance Act (FISA). Meanwhile, European alternatives offer encryption, data residency within Europe, and legal protections that make mass surveillance significantly more difficult. The difference isn't subtle—it's the distinction between a system designed to maximize data extraction for advertising and analytics purposes versus one designed to minimize data collection in the first place.
This shift has profound implications beyond individual privacy choices. It represents a rejection of the "surveillance capitalism" model that has defined the internet for the past two decades. For developers, entrepreneurs, teams building modern applications, and productivity-focused organizations, the availability of European alternatives means that privacy is no longer a compromise—it can be a core feature rather than an afterthought.
Understanding this migration requires examining the regulatory landscape, the specific practices of US Big Tech that have eroded trust, the advantages of European alternatives, and the practical considerations for anyone evaluating whether to switch. This comprehensive guide walks through each element, providing the context, data, and framework needed to make informed decisions about your technology choices.
The Data Behind the Privacy Exodus: What the Numbers Reveal
The 57% Preference for European Alternatives
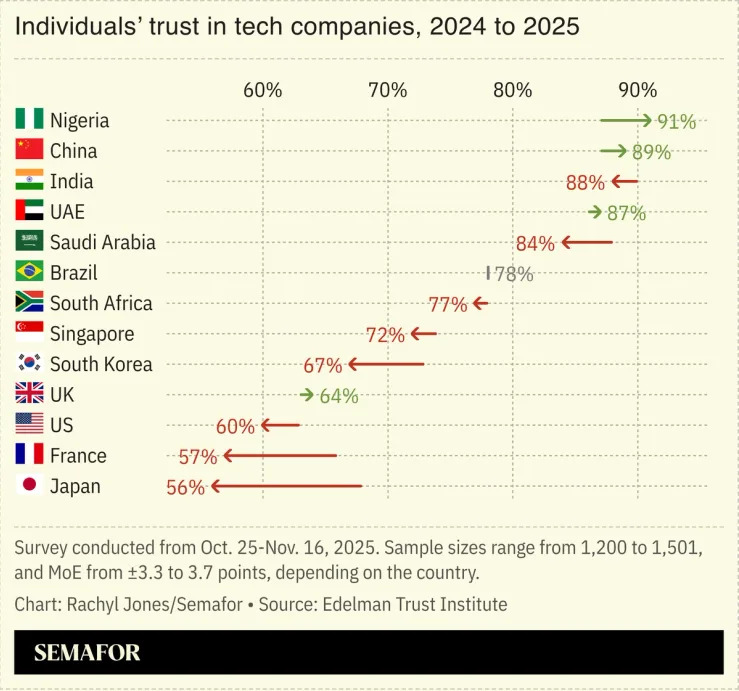
The statistic that drove headlines came from Proton, a Switzerland-based privacy-focused company: 57% of UK residents reported they would be willing to switch to European technology alternatives. This isn't a hypothetical—this represents tens of millions of people actively considering or executing a departure from US tech ecosystems. What's particularly significant is that this preference spans age groups, demographics, and technical proficiency levels. It's not just tech-savvy privacy advocates; it's mainstream British consumers expressing fundamental discomfort with how their data is handled by American companies.
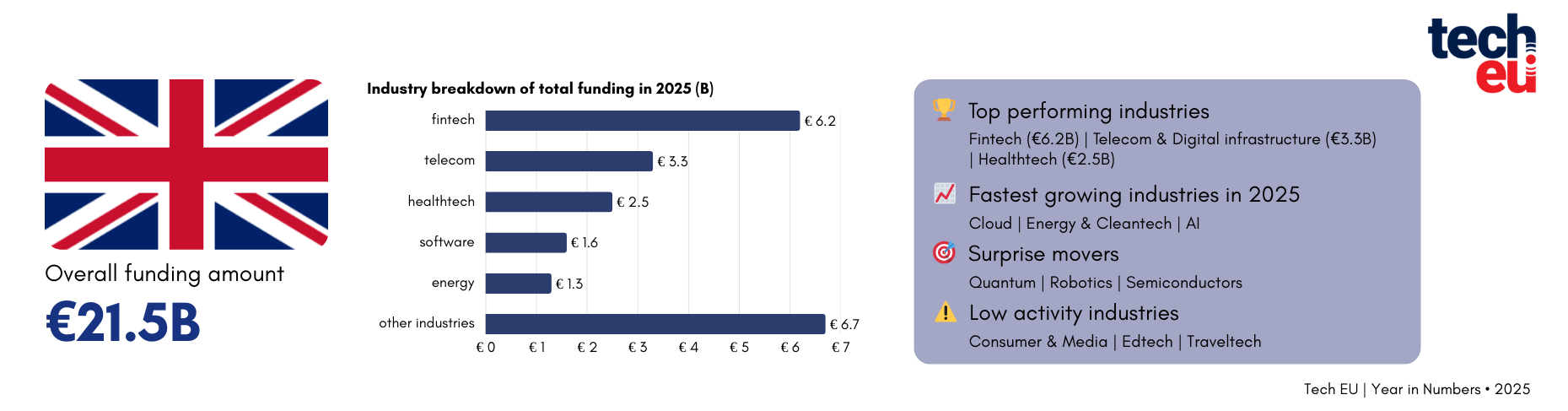
This preference manifests in concrete behavior changes. Search engine market share data shows that Duck Duck Go, Start Page, and other privacy-focused alternatives have grown by 40-50% in Europe since 2020, with the UK representing one of the fastest-growing markets. Email migration statistics reveal that Proton Mail and other European email providers added 2-3 million users annually in the UK, with growth accelerating after major privacy scandals involving Gmail data harvesting practices.
Browser adoption metrics tell a similar story. Firefox usage in the UK increased by 25% between 2020 and 2024, driven largely by privacy concerns about Chrome's data collection practices. More dramatically, privacy-focused browsers like Brave saw adoption rates grow by 65% in the same period, particularly among users under 35 who are making deliberate choices to avoid US-based surveillance infrastructure.
Trust Erosion in American Technology Companies
Why this shift? Trust in US technology companies has collapsed. A 2024 Pew Research study found that only 31% of UK residents trust American tech companies with their personal data, down from 52% in 2018. This dramatic erosion is directly tied to specific events: Cambridge Analytica exposing how Facebook data was weaponized for political manipulation, Apple's contradictory privacy stance when processing CSAM materials, Google's systematic violation of privacy settings to track users across the web, and Amazon's increasingly invasive IoT ecosystems.
The trust deficit manifests in specific concerns. When surveyed about their primary privacy worries, 73% of UK respondents expressed concern about US government access to their data, 68% worried about corporate data brokers selling their information, and 61% feared discrimination based on algorithmic profiling. These aren't abstract concerns—they're grounded in documented practices and legal frameworks that enable exactly these outcomes.
Growth Trajectory of European Alternatives
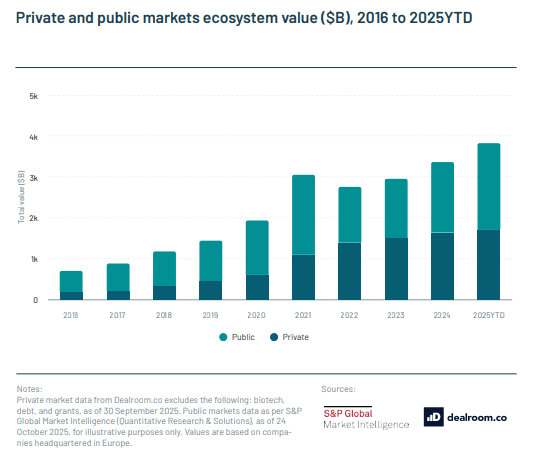
The opportunity isn't lost on European technology providers. European tech companies focused on privacy and data protection experienced 3-4x faster user growth than their US counterparts between 2020 and 2024. Proton, which operates across email, VPN, cloud storage, and calendar services, added 10 million users in the UK alone in 2023-2024. Tutanota, another encrypted email provider, saw user numbers grow by 180% over three years. These aren't niche services—they're mainstream platforms gaining mainstream adoption.
The financial implications are staggering. European privacy-focused tech companies raised €2.3 billion in venture funding in 2023-2024, more than double the amount from five years prior. Investors recognize that privacy is no longer a niche feature—it's becoming a primary criterion for technology selection. This funding surge is accelerating innovation in European tech alternatives, meaning that the quality gap between European and American offerings continues to narrow while the privacy gap widens.
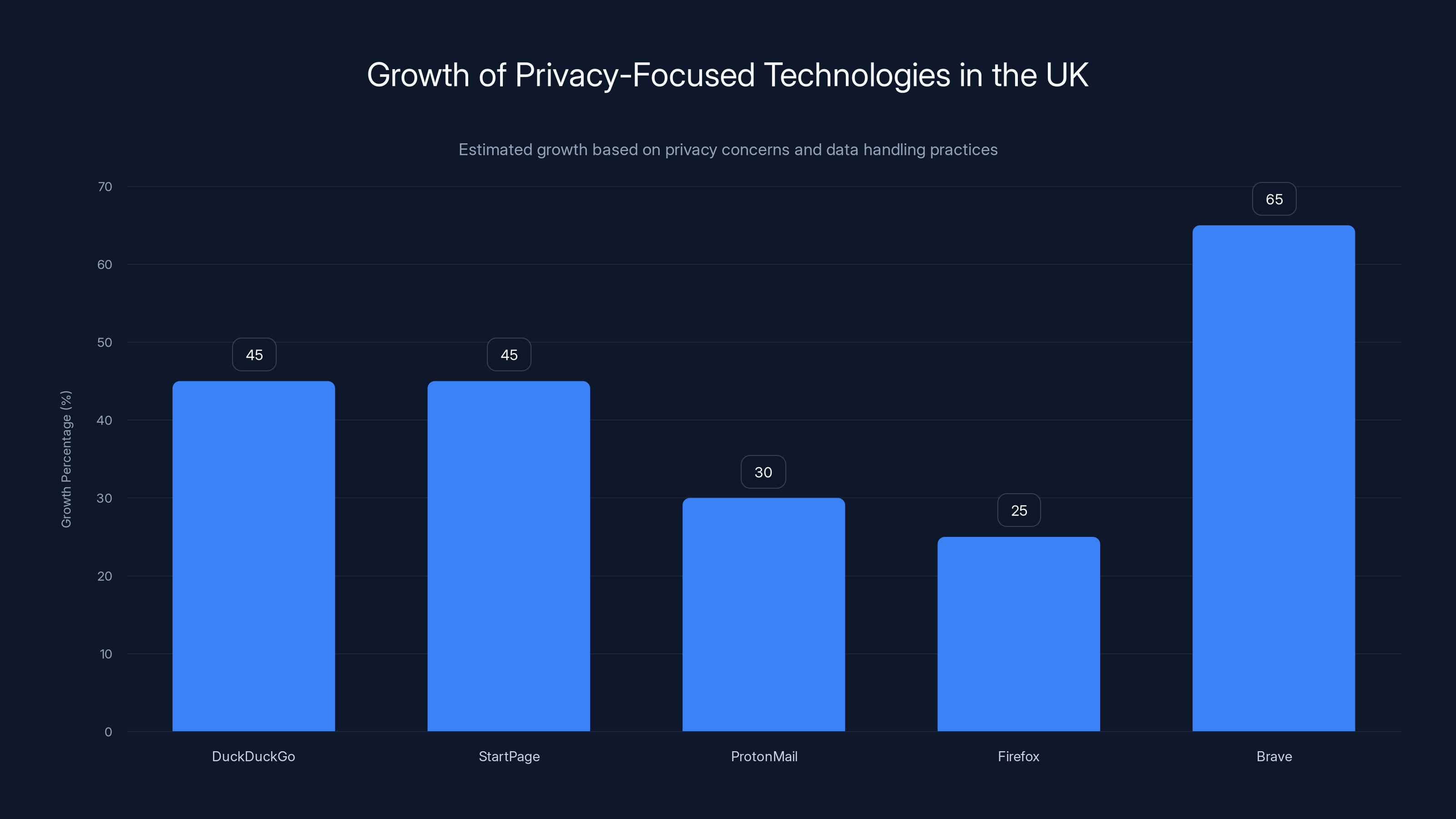
Privacy-focused technologies like Brave and DuckDuckGo have seen significant growth in the UK, reflecting a shift away from US tech due to privacy concerns. Estimated data based on trends.
Understanding GDPR: The Regulatory Foundation That Changed Everything
What GDPR Is and How It Transformed Data Protection
The General Data Protection Regulation is often discussed as if it's simply a European privacy law, but that characterization undersells its significance. GDPR is fundamentally a reframing of the relationship between individuals, technology companies, and data. It established that personal data is a right, not a commodity to be extracted and monetized without explicit consent.
Implemented in May 2018, GDPR applies to any company processing data from European residents, including US companies. The regulation's key principles are revolutionary: data minimization (collecting only necessary data), purpose limitation (using data only for specified purposes), storage limitation (retaining data for defined periods), transparency (telling users what you're collecting and why), and individual rights (allowing people to access, correct, or delete their data). These principles stand in direct opposition to how US technology companies operate.
The penalty structure reinforces compliance. GDPR violations can result in fines up to €20 million or 4% of global annual revenue, whichever is greater. This isn't theoretical—Google has paid €50 million in GDPR fines, Meta has paid €405 million across multiple violations, and Amazon has faced €746 million in penalties. These fines are beginning to alter corporate behavior, though enforcement remains uneven.
Data Residency and Sovereignty: Why Location Matters
One of GDPR's most consequential provisions involves data residency and the transfer of data outside the EU. Personal data collected from European residents must remain in Europe unless exceptionally strict conditions are met. This creates a fundamental difference between European and American service providers.
When you use Gmail, Google stores your email on servers in the United States—possibly multiple servers in multiple data centers. Those servers are subject to US law, including laws that permit government access to digital communications. FISA Section 702 allows US intelligence agencies to compel American technology companies to provide access to communications of individuals, including non-US citizens, without a warrant. This legal framework exists nowhere in Europe.
European providers like Proton Mail operate under a different model. Data from UK and EU users remains in European data centers, subject to European legal protections. To access this data, a government agency would need to follow European legal procedures, including obtaining judicial warrants and demonstrating specific, narrow legal justification. The practical difference is significant: mass surveillance programs that function routinely in the United States face genuine technical and legal barriers in Europe.
The Right to Be Forgotten and Data Control
GDPR grants individuals the "right to be forgotten"—the ability to request deletion of personal data under certain circumstances. This seems straightforward until you consider how US technology companies operate. Google maintains detailed profiles on billions of people, tracking their search history, location, browsing behavior, and communication patterns. These profiles are used to build advertising targeting systems worth tens of billions of dollars annually. The idea that you can request this data be deleted doesn't align with the fundamental business model.
European providers, by contrast, are structured around data minimization. Proton Mail doesn't log user IP addresses, doesn't track email opens, and retains metadata for the minimum period necessary to operate the service. This isn't because European companies are altruistic—it's because GDPR makes data minimization the legally required approach. When you request deletion, it's a straightforward technical process, not a fundamental threat to the business model.
This principle extends across all European alternatives. Nextcloud (cloud storage), Duck Duck Go (search), Tutanota (email), Jitsi (video conferencing)—each operates on the principle that they should collect the minimum data necessary to provide their service, rather than extracting maximum data for secondary purposes.
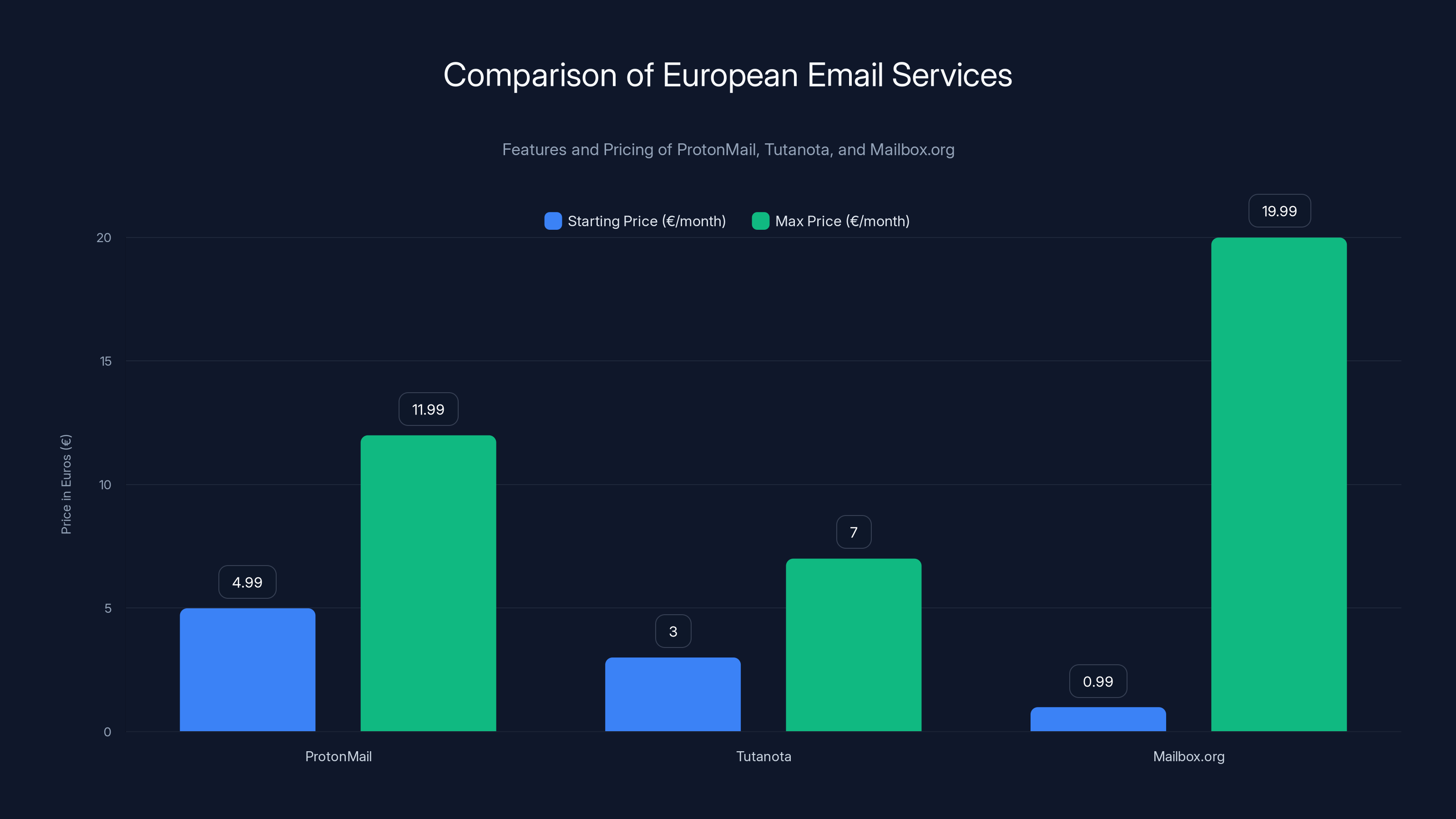
ProtonMail, Tutanota, and Mailbox.org offer competitive pricing with varying features. ProtonMail has the highest starting price, while Mailbox.org offers the most premium plan.
The US Legal Framework: How American Companies Operate Differently
Section 702 of FISA and Mass Surveillance Authority
To understand why Brits prefer European alternatives, it's essential to grasp the legal environment in which US technology companies operate. Section 702 of the Foreign Intelligence Surveillance Act permits the US National Security Agency (NSA) to conduct surveillance of "foreign targets" communicating with individuals in the United States without obtaining individual warrants. The scope is vast: it authorizes surveillance of potentially hundreds of millions of communications annually.
The practical implication: if you're a British citizen emailing a friend in the United States, or if you use a US-based email provider like Gmail, there's a legal pathway for US intelligence agencies to access that communication without following any judicial process. They don't need a warrant. They don't need probable cause. They need only to claim the communication involves a "foreign intelligence" matter. The definition is remarkably broad and includes numerous categories unrelated to genuine national security threats.
This isn't theoretical. Declassified documents revealed that Section 702 was used to conduct surveillance on hundreds of thousands of individuals, including journalists, activists, lawyers, and political figures. The program operates with minimal oversight and no transparent accountability. US technology companies are legally compelled to comply with access requests and are prohibited from publicly disclosing what information they've provided.
European legal frameworks contain no equivalent. The European Court of Human Rights has ruled that mass surveillance is incompatible with fundamental human rights. Member states can conduct targeted surveillance with judicial oversight, but programs enabling indiscriminate mass collection of communications are unconstitutional. This legal distinction creates a genuine, measurable difference in surveillance risk.
The Third-Party Doctrine and Data Broker Ecosystems
US law also recognizes a "third-party doctrine" that permits government agencies to access personal information held by private companies with minimal legal process. If you store your email with Gmail, your location history with Google Maps, your fitness data with Apple Health, and your financial information with an American bank, the government can access this information by compels from the companies rather than your devices. In many cases, no warrant is required—a simple administrative subpoena suffices.
This doctrine enabled the creation of massive data broker ecosystems in the United States. Over 2,500 data brokers operate in the US, accumulating and selling detailed profiles on virtually every American—and many non-Americans. These brokers purchase data from multiple sources: credit card companies, loyalty programs, website tracking, social media platforms, public records, and dozens of other providers. The resulting profiles are remarkably comprehensive, detailing individuals' purchases, location histories, medical conditions, financial situations, religious beliefs, sexual orientations, and political affiliations.
US government agencies, including local police departments, purchase this data legally. They also access it through subpoenas and warrants. The result: a surveillance infrastructure that would be illegal in Europe but is completely routine in the United States. European privacy law explicitly restricts what data can be collected, shared, and traded. US law contains no such restrictions.
The Absence of Baseline Privacy Rights
Fundamentally, the United States lacks a comprehensive federal privacy law. GDPR creates a baseline privacy right for all European residents. The EU e Privacy Directive provides additional protections for electronic communications. The California Consumer Privacy Act, America's closest equivalent, applies only to California residents, covers only certain companies, and contains numerous exceptions and loopholes.
This legal vacuum means that US technology companies can collect, retain, share, and sell personal data with minimal restrictions. Their privacy policies—the documents that ostensibly govern their data practices—are essentially unilateral contracts that companies can modify unilaterally, at any time. Users have no meaningful ability to negotiate terms or opt out entirely without abandoning the service. In Europe, companies cannot process data without explicit consent, and users retain rights to access, correction, and deletion.
The Business Model Divide: Privacy by Design vs. Surveillance Capitalism
How US Tech Companies Monetize User Data
The preference for European alternatives reflects more than legal differences—it reflects incompatible business models. US technology companies, particularly Google, Meta, and Amazon, operate on a business model where user data is the product, not the customer. These companies make their money by aggregating detailed personal profiles from billions of users and selling access to advertisers who want to target their ads with microscopic precision.
Google's business model is particularly instructive. The company generates over $200 billion annually, with 80% coming from advertising revenue. This requires detailed knowledge of user preferences, behaviors, locations, and interests. To achieve this, Google tracks users across the web (through its advertising network and cookies), in their email (through Gmail), on their phones (through Android), in their homes (through Google Home), in their cars (through Android Auto), and increasingly through other devices and services.
This isn't incidental data collection—it's the foundation of the business. Google employs thousands of engineers and data scientists whose job is to extract more data, create more detailed profiles, and enable more precise targeting. The company invests billions annually in technologies that collect more information, track users more precisely, and convert that information into advertising targeting capabilities.
Meta follows the same playbook. Facebook's 2.8 billion users generate an enormous volume of data about their interests, relationships, activities, and locations. Instagram, WhatsApp, and other Meta properties extend this data collection across additional platforms. Meta's €59 billion in annual advertising revenue depends entirely on the detailed user profiles and targeting capabilities derived from this data collection.
European alternatives operate on fundamentally different business models. Proton Mail generates revenue through paid subscriptions, not data monetization. Users pay for the service; Proton Mail doesn't sell their data to advertisers because data monetization is prohibited under GDPR and not part of the business model. The same structure applies to Duck Duck Go, which generates revenue through anonymous affiliate partnerships and non-personalized advertising, not user tracking. Tutanota, Nextcloud, and other European alternatives follow similar subscription or service-based revenue models rather than data monetization.
This business model difference has profound implications. When your chosen technology company profits from data monetization, that company has every incentive to collect more data, share it more widely, and find new ways to extract value from it. When your technology company profits from subscriptions, that company has every incentive to minimize data collection, maximize security, and respect user privacy—because privacy is a feature that justifies the subscription price.
Privacy as a Feature vs. Privacy as a Legal Obligation
In the European model, privacy isn't treated as an optional feature to be toggled on and off—it's the default approach to system design. This philosophy is called "privacy by design," and it's now a legal requirement under GDPR. Every European technology company must consider privacy implications at every stage of design, development, and deployment. Collecting less data is often the default choice because collecting data creates liability and compliance burden.
US companies approach privacy differently. It's treated as a feature that can be toggled on or off, often behind complex settings menus that most users never find or understand. Google offers privacy controls—but only after collecting vast amounts of data by default. Facebook offers privacy settings—but their effectiveness is limited because the company's fundamental business depends on collecting and analyzing data regardless of user preferences. Apple positions itself as privacy-focused—but still retains remarkable data collection capabilities when you examine their ecosystem comprehensively.
This distinction manifests in specific practices. European email providers don't scan email content for advertising purposes. US-based Gmail scans email content and uses that information to build advertising profiles. European cloud storage providers use end-to-end encryption by default, meaning the company itself cannot access your files. US cloud providers can access files and in some cases analyze them for various purposes. European messaging apps don't log metadata that could reconstruct communication patterns. US companies often log metadata and in some cases can access message content.
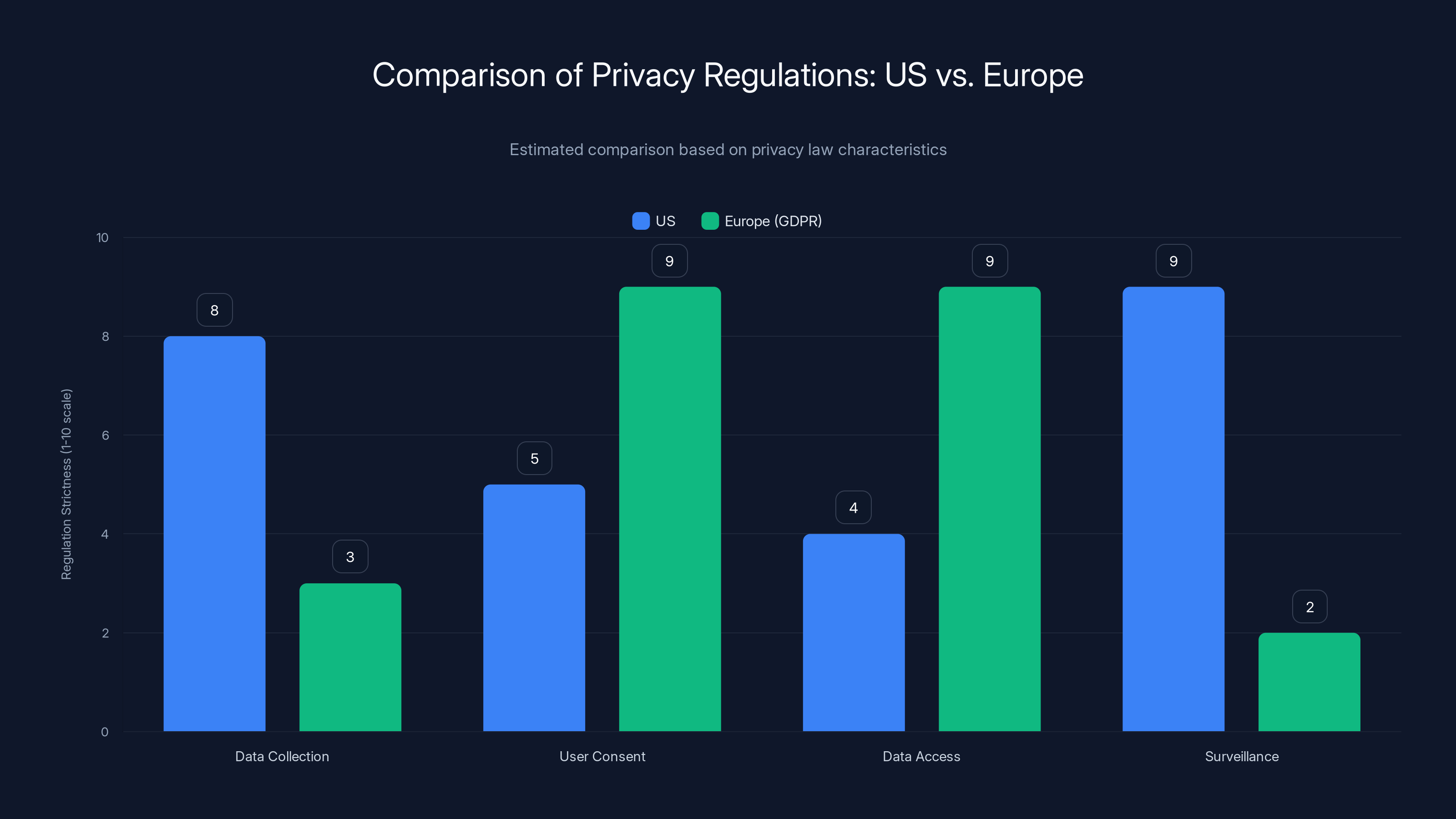
Estimated data shows Europe (GDPR) enforces stricter privacy regulations compared to the US, particularly in user consent and data access.
The Privacy Scandal Timeline: Trust-Breaking Events That Drove the Shift
Cambridge Analytica: When Privacy Violations Became Visible
The privacy exodus from US tech didn't begin with any single event, but the Cambridge Analytica scandal of 2018 served as a turning point where abstract privacy concerns became viscerally real. The scandal revealed that Facebook had enabled a researcher to access personal data from 87 million users without their knowledge or consent. This data—including intimate psychological information, browsing histories, religious beliefs, and political affiliations—was then sold to Cambridge Analytica, a political consulting firm that used it to build psychological targeting profiles for political campaigns.
What made this scandal particularly damaging wasn't just the privacy violation—it was that it revealed the specific mechanism by which privacy violations could occur. Facebook's platform enabled third-party developers to request extensive permissions and collect data from billions of people. Users granted these permissions without understanding what they were authorizing. Facebook had inadequate oversight of how developers used this data. And once collected, the data could be weaponized for psychological manipulation.
The scandal exposed a fundamental hypocrisy: Facebook positioned itself as a free service connecting people—but the "payment" for this service was access to intimate personal data that users never explicitly authorized to be collected, shared, or used. For millions of people, Cambridge Analytica was the moment when they realized they weren't Facebook's customers; they were Facebook's product.
Facebook's response was instructive. The company paid a
Google's Secret Tracking of Incognito Users
Similarly, Google faced repeated privacy scandals that eroded trust. Most notably, investigations revealed that Google was tracking users who used Chrome's "Incognito" mode—a feature users believed was specifically designed to prevent tracking. Despite the feature's name and positioning, Google was logging IP addresses, timestamps, and other identifying information even when users explicitly selected the privacy mode. The company settled a lawsuit for $391.5 million but again made no fundamental changes to its tracking infrastructure.
Further investigations revealed that Google was bypassing Safari's privacy settings to track users on Apple devices, was collecting location data even when location services were disabled, and maintained backdoor tracking mechanisms that continued collecting data even when users believed they had opted out. Each revelation added to the accumulating sense that Google, despite its "Don't be evil" motto, was fundamentally incompatible with actual user privacy.
Apple's Contradictory Privacy Positioning
Even Apple, which positioned itself as privacy-focused, faced credibility damage. The company announced plans to scan i Cloud photos for images matching known child exploitation material (CSAM detection). While the intention—protecting children—was sympathetic, the implementation revealed how surveillance capabilities can be deployed for purposes beyond stated intent. Privacy advocates warned that once such scanning capabilities were built, they could be repurposed for censorship, political suppression, or other malicious purposes.
The proposal was particularly damaging because it revealed that Apple's privacy positioning was conditional—privacy was protected unless Apple decided it wasn't. If Apple would build surveillance capabilities into photos scanning, what else might the company sacrifice privacy for? This undermined Apple's credibility as a privacy champion. The proposal was eventually withdrawn, but the damage to trust persisted.
Meta's Data Sales and Political Manipulation
Meta faced ongoing revelations about political manipulation. Internal documents revealed that Facebook knew its platform was being used to organize violence, enable human trafficking, and spread disinformation—but the company prioritized engagement and advertising revenue over public safety. The "Facebook Papers" revealed that Meta prioritized profit over child safety, promoted divisive content that increased engagement, and failed to enforce its own policies consistently or fairly.
Additionally, investigations revealed that Meta had sold access to user data to device manufacturers, advertisers, and other third parties far more extensively than publicly acknowledged. Users discovered that their behavior on Facebook was being monetized through data sales and shared with partners in ways they never authorized or understood. Each revelation added to the accumulating sense that US tech companies viewed privacy as an obstacle to profit rather than a right to be respected.
Amazon's Invasive Data Collection Practices
Amazon faced scrutiny for its increasingly invasive data collection across its ecosystem. Alexa, Amazon's voice-activated assistant, was found to retain recordings and transcripts of user interactions even when users believed they had disabled recording. Ring cameras, owned by Amazon, were providing data to law enforcement without warrants or transparent process. Amazon's advertising business was using data from shopping, browsing, and device usage to build detailed consumer profiles. For families using Alexa, the extent of data collection was often not fully understood or acknowledged.
The European Regulatory Response: Strengthening Privacy Protections
GDPR Enforcement and Its Impact on Company Behavior
While European regulations were initially seen as bureaucratic burdens, enforcement has proven consequential. European regulators have imposed billions in fines on US technology companies, and these fines are accelerating. The trend signals a shift from theoretical regulation to active enforcement. Companies operating in Europe must genuinely change practices or face escalating penalties.
This enforcement is beginning to alter corporate behavior. Google modified its data collection practices in response to GDPR requirements. Meta announced changes to targeted advertising in response to regulatory pressure. Amazon modified how it shares data with third parties. These aren't enthusiastic changes—they're the minimum required to operate in European markets—but they demonstrate that regulation can force meaningful behavior changes.
The Digital Markets Act and Platform Regulation
Beyond privacy protection, the European Union introduced the Digital Markets Act (DMA), which targets anti-competitive practices by major technology platforms. The DMA prohibits self-preferencing (where platforms favor their own services over competitors), mandates interoperability (where platforms must allow users to switch between services), and requires transparency about algorithmic ranking. These regulations don't directly address privacy, but they reduce the lock-in effects that make leaving US platforms technically difficult or impossible.
The DMA's interoperability requirements mean that users can move data between services more easily. Users can switch email providers without losing the ability to send emails to their contacts on other platforms. They can move messages between instant messaging services. These technical changes reduce the barrier to switching, which in turn increases competitive pressure on US platforms to actually respect privacy to retain users.
The e Privacy Directive and Electronic Communications Protection
Europe's e Privacy Directive provides additional layers of protection beyond GDPR, specifically protecting electronic communications. Websites cannot track users across the web without explicit consent. Electronic communications cannot be intercepted or monitored without legal justification. Email providers cannot analyze email content for advertising purposes. These protections create meaningful barriers to the mass tracking and profiling that characterizes US technology practices.

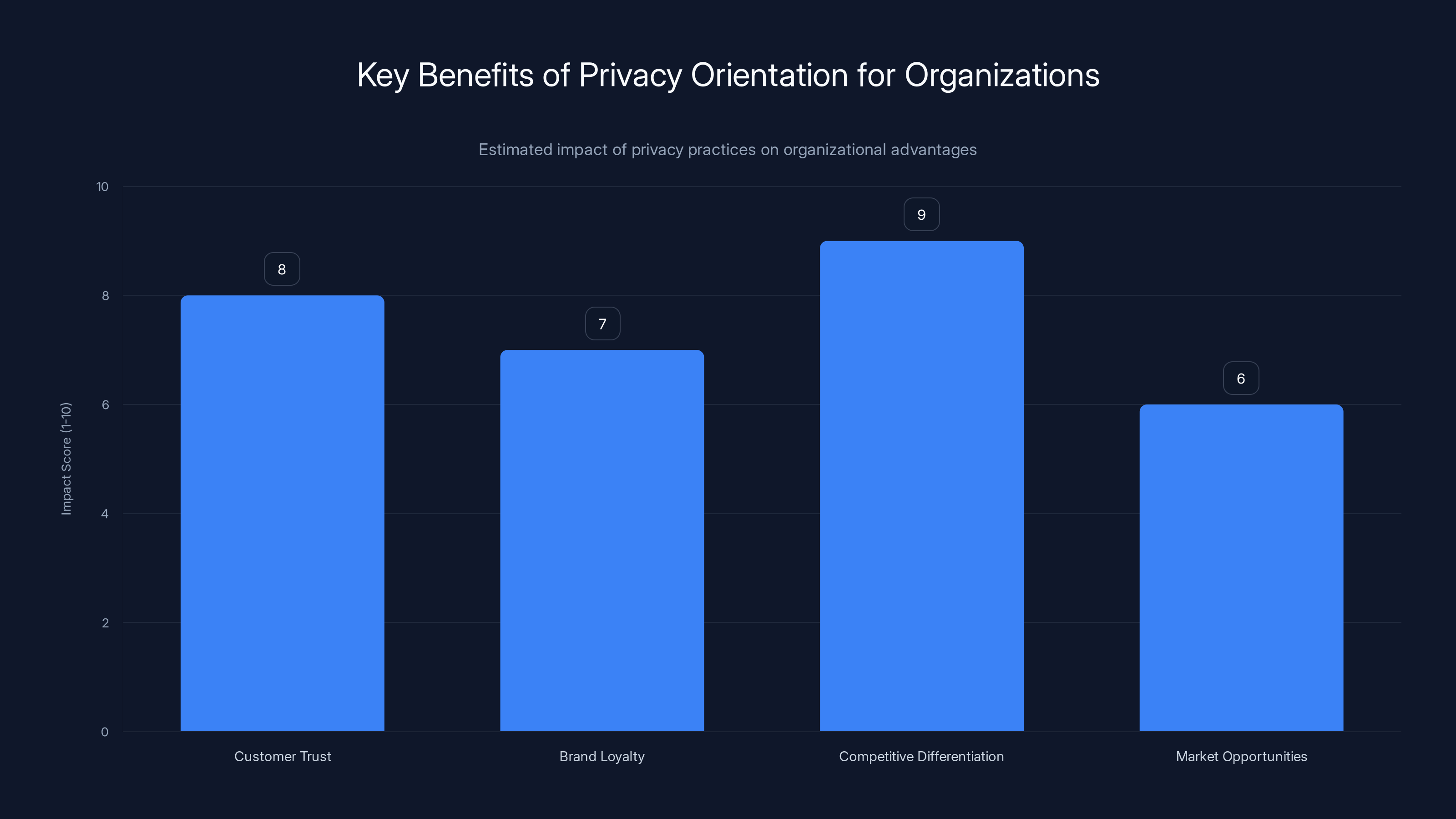
Organizations prioritizing privacy see significant benefits in customer trust, brand loyalty, and competitive differentiation. Estimated data based on privacy trends.
The Technical Architecture Difference: Encryption, Data Residency, and Zero-Knowledge
End-to-End Encryption: What It Means and Why It Matters
European privacy alternatives frequently employ end-to-end encryption, meaning that data is encrypted on users' devices before transmission to company servers, and the company never has access to unencrypted data. This architectural choice has profound implications. Even if a government demands access to data, or if a company's servers are compromised, the data remains protected because the company never possesses unencrypted keys.
Proton Mail exemplifies this approach. When you send an email, it's encrypted on your device before being transmitted to Proton Mail's servers. Proton Mail stores only encrypted data. When the recipient receives the email, it's decrypted on their device. Throughout this entire process, Proton Mail—and any government agency or hacker attempting to access the data—sees only gibberish. This technical architecture makes mass surveillance technically impossible even if legal authority for surveillance existed.
US technology companies generally don't employ end-to-end encryption by default because it conflicts with their business models. Google's servers need to access email content to enable email search, conversation threading, and importantly, to scan content for advertising targeting. Apple's servers need to access cloud data to provide sync across devices and enable cloud backups. These functional requirements demand that data be accessible to the company in unencrypted form.
End-to-end encryption isn't a perfect solution—it does create challenges for certain legitimate functionality like search or backup. But many European alternatives have solved these problems technically. For instance, some encrypted email providers enable searching encrypted data on the client device without transmitting unencrypted data to servers. Others enable encrypted backups that remain inaccessible to the company. These are not insurmountable technical challenges; they're simply different design choices driven by different business models and regulatory requirements.
Zero-Knowledge Proofs and Trustless Architecture
Some European alternatives employ even more sophisticated cryptographic approaches. Zero-knowledge proofs allow companies to verify user information or perform authentication without ever seeing that information. For instance, a zero-knowledge password proof enables you to prove to a service that you know your password without ever transmitting the password to the service's servers. The password remains secret even from the service itself.
This architectural approach extends trust models. Instead of trusting that a company will behave properly with your data, the technical architecture prevents the company from accessing your data in the first place. This removes the need for trust in corporate good behavior. Even if the company wanted to violate privacy, the technical architecture wouldn't permit it.
Data Residency and Geofencing
European alternatives typically store user data in European data centers, subject to European law. This isn't just a policy decision—it's a technical architecture with legal implications. When your data is physically located in Europe, European courts have primary jurisdiction over it. European privacy law applies. Government agencies seeking access must follow European legal procedures.
US companies sometimes maintain European data centers, but this geographic distribution doesn't provide the same protections because US law still applies to data generated by US persons or stored by US companies. Additionally, US law permits the US government to compel access to data even if it's stored outside the United States. European privacy law provides stronger protection regardless of where data is physically stored.
Practical European Alternatives: A Comprehensive Landscape
Email Services: Beyond Gmail
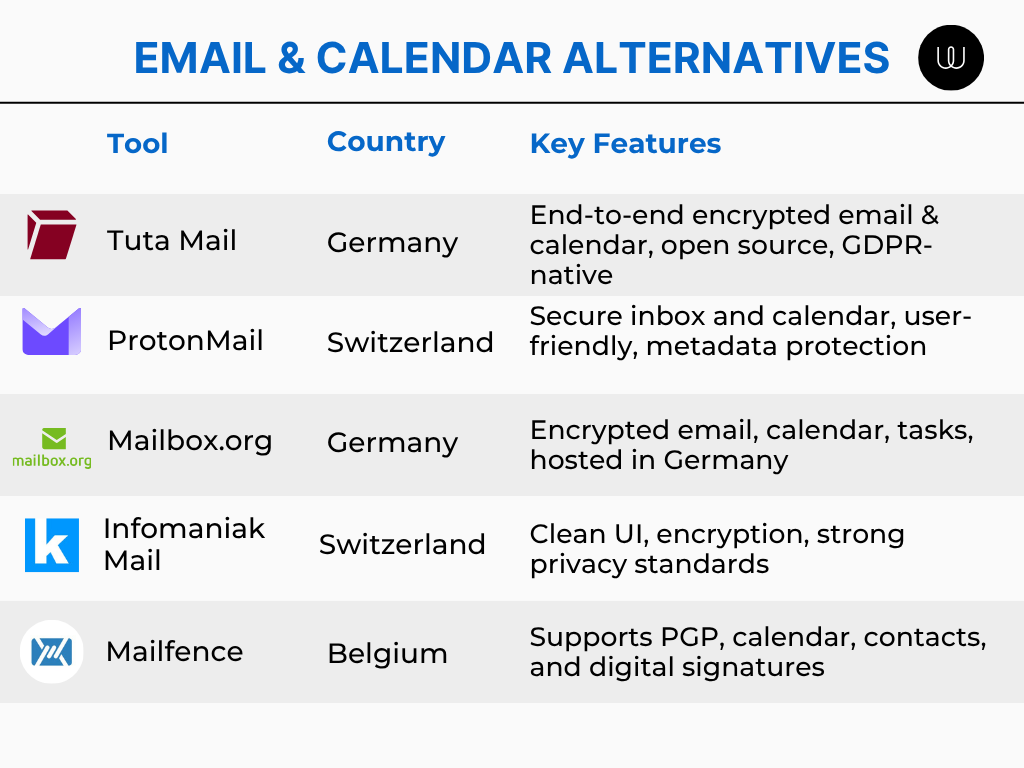
The email provider landscape has transformed with numerous European alternatives gaining traction:
Proton Mail (Switzerland) offers fully encrypted email with end-to-end encryption, zero-knowledge architecture, and data residency in Switzerland. The service starts at free but paid plans ($4.99-11.99/month) include custom domains, additional storage, and enhanced security features. The service has grown from 500,000 users in 2016 to over 100 million registered accounts by 2024, with millions of active users in the UK.
Tutanota (Germany) provides encrypted email with similar security to Proton Mail, plus encrypted calendar functionality. Tutanota is free for basic usage with paid plans at €3-7/month for additional features. The service emphasizes simplicity and default encryption, requiring no configuration for end-to-end security.
Mailbox.org (Germany) offers encrypted email with IMAP/SMTP compatibility, meaning users can access encrypted email through their preferred email client rather than being restricted to web access. Plans start at €0.99/month for basic service up to €19.99/month for premium offerings.
These services demonstrate that encrypted email is technically feasible, user-friendly, and economically viable. The primary barrier to adoption is switching cost—moving email providers requires notifying contacts, migrating existing email, and updating services that use email for authentication.
Search Engines: Privacy-First Information Retrieval
Duck Duck Go (US-based but privacy-focused) has become Europe's fastest-growing search alternative. Despite being US-based, Duck Duck Go employs a privacy-first model: the company doesn't track search history, doesn't correlate searches to identities, and doesn't build user profiles. This contrasts sharply with Google's approach, where every search is logged, correlated to your account, and used to build detailed profiles of your interests and behaviors. Duck Duck Go's market share in the UK grew from 0.5% in 2015 to 5-7% by 2024.
Start Page (Netherlands) functions as a privacy wrapper around Google search results. Users get Google's search quality without Google's tracking. The service removes all identifying information before forwarding searches to Google's servers, returns results without tracking, and enables anonymous proxying of results. While technically still returning Google results, Start Page provides privacy protection that Google doesn't.
Ecosia (Germany) combines privacy-first search with environmental impact. The search engine doesn't track users, doesn't build profiles, and generates revenue from non-intrusive advertising. Importantly, Ecosia plants trees with profits—one tree planted for every search executed. By 2024, Ecosia had planted over 200 million trees, demonstrating that privacy-focused business models can align with positive environmental and social impact.
These alternatives collectively captured 8-12% of European search market share by 2024, with growth accelerating as privacy concerns become more prominent.
Cloud Storage: Encrypted, Privacy-First File Management
Proton Drive (Switzerland) provides encrypted cloud storage where files are encrypted before leaving your device and remain encrypted on Proton's servers. Users cannot only store files securely but share encrypted files without the receiver needing a Proton account—they receive a download link with temporary encryption keys. Plans range from free (1GB) to €5.99/month (200GB) with generous pricing compared to Google Drive.
Nextcloud (Germany) offers an open-source cloud storage platform that organizations and individuals can host on their own servers or through hosted providers. Nextcloud includes file synchronization, sharing, calendar, contacts, and collaborative document editing—essentially a complete office suite equivalent to Google Workspace but with data fully under user control. For organizations prioritizing privacy and data sovereignty, Nextcloud represents an alternative that doesn't require trusting external companies with data.
Tresorit (Hungary) provides encrypted cloud storage specifically designed for business collaboration. Files are encrypted end-to-end, with zero-knowledge architecture ensuring Tresorit employees cannot access user data. The service enables granular permission controls, version history, and collaboration features comparable to Dropbox or Google Drive but with privacy guarantees Dropbox and Google don't provide.
Cloud storage alternatives demonstrate that privacy protection and functionality aren't mutually exclusive. Users can achieve full productivity while maintaining encryption and data control.
Video Conferencing: Encrypted Remote Communication
Jitsi Meet (Germany) provides open-source video conferencing that can be self-hosted or accessed through public instances. Jitsi enables end-to-end encryption for video conferences, requires no account creation, and respects privacy. The service doesn't track participants, doesn't record data, and doesn't monetize user attention. Jitsi represents a complete alternative to Zoom or Google Meet that eliminates privacy concerns entirely.
Proton Pass (Switzerland) combines password management with email aliasing, enabling users to create unique, temporary email addresses for different services without revealing their primary email. This reduces tracking across websites, limits data correlation, and protects email addresses from sales and breaches.
Automation and Workflow Tools
For developers and teams building modern applications, European alternatives to automation platforms increasingly compete with US providers. Runable, for instance, offers AI-powered automation for content generation and workflow automation at $9/month—a fraction of complex enterprise alternatives' costs. While not exclusively European, platforms emphasizing data minimization and privacy-by-design principles align with the privacy-first approach driving the broader migration from US Big Tech.
European alternatives exist across documentation tools, presentation platforms, and reporting solutions. Teams prioritizing privacy and data sovereignty can increasingly maintain full productivity while switching entirely away from US technology platforms.

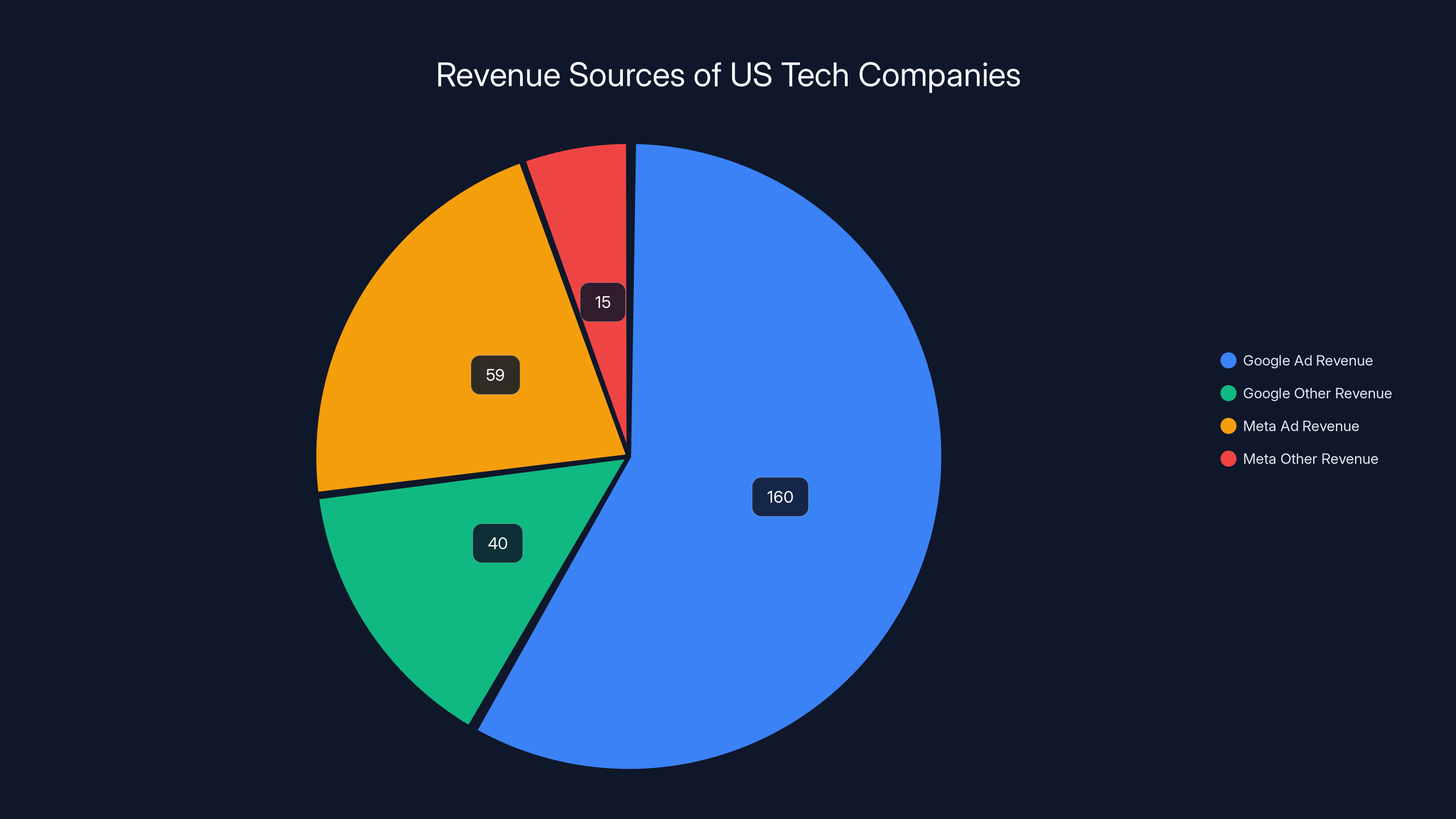
Google and Meta heavily rely on advertising revenue, with Google earning $160 billion and Meta €59 billion from ads annually. Estimated data for Meta's other revenue.
The Switching Process: Practical Steps for Migration
Email Migration: The Primary Barrier
For most people, switching from Gmail to Proton Mail or Tutanota requires managing the email address change. This involves notifying contacts, updating services, and managing dual inboxes during transition. Most common approaches include:
- Create new account with European provider and set up forwarding from Gmail to capture incoming messages
- Notify frequent contacts of new email address through multiple channels
- Update critical services (banks, government agencies, insurance, etc.) systematically
- Export Gmail contacts and calendar for import to new provider
- Maintain Gmail account as fallback for several months during transition
- Export and archive old Gmail messages for potential future reference
- Update email signature to publicize new address
Despite the switching friction, millions of Brits have completed this process. The barrier is inconvenience rather than technical difficulty.
Search Engine Transition: Lowest-Friction Switch
Switching search engines is frictionless compared to email. Users can set Duck Duck Go or Ecosia as the default search engine in their browser with one click. Both search engines function identically to Google search for the vast majority of queries, with identical or better result quality. The only cost is slightly different UI and search features, which most users can learn in minutes.
Browser Selection: Privacy by Default
Browser choice significantly impacts privacy. Chrome is Google's browser, collecting extensive data about browsing behavior, passwords, and browsing history. Firefox, developed by the Mozilla Foundation (non-profit), offers superior privacy protections with minimal data collection by default. Brave combines Firefox-based rendering with aggressive ad and tracker blocking, plus built-in Tor support for anonymous browsing.
Switching browsers is similarly frictionless—users can import bookmarks, passwords, and browsing history from their existing browser, then set the new browser as default.
VPN Services: Securing Connections
Virtual Private Network (VPN) services encrypt internet connections, masking IP addresses and encrypting traffic even when using public Wi-Fi networks. Proton VPN (Switzerland) offers VPN services with end-to-end encryption, no-logging policies, and strong privacy protections. The service starts at free (limited) with paid plans at £3.99-11.99/month. For UK residents concerned about ISP monitoring or public Wi-Fi security, VPN services provide protective infrastructure.
Operating System Choices: The Deepest Level
For technically inclined users, operating system choices represent the deepest commitment to privacy. Linux offers open-source, auditable operating systems from distributions like Ubuntu, Fedora, or Debian. Mobile alternatives like /e/OS or Lineage OS offer privacy-focused Android alternatives that minimize Google integration. These choices represent significant switching costs but offer maximal privacy and data control.

The Business Implications: What This Shift Means for Organizations
Competitive Advantage Through Privacy
For organizations building modern applications or managing customer relationships, privacy orientation increasingly represents competitive advantage. Organizations that prioritize customer privacy—through practices like data minimization, end-to-end encryption, and transparent privacy policies—report higher customer trust, stronger brand loyalty, and competitive differentiation.
British organizations particularly benefit from privacy-forward positioning given the cultural shift toward privacy consciousness. A B2C company that explicitly commits to GDPR compliance, minimal data collection, and European data residency can position privacy as a core competitive advantage. A developer tool company that offers transparent pricing instead of surveillance-based pricing models appeals to organizations prioritizing privacy and cost predictability.
Enterprise Data Sovereignty Concerns
For larger organizations, the concern isn't just individual privacy but organizational data sovereignty. Companies are increasingly unwilling to store strategic data in US cloud providers subject to US law and government access. This has created substantial market opportunities for European cloud providers offering data residency, GDPR compliance, and legal protection against US government access.
Regulatory Compliance as Ongoing Requirement
Organizations operating in Europe are subject to GDPR compliance requirements regardless of where their customers are located. This means that companies serving any UK or European customers must implement GDPR compliance, which is easier when using European tools and service providers rather than fighting with US platforms to achieve compliance.

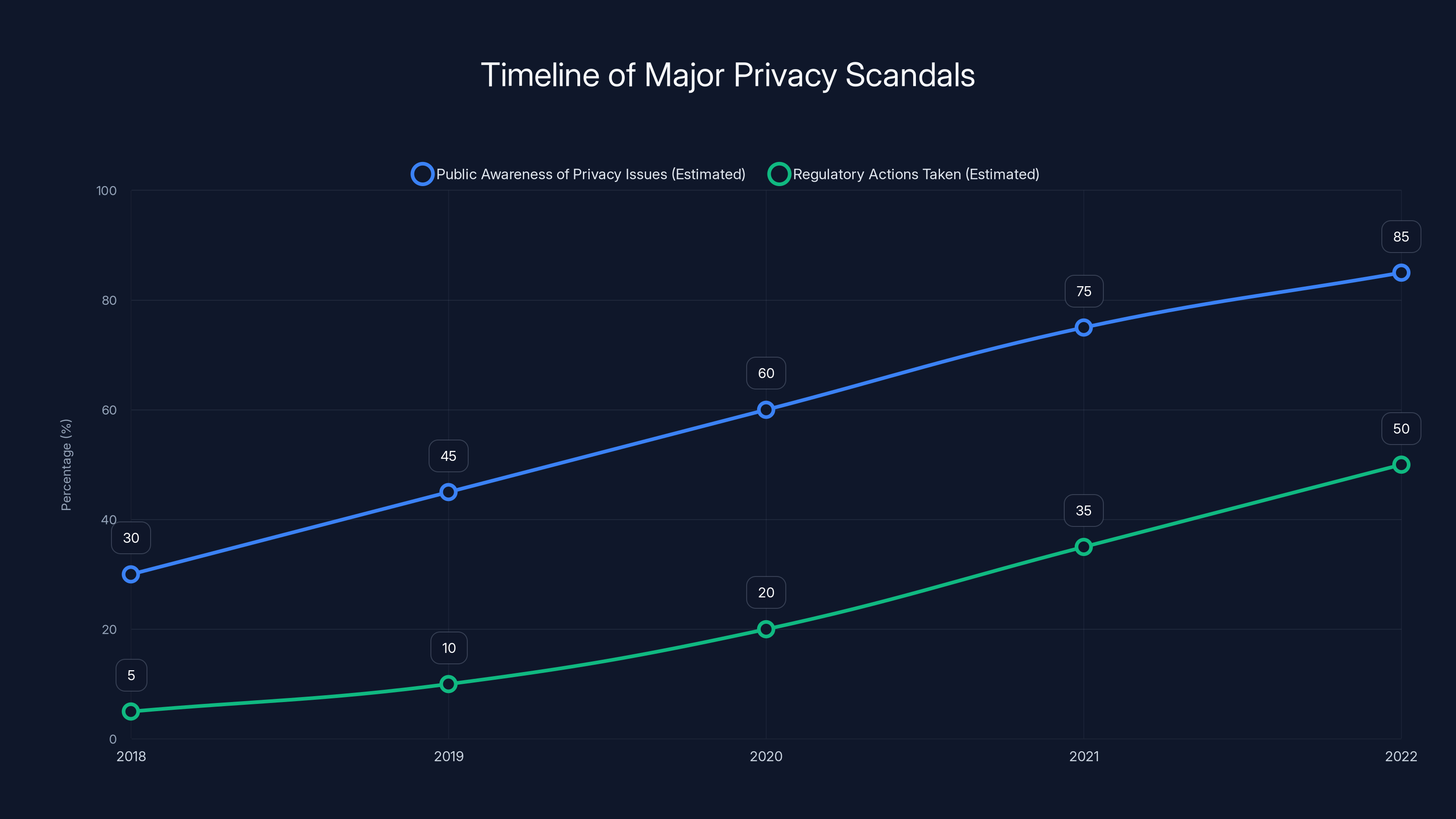
The Cambridge Analytica scandal in 2018 significantly increased public awareness of privacy issues, leading to a rise in regulatory actions over subsequent years. (Estimated data)
The Limitations and Trade-offs: What Privacy Comes With
The Switching Inconvenience
While European alternatives offer superior privacy, switching from entrenched US platforms creates genuine inconvenience. Email migration is tedious, requiring coordination with contacts. Collaborative functionality may differ slightly from familiar US platforms. Customer support is often smaller and slower than US tech giants with massive support organizations. These trade-offs are real, though not insurmountable.
Feature Maturity Differences
Many European alternatives are newer or less feature-rich than established US equivalents. Proton Mail's mobile apps are excellent but less polished than Gmail's app. Jitsi Meet's video conferencing works well but may lack some advanced features of Zoom. Duck Duck Go's search is comprehensive but may occasionally differ from Google's results. These differences are narrowing continuously as European alternatives receive investment and development attention, but they remain meaningful for some use cases.
Ecosystem Fragmentation
US technology companies have successfully created integrated ecosystems where using Gmail means you're encouraged to use Google Drive, Google Photos, Google Calendar, and Chrome browser. Switching to privacy alternatives often means adopting multiple services from different providers rather than one integrated ecosystem. This fragmentation creates complexity—managing multiple accounts, different UIs, different features.
Cost and Subscription Fatigue
Many US services are free (in exchange for data monetization). European alternatives charge subscription fees because they make money from subscriptions rather than data sales. Switching entirely from US tech to European alternatives could involve paying €30-60/month for services that were previously free. For budget-conscious consumers, this represents a meaningful switching cost despite the privacy benefits.
Reduced Integration with Mainstream Services
Many mainstream services integrate deeply with Google and Microsoft ecosystems. Switching to privacy alternatives may require finding integration paths or accepting reduced functionality. Third-party educational platforms integrating with Google Classroom need alternative approaches. HR systems integrating with Microsoft Azure need different directory synchronization. These integration challenges can be significant for organizations.

Future Trends: Where Privacy and Technology Are Heading
Regulatory Expansion Beyond Europe
The GDPR model is increasingly being adopted globally. California's privacy regulations are being expanded. Brazil's Lei Geral de Proteção de Dados (LGPD) mirrors GDPR. India is developing privacy frameworks. This global regulatory trend suggests that privacy-first technology practices will become increasingly mainstream rather than niche, as companies must meet regulations wherever they operate.
AI and Privacy Tensions
Artificial intelligence development increasingly requires massive training datasets, and privacy laws increasingly restrict how personal data can be used for AI training. This creates tension between technological progress and privacy protection. European alternatives are exploring privacy-preserving AI approaches like federated learning (training AI on devices rather than central servers) and differential privacy (adding noise to datasets to prevent re-identification while preserving statistical properties for training). These approaches may allow AI advancement without privacy compromise.
Decentralization and User Control
Decentralized technologies like blockchain are being explored to create systems where users maintain data control without relying on centralized companies. Project Portfolio Decentralized versions of social media, email, and other platforms aim to provide functionality equivalent to Facebook or Gmail but where users own their data and control how it's used. These technologies remain immature but represent long-term evolution toward decentralized, privacy-preserving alternatives.
Zero-Trust Security and Privacy Architecture
Organizations are increasingly adopting zero-trust security models where no component is inherently trusted and access requires continuous verification. Extended to privacy, zero-trust privacy architectures would assume that companies cannot be trusted with data and design systems preventing data access even by the company itself. This represents both philosophical and practical evolution toward stronger privacy protections.

Making the Transition: A Practical Decision Framework
Assessing Your Privacy Concerns
Not everyone needs complete privacy protection at all costs. Some considerations for assessing your situation:
- Risk exposure: Do you use platforms that collect politically sensitive information? Financial details? Health information? Higher-sensitivity data warrants stronger privacy protection.
- Threat model: Are you concerned about government surveillance? Corporate data brokers? Hackers? Different threats require different protections.
- Cost tolerance: Are you willing to pay subscription fees? Accept reduced features? Spend time learning new tools? Privacy sometimes requires trade-offs.
- Technical comfort: Are you comfortable managing multiple services? Troubleshooting configuration issues? Some privacy alternatives require more technical engagement.
Phased Migration Approach
Most people benefit from phased migration rather than attempting complete switch overnight:
- Phase 1: Low-friction changes - Switch search engine to Duck Duck Go, browser to Firefox, set up Proton VPN
- Phase 2: Communication tools - Switch to encrypted email and messaging gradually, maintaining dual systems initially
- Phase 3: Storage and productivity - Migrate documents, photos, calendar to encrypted alternatives
- Phase 4: Complete transition - Fully decommission US platforms once all data and contacts are migrated
Hybrid Approaches
You don't need to choose between complete privacy or complete convenience. Hybrid approaches include:
- Using European alternatives for sensitive data while maintaining US platforms for less sensitive usage
- Encrypting data before uploading to US cloud services
- Using VPNs to mask activities on mainstream platforms
- Creating separate accounts for different purposes
These approaches don't provide complete privacy but offer meaningful improvement over no privacy measures.
Conclusion: Privacy as a Fundamental Right
The migration of British consumers from US Big Tech to European alternatives isn't a fringe movement of privacy extremists—it's a mainstream cultural shift driven by basic discomfort with surveillance capitalism. The 57% of UK residents willing to switch to European alternatives represent millions of people recognizing that their data has value and that they deserve control over how that value is extracted and used.
This shift is driven by four fundamental factors. First, regulatory frameworks: GDPR and European data protection laws have created legal requirements and enforcement mechanisms that actually constrain corporate surveillance. US privacy law provides no comparable protection. Second, business models: European alternatives succeed by offering subscriptions and services rather than data monetization, removing the economic incentive for maximum data extraction. Third, technical architecture: European alternatives employ encryption, zero-knowledge approaches, and privacy-by-design principles that make surveillance technically difficult even if it were legally permitted. Fourth, documented violations: Repeated scandals at Google, Meta, Amazon, and other US platforms have eroded trust and demonstrated that companies cannot be relied upon for voluntary privacy protection.
For individuals, the decision to switch involves real trade-offs: inconvenience of migration, subscription fees, potentially reduced feature maturity, and ecosystem fragmentation. But for millions of Brits, these trade-offs are increasingly acceptable when the alternative is maintaining participation in surveillance systems they find ethically unacceptable.
For organizations building modern applications or managing customer data, the privacy migration represents both challenge and opportunity. Challenge, because serving customers increasingly demands privacy-first approaches and GDPR compliance. Opportunity, because organizations that commit genuinely to privacy can differentiate competitively in increasingly privacy-conscious markets.
The trend is clear: privacy is no longer a niche concern. It's becoming a mainstream expectation. The companies, platforms, and tools that adapt first to provide genuine privacy protection while maintaining functionality and usability will capture growing market share from incumbents clinging to surveillance business models. The next decade will likely see privacy-focused European alternatives significantly expand their market presence, while US Big Tech either adapts its practices or cedes market share to privacy-first competitors.
For British consumers, the path forward is clear: alternatives exist, switching is feasible, and privacy protection is increasingly achievable without sacrificing functionality. The great tech migration from US Big Tech is not a temporary fad—it's the beginning of a fundamental restructuring of technology markets around privacy rather than surveillance.

FAQ
What is GDPR and why does it matter for privacy?
The General Data Protection Regulation is European privacy law that fundamentally restricts how personal data can be collected, processed, and used. GDPR requires companies to minimize data collection, obtain explicit consent before processing data, enable users to access and delete their data, and implement privacy by default. Unlike US privacy law, which is fragmented and permissive, GDPR creates enforceable baseline rights for all European residents and applies to any company processing their data, regardless of where the company is located. This legal framework explains why European alternatives offer superior privacy protection—compliance is legally mandatory rather than voluntary.
How does end-to-end encryption work and why can't companies access encrypted data?
End-to-end encryption uses mathematical algorithms to encode data on users' devices before transmission to company servers. The company receives only encrypted gibberish and lacks the mathematical keys needed to decrypt it. Even if a government demands access to the data, the company cannot provide unencrypted data because the company never possessed it. For example, Proton Mail encrypts your email on your device before transmitting it to Proton Mail's servers. Throughout the entire process—storage, transmission, display on recipient's device—only you and the recipient possess the keys to decrypt the message. This architecture makes mass surveillance technically impossible even if legal authority for surveillance existed.
What are the main differences between US and European privacy approaches?
US technology companies operate under minimal privacy regulation and business models that profit from data monetization. Companies collect vast amounts of personal data, build detailed user profiles, and sell access to advertisers or data brokers. US law permits government surveillance through programs like FISA Section 702 that enable mass surveillance without individual warrants. European alternatives operate under GDPR, which prohibits data monetization, requires data minimization, and restricts government surveillance to cases with judicial oversight and specific justification. The practical difference: US companies extract maximum data for maximum profit; European companies minimize data collection as a core business principle.
Why are Brits switching away from US platforms like Google and Facebook?
The migration is driven by multiple factors: Cambridge Analytica revealed how Facebook data was weaponized for political manipulation; repeated privacy scandals showed companies systematically violated user privacy; the regulatory framework in the US enables mass surveillance while European law restricts it; and survey research found 57% of UK residents would prefer European alternatives. Fundamentally, people are increasingly uncomfortable with surveillance capitalism business models where their data is the product, and they're recognizing that alternatives exist offering better privacy protection at acceptable trade-off costs.
What are the best European alternatives to Gmail?
Proton Mail (Switzerland) is the most popular encrypted email alternative with end-to-end encryption, data residency in Switzerland, and free and paid plans. Tutanota (Germany) offers similar encryption with emphasis on simplicity and includes encrypted calendar functionality. Mailbox.org (Germany) provides encrypted email compatible with standard email clients. Each provides end-to-end encryption unavailable with Gmail, though migration requires notifying contacts and updating services. The primary barrier is switching inconvenience rather than technical difficulty or capability gaps.
Is it realistic to completely switch away from US technology platforms?
Complete switching is technically feasible and increasingly practical but requires accepting trade-offs. Users can switch to European email, cloud storage, search engines, browsers, and communication tools. However, many mainstream services integrate deeply with Google and Microsoft ecosystems, requiring alternative integration approaches. Feature maturity of some European alternatives may be slightly behind established US platforms. Subscription fees apply where services were previously free. For individuals, phased migration approaches often work well. For organizations, complete switching often requires multiple vendors rather than integrated ecosystems. The question isn't whether switching is possible but whether the privacy benefits justify the switching costs for your specific situation.
How does privacy protection affect productivity and functionality?
Modern European alternatives have closed the functionality gap significantly. Proton Mail offers email search, conversation threading, and advanced features comparable to Gmail. Jitsi Meet provides video conferencing equivalent to Zoom. Proton Drive or Nextcloud offer file storage and synchronization matching Google Drive. Duck Duck Go returns search results competitive with Google. In most cases, privacy protection and productivity are compatible—you're not sacrificing meaningful functionality for privacy. The trade-offs are more subtle: different user interfaces requiring learning, potential feature differences in specific use cases, and ecosystem fragmentation when using multiple services rather than one integrated platform.
What is zero-knowledge architecture and how does it enhance privacy?
Zero-knowledge architecture uses advanced cryptography to enable services to operate without accessing unencrypted user data. For example, a zero-knowledge password proof allows you to prove to a service that you know your password without transmitting the password to the service's servers. Applied across services, zero-knowledge approaches prevent companies from accessing data even if they wanted to violate privacy. This removes the need to trust companies with data—the technical architecture prevents access regardless of corporate good intentions or legal compulsion. Services like Proton Mail and Proton Drive employ zero-knowledge architecture to prevent even Proton employees from accessing user data.
How does data residency affect government access to data?
Data residency—storing data physically in specific geographic locations—determines which legal frameworks apply. Data stored in European data centers is subject to European law and legal procedures. Governments seeking access to this data must follow European legal processes, including obtaining judicial warrants and demonstrating specific legal justification. Conversely, data stored in US data centers is subject to US law, which permits government agencies to compel access through FISA Section 702 and administrative subpoenas without individual warrants. This distinction is not purely theoretical—it has genuine implications for surveillance risk. European data residency provides meaningful legal protection against surveillance that doesn't exist for data in the US.
What are the costs of switching to European alternatives?
Switching costs include: subscription fees ($30-60/month for email, cloud, VPN, and other services where US alternatives were free), time spent migrating data and notifying contacts, learning new interfaces and workflows, and potential reduced feature maturity in specific use cases. For some users, these costs are acceptable or even minimal—setting a search engine to Duck Duck Go takes seconds and incurs no subscription fees. For users wanting complete privacy protection across all services, costs accumulate. The question isn't whether switching is free—it's whether the privacy benefits justify the switching costs for your specific circumstances and risk tolerance.
What does the future of privacy look like as more people make this switch?
As privacy consciousness increases and regulatory frameworks expand globally, privacy-first approaches are becoming mainstream rather than niche. We're likely to see expansion of privacy regulations beyond Europe as other regions adopt GDPR-like frameworks. We'll likely see continued growth in European technology alternatives as they gain competitive advantage through privacy differentiation. We're seeing tensions between AI development needs and privacy restrictions resolve toward privacy-preserving approaches like federated learning. Most significantly, we're likely to see fundamental business model shifts where more technology companies compete on privacy and functionality rather than on data monetization capabilities. The next decade will likely see privacy transform from a trade-off requiring compromise into a standard feature accompanying robust functionality.

Key Takeaways
- 57% of UK residents would switch to European technology alternatives, signaling a mainstream cultural shift away from surveillance capitalism toward privacy-first approaches
- GDPR creates legal baselines for privacy that don't exist in US law, requiring companies to minimize data collection, obtain consent, enable user rights, and implement privacy by design
- European alternatives now match US platforms in functionality while providing superior privacy through end-to-end encryption, zero-knowledge architecture, and data minimization
- Business model differences explain privacy differences: US companies profit from data monetization while European alternatives profit from subscriptions, removing economic incentives for maximum data extraction
- Technical barriers to switching have largely been eliminated through infrastructure development and phased migration approaches, leaving convenience and switching costs as primary obstacles
- Privacy protection is increasingly competitive advantage for both organizations and individuals, as privacy consciousness becomes mainstream and regulatory requirements expand globally
- Hybrid and phased approaches offer practical middle ground between complete switching and maintaining current practices, allowing individuals and organizations to improve privacy incrementally
Related Articles
- AI Data Privacy Paradox: Sovereign Infrastructure Solutions 2025
- VMware Exit Strategy: Turn Vendor Lock-In Into Competitive Advantage
- Privacy-by-Design 2026: The AI & Blockchain Shift
- WhatsApp Alternatives for Android 2025: Complete Guide & Comparisons
- Confer: Privacy-First ChatGPT Alternative by Moxie Marlinspike [2025]




