Hackers Exploiting WhatsApp and Cloud Tools for Silent Computer Takeovers [2025]
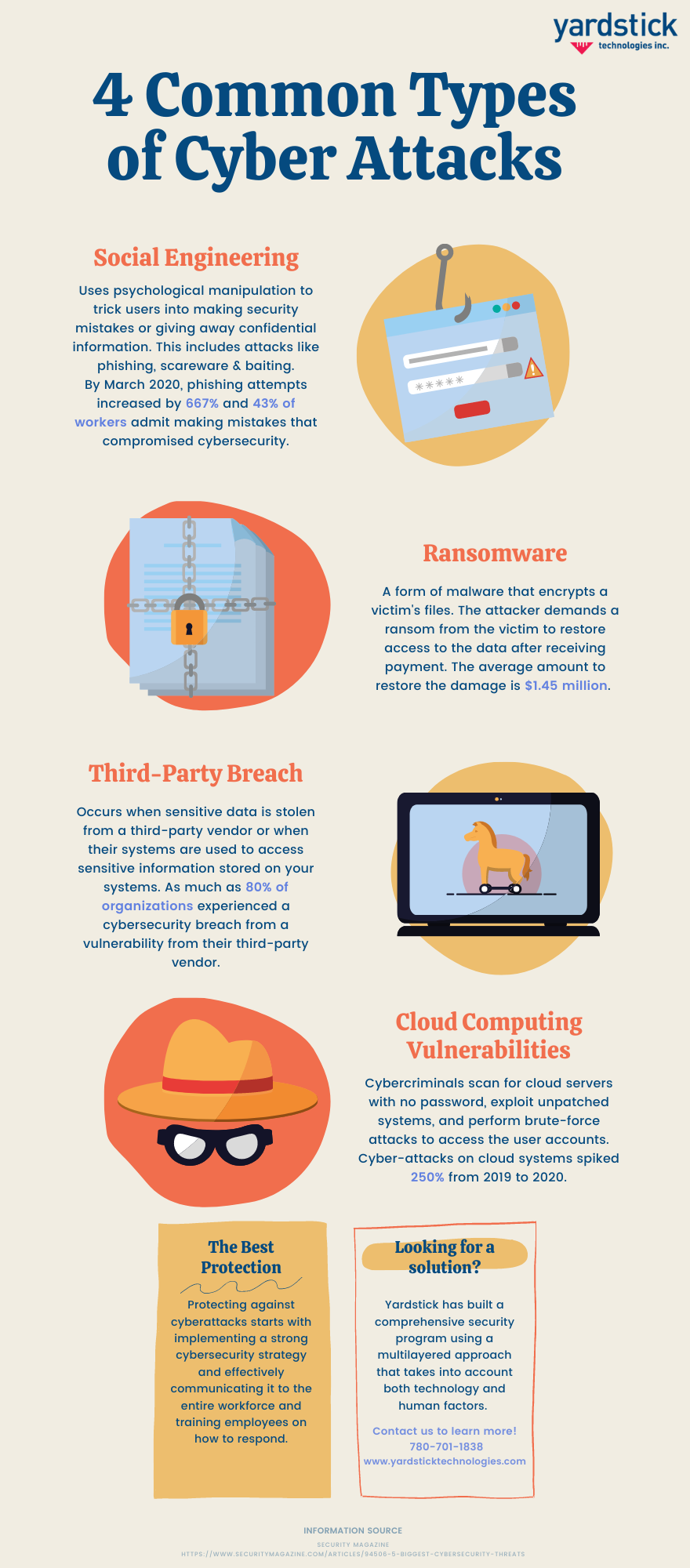
In the constantly evolving landscape of cybersecurity, hackers are always on the lookout for new vulnerabilities and exploits. Recently, there’s been a surge in cyberattacks leveraging popular messaging apps like WhatsApp and cloud-based services to silently take over computers. This article dives deep into these threats, offering practical insights and strategies to mitigate risks.
TL; DR
- WhatsApp and cloud services are being used in tandem to launch stealthy cyberattacks. According to Forbes, these platforms are increasingly targeted due to their widespread use.
- Attackers exploit the trust in these platforms to distribute malicious scripts and files. As noted by Microsoft, attackers use trusted platforms to reduce visibility and increase the likelihood of successful execution.
- Effective cybersecurity requires vigilance, advanced threat detection, and user education. Business.com emphasizes the importance of comprehensive security measures in safeguarding business operations.
- Future trends point towards more sophisticated attacks targeting integrated services. A CYFIRMA report predicts an increase in sophisticated cyber threats.
- Organizations must invest in comprehensive security measures to safeguard their systems. As highlighted by Wiz.io, investment in AI-driven security solutions is crucial for future-proofing against cyber threats.
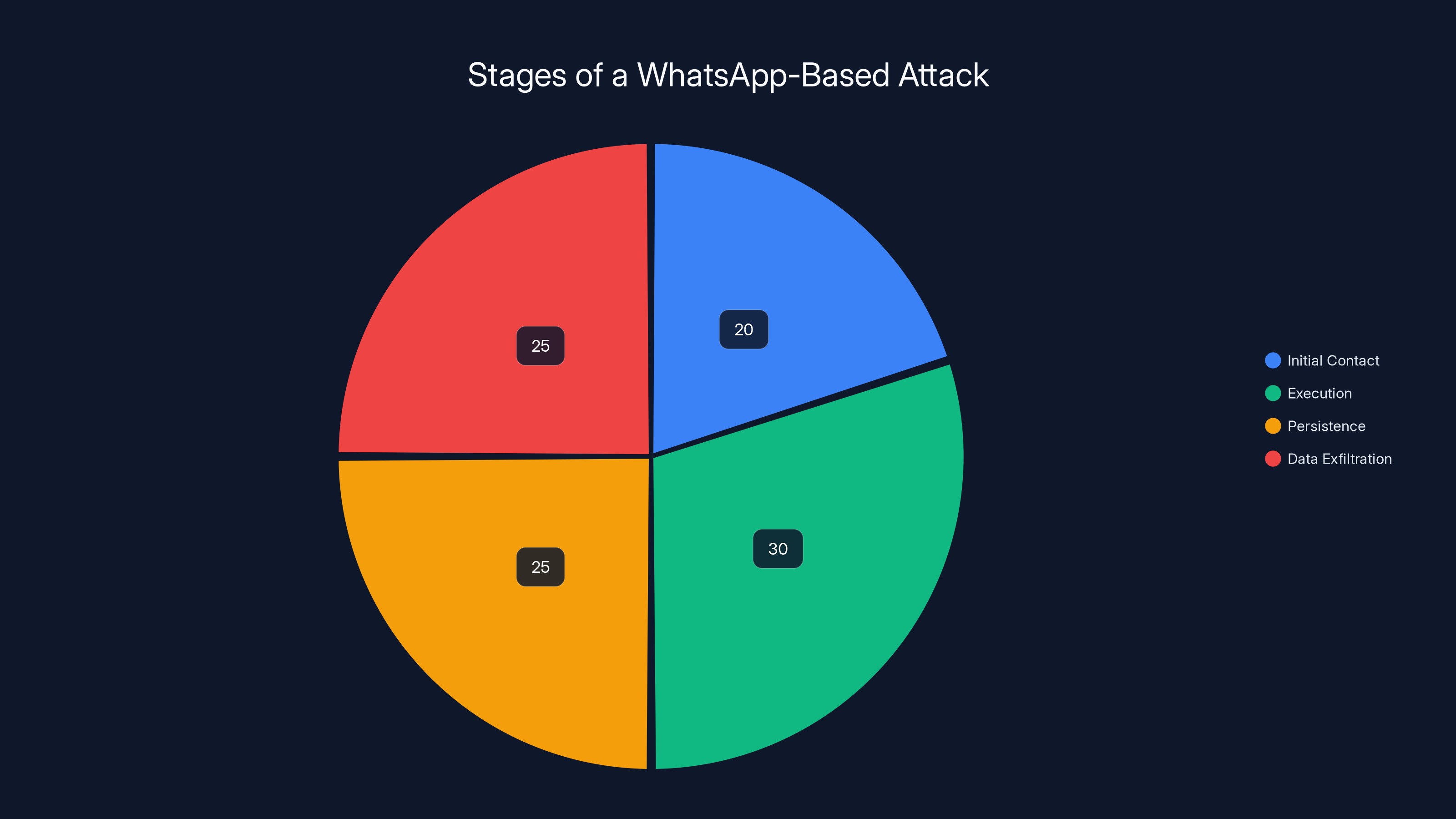
Estimated data shows that execution and data exfiltration are the most time-consuming stages of a WhatsApp-based attack.
The New Frontier in Cyber Threats
The Rise of Cloud-Based Attacks
Cloud services have become integral to modern business operations. They offer scalability, convenience, and cost savings. However, they also present new security challenges. Hackers have begun exploiting these platforms to hide malicious activities, leveraging their reputation and widespread use to bypass traditional security measures, as reported by Trend Micro.
Why WhatsApp?
WhatsApp is one of the most popular messaging apps worldwide, boasting over 2 billion users. Its ubiquity and the trust it commands make it an attractive target for cybercriminals. By embedding malicious payloads within seemingly innocuous messages, attackers can exploit the app’s functionality to infiltrate users’ devices, as detailed in Microsoft's security blog.
How Attackers Use Cloud Services
Hackers utilize cloud-based tools to host malicious files, reducing the likelihood of detection. These files are often disguised as legitimate documents or applications, tricking users into downloading them. Once executed, they can deliver a variety of payloads, from keyloggers to ransomware, as explained by Aikido.

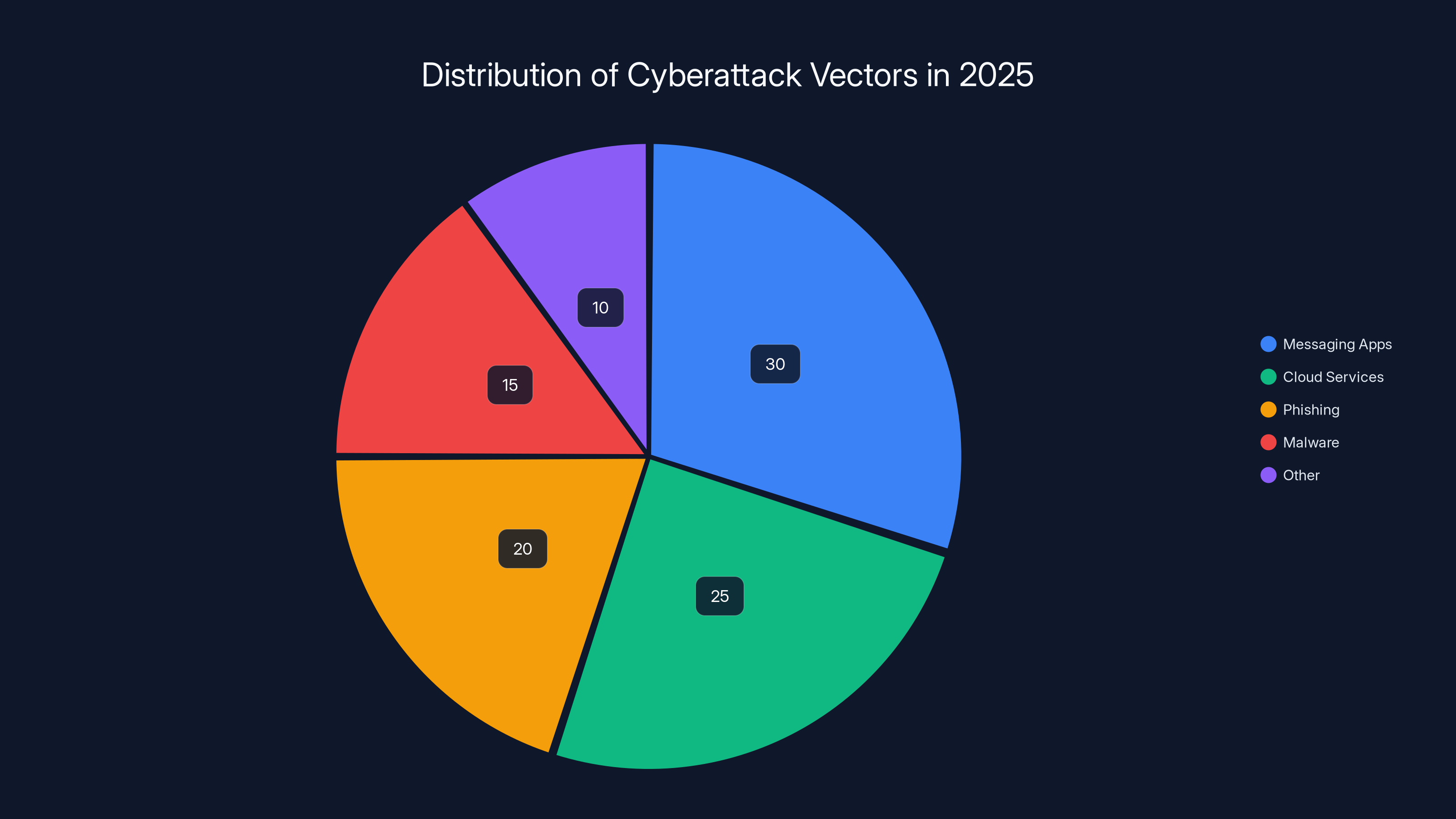
Messaging apps and cloud services are estimated to account for 55% of cyberattack vectors in 2025, highlighting their growing role in cybersecurity threats. Estimated data.
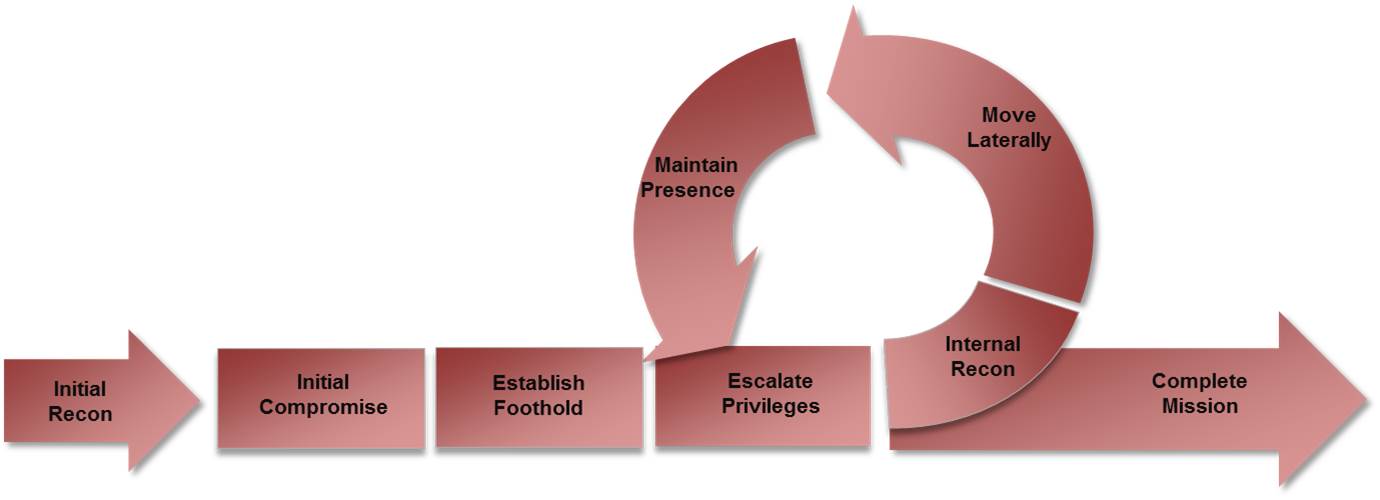
Anatomy of a WhatsApp-Based Attack
Step 1: Initial Contact
The attack usually starts with a seemingly harmless message sent through WhatsApp. It might contain a link to a cloud-hosted file or a direct attachment, such as a VBS script or MSI file, as described in The Hacker News.
Step 2: Execution
Once the user downloads and opens the file, the malicious script executes. This script can perform various tasks, such as establishing a backdoor, stealing credentials, or encrypting files, as noted by Recorded Future.
bash# Example of a simple VBS script used in attacks
Set Wsh Shell = Create Object("WScript. Shell")
Wsh Shell. Run "cmd.exe /c echo Malicious Command", 0, True
Step 3: Persistence and Data Exfiltration
Attackers often deploy persistence mechanisms to ensure their malware survives reboots. They also use encrypted channels to exfiltrate data to their command-and-control servers, often hosted on reputable cloud platforms to avoid suspicion, as highlighted by Microsoft.

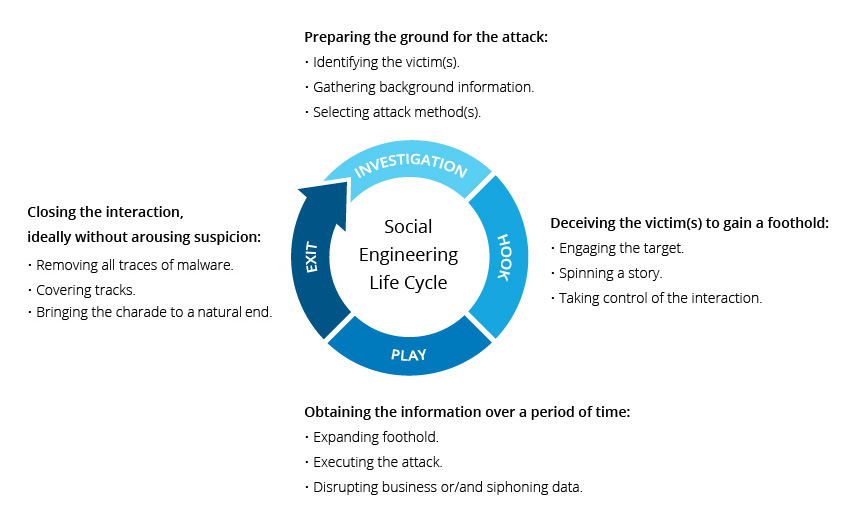
The Role of Social Engineering
Social engineering is a critical component of these attacks. Cybercriminals craft convincing messages that encourage users to click links or download files. Common tactics include:
- Impersonating trusted contacts or organizations
- Creating a sense of urgency or panic
- Offering fake rewards or incentives
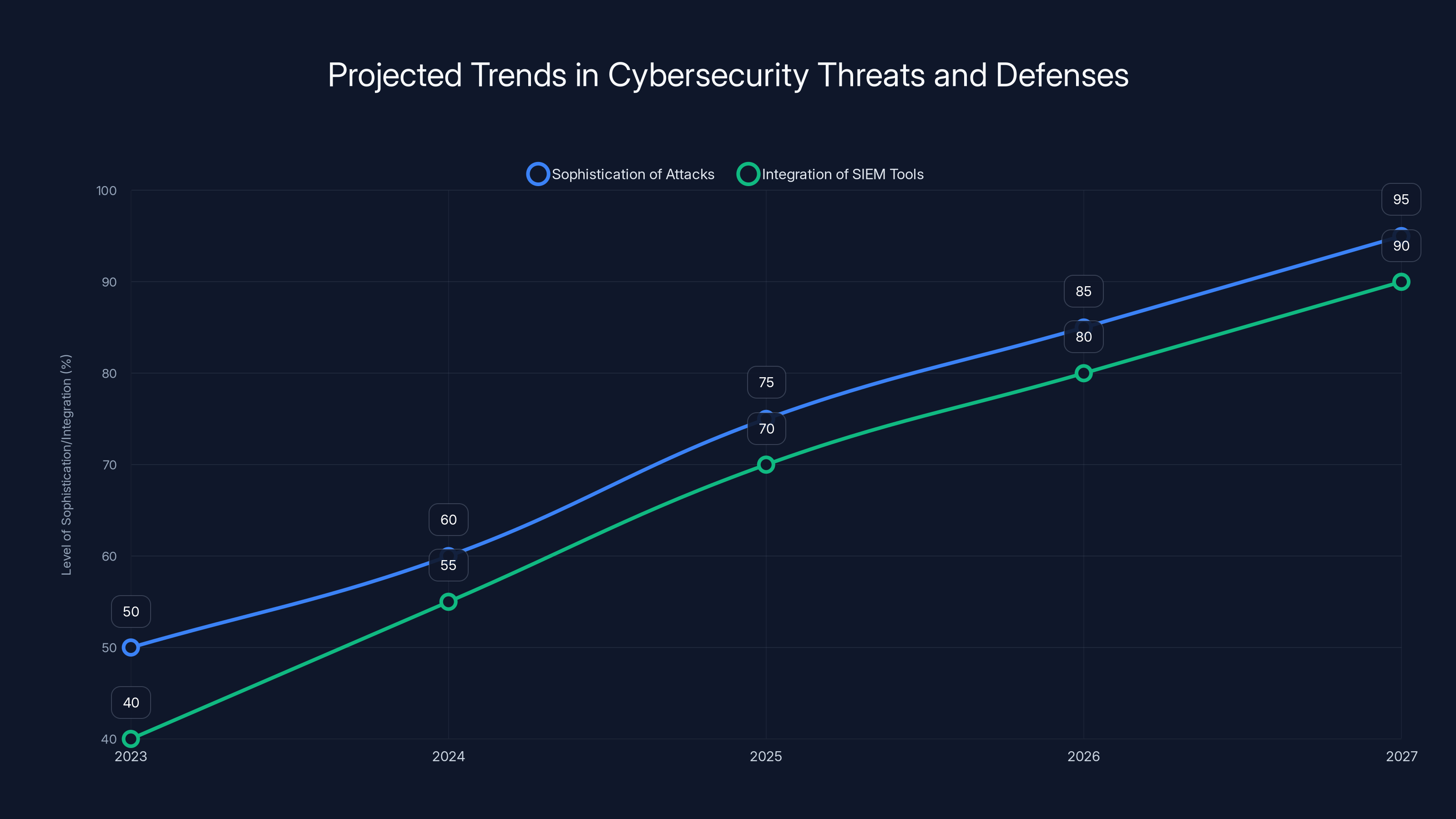
The sophistication of cyber attacks and the integration of SIEM tools are both expected to increase significantly over the next five years. (Estimated data)
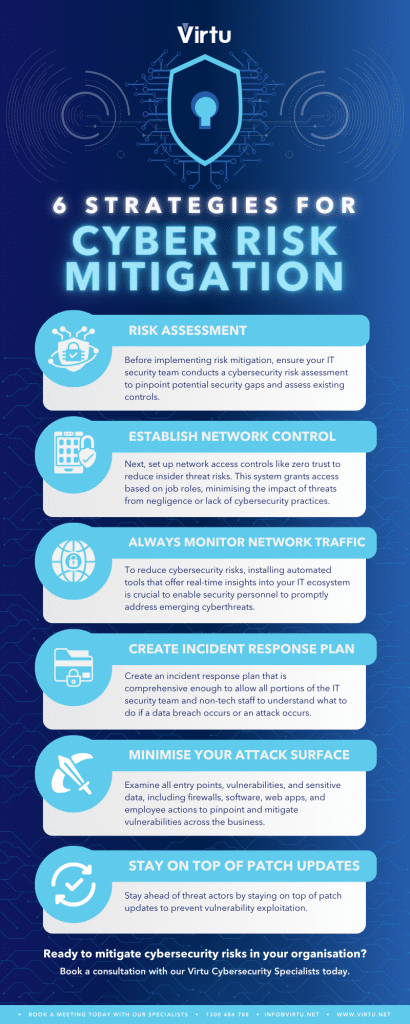
Mitigating the Threat
Implementing Advanced Threat Detection
Organizations must deploy advanced threat detection systems that can identify and neutralize malicious activities in real-time. These systems should leverage machine learning to adapt to new threats and reduce false positives, as recommended by Wiz.io.
Educating Users
User education is paramount in preventing successful cyberattacks. Organizations should conduct regular training sessions to inform employees about the latest threats and best practices for identifying suspicious activities, as emphasized by Business.com.
Strengthening Authentication
Implementing multi-factor authentication (MFA) adds an extra layer of security. Even if attackers gain access to credentials, MFA can prevent unauthorized access, as noted by Forbes.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities and ensure compliance with security policies. These audits should include penetration testing and vulnerability assessments, as advised by CYFIRMA.
Future Trends in Cybersecurity
Increasing Sophistication of Attacks
As cybersecurity defenses improve, attackers will develop more sophisticated methods to bypass them. Expect to see increased use of artificial intelligence and machine learning by both attackers and defenders, as predicted by Wiz.io.
Integration of SIEM Tools
Security Information and Event Management (SIEM) tools will become more integrated into cloud services, providing real-time insights and automated responses to security incidents, as noted by Recorded Future.
Conclusion
In the digital age, cybersecurity is not optional—it’s a necessity. As hackers continue to innovate, leveraging trusted platforms like WhatsApp and cloud services to conduct attacks, organizations must remain vigilant. By implementing robust security measures and fostering a culture of awareness, businesses can protect themselves against these evolving threats, as emphasized by Microsoft.
FAQ
What are cloud-based attacks?
Cloud-based attacks exploit vulnerabilities in cloud services to conduct malicious activities, often by leveraging their trusted reputation to bypass security measures, as explained by Trend Micro.
How can WhatsApp be used in cyberattacks?
Hackers use WhatsApp to distribute malicious files or links, exploiting the app’s trust and widespread use to reach a large audience, as detailed by Microsoft.
What is the role of social engineering in these attacks?
Social engineering tricks users into performing actions that compromise security, such as clicking malicious links or downloading harmful files, as noted by Imperva.
How can organizations protect themselves from these threats?
Implement advanced threat detection, educate users, use multi-factor authentication, and conduct regular security audits to mitigate risks, as advised by Business.com.
What future trends should we expect in cybersecurity?
Expect more sophisticated attacks using AI, greater integration of SIEM tools, and increased focus on cloud security, as predicted by Wiz.io.
Why is user education important in cybersecurity?
Educated users are less likely to fall for social engineering tactics, reducing the risk of successful attacks, as emphasized by Business.com.
Key Takeaways
- WhatsApp and cloud services are being exploited for stealthy cyberattacks.
- Attackers use trusted platforms to distribute malicious scripts.
- Organizations need advanced threat detection and user education.
- Future trends include more sophisticated AI-driven attacks.
- Comprehensive security measures are crucial for protection.
Related Articles
- Beware: How Hackers Exploit LinkedIn's Job Alerts to Steal Your Login Details [2025]
- Stolen Session Cookies: The Hidden Threat to Account Security [2025]
- Anthropic Teams Up With Its Rivals to Keep AI From Hacking Everything | WIRED
- Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]
- Stay Safe from Deepfakes: Expert Steps to Verify Before You Act [2025]
- Inside the Shadowy World of Modern Scam Factories: Lessons from a Bombed Casino Near the Cambodia–Thailand Border [2025]
![Hackers Exploiting WhatsApp and Cloud Tools for Silent Computer Takeovers [2025]](https://tryrunable.com/blog/hackers-exploiting-whatsapp-and-cloud-tools-for-silent-compu/image-1-1775603068232.jpg)



