How AI Tools Empower North Korean Hackers to Steal Millions [2025]
The world of cybersecurity is no longer just about firewalls and antivirus software. The rise of AI has introduced a new paradigm, where artificial intelligence not only aids in defense but also equips cybercriminals with unprecedented capabilities. North Korean hackers, often considered mediocre due to their reliance on state-sponsored resources rather than raw skill, are leveraging these AI tools to commit large-scale cryptocurrency thefts and more. Let's dive into how AI is reshaping the landscape of cybercrime and what this means for the future of cybersecurity.
TL; DR
- AI tools are democratizing cybercrime, making it accessible to less skilled hackers.
- North Korean hackers are using AI to automate and enhance malware campaigns.
- Credential-stealing malware has been deployed on over 2,000 computers.
- Cryptocurrency theft is a primary target, with millions stolen.
- The future of cybersecurity needs a focus on AI-driven defense mechanisms.
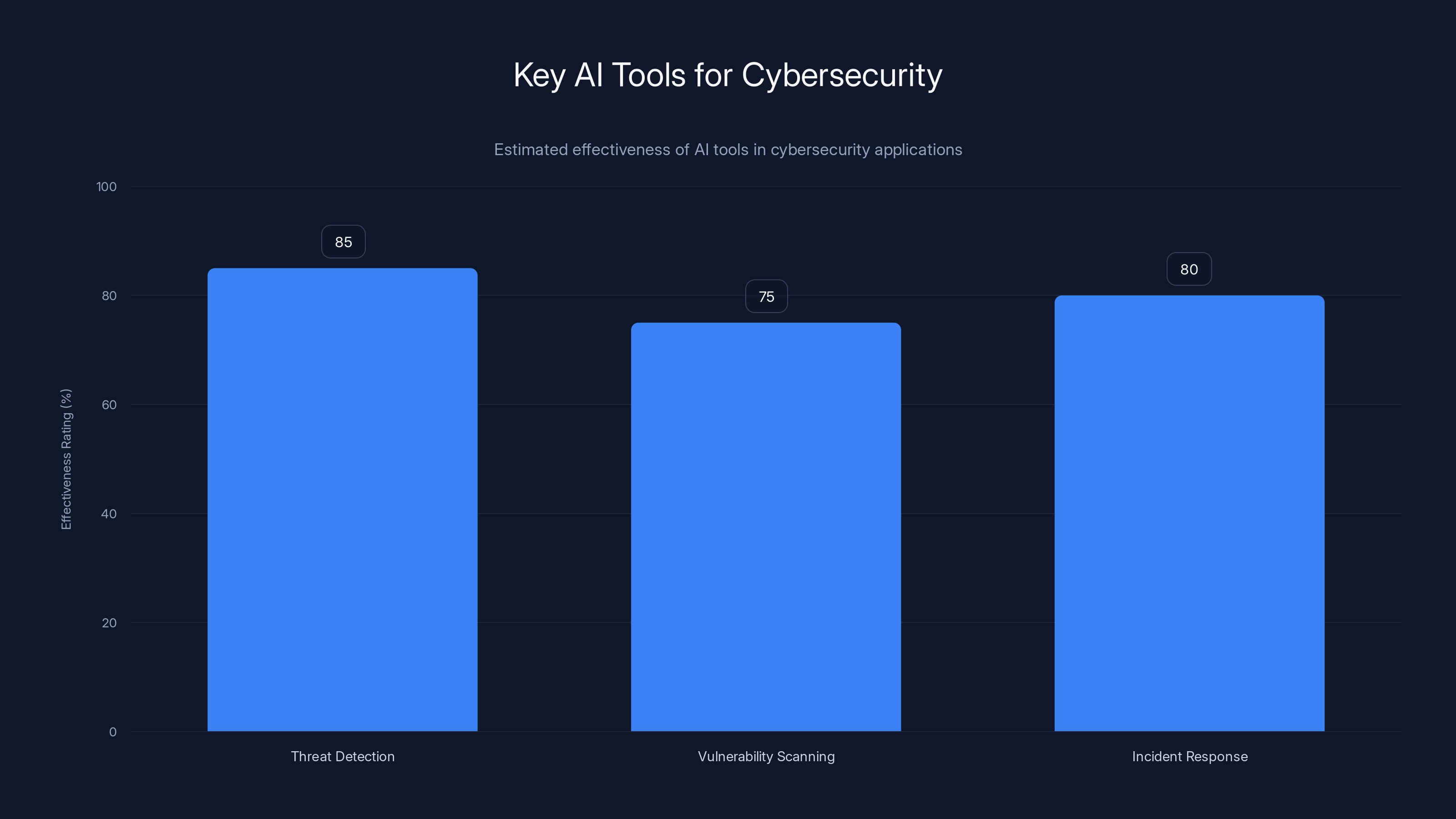
Threat detection AI tools are estimated to be the most effective in cybersecurity, followed by incident response and vulnerability scanning. (Estimated data)
The Rise of AI in Cybercrime
Artificial intelligence is often seen as a double-edged sword. While it holds the promise of revolutionizing industries and improving lives, it also poses significant risks when used maliciously. In the realm of cybersecurity, AI tools are increasingly utilized by hackers to automate tasks, identify vulnerabilities, and execute sophisticated attacks that were once the domain of highly skilled individuals.
How AI Lowers the Bar for Hackers
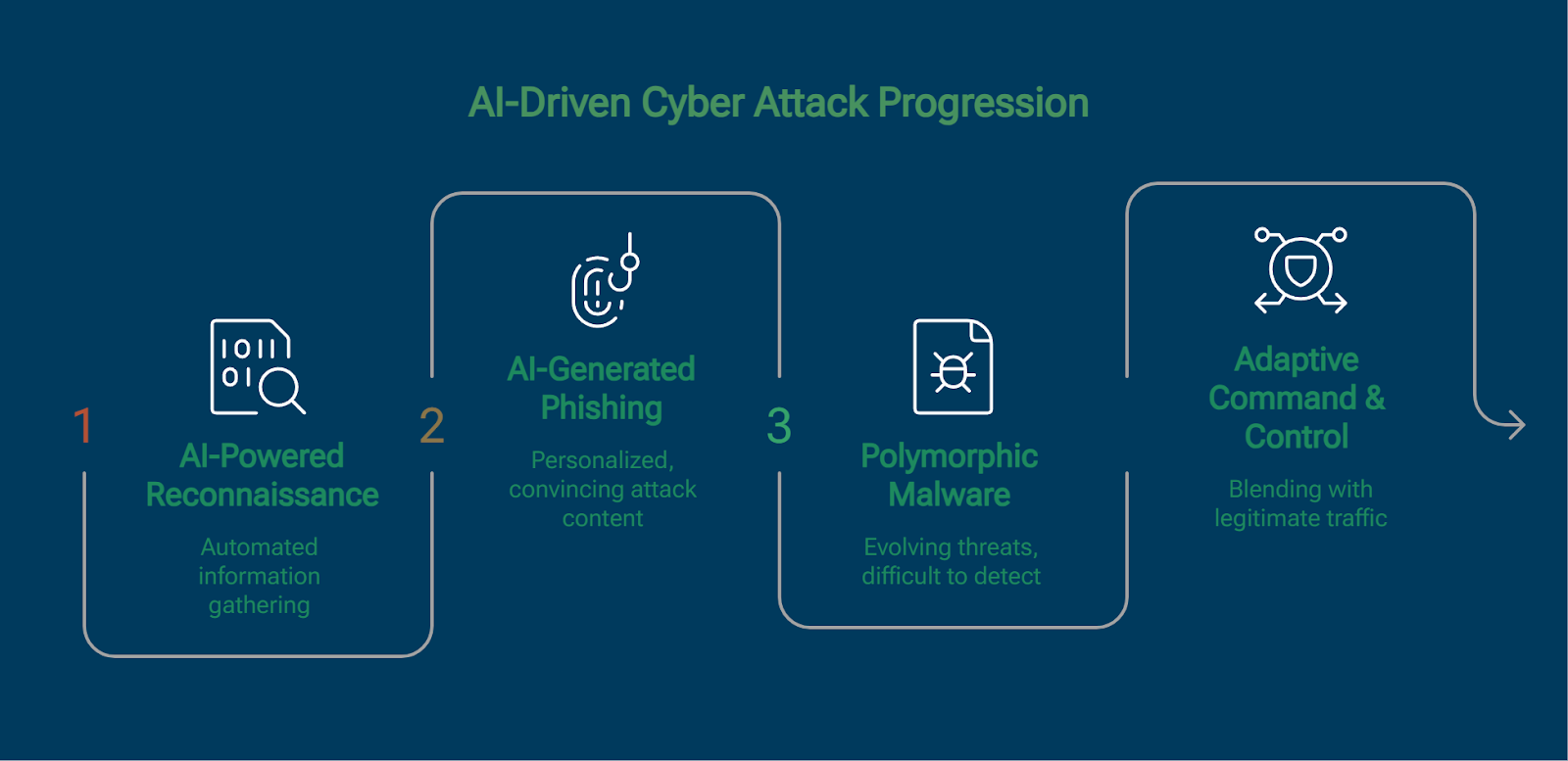
AI has drastically lowered the barrier to entry for cybercriminals. Tools that automate the discovery of vulnerabilities, generate phishing emails, and even write malicious code have made it possible for less skilled hackers to carry out effective attacks.
- Automated Vulnerability Scanning: AI tools can scan software for known vulnerabilities, a task that traditionally required significant expertise.
- Phishing Campaigns: AI can craft convincing phishing emails, increasing the likelihood of deceiving victims.
- Malware Generation: AI-generated malware can adapt to evade detection, posing challenges for traditional security measures.
Case Study: North Korean Hackers
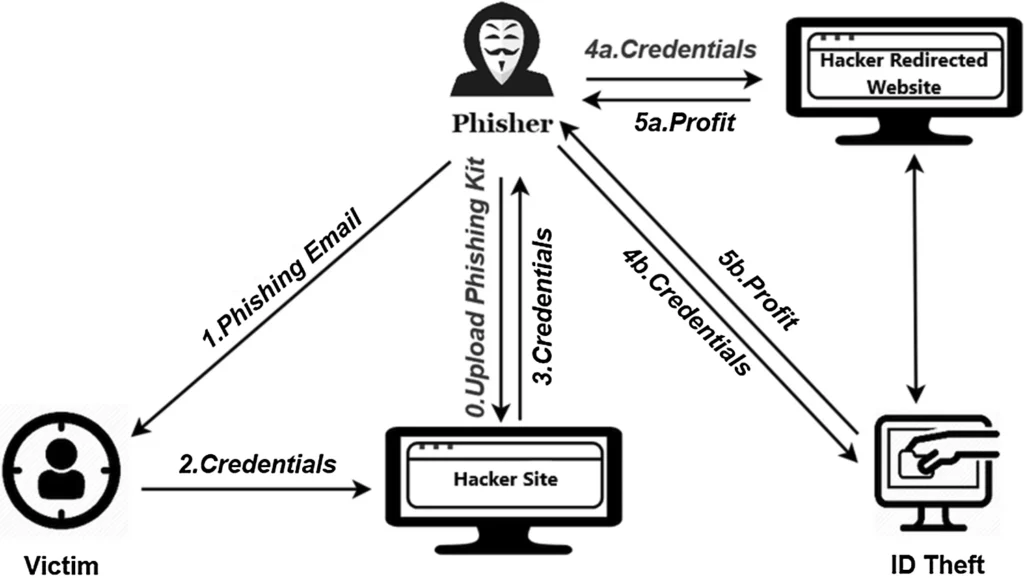
A recent report by cybersecurity firm Expel highlights a North Korean state-sponsored group leveraging AI to enhance their cybercriminal activities. This group has deployed credential-stealing malware across thousands of computers, focusing on cryptocurrency exchanges.
Key Tactics:
- Credential Harvesting: Using AI to automate the process of stealing login credentials.
- Cryptocurrency Wallet Attacks: Targeting digital wallets to siphon funds.
- AI-Driven Obfuscation: Making malware harder to detect by security software.
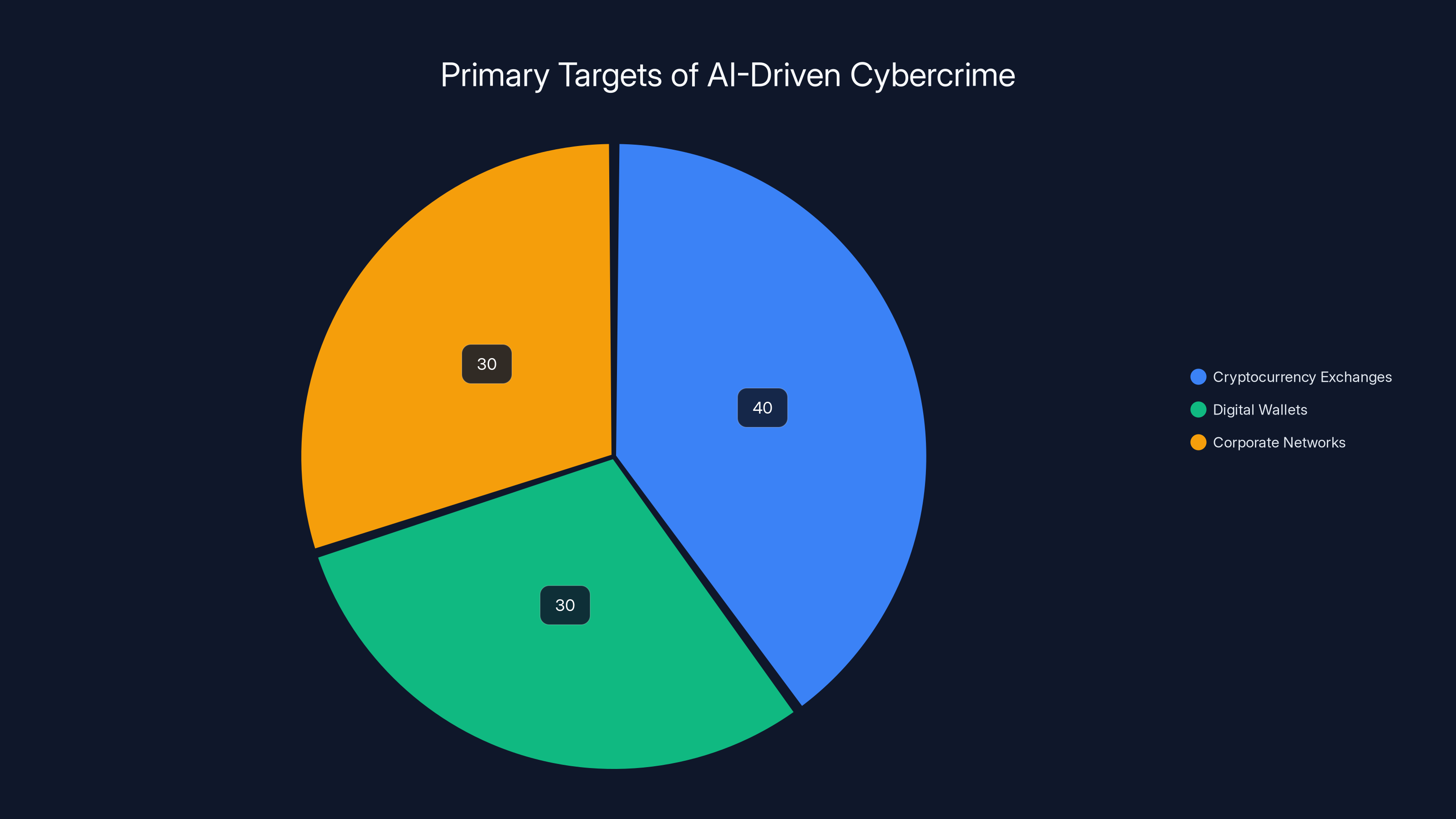
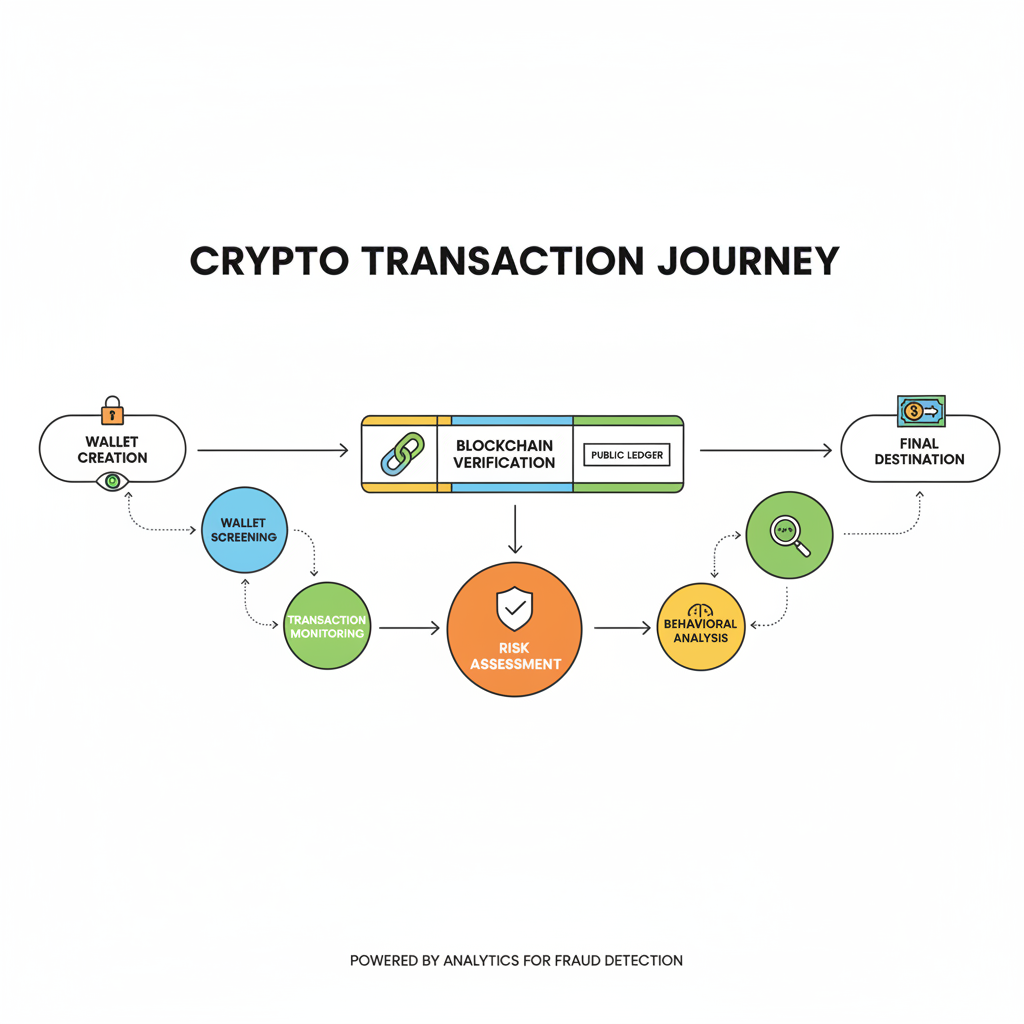
Cryptocurrency exchanges are the most targeted by AI-driven cybercrime due to their high value and transaction anonymity. Estimated data.
AI Tools Transforming Cybercrime
AI-Powered Vulnerability Scanners
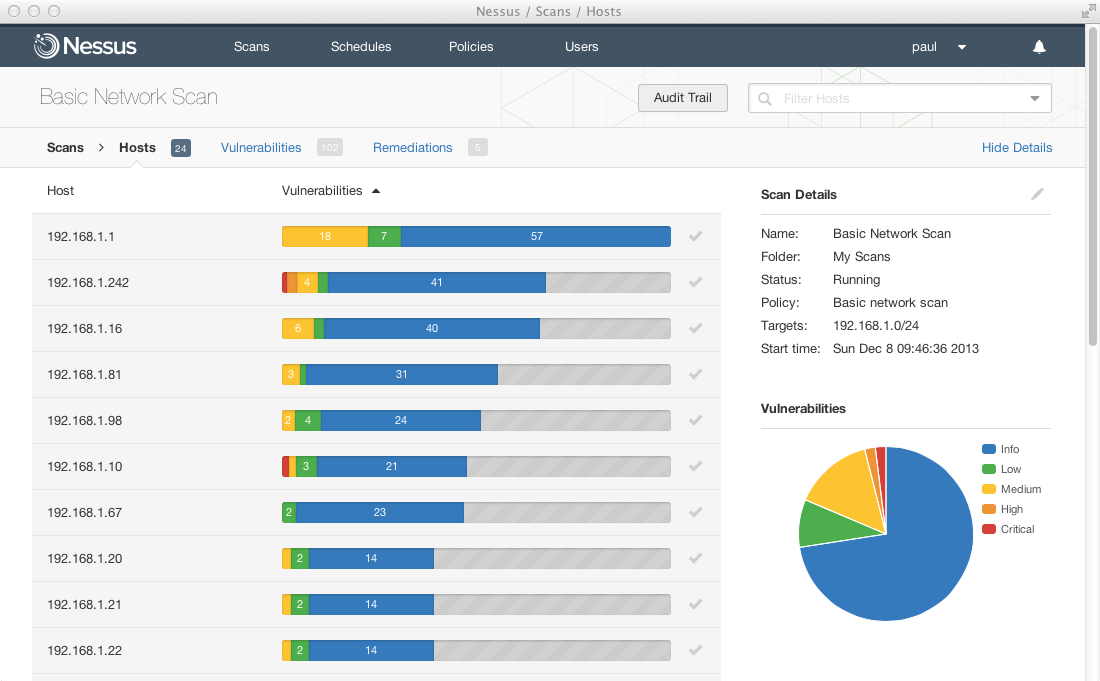
AI vulnerability scanners have become a staple in the toolkit of modern hackers. These tools can identify security flaws in software applications much faster than human analysts.
- Speed and Efficiency: Scans that took days can now be completed in hours.
- Comprehensive Coverage: AI can scan vast amounts of code, uncovering vulnerabilities that human analysts might miss.
Example Tool: Nessus uses AI to enhance its vulnerability scanning capabilities, providing detailed reports that guide remediation efforts.
AI in Phishing
Phishing remains one of the most effective methods for compromising systems. AI enhances phishing campaigns by crafting personalized and convincing emails that are more likely to trick recipients.
- Natural Language Processing (NLP): AI uses NLP to create emails that mimic human writing styles.
- Targeted Phishing: Leveraging AI to gather intelligence on targets and tailor phishing attempts accordingly.
Cryptocurrency: The Prime Target
Cryptocurrencies are a lucrative target for hackers due to their anonymity and irreversibility. AI tools are employed to exploit vulnerabilities in cryptocurrency exchanges and wallets.
Techniques in Cryptocurrency Theft
- Wallet Exploitation: AI tools identify weaknesses in wallet security protocols.
- Exchange Attacks: Targeting exchange platforms to gain unauthorized access to user accounts.
- Automated Transactions: Using AI to execute rapid transactions that drain accounts before victims can respond.
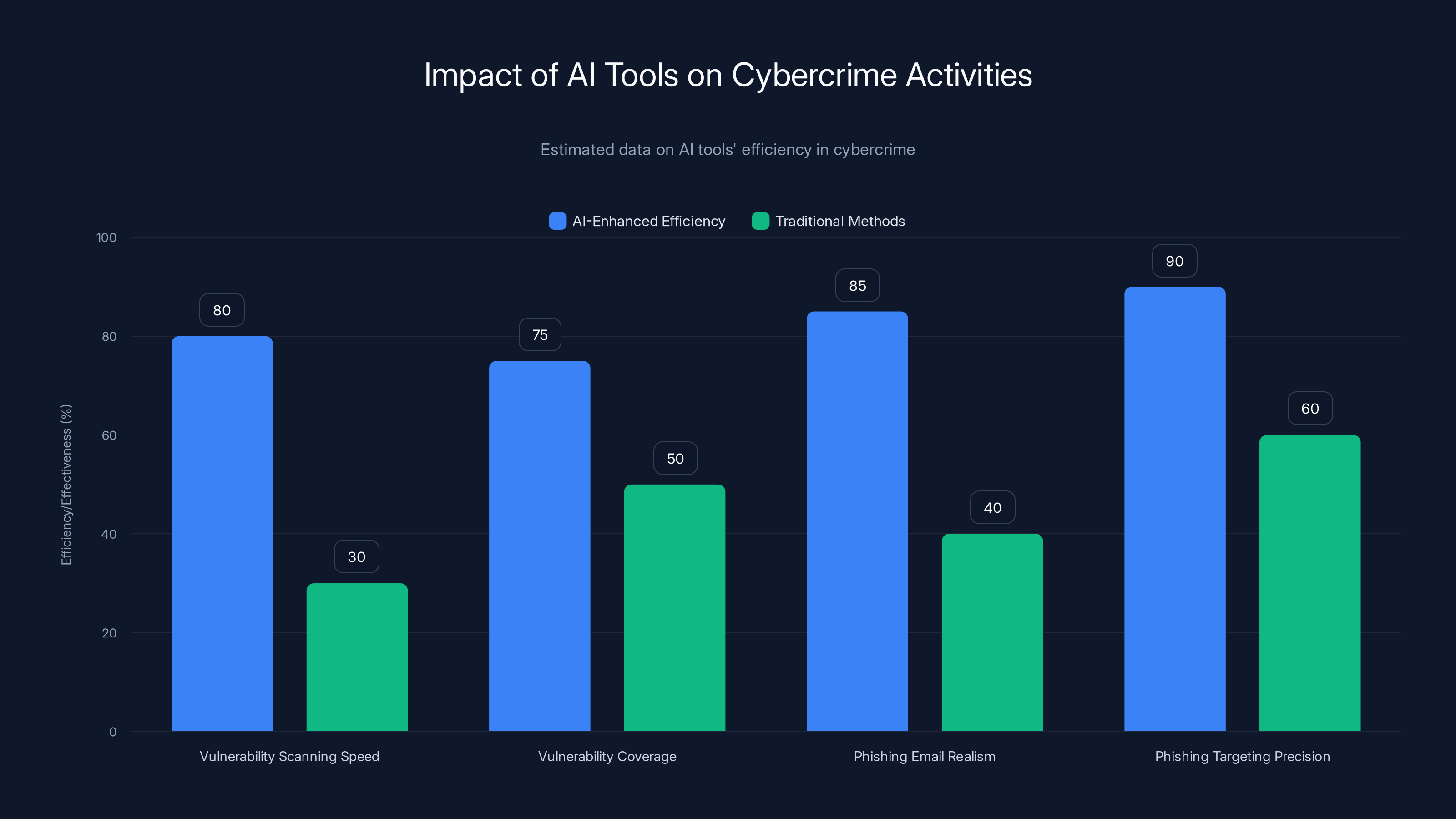
AI tools significantly enhance the efficiency and effectiveness of cybercrime activities, with notable improvements in phishing and vulnerability scanning. (Estimated data)
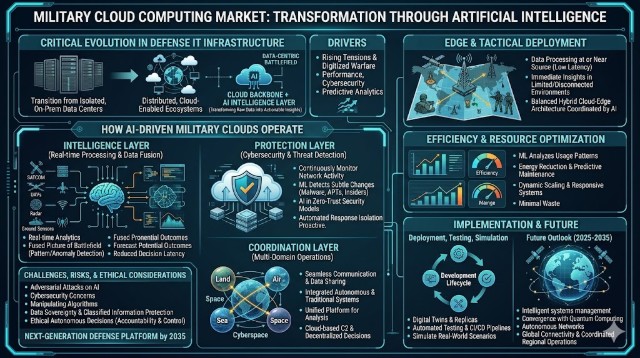
Defensive Measures Against AI-Driven Cybercrime
As AI empowers hackers, it also offers new tools for defenders. Organizations must adopt AI-driven security solutions to stay ahead of evolving threats.
AI-Powered Defense Tools
- Behavioral Analytics: AI monitors user behavior to detect anomalies indicative of cyberattacks.
- Automated Incident Response: AI enables rapid responses to detected threats, minimizing damage.
- Threat Intelligence: AI analyzes vast datasets to predict and thwart potential attacks.
Example Solution: Darktrace uses AI to detect and respond to cyber threats in real-time, offering a proactive approach to security.
Implementation Guide: Strengthening Cybersecurity with AI
Step 1: Evaluate Current Security Posture
Before integrating AI into your security strategy, assess your organization's current security measures and identify areas for improvement.
- Conduct a Risk Assessment: Determine which assets are most valuable and vulnerable.
- Review Security Policies: Ensure that existing policies align with industry best practices.
Step 2: Integrate AI Tools
Choose AI tools that complement your existing security infrastructure and address specific needs.
- Select Appropriate Tools: Consider tools that offer threat detection, vulnerability scanning, and incident response.
- Pilot Programs: Test AI tools in a controlled environment to evaluate their effectiveness.
Step 3: Continuous Monitoring and Improvement
AI tools require ongoing management to ensure they adapt to evolving threats.
- Regular Updates: Keep AI tools updated with the latest threat intelligence.
- Feedback Loops: Use insights from AI tools to refine security strategies.
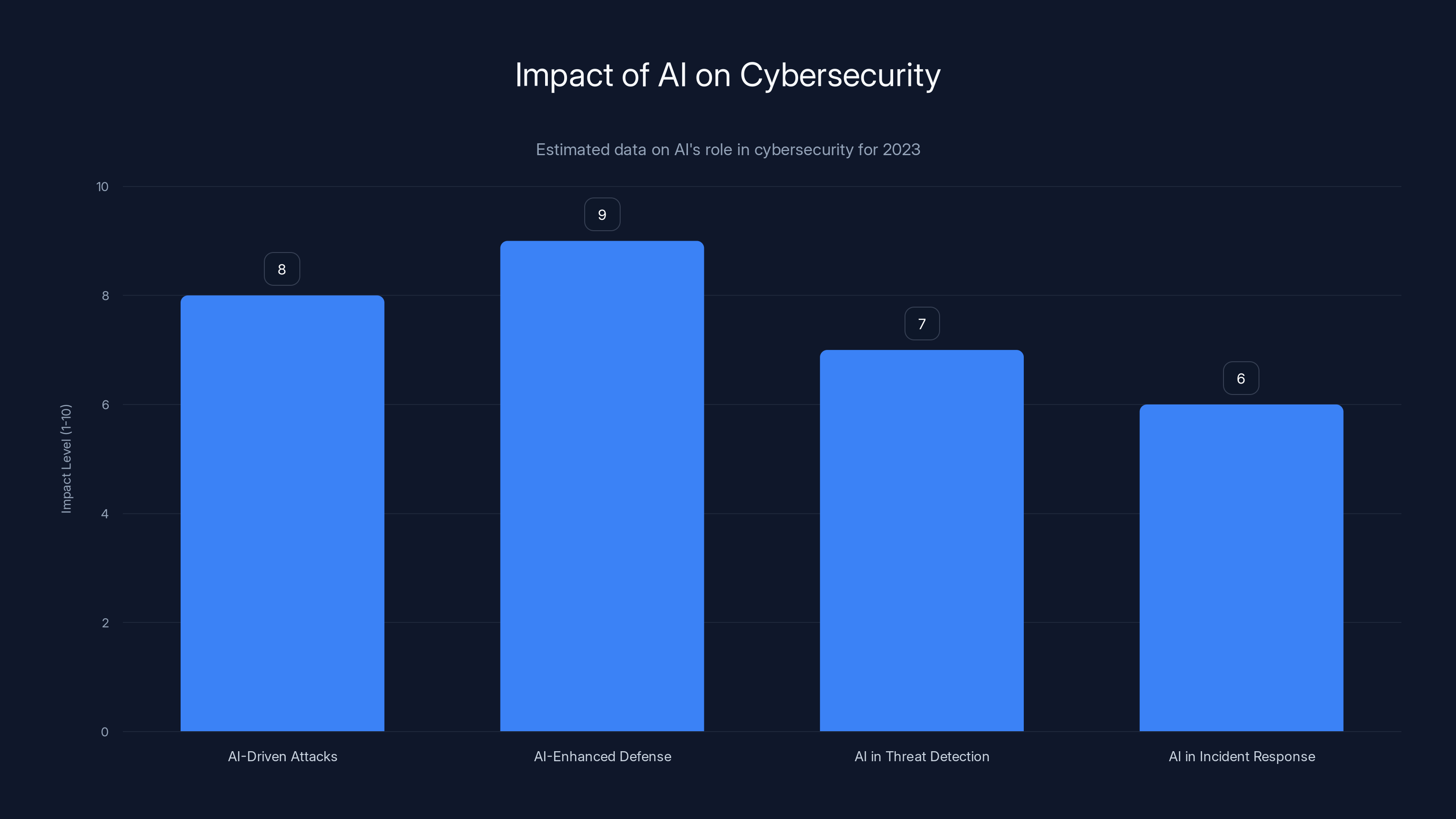
AI plays a significant role in both enhancing cybersecurity defenses and enabling sophisticated attacks. Estimated data reflects the dual impact of AI in 2023.
Common Pitfalls and Solutions
Overreliance on AI
While AI offers powerful capabilities, overreliance can lead to complacency. Human oversight remains essential to address nuanced threats.
- Solution: Combine AI with human expertise for a balanced security approach.
Data Privacy Concerns
AI tools often require access to sensitive data, raising privacy concerns.
- Solution: Implement strict data governance policies and ensure AI tools comply with regulations such as GDPR.
Future Trends in AI-Driven Cybercrime
The landscape of cybercrime is constantly evolving, with AI playing a pivotal role in shaping future trends.
AI and the Rise of Autonomous Cyber Attacks
As AI technologies advance, we may see the emergence of autonomous cyberattacks that require minimal human intervention.
- Implications: Traditional defense mechanisms may struggle to keep pace with rapidly evolving AI-driven threats.
Collaboration Between AI and Cybersecurity Experts
The future of cybersecurity will rely on collaboration between AI developers and cybersecurity professionals to develop robust defense strategies.
- Opportunities: Joint efforts can lead to innovative solutions that anticipate and neutralize emerging threats.
Conclusion: Navigating the AI-Driven Cybersecurity Landscape
AI has fundamentally transformed the world of cybersecurity, offering both challenges and opportunities. While AI tools empower hackers, they also provide defenders with powerful capabilities to combat cybercrime. By understanding the dynamics of AI-driven attacks and implementing robust security measures, organizations can protect themselves from the growing threat of AI-enhanced cybercrime.
Use Case: Automating your weekly reports with AI-powered tools like Runable.
Try Runable For Free
FAQ
What is AI-driven cybercrime?
AI-driven cybercrime involves using artificial intelligence tools to enhance the effectiveness and efficiency of cyberattacks. These tools can automate tasks such as vulnerability scanning, phishing, and malware generation, making it easier for less skilled hackers to carry out successful attacks.
How does AI empower mediocre hackers?
AI tools lower the skill threshold required for effective hacking by automating complex tasks and providing intelligent insights that guide attackers. This enables even mediocre hackers to execute sophisticated attacks with relative ease.
What are the primary targets of AI-driven cybercrime?
AI-driven cybercrime primarily targets high-value assets such as cryptocurrency exchanges, digital wallets, and corporate networks. The anonymity and irreversibility of cryptocurrency transactions make them particularly attractive to cybercriminals.
How can organizations defend against AI-driven attacks?
Organizations can defend against AI-driven attacks by integrating AI-powered security solutions that offer real-time threat detection, behavioral analytics, and automated incident response. Continuous monitoring and adaptation of security strategies are essential to staying ahead of evolving threats.
What are the future trends in AI and cybersecurity?
Future trends include the rise of autonomous cyberattacks, increased collaboration between AI developers and cybersecurity experts, and the development of innovative defense strategies that leverage AI to anticipate and neutralize emerging threats.
Why is human oversight important in AI-driven cybersecurity?
Human oversight is crucial because AI tools, while powerful, may miss nuanced threats or make errors in judgment. A balanced approach that combines AI with human expertise ensures a more comprehensive and effective cybersecurity strategy.
How does AI impact data privacy in cybersecurity?
AI tools often require access to large datasets to function effectively, raising concerns about data privacy. Organizations must implement strict data governance policies and ensure compliance with regulations such as GDPR to protect sensitive information.
How can AI enhance phishing campaigns?
AI enhances phishing campaigns by using natural language processing to create personalized and convincing emails that mimic human writing styles. This increases the likelihood of deceiving recipients and gaining unauthorized access to sensitive information.

Key Takeaways
- AI tools democratize cybercrime, enabling even mediocre hackers.
- North Korean hackers use AI for large-scale cryptocurrency theft.
- AI enhances phishing, malware, and vulnerability exploitation.
- Organizations must adopt AI-driven defense tools to combat threats.
- Future trends include autonomous cyberattacks and AI-expert collaboration.
- Human oversight remains crucial in AI-driven cybersecurity strategies.
Related Articles
- Anthropic's Mythos Under Investigation for Unauthorized Access [2025]
- The AI Governance Mirage: Understanding the Security Gap Enterprises Face [2025]
- Why AI Won't Replace Jobs, But Will Elevate Work Quality [2025]
- Inside the $290M Kelp DAO Heist: North Korea's Lazarus Group Strikes Again [2025]
- Understanding the Rising Threat of Hacktivist Attacks in the UK [2025]
- Ransomware and the Felony Murder Law: A New Legal Frontier [2025]
![How AI Tools Empower North Korean Hackers to Steal Millions [2025]](https://tryrunable.com/blog/how-ai-tools-empower-north-korean-hackers-to-steal-millions-/image-1-1776876029404.jpg)



