Inside the $290M Kelp DAO Heist: North Korea's Lazarus Group Strikes Again [2025]
Blockchain technology has been hailed as a revolutionary advancement in secure digital transactions. However, as the recent Kelp DAO heist demonstrates, vulnerabilities in its implementation can lead to substantial financial losses. In this article, we delve into the details of the $290 million cryptocurrency theft orchestrated by North Korea's infamous Lazarus Group. We'll explore how they managed to exploit the system, the implications of such attacks, and offer best practices for safeguarding against similar threats.
TL; DR
- Lazarus Group: A North Korean cybercrime syndicate known for high-profile crypto heists.
- $290M Stolen: Via fraudulent transactions exploiting Layer Zero integration.
- Cross-Chain Vulnerability: Exploited weaknesses in Kelp DAO's transaction verification.
- Security Measures: Importance of multi-signature wallets and transaction monitoring.
- Future Trends: Increased use of AI for threat detection and blockchain security.

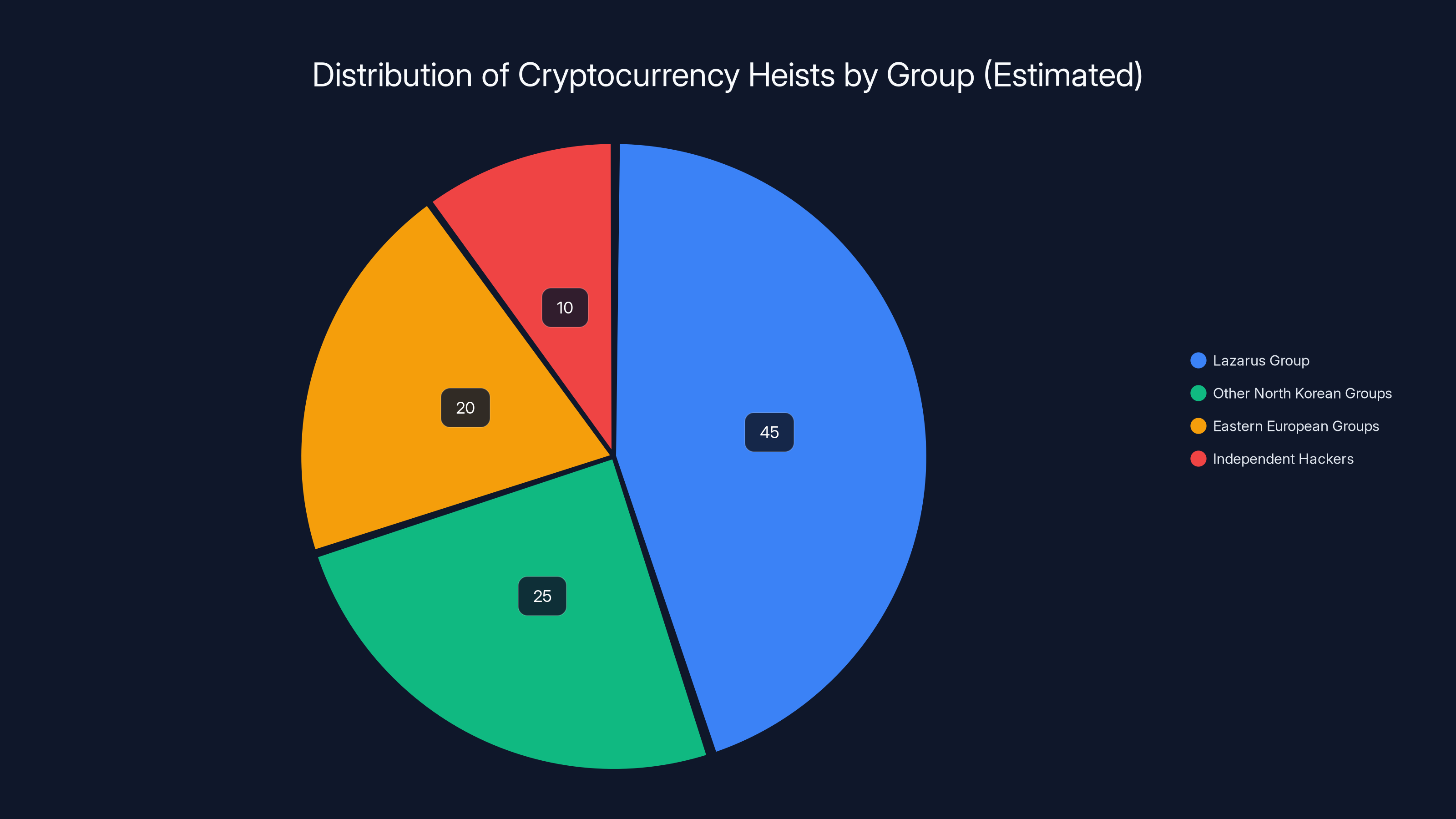
Lazarus Group is estimated to be responsible for 45% of major cryptocurrency heists, highlighting their significant impact on the crypto security landscape. Estimated data.
Understanding the Lazarus Group
The Lazarus Group is a cybercrime syndicate with origins traced back to North Korea. Known for their sophisticated cyberattacks, they have been linked to numerous high-profile cases, including the 2014 Sony Pictures hack and multiple cryptocurrency thefts. Their operations are often politically motivated, aiming to fund North Korea's regime through illegal activities.
A History of Cybercrime
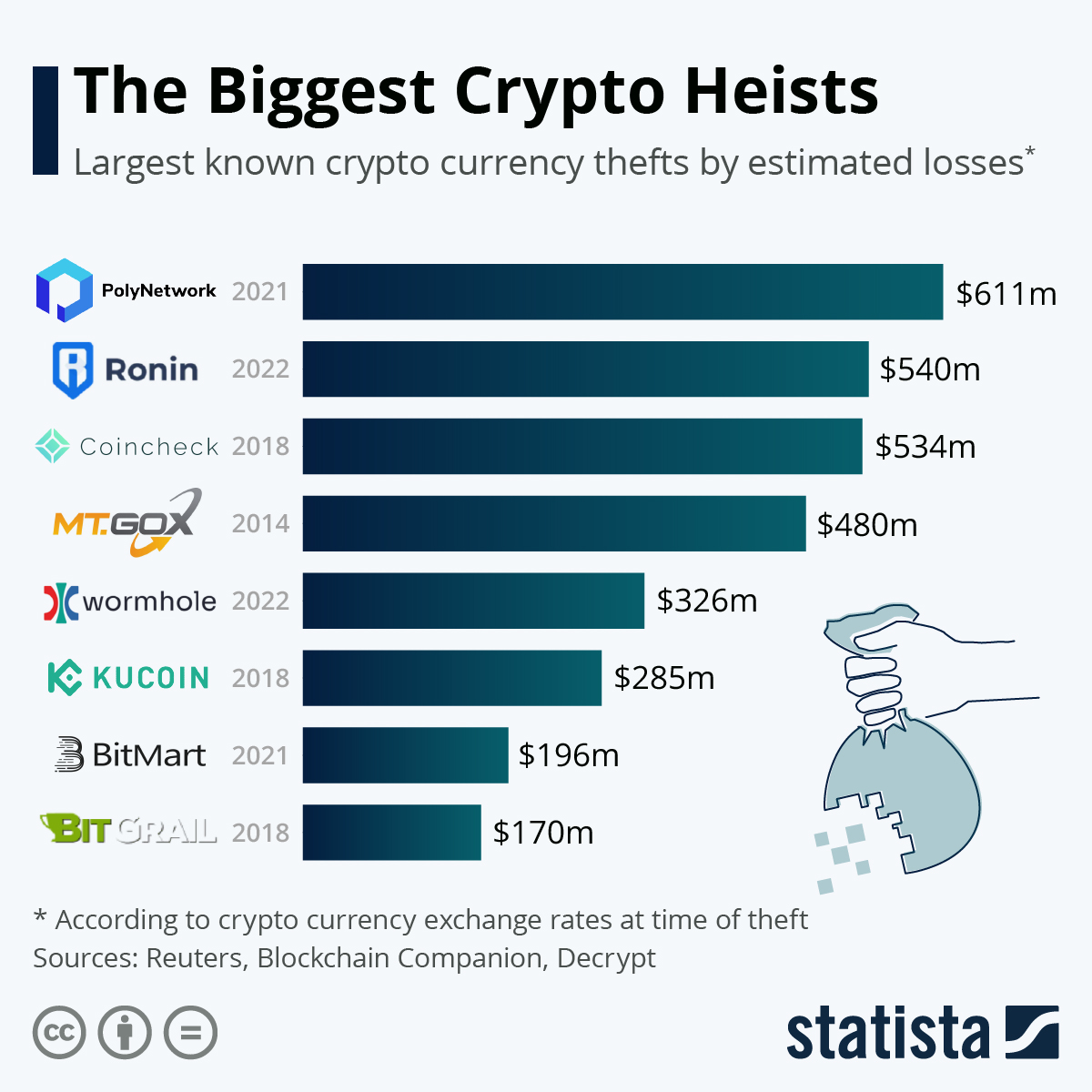
Lazarus first garnered international attention with their attack on Sony Pictures in 2014. Since then, they have shifted their focus to the lucrative world of cryptocurrency. They have been implicated in several digital heists, including the
Techniques and Tactics
Lazarus employs a variety of tactics to infiltrate systems and steal assets. These include spear-phishing, social engineering, malware deployment, and exploiting software vulnerabilities. Their ability to adapt and innovate makes them a formidable threat in the cybersecurity landscape.

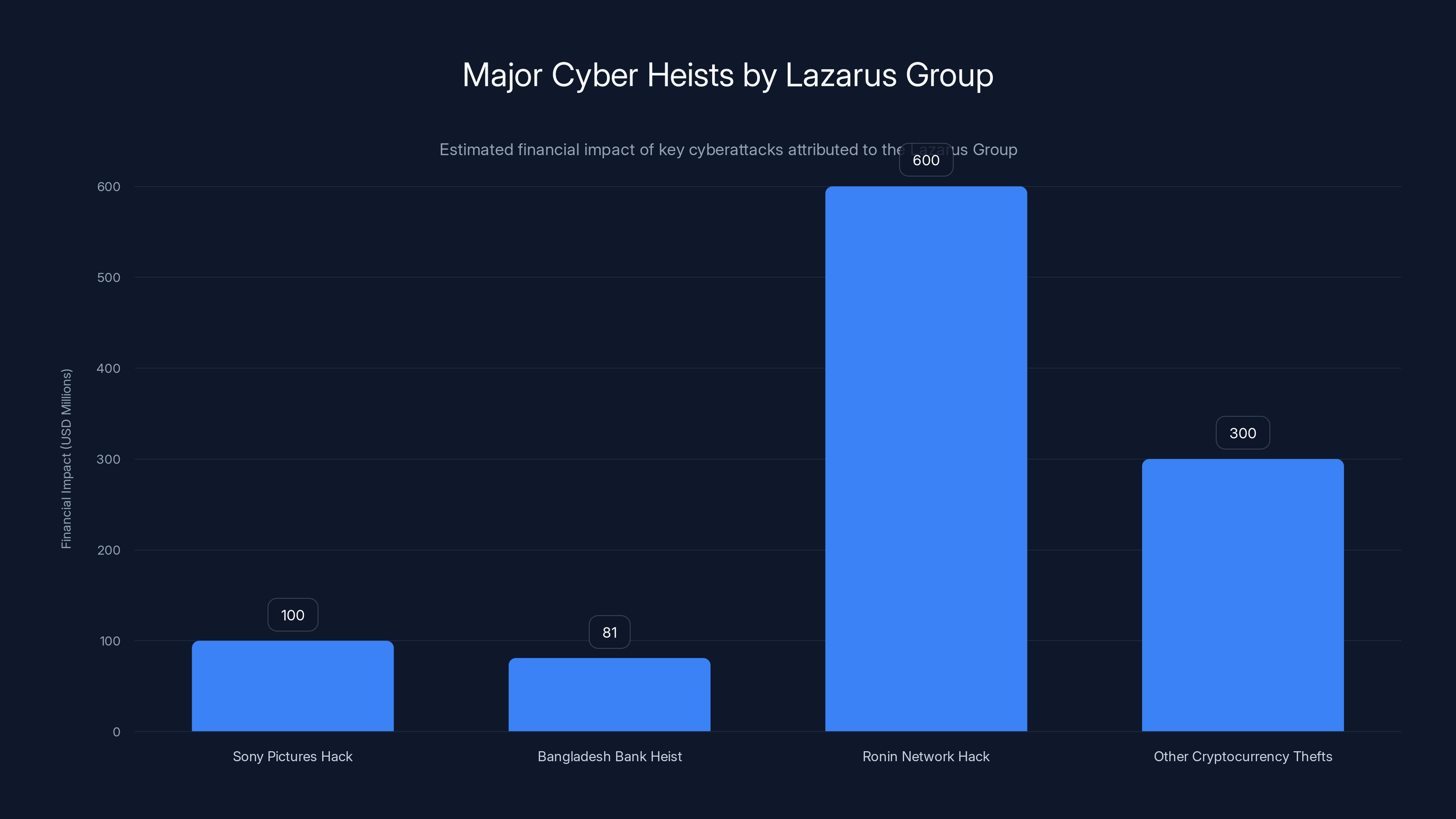
The Lazarus Group has been linked to significant financial losses through cyberattacks, with the Ronin Network hack alone estimated at $600 million. (Estimated data)
The Kelp DAO Heist: How It Unfolded
In the Kelp DAO incident, Lazarus exploited vulnerabilities in the Layer Zero protocol, which is used for cross-chain transactions. Kelp DAO, a decentralized autonomous organization, relied on Layer Zero for verifying transactions across different blockchain networks.
Exploiting Cross-Chain Transactions
Cross-chain technologies allow for the exchange of assets across different blockchain networks. However, these systems can be complex, and any oversight in security can be disastrous. Lazarus exploited a vulnerability in the cross-chain verification process, allowing them to initiate fraudulent transactions.
Step-by-Step Breakdown
- Reconnaissance: Lazarus identified vulnerabilities in Kelp DAO's transaction verification processes.
- Exploitation: They used these vulnerabilities to manipulate transaction records.
- Withdrawal: Once fraudulent transactions were validated, Lazarus withdrew funds from Kelp DAO.
- Obfuscation: The stolen funds were laundered through a series of tumblers and exchanges to obscure their origin.

Technical Analysis of the Exploit
The Layer Zero protocol, pivotal in this heist, facilitates interoperability between blockchains. Understanding its weakness provides insight into how the theft was executed.
Layer Zero Protocol
Layer Zero's architecture allows for seamless cross-chain interactions by leveraging oracles and relayers. It is designed to enhance interoperability without compromising security. However, the protocol's reliance on external verification mechanisms can introduce points of failure.
Key Weaknesses Identified:
- Oracles and Relayers: Misconfigured or compromised oracles can serve incorrect data.
- Verification Delays: Delays or errors in transaction verification can be exploited to initiate unauthorized transactions.
Preventative Measures
- Multi-Signature Wallets: Implementing multi-signature requirements for transactions can prevent unauthorized withdrawals.
- Enhanced Monitoring: Continuous monitoring of cross-chain transactions can help identify suspicious activities.
- Regular Audits: Routine security audits can uncover vulnerabilities before they are exploited.

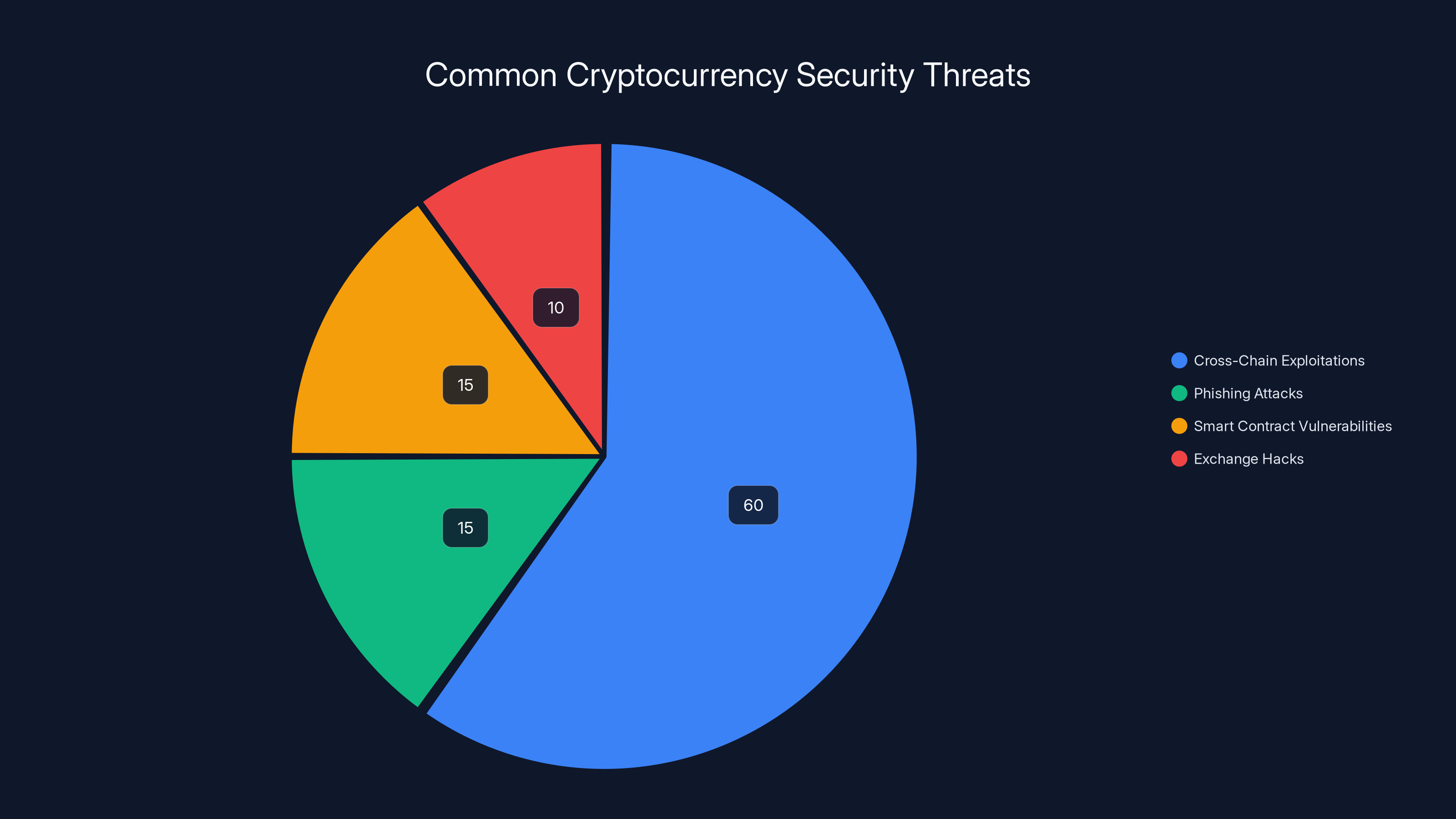
Cross-chain exploitations account for an estimated 60% of cryptocurrency thefts, highlighting the need for robust security protocols. Estimated data based on industry trends.
The Impact of the Heist
The theft of $290 million from Kelp DAO had significant repercussions, not only for the organization but also for the broader cryptocurrency market.
Economic Implications
Such a substantial loss can destabilize cryptocurrency markets, leading to fluctuations in token values and eroding investor confidence. The heist also highlights the persistent risks associated with decentralized finance (DeFi) platforms.
Reputational Damage
For Kelp DAO, the incident represents a severe blow to its credibility. Trust is paramount in the crypto space, and recovering from such a breach requires substantial effort and transparency.
Lessons Learned and Best Practices
In the face of growing threats, organizations must adopt robust security measures to safeguard digital assets.
Implementing Security Protocols
- Multi-Factor Authentication (MFA): Enforce MFA across all access points to enhance security.
- Decentralized Verification: Employ decentralized oracle networks to minimize single points of failure.
- Threat Intelligence: Leverage threat intelligence platforms to anticipate and counteract cyber threats.
Community and Regulatory Response
The crypto community must collaborate to establish standards for security, while regulators could play a role in enforcing compliance and best practices.
Future Trends in Blockchain Security
As technology evolves, so do the methods employed by cybercriminals. Anticipating these changes is crucial for developing effective countermeasures.
AI and Machine Learning
Artificial intelligence and machine learning are emerging as powerful tools for detecting anomalies and predicting potential threats. By analyzing patterns in transaction data, these technologies can provide early warnings of suspicious activity.
Quantum Computing
The advent of quantum computing poses both risks and opportunities for blockchain security. While it could potentially break current cryptographic algorithms, it also offers the possibility of developing new, more secure encryption methods.
Practical Implementation Guides
For organizations looking to enhance their security posture, implementing the following steps can provide a robust foundation.
Building a Secure Infrastructure
- Conduct Risk Assessments: Identify potential vulnerabilities in your blockchain infrastructure.
- Implement Layered Security: Use a multi-layered approach to protect against various attack vectors.
- Educate and Train Staff: Regularly train employees on security best practices and threat awareness.
Common Pitfalls and Solutions
Despite best efforts, certain pitfalls are common when securing blockchain networks. Recognizing and addressing these can significantly reduce risk.
Overreliance on Automation
While automation can enhance efficiency, overreliance can lead to neglect of manual oversight. Balancing automated systems with human review is essential.
Insufficient Incident Response Plans
Having a robust incident response plan is crucial. Ensure plans are regularly updated and tested to remain effective against emerging threats.
Conclusion: Strengthening Blockchain Security
The $290 million Kelp DAO heist is a stark reminder of the vulnerabilities inherent in blockchain systems. By understanding the methods employed by groups like Lazarus and implementing comprehensive security strategies, the blockchain community can better safeguard its assets.
FAQ
What is the Lazarus Group?
The Lazarus Group is a North Korean cybercrime syndicate known for executing sophisticated cyberattacks, particularly in the cryptocurrency sector.
How did the Kelp DAO heist occur?
Lazarus exploited vulnerabilities in the Layer Zero protocol used by Kelp DAO for cross-chain transactions, allowing them to siphon off $290 million.
What are the key vulnerabilities in cross-chain technologies?
Key vulnerabilities include compromised oracles, verification delays, and misconfigured relayers, which can be exploited to manipulate transactions.
How can organizations protect against similar heists?
Implementing multi-signature wallets, continuous monitoring, regular audits, and leveraging decentralized oracle networks are effective measures.
What role does AI play in blockchain security?
AI and machine learning can detect anomalies and predict threats by analyzing transaction patterns, providing early warnings of suspicious activities.
What are the future trends in blockchain security?
Future trends include the use of AI for threat detection and the development of quantum-resistant encryption methods.
How important is community collaboration in enhancing security?
Community collaboration is vital for establishing security standards and sharing threat intelligence to collectively enhance resilience against cyber threats.
Key Takeaways
- Lazarus Group exploits cross-chain vulnerabilities for $290M theft.
- LayerZero protocol weaknesses highlighted in Kelp DAO heist.
- Multi-signature wallets recommended for enhanced security.
- AI and machine learning crucial in future threat detection.
- Quantum computing poses risks and opportunities for blockchain.
Related Articles
- Why AES 128 Remains Secure in a Post-Quantum World [2025]
- WordPress Vulnerability: How Hackers Exploit Simple Plugin Flaws [2025]
- Understanding and Mitigating Microsoft Teams Helpdesk Impersonation Attacks [2025]
- They Built a Legendary Privacy Tool. Now They’re Sworn Enemies | WIRED
- Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
- BackgroundChecks.com Review: Comprehensive Insights for 2025
![Inside the $290M Kelp DAO Heist: North Korea's Lazarus Group Strikes Again [2025]](https://tryrunable.com/blog/inside-the-290m-kelp-dao-heist-north-korea-s-lazarus-group-s/image-1-1776782309475.jpg)



