How Hackers Are Using AI to Exploit Security Flaws Faster Than Ever [2025]
Last Tuesday, a CTO told me, "We just got hit. They found a hole in our API we didn't even know existed." This isn't an isolated incident. Hackers are increasingly using AI to find and exploit security vulnerabilities at unprecedented speed. AI isn't just a tool for defenders anymore—it's quickly becoming a favorite weapon for attackers too.
TL; DR
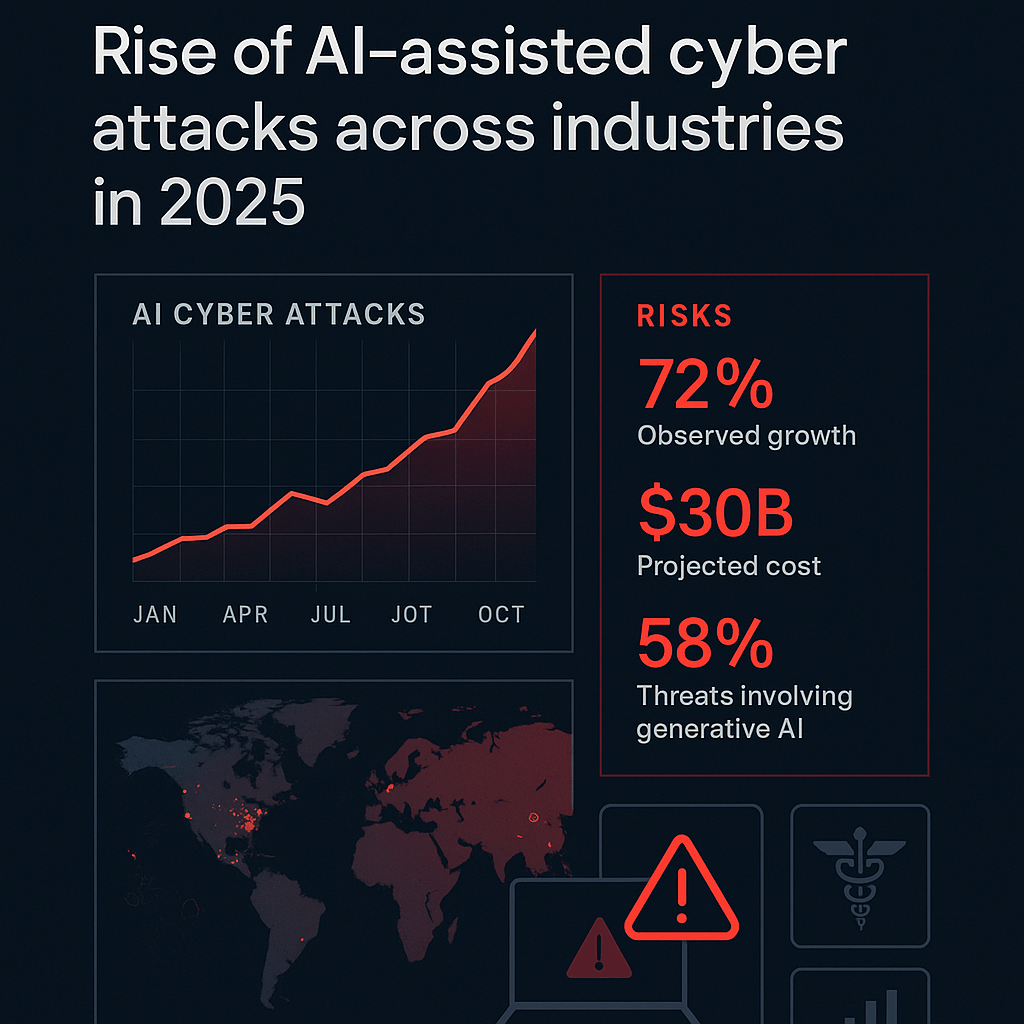
- AI-Powered Attacks: Hackers are using AI to automate the discovery and exploitation of security flaws, leading to a 44% increase in attacks.
- Vulnerability Exploitation: AI helps attackers identify and exploit vulnerabilities faster than traditional methods.
- Low Barrier to Entry: Generative AI lowers the skill level required to conduct sophisticated attacks.
- Ransomware Surge: AI has contributed to a 50% increase in ransomware incidents.
- Future Trends: As AI technology advances, expect more sophisticated and automated attacks.
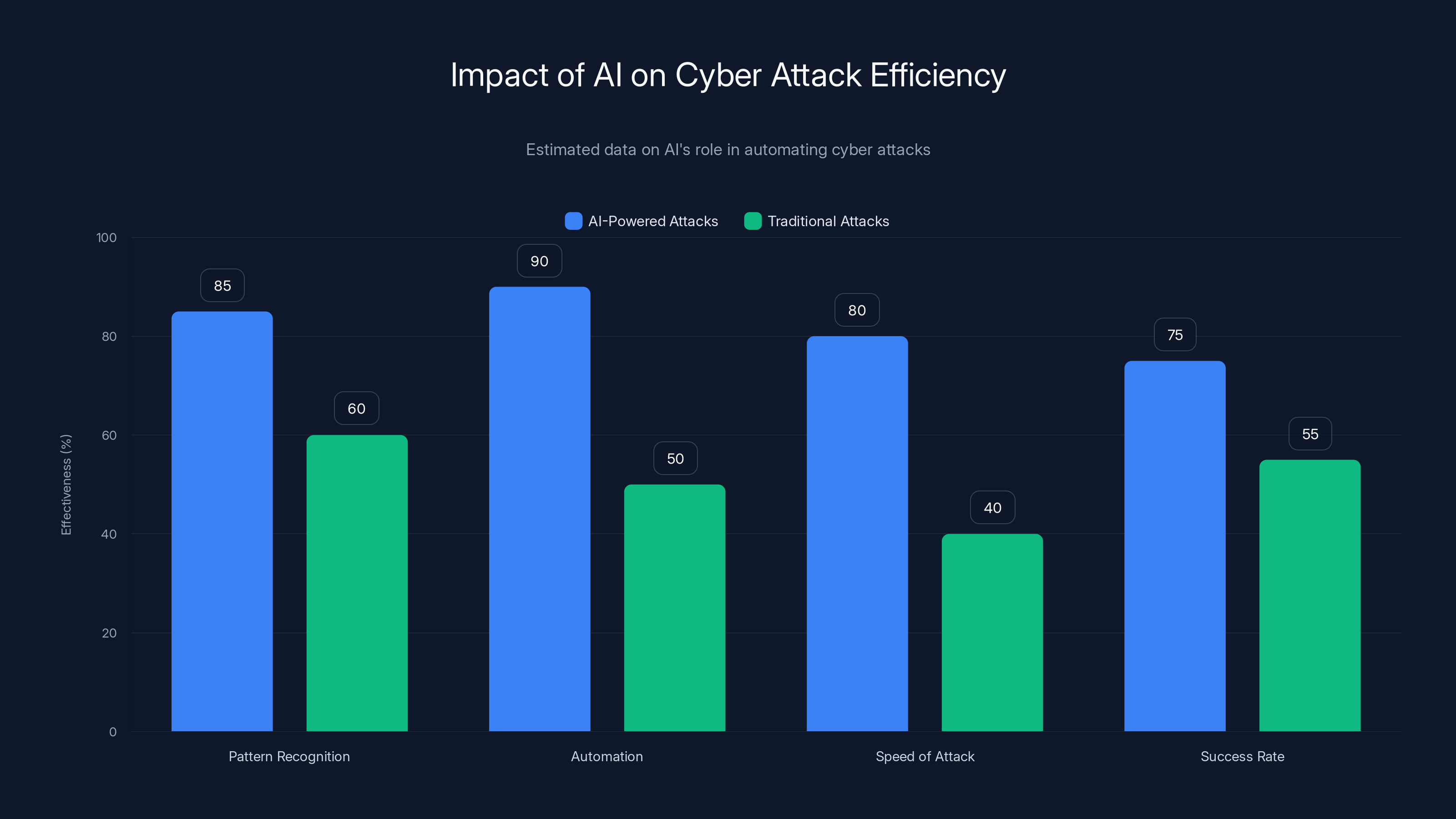
AI significantly enhances the efficiency of cyber attacks by improving pattern recognition, automation, and speed. Estimated data shows AI-powered attacks outperform traditional methods in key areas.
Introduction
In today's digital age, the integration of artificial intelligence (AI) into various business operations has transformed industries, enhancing efficiency and productivity. However, this same technology is also being co-opted by cybercriminals to expedite and scale their attacks. This article explores how hackers are leveraging AI to exploit security flaws more quickly and effectively than ever before.

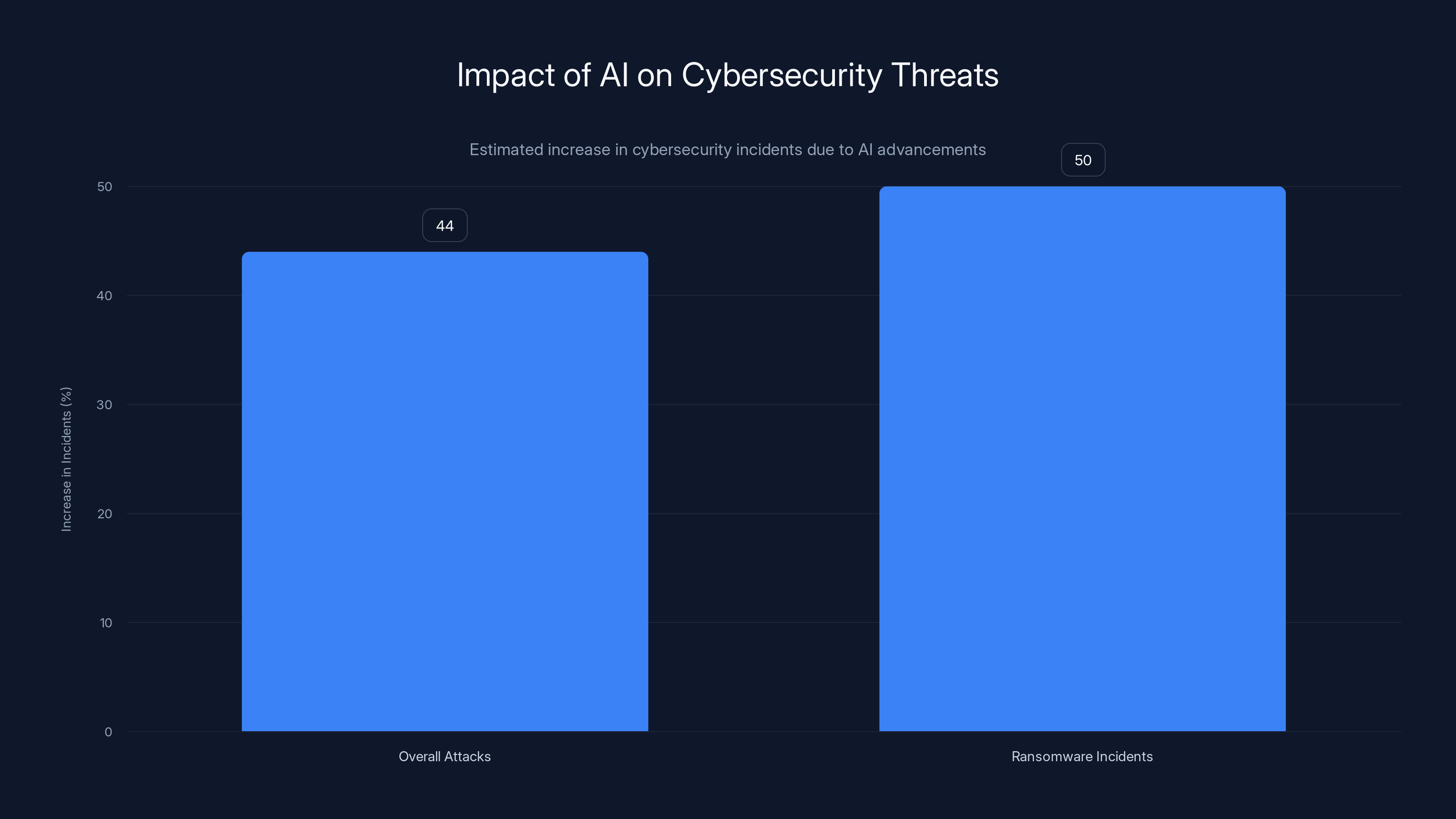
AI advancements have led to a 44% increase in overall cyber attacks and a 50% rise in ransomware incidents, highlighting the growing impact of AI in cybersecurity threats.
The Rise of AI-Powered Cyber Attacks
Let's start by understanding what makes AI such an attractive tool for hackers. Traditionally, cyber-attacks required extensive manual work, including identifying vulnerabilities, crafting exploits, and executing attacks. AI changes this dynamic by automating these processes.
How AI Automates Attacks
AI can analyze vast amounts of data to identify patterns and anomalies that might indicate a security weakness. For instance, machine learning algorithms can be trained to recognize the signatures of common vulnerabilities in software code or network configurations.
- Pattern Recognition: AI excels at identifying subtle patterns that humans might miss. This makes it invaluable for discovering vulnerabilities in complex systems.
- Automation: Once a vulnerability is identified, AI can automate the creation and deployment of exploits, significantly reducing the time between discovery and attack.
Case Study: Automated SQL Injection Attacks
Consider SQL injection attacks, where malicious SQL statements are inserted into an entry field for execution. AI can automate this process by continuously scanning web applications for vulnerable endpoints and generating tailored SQL payloads to exploit them.
Generative AI Lowers the Barrier to Entry
Generative AI, such as OpenAI's GPT models, has made it easier for less skilled actors to execute sophisticated attacks. These models can generate human-like text, which can be used to craft convincing phishing emails or social engineering scripts.
Phishing and Social Engineering
AI can generate highly convincing phishing emails by mimicking the writing style of legitimate communications from trusted sources. This increases the likelihood of a successful attack, as recipients are more likely to be deceived by the authenticity of the message.
- Email Personalization: AI can analyze a target's online presence to craft personalized phishing emails, increasing the chances of a successful attack.
- Voice Cloning: Tools like Eleven Labs allow attackers to clone a person's voice, making phone-based social engineering even more convincing.


AI-powered defense tools and multi-factor authentication are estimated to be the most effective strategies against AI-powered attacks, with high ratings of 9 and 8 respectively. Estimated data.
The Role of AI in Ransomware
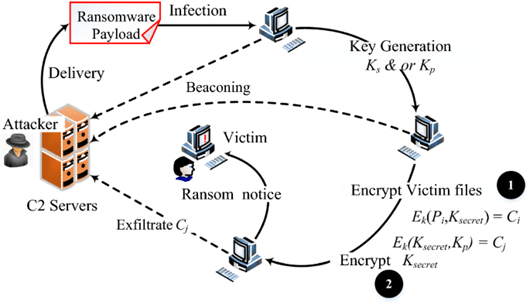
Ransomware attacks have seen a significant increase, partly due to the capabilities that AI brings to the table. AI can be used to automate the encryption process, making ransomware attacks faster and more efficient.
Ransomware-as-a-Service (Raa S)
Raa S platforms allow less skilled attackers to launch sophisticated ransomware attacks by providing all the necessary tools and infrastructure. AI plays a crucial role in these platforms by automating various stages of the attack lifecycle, from initial infection to data exfiltration and encryption.
- Payload Generation: AI can create malicious payloads designed to evade detection by antivirus software.
- Network Analysis: AI can map a target's network to identify critical systems for encryption.

Best Practices for Defending Against AI-Powered Attacks
With the growing threat of AI-powered cyber-attacks, businesses must adopt proactive measures to protect themselves. Here are some best practices:
- Regular Security Audits: Conduct frequent security assessments to identify and patch vulnerabilities before attackers can exploit them.
- AI-Powered Defense Tools: Utilize AI-based security solutions that can detect and respond to threats in real-time.
- Employee Training: Educate employees about the latest phishing techniques and social engineering tactics.
- Network Segmentation: Limit the spread of ransomware by segmenting networks to contain potential infections.
- Incident Response Plan: Develop and regularly update an incident response plan to quickly mitigate the effects of a security breach.
Future Trends in AI-Driven Cybersecurity
As AI technology continues to evolve, we can expect even more sophisticated cyber threats. Here are some trends to watch:
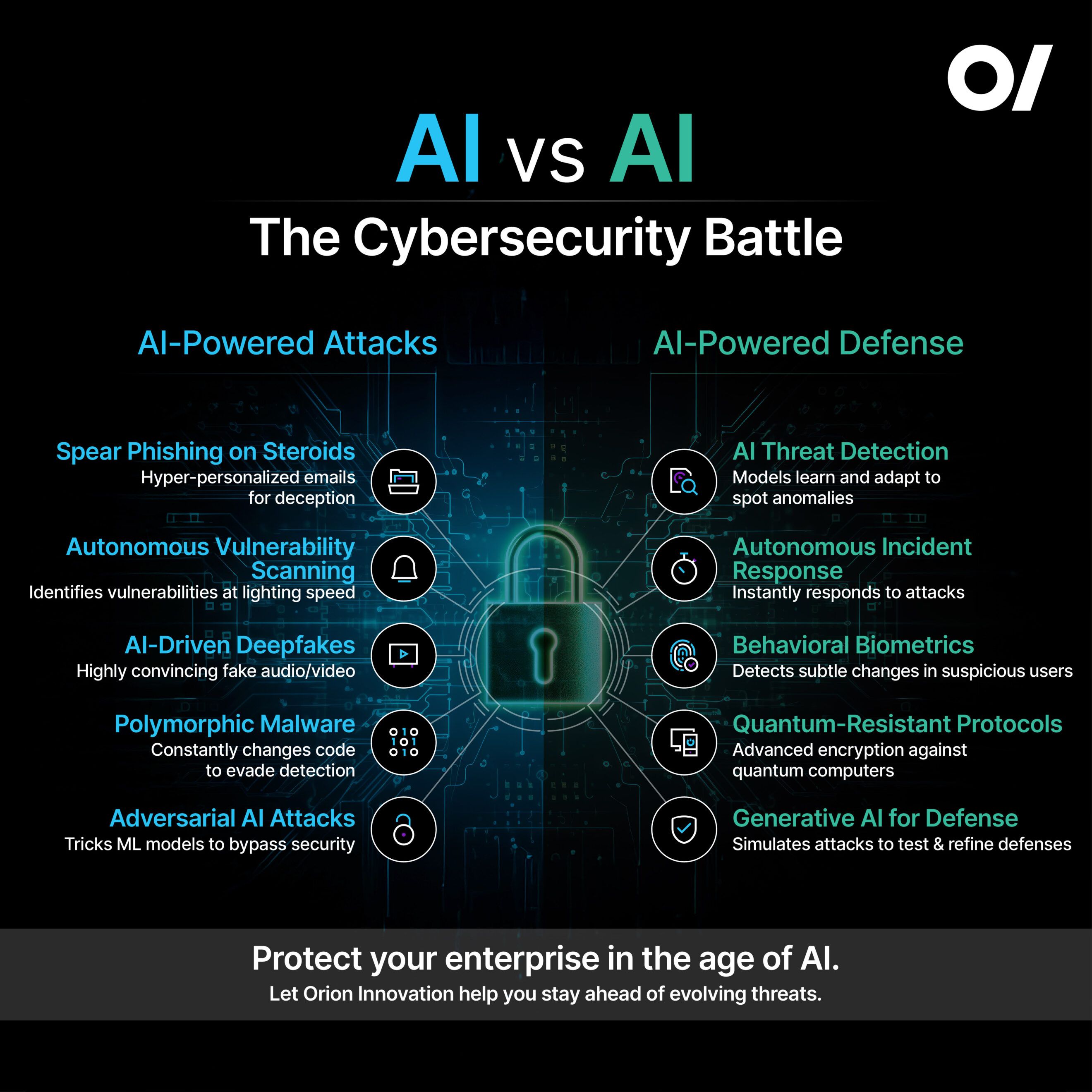
AI vs. AI
The future of cybersecurity will likely involve AI systems battling each other. Defensive AI will need to outsmart offensive AI, leading to an arms race in the cyberspace arena.
- Adversarial Machine Learning: Attackers may use adversarial techniques to trick AI-based security systems into misclassifying threats.
- AI Red Teaming: Organizations will employ AI-powered red teams to simulate attacks and test their defenses.
Quantum Computing
Quantum computing poses a significant threat to traditional encryption methods. As quantum technology matures, it may render current cryptographic algorithms obsolete, necessitating the development of quantum-resistant encryption.

Conclusion
The integration of AI into cyber-attacks is a double-edged sword. While it enhances the capabilities of security professionals, it also empowers hackers to execute more efficient and devastating attacks. Staying one step ahead in this rapidly evolving landscape requires constant vigilance, investment in AI-driven defense tools, and a commitment to cybersecurity best practices.
FAQ
What is AI's role in modern cyber-attacks?
AI automates and accelerates the discovery and exploitation of security vulnerabilities, making attacks faster and more efficient.
How does AI make phishing attacks more effective?
AI can generate personalized and convincing phishing emails that are more likely to deceive recipients, increasing the success rate of these attacks.
What can businesses do to protect against AI-powered cyber threats?
Businesses should conduct regular security audits, use AI-based defense tools, train employees, segment networks, and have an incident response plan in place.
What is Ransomware-as-a-Service (Raa S)?
Raa S platforms provide the tools and infrastructure for launching ransomware attacks, often using AI to automate and enhance the attack process.
How will quantum computing impact cybersecurity?
Quantum computing could break traditional encryption methods, necessitating the development of new quantum-resistant cryptographic algorithms.
Key Takeaways
- AI is automating vulnerability discovery and exploitation, increasing attack speed.
- Generative AI lowers the skill barrier for executing sophisticated cyber-attacks.
- Ransomware incidents have risen by 50% due to AI-enhanced tactics.
- Businesses must adopt AI-powered defense tools to counteract these threats.
- Quantum computing may necessitate new encryption methods in the near future.
Related Articles
- The Human Risk Reckoning: Evolving Security for an AI-Augmented Workforce [2025]
- Understanding the Implications of Data Leaks: A Deep Dive into the Frivol Incident [2025]
- The Dark Side of AI: How a Hacker Explited Anthropic's Claude to Breach Mexican Government Agencies [2025]
- Why Sierra the Supercomputer Had to Die: A Deep Dive into the Lifecycle of High-Performance Computing [2025]
- Mastering Phone Privacy: How NordVPN's Birthday Sale Can Upgrade Your Security to Samsung Galaxy S26 Ultra Levels [2025]
- Navigating the Complex World of Anti-Bot Systems: The OpenClaw Dilemma [2025]
![How Hackers Are Using AI to Exploit Security Flaws Faster Than Ever [2025]](https://tryrunable.com/blog/how-hackers-are-using-ai-to-exploit-security-flaws-faster-th/image-1-1772120094512.jpg)



