Understanding the Implications of Data Leaks: A Deep Dive into the Frivol Incident [2025]
Data leaks are becoming increasingly common, posing significant risks to both individuals and organizations. The recent incident involving the adult website Frivol has brought attention to the vulnerabilities that can lead to such breaches. In this article, we will explore the details of the Frivol data leak, understand the technologies involved, and discuss best practices for preventing similar incidents in the future.
TL; DR
- Frivol Data Leak: Approximately 479,000 user emails exposed due to an unsecured Kibana instance, as reported by Cybernews.
- Key Risks: Includes extortion and phishing threats posed by exposed data.
- Best Practices: Implement strong access controls and regular security audits to prevent data leaks.
- Future Trends: Increasing need for AI-driven security measures to detect and mitigate potential breaches.
- Bottom Line: Organizations must prioritize data protection to maintain user trust and mitigate risks.


The zero trust security market is expected to grow significantly, reaching $51.6 billion by 2026, driven by the increasing need for robust security measures.
What Happened in the Frivol Data Leak?
The Frivol data leak was identified by researchers from Cybernews, revealing a misconfigured Kibana instance that left user data exposed. The instance contained sensitive information, including around 479,000 user email addresses, some of which belonged to corporate entities. The breach highlights the risks associated with improperly secured databases accessible via the internet.
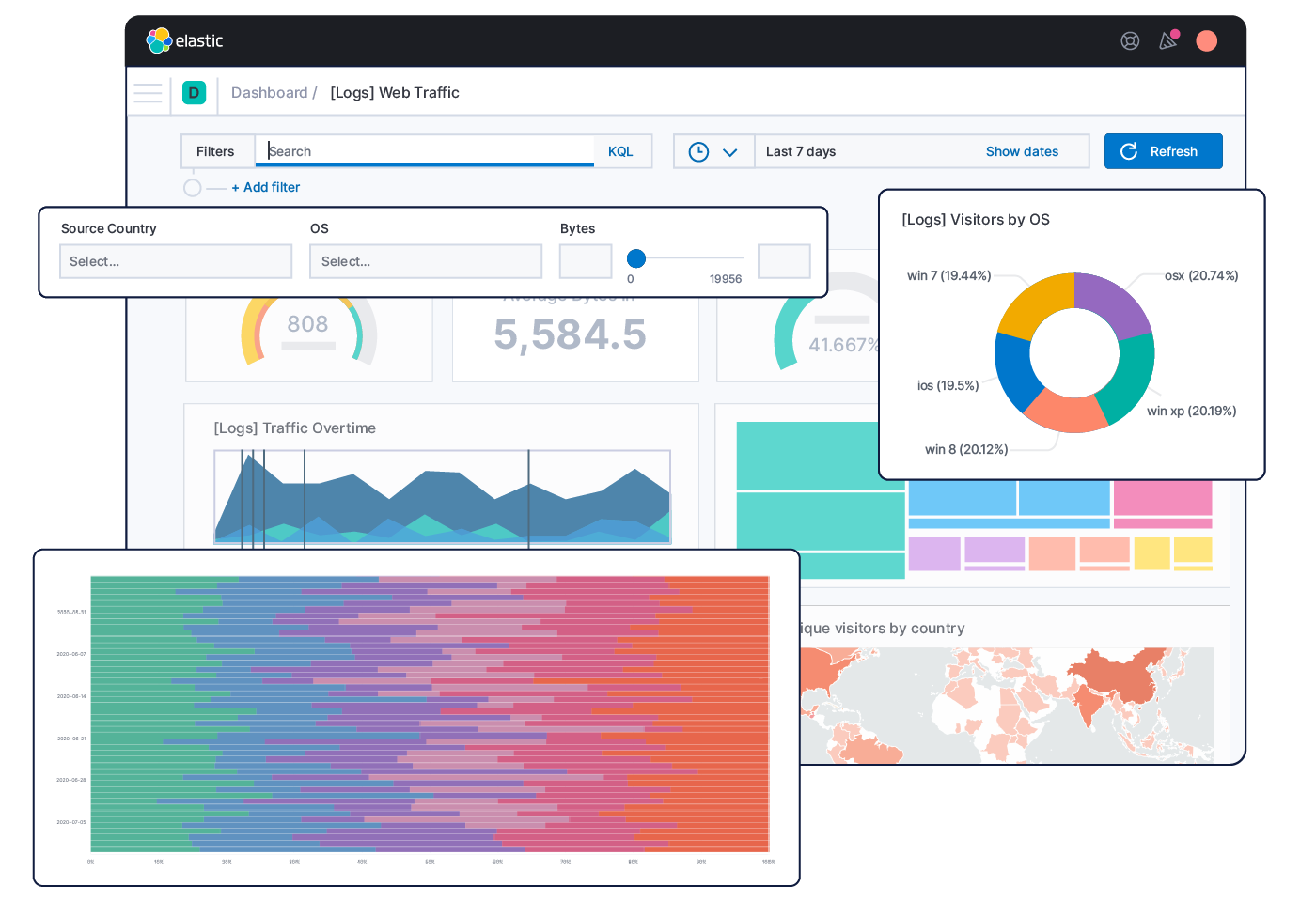
Understanding Kibana and Its Role
Kibana is a powerful data visualization tool that works in conjunction with Elasticsearch, allowing users to explore and analyze large volumes of data. While Kibana itself is not inherently insecure, misconfigurations can expose sensitive data to unauthorized access.
Risks Associated with Data Exposure
Data leaks like the one experienced by Frivol can lead to various security threats, including:
- Extortion: Cybercriminals may use the data to threaten individuals or organizations with exposure unless a ransom is paid.
- Phishing: Exposed email addresses can be targeted for phishing attacks, leading to further data breaches or financial loss.
These risks underscore the importance of securing data and implementing robust cybersecurity practices, as highlighted by Cybersecurity Ventures.

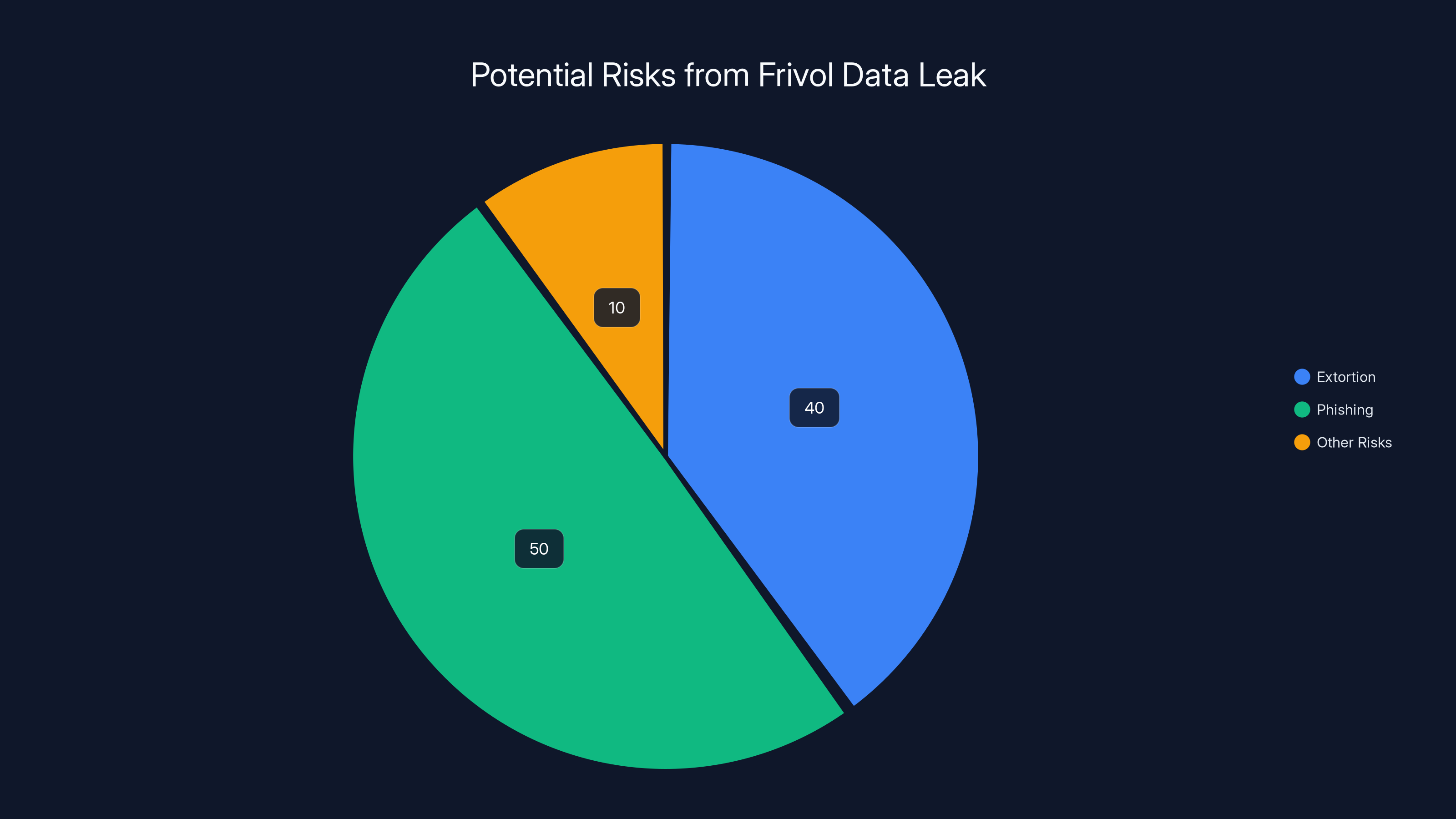
Phishing (50%) and extortion (40%) are the primary risks from the Frivol data leak, highlighting the need for better data security. Estimated data.
Best Practices for Preventing Data Leaks
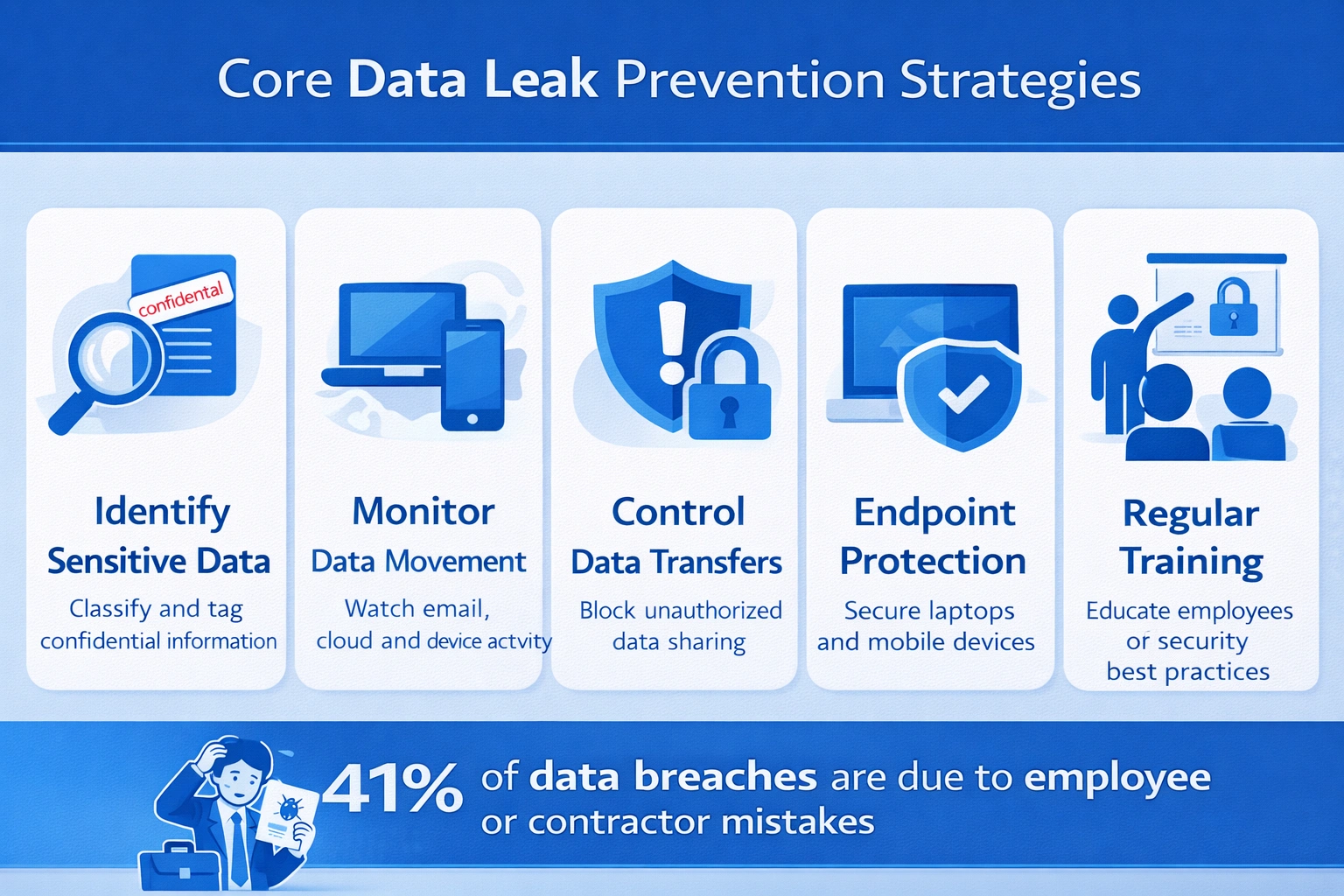
Preventing data leaks requires a comprehensive approach to cybersecurity. Here are some best practices to consider:
1. Implement Strong Access Controls
Access controls are critical in ensuring that only authorized users can access sensitive data. This includes using role-based access controls (RBAC), enforcing strong password policies, and implementing multi-factor authentication (MFA).
2. Regular Security Audits
Conducting regular security audits can help identify vulnerabilities in your systems before they are exploited. Audits should include:
- Penetration Testing: Simulate cyberattacks to identify potential weaknesses.
- Vulnerability Assessments: Regularly scan for and address vulnerabilities in your software and infrastructure.
3. Encrypt Sensitive Data
Data encryption ensures that even if data is accessed by unauthorized parties, it remains unreadable without the appropriate decryption key. Implement encryption for data at rest and in transit, as recommended by HIPAA Journal.
4. Monitor and Log Network Activity
Monitoring network activity can help detect suspicious behavior early. Implement logging and alert systems to track access and changes to sensitive data.
Common Pitfalls and Solutions
Despite best efforts, organizations may still encounter pitfalls when securing their data. Here are common issues and solutions:
Misconfigured Services
Services like Kibana can be powerful but are often complex to configure securely. Ensure that security settings are correctly applied and regularly reviewed, as noted by BitSight.
Overreliance on Perimeter Security
Relying solely on firewalls and perimeter defenses can leave internal assets vulnerable. Adopt a zero-trust architecture where every access request is verified.
Inadequate User Training
Employees are often the first line of defense against cyber threats. Provide regular training on security best practices and how to identify phishing attempts.

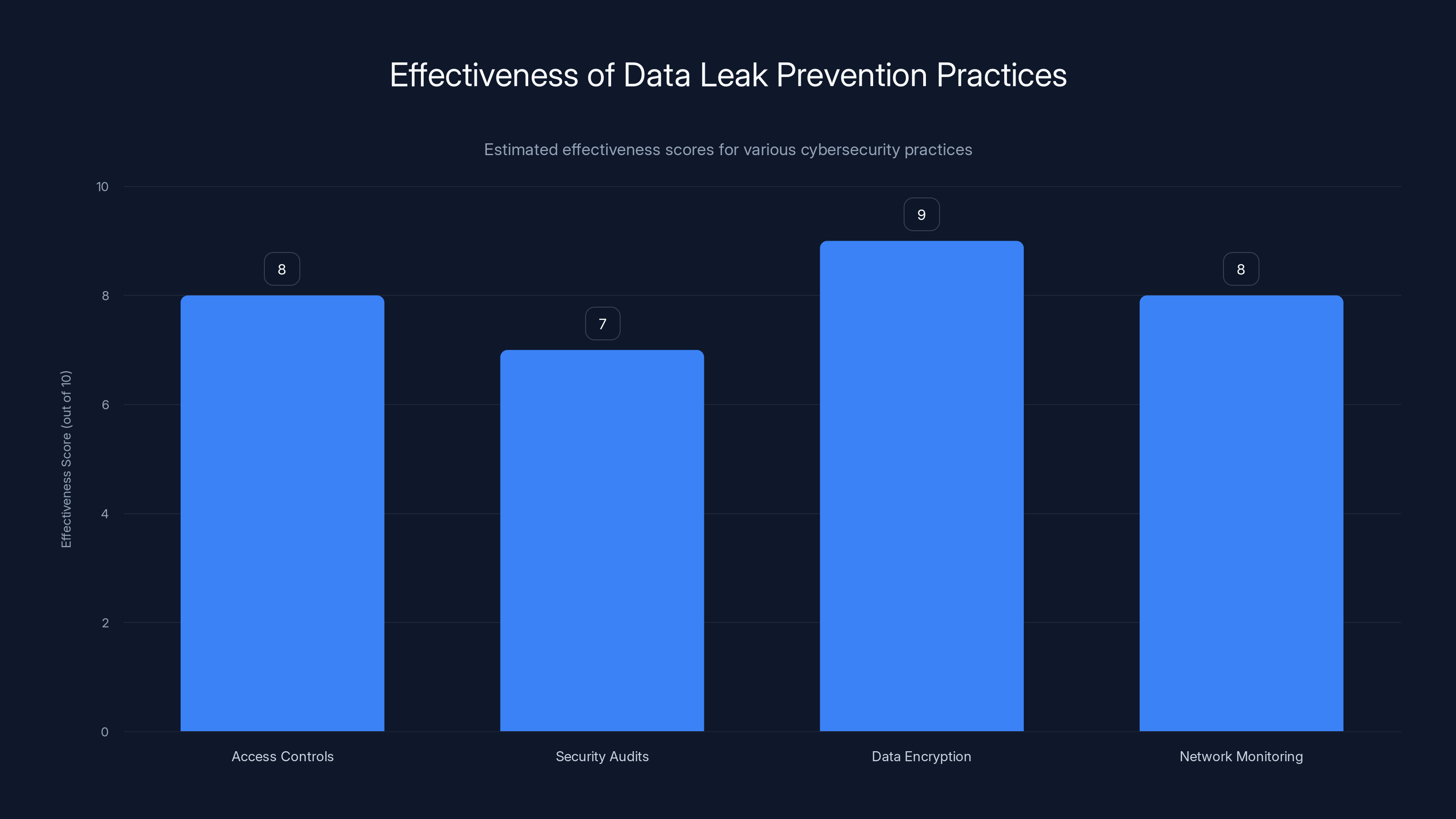
Data encryption is estimated to be the most effective practice for preventing data leaks, with a score of 9 out of 10. Estimated data.
Future Trends in Data Security
As cyber threats evolve, so must our strategies for combating them. Here are some emerging trends in data security:
AI-Driven Security Solutions
Artificial intelligence (AI) is increasingly being used to enhance security measures. AI can quickly analyze large datasets to identify patterns and anomalies indicative of a potential breach, as discussed by Anthropic.
Zero Trust Architecture
The zero-trust model operates on the principle of "never trust, always verify," ensuring that all users and devices are continuously authenticated and authorized. This approach is gaining traction, with the market projected to reach $51.6 billion by 2026, according to World Economic Forum.
Blockchain for Data Integrity
Blockchain technology can provide a tamper-proof record of data transactions, enhancing data integrity and security.

Conclusion
The Frivol data leak serves as a stark reminder of the importance of securing sensitive information. By implementing best practices and staying informed about emerging security trends, organizations can better protect themselves against data breaches. In a world where data is a valuable asset, ensuring its security is not just a technical necessity but a business imperative.
FAQ
What is a data leak?
A data leak occurs when sensitive information is unintentionally exposed to unauthorized individuals, often due to a security flaw or misconfiguration.
How does encryption protect data?
Encryption converts data into a coded format that is unreadable without the appropriate decryption key, ensuring that even if data is accessed, it remains secure.
What are the benefits of zero trust architecture?
Zero trust architecture enhances security by requiring continuous authentication and authorization for all users and devices, reducing the risk of unauthorized access.
How can AI improve cybersecurity?
AI can analyze large datasets to identify patterns and anomalies indicative of potential security threats, enabling faster and more accurate threat detection.
Why is user training important in cybersecurity?
User training helps individuals recognize and respond to security threats, reducing the likelihood of successful phishing attacks and other breaches.
What should organizations do after a data leak?
Organizations should immediately assess the scope of the leak, inform affected parties, and implement measures to prevent future incidents.
How can blockchain enhance data security?
Blockchain provides a tamper-proof record of data transactions, ensuring data integrity and preventing unauthorized modifications.
Key Takeaways
- Approximately 479,000 user emails exposed in the Frivol data leak.
- Exposed data poses risks of extortion and phishing.
- Implement strong access controls and security audits to prevent data leaks.
- AI-driven security measures are crucial for future threat detection.
- Zero trust architecture enhances security by verifying all access requests.
Related Articles
- Understanding the Marquis vs. SonicWall Case: Lessons on Firewall Security and Ransomware [2025]
- Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]
- Navigating 1Password's Upcoming Price Hike: How to Maximize Your Subscription [2025]
- US Diplomatic Efforts Against Foreign Data Sovereignty Laws [2025]
- 1Password Pricing Update: What Users Need to Know [2025]
- OpenAI's Legal Victory: Navigating the Complexities of Trade Secret Lawsuits in AI [2025]
![Understanding the Implications of Data Leaks: A Deep Dive into the Frivol Incident [2025]](https://tryrunable.com/blog/understanding-the-implications-of-data-leaks-a-deep-dive-int/image-1-1772040987859.jpg)



