Inside the World of Cyber Espionage: How Iranian Hackers Exploit Telegram for Global Data Breaches [2025]
The digital realm is teeming with threats, but few are as insidious as state-sponsored cyber espionage. Recently, the FBI shed light on a disturbing trend: Iranian hackers leveraging the popular messaging app, Telegram, to execute sophisticated malware attacks. In this deep dive, we'll explore how these cybercriminals operate, the vulnerabilities they exploit, and how you can protect yourself and your organization from falling victim.
TL; DR
- Iranian hackers are using Telegram to execute sophisticated malware attacks, targeting dissidents and journalists globally.
- The attack involves social engineering to distribute malware disguised as legitimate apps such as Telegram and WhatsApp.
- Remote control is established through Telegram bots, enabling hackers to steal data and monitor activities.
- Cybersecurity measures must evolve to detect such covert operations embedded in legitimate network traffic.
- Awareness and education are key to preventing social engineering attacks.

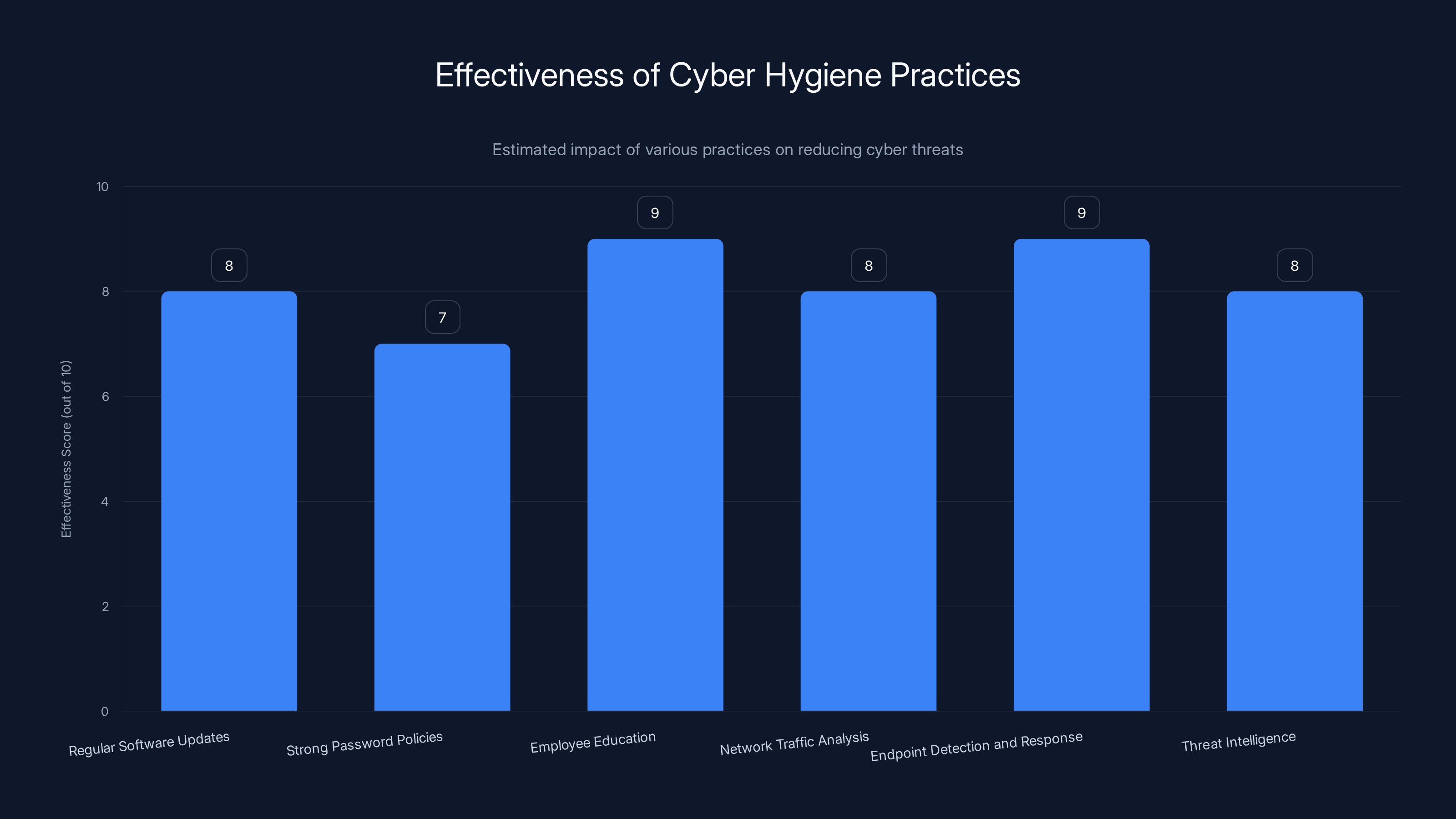
Employee education and endpoint detection are highly effective in reducing cyber threats. Estimated data.
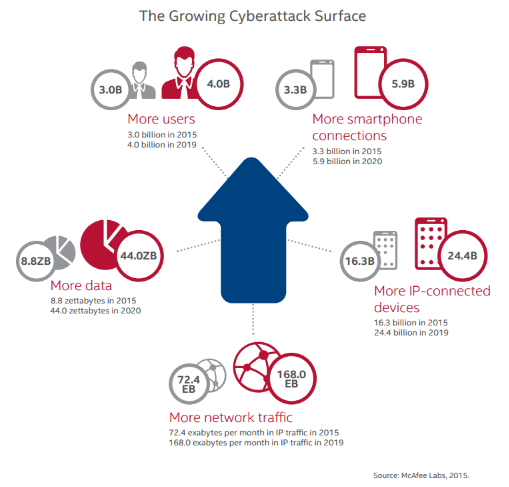
Understanding the Threat Landscape
In the complex world of cybersecurity, staying ahead of potential threats is crucial. Iranian hackers have developed a particular knack for exploiting popular applications as vectors for their malicious activities. By using Telegram, they benefit from a trusted platform, thus cloaking their operations under the guise of legitimate traffic.
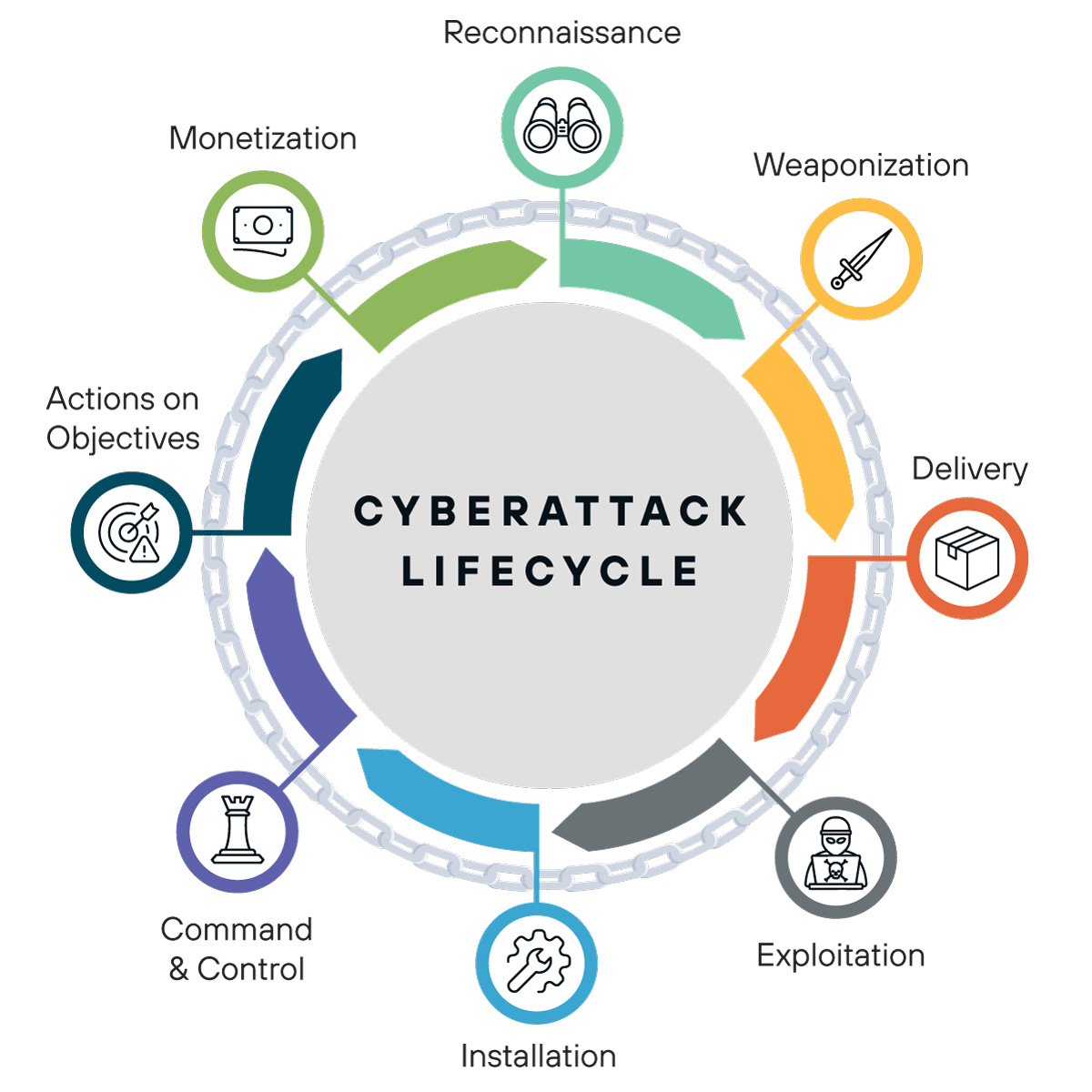
How the Attack Unfolds
The typical attack begins with social engineering, a technique wherein hackers impersonate trusted contacts or tech support personnel. Their goal is simple: to trick targets into downloading a malicious file, often masquerading as a legitimate app.
Once the malware is installed, the second phase kicks in. Here, the attackers exploit Telegram's API to establish a command-and-control (C&C) channel. This channel allows them to remotely access victims' devices, steal sensitive information, and monitor communications.
- Stage 1: Social engineering to spread malware disguised as apps.
- Stage 2: Establishing a C&C channel through Telegram for data exfiltration.
The Role of Telegram
Telegram is a highly secure messaging app known for its end-to-end encryption and privacy features. Ironically, these same features make it an attractive tool for cybercriminals. By embedding their operations within Telegram's network, hackers can easily blend in with legitimate traffic, making detection challenging for cybersecurity systems.
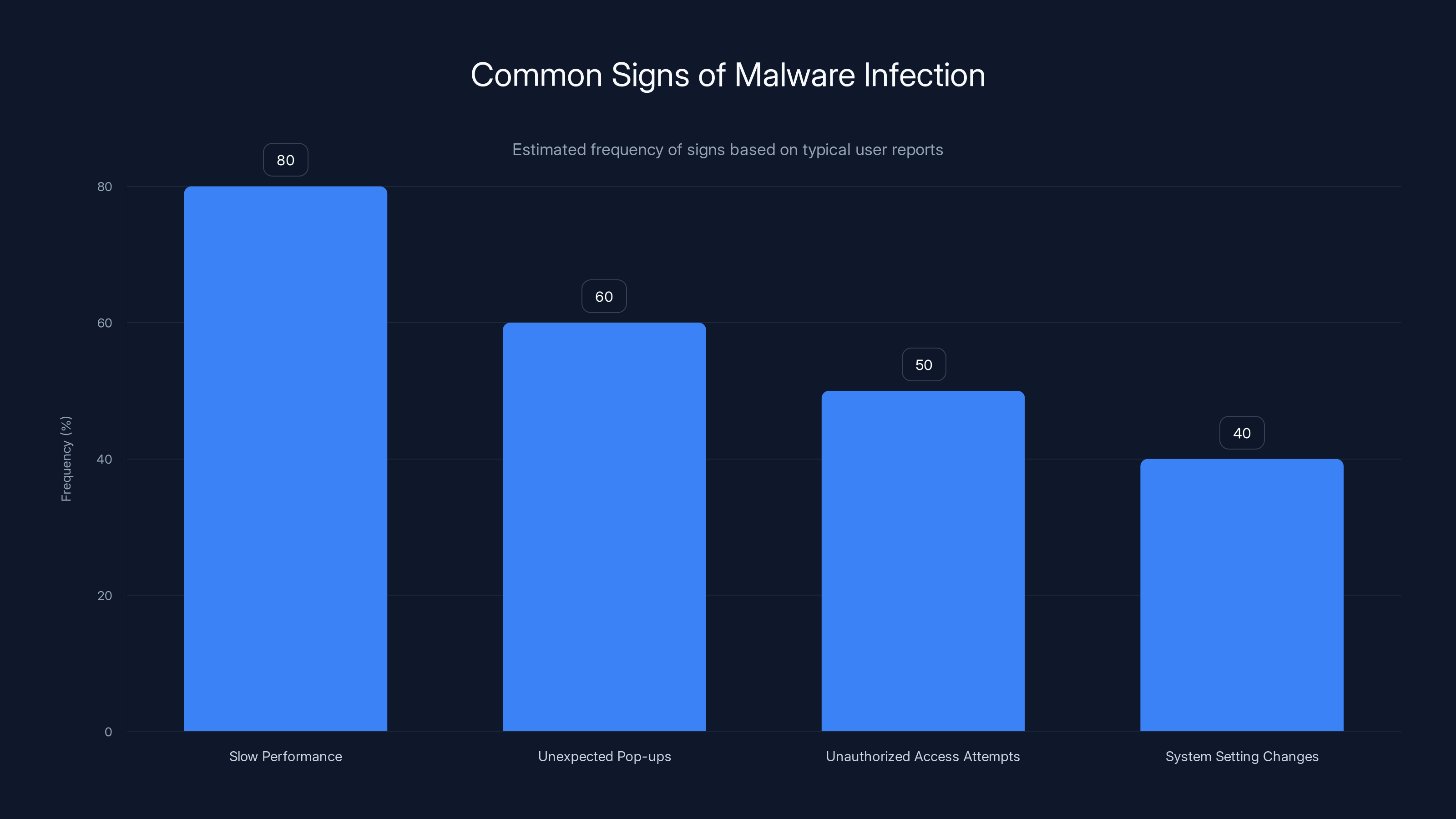
Slow device performance is the most common sign of malware infection, reported by 80% of affected users. Estimated data.
Technical Breakdown of the Attack
To truly understand the threat, let's delve into the technical details of how these attacks are orchestrated.
Social Engineering Tactics
Social engineering is an art as much as it is a science. Hackers often rely on psychological manipulation to gain the trust of their targets. Common tactics include:
- Impersonation: Pretending to be a known contact or IT support.
- Urgency: Creating a sense of urgency to encourage quick action.
- Trust Exploitation: Using familiar apps to lower suspicion.
Deployment of Malicious Software
Once the victim is convinced, they download a file that appears to be a legitimate application. This file, however, contains malware designed to infiltrate their system.
- File Types: Malicious files often carry extensions like
.exe,.apk, or.rar. - Obfuscation: The malware is often obfuscated or encrypted to avoid detection.
Establishing Command and Control
Telegram's API is leveraged to create a C&C channel. This channel is the hacker's lifeline to the victim's device.
- Bot Accounts: Hackers use Telegram bots to issue commands.
- Stealth Operations: Commands and data are hidden within normal Telegram traffic.

Protecting Yourself and Your Organization
Knowing the threat is only half the battle. Implementing robust security measures can significantly reduce the risk of falling victim to such sophisticated attacks.
Cyber Hygiene Best Practices
-
Regular Software Updates: Keep all applications and operating systems up to date to patch vulnerabilities.
-
Strong Password Policies: Use complex passwords and enable two-factor authentication where possible.
-
Educate Employees: Conduct regular training sessions on recognizing and responding to social engineering attempts.
Advanced Security Measures
- Network Traffic Analysis: Use security tools that can analyze network traffic for anomalies associated with C&C communications.
- Endpoint Detection and Response (EDR): Deploy EDR solutions to monitor and respond to suspicious activities on endpoints.
- Threat Intelligence: Stay informed about the latest cyber threats and tactics used by hackers.
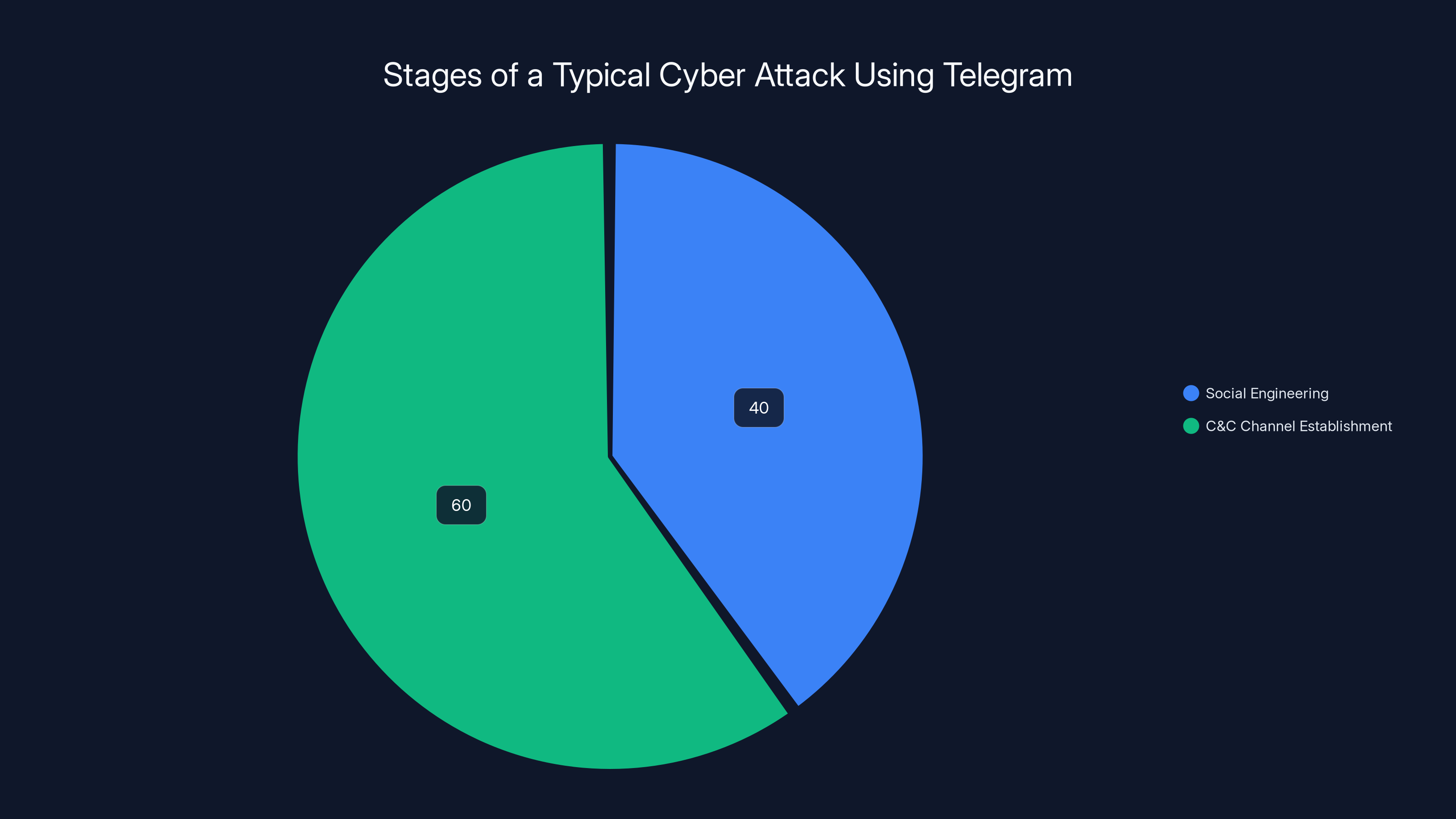
Estimated data suggests that 60% of the attack focus is on establishing a command-and-control channel through Telegram, while 40% is dedicated to social engineering tactics.
Real-World Case Studies
To provide context, let's examine some real-world scenarios where similar tactics have been used.
Case Study 1: Disguised Apps
In a recent attack, hackers disguised malware as a popular productivity app. Employees of a multinational corporation received an email urging them to download a 'security update.' Those who did unwittingly allowed hackers to infiltrate the company's network.
- Outcome: The breach led to the theft of sensitive corporate data, resulting in financial losses and reputational damage.
Case Study 2: Telegram Botnet
A government agency discovered a botnet operation controlled via Telegram. The botnet targeted devices to steal credentials and financial information.
- Outcome: The agency collaborated with cybersecurity firms to dismantle the botnet, but not before significant data was compromised.
Common Pitfalls and Solutions
Even with robust security measures, organizations can fall prey to cyberattacks. Here are common pitfalls and how to avoid them:
Over-reliance on Traditional Security
Many organizations still rely heavily on outdated security protocols that fail to detect sophisticated threats.
- Solution: Implement advanced AI-driven security solutions that can adapt to evolving threats.
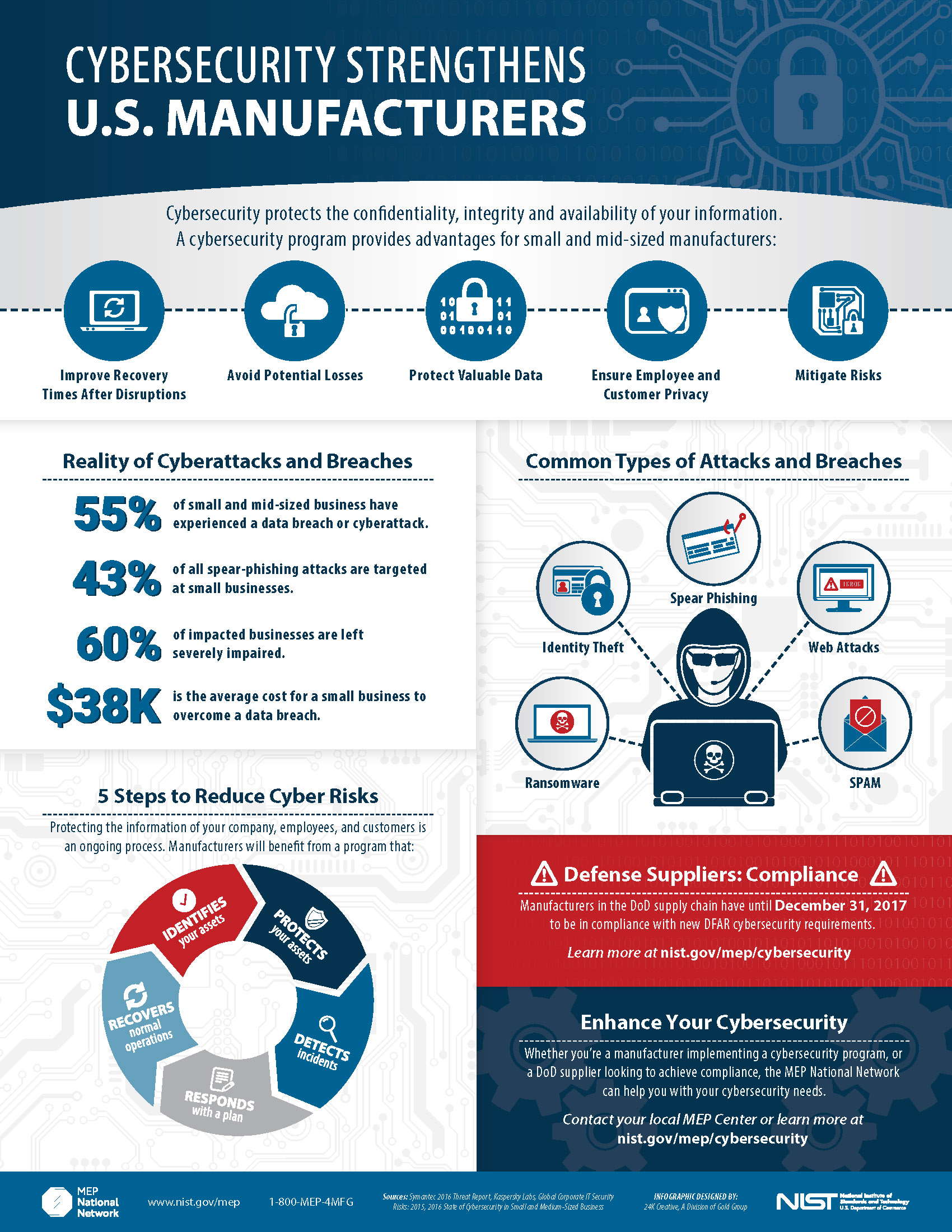
Neglecting Employee Training
Employees are often the weakest link in the security chain.
- Solution: Conduct regular training and simulations to improve employee awareness and response to cyber threats.
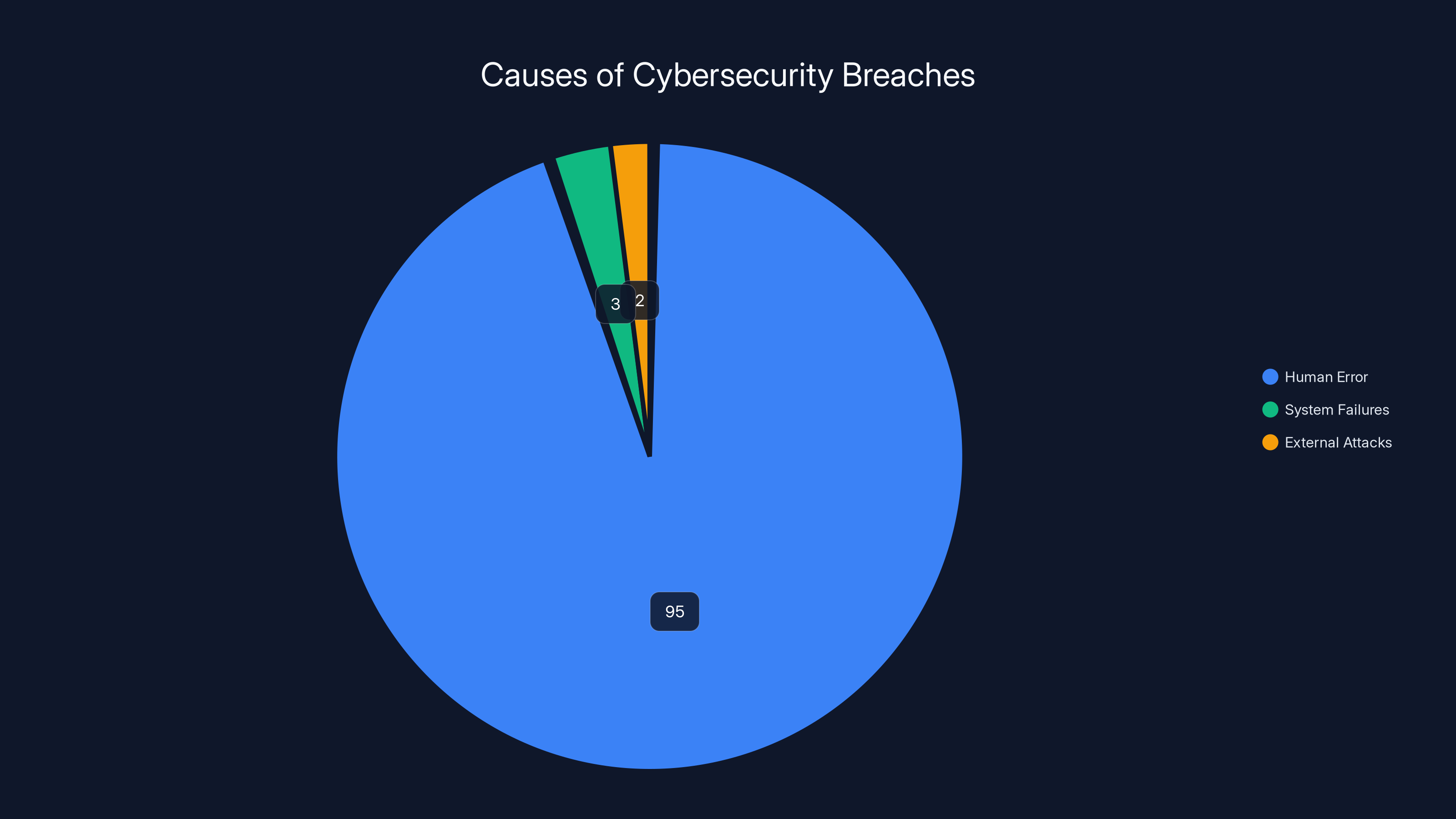
Human error accounts for 95% of cybersecurity breaches, highlighting the need for improved employee training.
Future Trends in Cybersecurity
The landscape of cybersecurity is continuously evolving. Here are some trends that are likely to shape the future:
Increased Use of AI in Cyber Defense
Artificial intelligence is being increasingly integrated into cybersecurity solutions. AI can analyze vast amounts of data quickly, identifying patterns and anomalies that may indicate a threat.
- Prediction: More organizations will adopt AI-driven cybersecurity tools to preemptively detect and neutralize threats.
Rise of Zero Trust Architecture
The Zero Trust model operates on the principle of 'never trust, always verify.' This approach assumes that threats can originate from both outside and inside the network.
- Impact: Organizations will implement Zero Trust to limit access and reduce the impact of breaches.
Enhanced Focus on Endpoint Security
With the rise in remote work, securing endpoints (laptops, mobile devices) has become a priority.
- Development: Expect advancements in EDR solutions that provide comprehensive protection for endpoints.
Recommendations for Organizations
To stay ahead of cyber threats, organizations must adopt a proactive approach to cybersecurity.
Conduct Regular Risk Assessments
Regularly assess the security posture of your organization to identify vulnerabilities and areas for improvement.
Foster a Culture of Security
Build a culture where security is everyone's responsibility. Encourage open communication about cybersecurity issues and incidents.
Collaborate with Cybersecurity Experts
Partner with cybersecurity firms and experts to gain insights into the latest threats and best practices.

Conclusion
As cyber threats become more sophisticated, staying informed and vigilant is crucial. By understanding the tactics used by hackers and implementing robust security measures, individuals and organizations can protect themselves against cyber espionage. Remember, in the world of cybersecurity, an ounce of prevention is worth a pound of cure.
FAQ
What is cyber espionage?
Cyber espionage refers to the use of hacking techniques to gain unauthorized access to confidential information for strategic or political advantage.
How do hackers use Telegram for cyber attacks?
Hackers exploit Telegram's API to create command-and-control channels, disguising malicious activities within legitimate network traffic.
What are common signs of a malware infection?
Common signs include slow device performance, unexpected pop-ups, unauthorized access attempts, and changes to system settings.
How can individuals protect themselves from social engineering attacks?
Remain skeptical of unsolicited communications, verify identities independently, and avoid downloading files from unknown sources.
Why is employee training important in cybersecurity?
Employees are often targeted in cyberattacks. Training helps them recognize threats and respond appropriately to mitigate risks.
What is the Zero Trust security model?
Zero Trust is a security framework that requires verification for every user and device, both inside and outside the network, before granting access.
How can AI enhance cybersecurity?
AI can analyze large data sets to detect anomalies, automate threat detection, and respond to incidents faster than traditional methods.
What role does endpoint security play in protecting remote workers?
Endpoint security ensures that devices used by remote workers are protected from malware, unauthorized access, and data breaches.
What should organizations do after a data breach?
Organizations should conduct a thorough investigation, notify affected parties, implement remediation measures, and update security protocols.
Key Takeaways
- Iranian hackers exploit Telegram to execute malware attacks globally.
- Social engineering is used to distribute malware disguised as apps.
- Telegram's API helps establish remote control for data theft.
- Cybersecurity must adapt to detect covert operations in legitimate traffic.
- Awareness and education are crucial in preventing social engineering attacks.
- Future trends include AI in cybersecurity and Zero Trust models.
Related Articles
- Understanding the FBI's Takedown of Pro-Iranian Hacking Group Websites [2025]
- US Takes Down Botnets Used in Record-Breaking Cyberattacks | WIRED
- Exposing the Visibility Gap: Unleashing the Full Potential of Agentic SOC [2025]
- How Biometric Authentication Can Tackle Bot Problems on Social Platforms [2025]
- The Future of Online Privacy: Age Checks and VPN Regulations [2025]
- URSP and SD-WAN: Navigating the Future of Network Slicing [2025]
![Inside the World of Cyber Espionage: How Iranian Hackers Exploit Telegram for Global Data Breaches [2025]](https://tryrunable.com/blog/inside-the-world-of-cyber-espionage-how-iranian-hackers-expl/image-1-1774280160775.jpg)



