Unmasking the Call Phantom Scam: A Deep Dive into the Google Play Breach [2025]
The digital world is a double-edged sword. On one side, it offers unparalleled convenience and connectivity. On the other, it opens doors to cyber threats that can compromise our privacy and security. Recently, a new threat emerged in the form of the Call Phantom scam, affecting millions of users through Google Play apps. This article delves into the intricacies of this scam, how it operated, and what you can do to safeguard your digital life.
TL; DR
- Over 7 million downloads: The Call Phantom scam affected 28 apps on Google Play.
- Data theft: Apps falsely promised access to call logs but stole personal information.
- Google's response: Rapid removal of fraudulent apps from the store.
- Prevention tips: Always verify app permissions and use robust security solutions.
- Future vigilance: Continuous updates and awareness are crucial in combating such threats.


Real-time scanning is rated as the most important feature in security solutions, followed by app reputation checks. Estimated data based on typical security software evaluations.
Introduction to the Call Phantom Scam
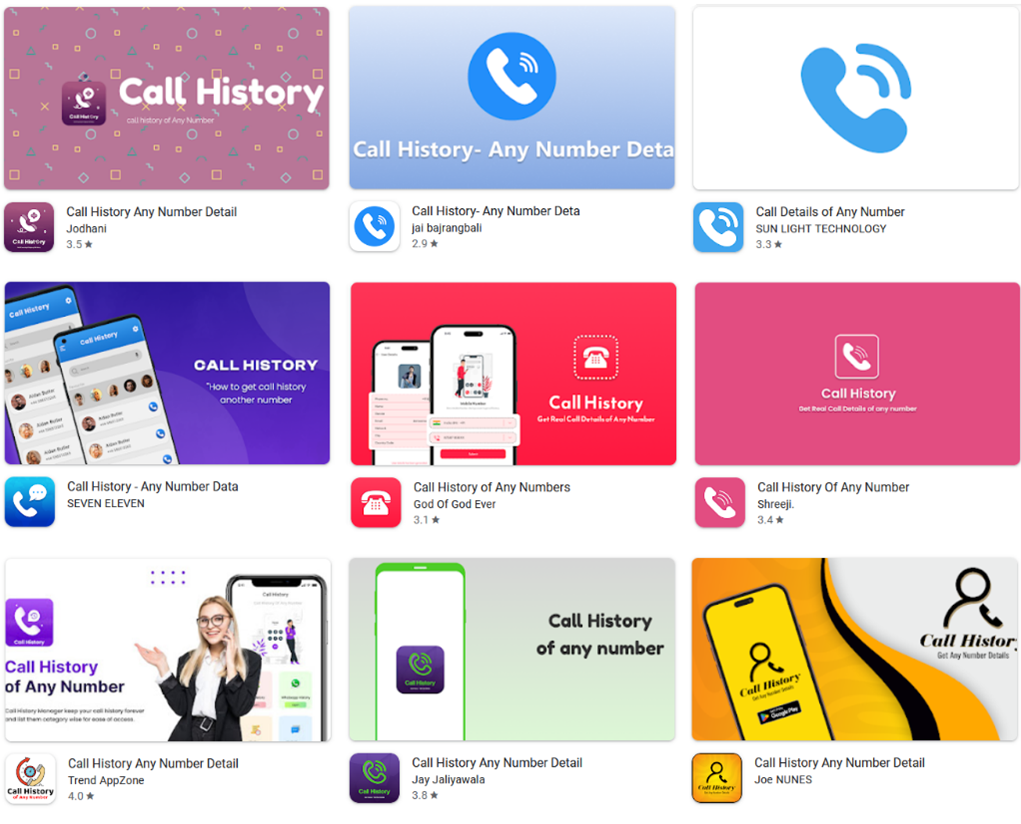
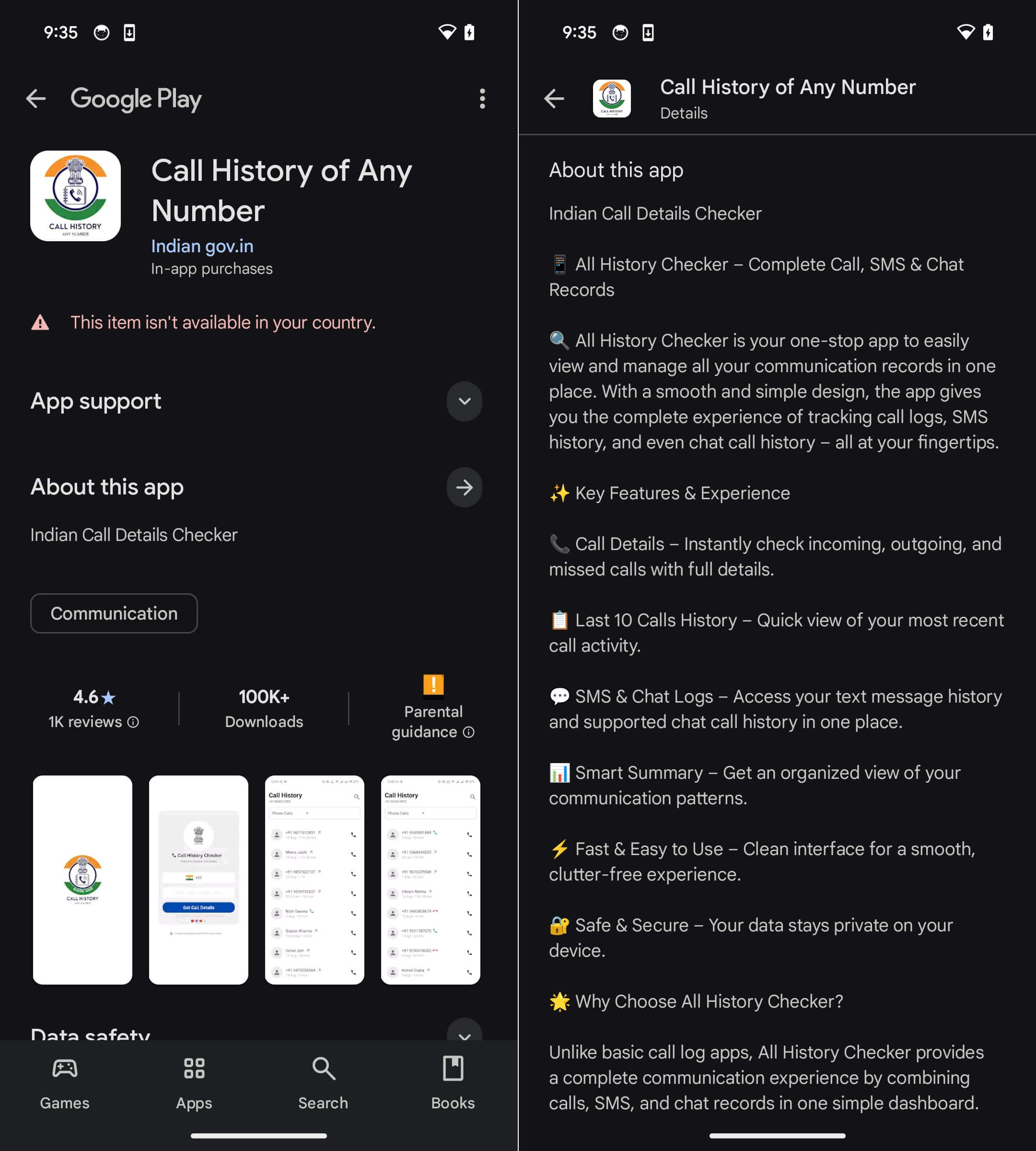
The Call Phantom scam is a recent cyber threat that infiltrated the Google Play Store, affecting over 7 million users. The scam involved 28 apps that falsely promised users access to their call logs, a feature that intrigued many but led to significant privacy compromises.
What Happened?
ESET, a leading cybersecurity firm, uncovered these fraudulent apps. They were designed to lure users with the promise of enhanced phone functionalities, specifically targeting those interested in monitoring their call logs. However, the real intent was to harvest personal data.
How Did It Work?
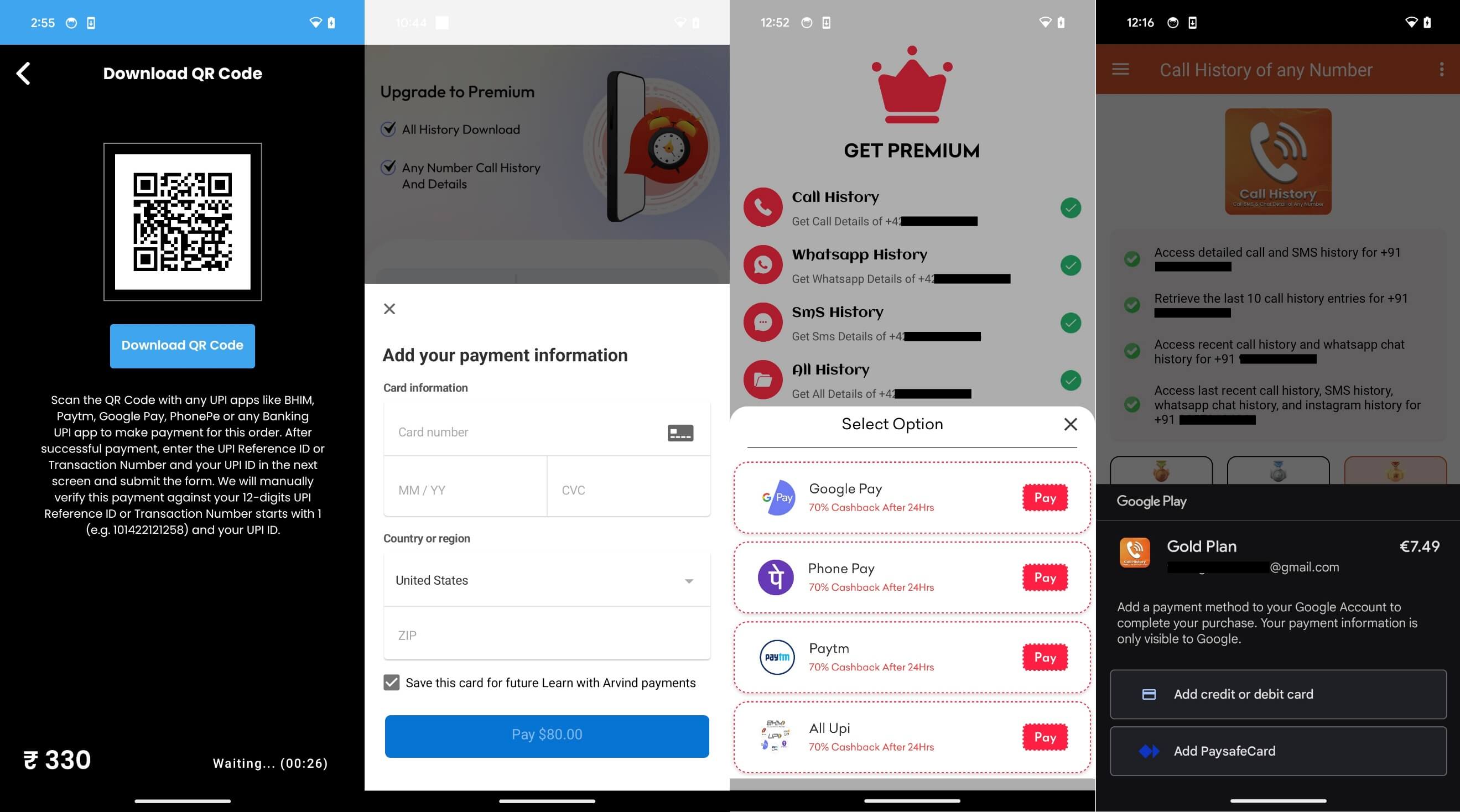
These apps requested extensive permissions, far beyond what was necessary for their advertised functions. Once installed, they could access personal information, including contact details and online activity. This data was then sent to remote servers, where it could be used for malicious purposes.

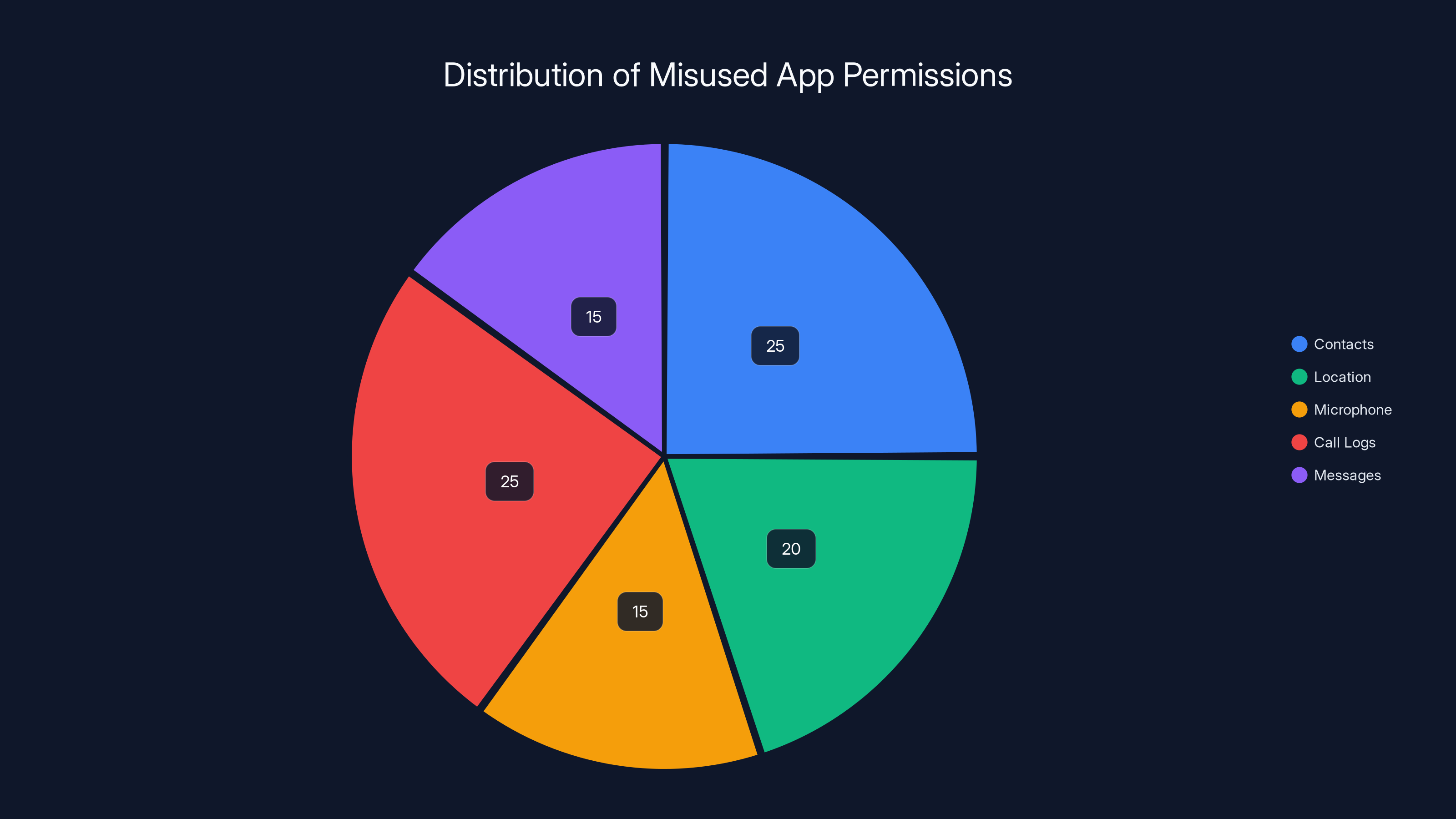
Estimated data shows that contacts and call logs were the most exploited permissions, each accounting for 25% of misuse in fraudulent apps.
The Core Mechanics of the Scam
Understanding the mechanics of the Call Phantom scam helps in identifying and preventing similar threats in the future.
App Permissions: The Trojan Horse
Permissions play a crucial role in how apps function. However, they also serve as a gateway for malicious activity if misused.
- Excessive Permissions: The fraudulent apps requested permissions unrelated to their functionality, such as access to contacts, location, and even the microphone.
- User Consent Manipulation: Many users unknowingly granted these permissions due to misleading prompts or the allure of promised features.
Data Harvesting Techniques
Once permissions were granted, these apps could:
- Access Call Logs: Though they promised this feature, the apps also accessed additional data like contacts and messages.
- Send Data to Remote Servers: Information was transferred to external servers controlled by the attackers, posing significant privacy risks.
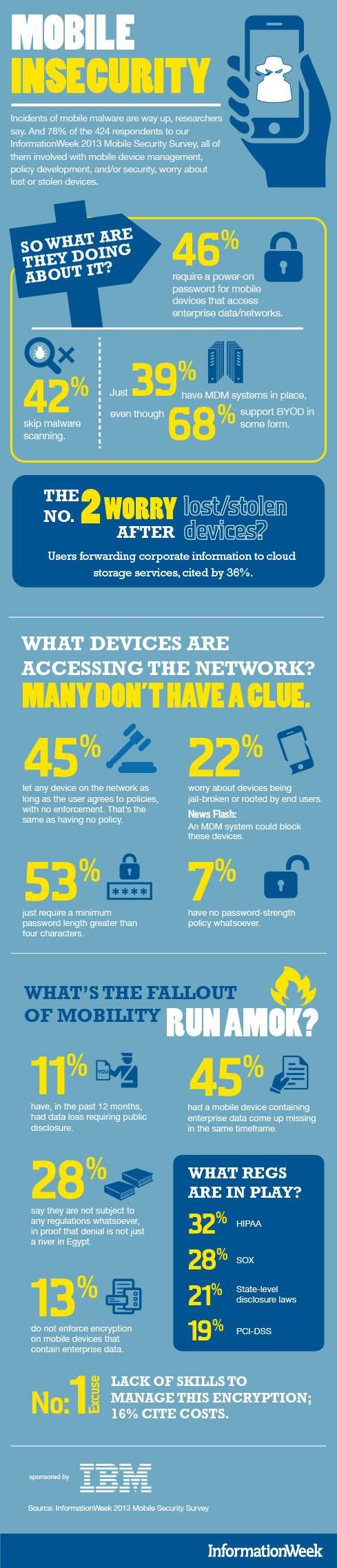
Practical Implementation Guide: Protecting Yourself
In the wake of such scams, it's crucial to adopt practices that protect your data and privacy.
Be Cautious with Permissions
Before downloading an app, review the permissions it requests. Ask yourself:
- Are these permissions necessary?
- What is the app's reputation and reviews?
- Is there a legitimate need for this app?
Use Trusted Security Solutions
Invest in robust security software that can detect and prevent malicious apps from installing on your device. Look for features like:
- Real-time scanning
- App reputation checks
- Automatic updates

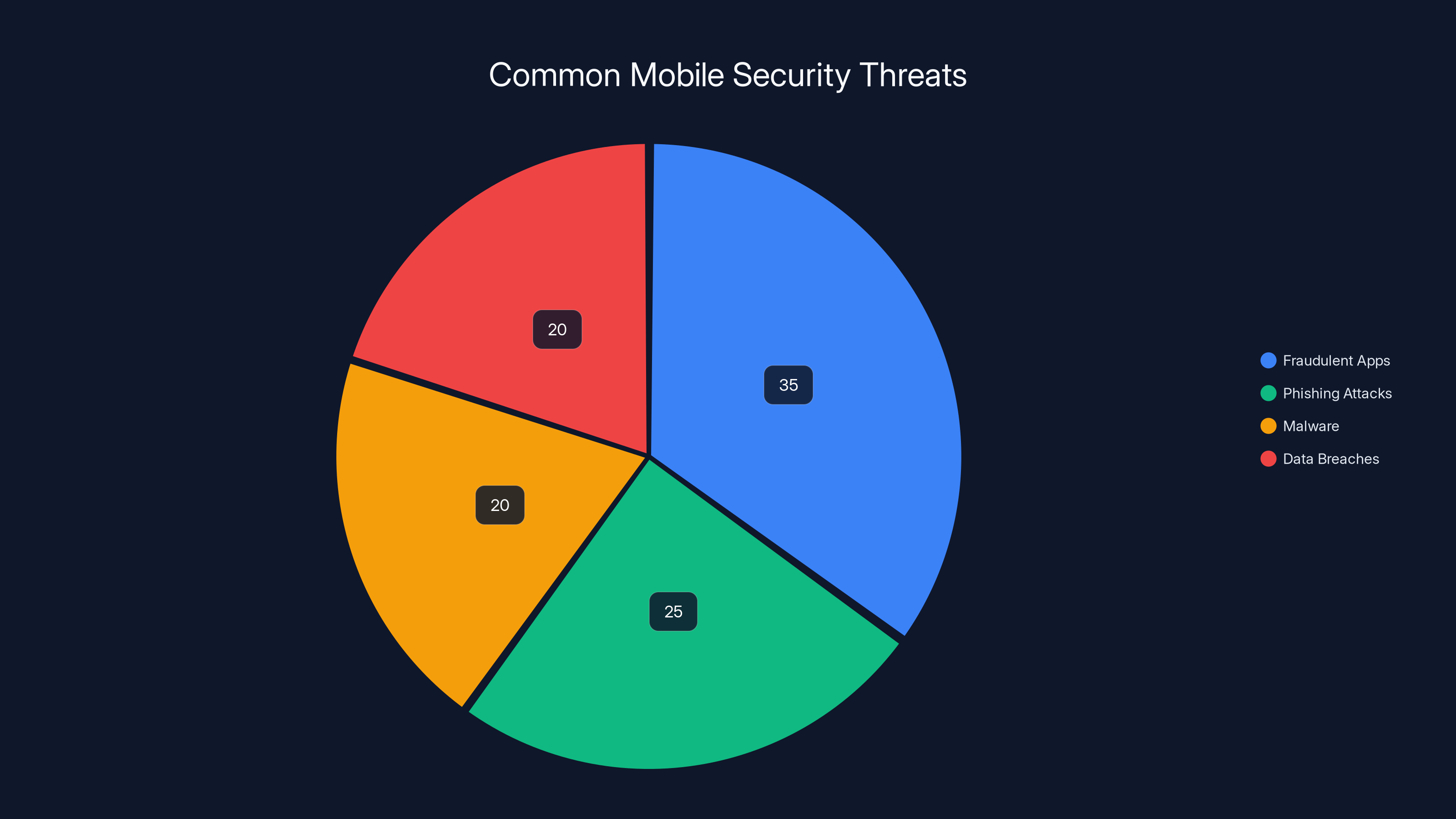
Fraudulent apps represent a significant portion of mobile security threats, highlighting the importance of cautious app permissions and trusted sources. (Estimated data)
Common Pitfalls and Solutions
Pitfall: Ignoring Permissions
Solution: Take time to read and understand permissions. If something seems unnecessary, reconsider installing the app.
Pitfall: Relying Solely on App Store Reviews
Solution: While reviews can be helpful, they are not foolproof. Look for detailed reviews from reputable sources.

Future Trends in Mobile Security
With the rise of mobile threats like Call Phantom, the future of cybersecurity will likely focus on several key areas:
Enhanced App Vetting Processes
App stores will continue to improve their vetting processes to detect and remove malicious apps more efficiently.
AI and Machine Learning in Security
AI technologies will play a significant role in identifying and responding to threats in real time.
Recommendations
Regular Software Updates
Ensure your device and apps are regularly updated to protect against known vulnerabilities.
Educate Yourself and Others
Stay informed about the latest threats and share this knowledge with friends and family to build a safer digital community.
Conclusion
The Call Phantom scam serves as a stark reminder of the vulnerabilities inherent in our digital lives. By staying informed and adopting best practices, we can protect ourselves from future threats. As technology evolves, so must our strategies for safeguarding our privacy and security.
FAQ
What is the Call Phantom scam?
The Call Phantom scam involved 28 fraudulent apps on Google Play that promised access to call logs but stole personal data instead.
How can I protect myself from similar scams?
Be cautious with app permissions, use trusted security solutions, and stay informed about the latest cybersecurity threats.
What should I do if I suspect an app is malicious?
Immediately uninstall the app, run a security scan, and report the app to the app store to protect other users.
How does Google respond to such threats?
Google actively monitors and removes fraudulent apps from its store, often in collaboration with cybersecurity firms.
Are all permissions dangerous?
Not all permissions are dangerous, but excessive or irrelevant permissions should raise red flags about an app's intentions.
What role does AI play in mobile security?
AI helps in real-time threat detection and response, enhancing the overall security of mobile devices.
Is it safe to download apps from third-party sources?
Downloading apps from third-party sources increases risk. Stick to official app stores to minimize exposure to malicious apps.
Key Takeaways
- Data-backed takeaway: Over 7 million users affected by the Call Phantom scam.
- Statistical insight: 28 apps involved in the scam, highlighting the scale of the threat.
- Actionable step: Always review app permissions before installation.
- Industry trend: Increasing use of AI in cybersecurity measures.
- Expert observation: Continuous education and awareness are vital in combating cyber threats.
Related Articles
- Understanding SMS Blasting: The Hidden Threat and How to Protect Against It [2025]
- The Canvas Hack Is a New Kind of Ransomware Debacle | WIRED
- Understanding the Canvas Data Breach: Impact on Top Universities and Future Security Measures [2025]
- North Korean Hackers Target Gamers with Trojanized Platform - Here's What to Look Out For [2025]
- Navigating Economic Challenges: Truecaller's Strategic Response to Declining Ad Sales [2025]
- The Role of Simple Fitness Bands in the AI Health Era [2025]
![Unmasking the CallPhantom Scam: A Deep Dive into the Google Play Breach [2025]](https://tryrunable.com/blog/unmasking-the-callphantom-scam-a-deep-dive-into-the-google-p/image-1-1778254537159.jpg)



