Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]
In late 2025, a major cyberattack on the French healthcare sector sent shockwaves through the industry, exposing critical vulnerabilities in medical IT infrastructure. Over 15 million records were leaked, including sensitive personal and health information. This article explores the details of the breach, the implications for healthcare cybersecurity, and the best practices that can help prevent such incidents in the future.
TL; DR
- Over 15 million records were leaked in a cyberattack on a French medical platform, as reported by Voz.
- Sensitive health information and administrative data were compromised, highlighting the need for improved security measures.
- The breach emphasizes the need for robust cybersecurity measures in the healthcare industry, according to HIPAA Journal.
- Recommendations include encryption, regular security audits, and staff training.
- The future of healthcare IT demands more advanced threat detection and response systems.

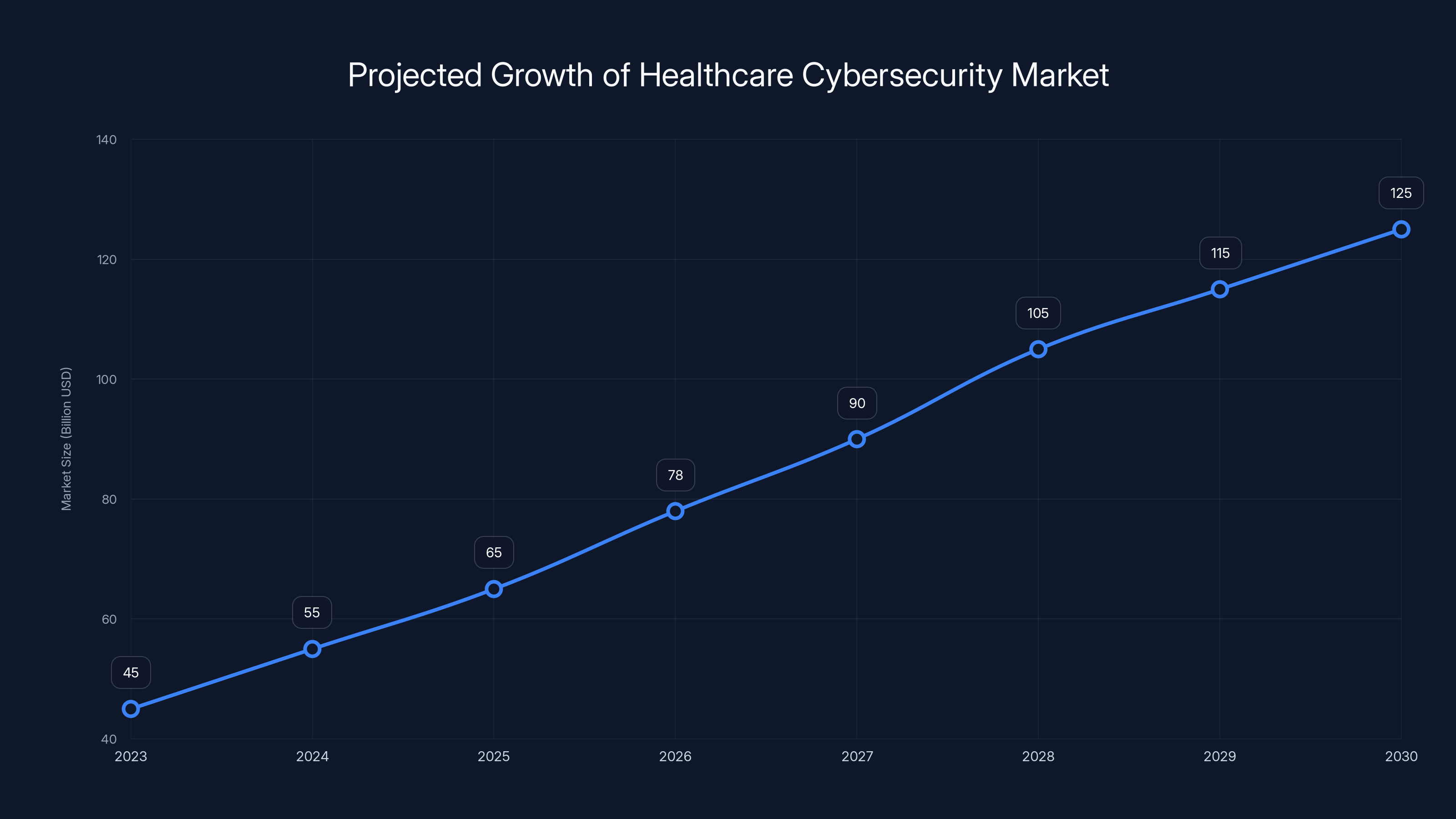
The healthcare cybersecurity market is projected to grow significantly, reaching $125 billion by 2030, according to Cybersecurity Ventures. Estimated data highlights the increasing importance of cybersecurity in healthcare.
Introduction
Last year, a staggering data breach on a French medical platform exposed the sensitive information of millions of individuals, including some senior politicians. This breach not only underscores the vulnerabilities present in the healthcare IT infrastructure but also serves as a wake-up call for the industry to bolster its defenses against cyber threats.
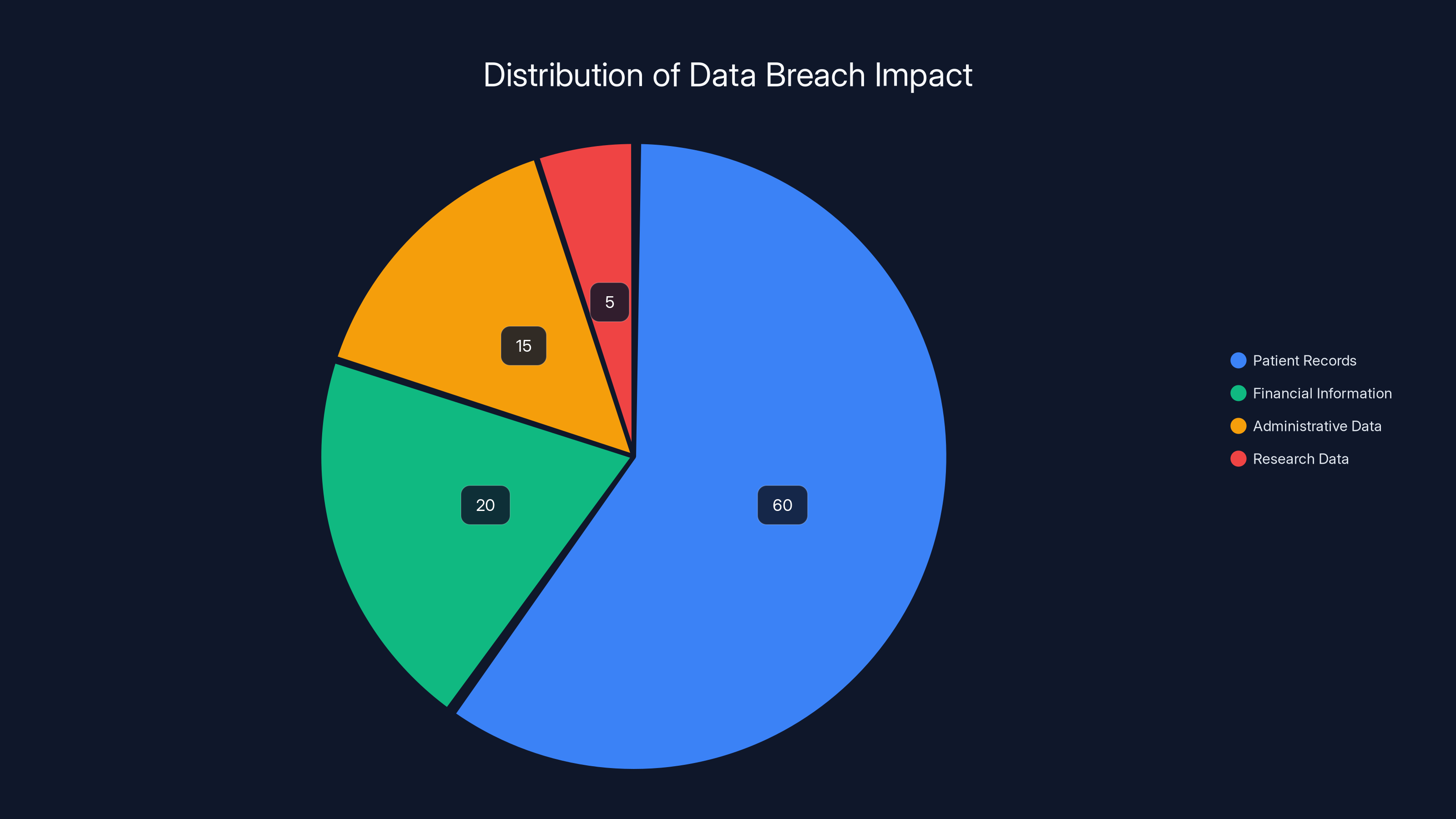
Estimated data shows that patient records constituted the majority of the breach, highlighting the need for enhanced data protection measures in healthcare systems.
The Breach: What Happened?
In late 2025, Cegedim Santé, a French healthcare software provider, confirmed a cyberattack targeting its Mon Logiciel Medical (MLM) platform. This web-based management application is widely used by healthcare professionals for managing patient records and administrative tasks. The attackers exfiltrated patient administrative data and limited doctor notes, highlighting a significant lapse in data security.
How the Breach Occurred
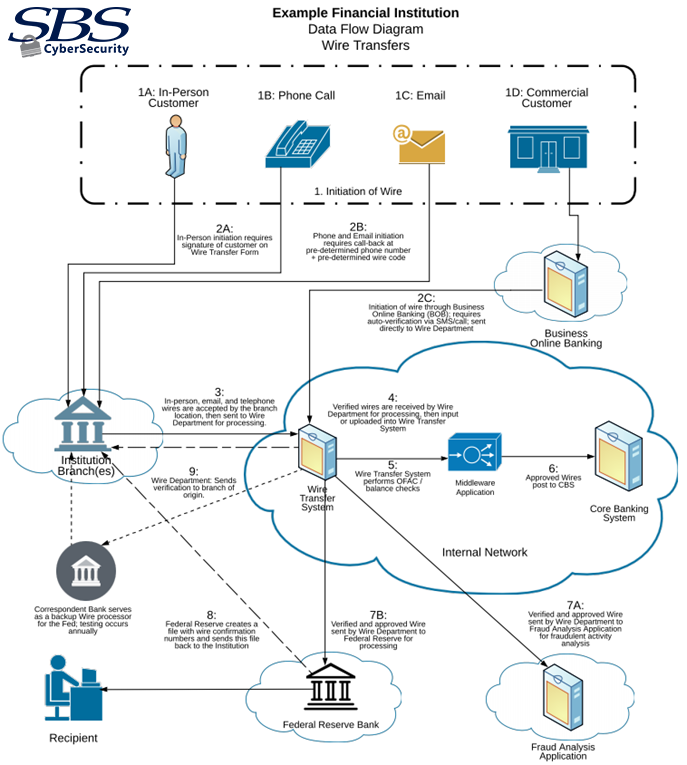
The breach was identified when abnormal application request behavior was detected on the MLM accounts used by doctors. This unusual activity suggested unauthorized access, prompting an immediate investigation.
The Impact of the Breach
The breach affected over 15 million records, including sensitive health information. This incident not only compromised patient privacy but also raised concerns about the potential misuse of the data. Additionally, the leak's impact on senior politicians' records could have broader political implications.
Understanding the Vulnerabilities
Common Security Flaws in Healthcare IT
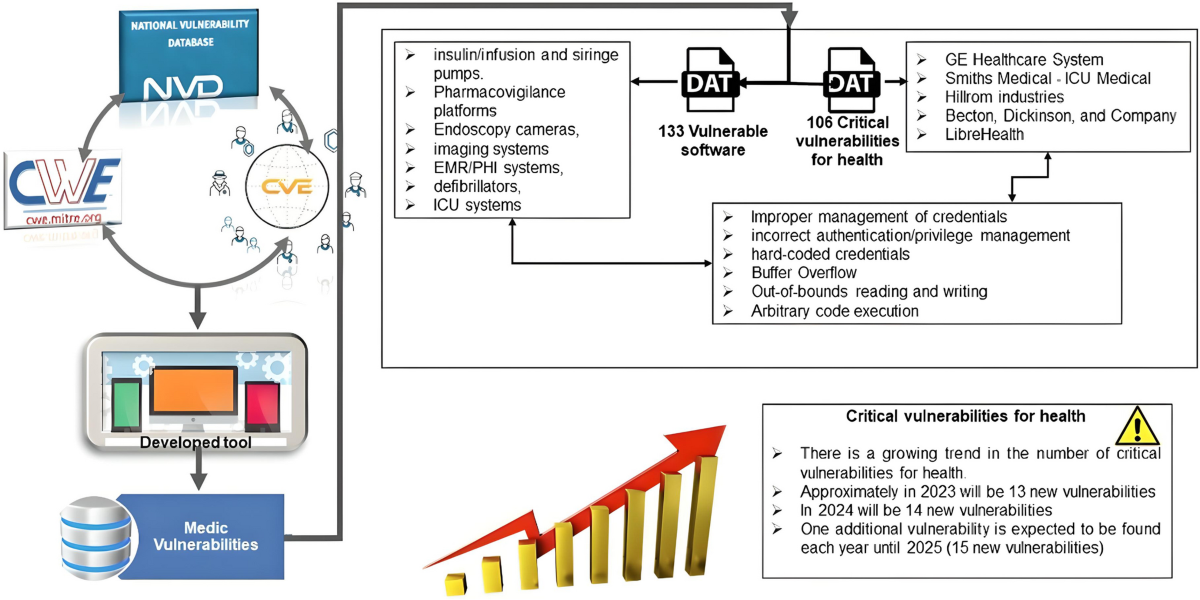
Healthcare IT systems are often plagued by several vulnerabilities, including:
- Outdated Software: Many healthcare institutions run legacy systems that are no longer supported with security updates, as noted by HIPAA Journal.
- Insufficient Encryption: Data at rest and in transit may not be adequately protected by encryption.
- Lack of Staff Training: Employees may not be adequately trained to recognize phishing attempts or other social engineering tactics.
Specific Vulnerabilities in Cegedim Santé's System
While the exact vulnerabilities exploited in the Cegedim Santé breach remain undisclosed, common issues could have included insufficient access controls and unpatched software vulnerabilities.
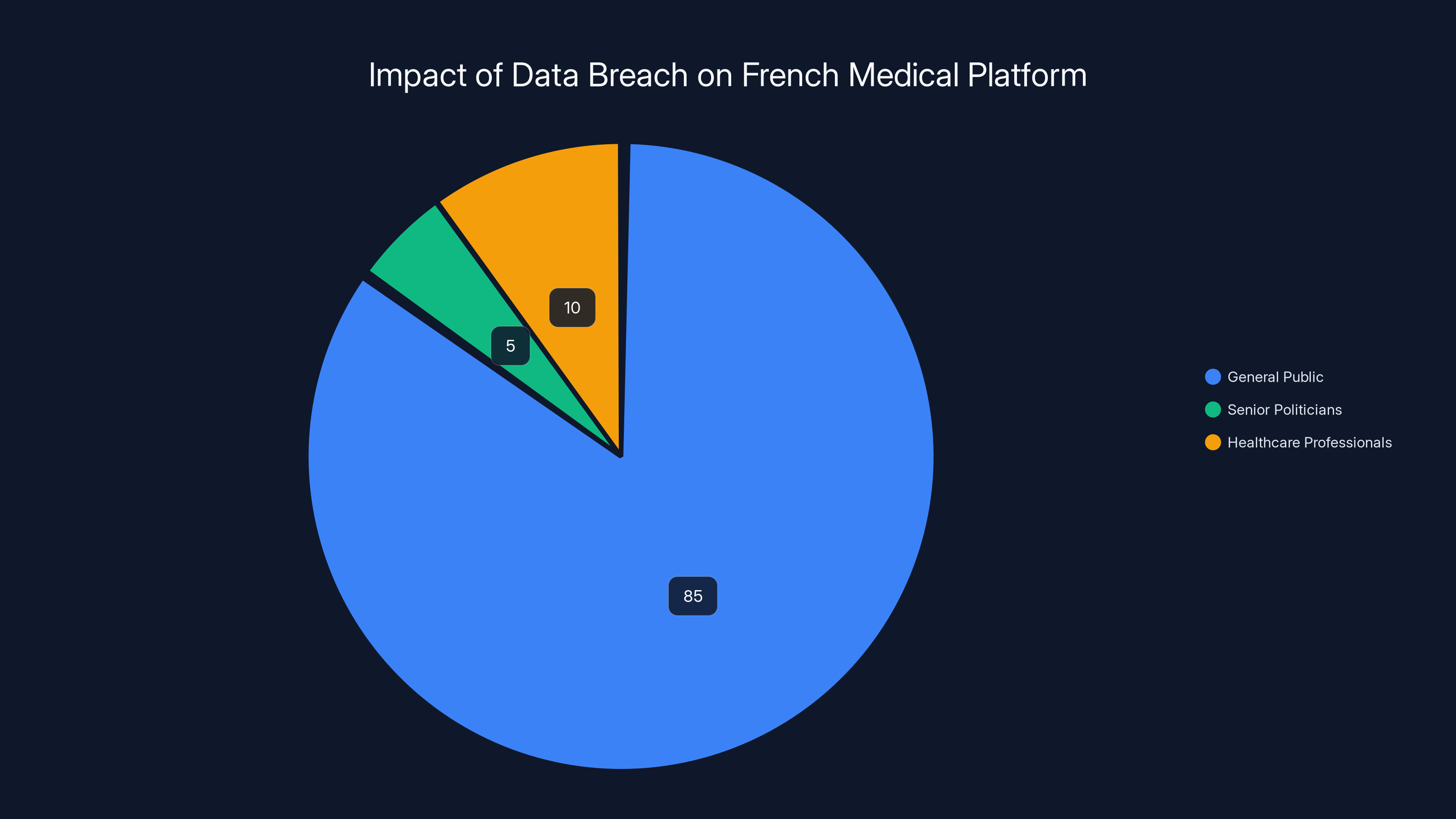
Estimated data shows that the majority of affected individuals were from the general public, with a small percentage being senior politicians and healthcare professionals.
Best Practices for Healthcare Cybersecurity
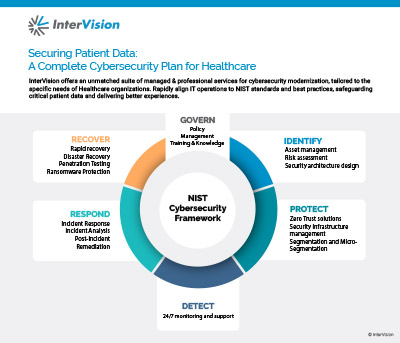
To prevent future breaches, healthcare providers must adopt comprehensive cybersecurity strategies. Here are some best practices:
Implement Strong Access Controls
- Role-Based Access Control (RBAC): Ensure that users have access only to the data necessary for their roles.
- Multi-Factor Authentication (MFA): Require multiple forms of verification for system access.
Regular Security Audits
Conduct regular security audits to identify and address vulnerabilities before they can be exploited.
Data Encryption
Encrypt data both at rest and in transit to protect sensitive information from unauthorized access.
Staff Training
Regularly train employees on cybersecurity best practices, including recognizing phishing attempts and secure password management.
Incident Response Plan
Develop and regularly update an incident response plan to quickly mitigate the impact of a breach.

Future Trends in Healthcare Cybersecurity
The future of healthcare cybersecurity will likely see several emerging trends:
Artificial Intelligence and Machine Learning
AI and machine learning can enhance threat detection and response capabilities, allowing for quicker identification of suspicious activities.
Blockchain Technology
Blockchain can provide a secure, decentralized method of storing and sharing patient data, reducing the risk of unauthorized access.
Regulatory Changes
Governments are expected to introduce stricter regulations regarding data protection in healthcare, increasing compliance requirements for providers.

Common Pitfalls and Solutions
Overlooking Insider Threats
Many breaches are the result of insider threats, whether intentional or accidental. Implementing strict access controls and monitoring can mitigate this risk.
Underestimating Phishing Risks
Phishing remains a prevalent threat in healthcare. Training staff to recognize phishing attempts is crucial for preventing unauthorized access.
Ignoring Software Updates
Failing to regularly update software can leave systems vulnerable to known exploits. Implement automated update systems to ensure all software remains up-to-date.

Practical Implementation Guides
Here's how healthcare providers can implement robust cybersecurity measures:
Step 1: Conduct a Risk Assessment
Identify potential vulnerabilities in your systems and prioritize them based on the level of risk they pose.
Step 2: Develop a Security Policy
Create a comprehensive security policy that outlines how data will be protected and how breaches will be handled.
Step 3: Implement Technical Controls
Deploy technical controls such as firewalls, intrusion detection systems, and encryption to protect data.
Step 4: Train Your Staff
Educate your staff on cybersecurity best practices and conduct regular training sessions to reinforce this knowledge.
Step 5: Test Your Systems
Regularly test your security systems with penetration testing to identify and address vulnerabilities.
Conclusion
The recent data breach on the French medical platform serves as a stark reminder of the vulnerabilities present in healthcare IT systems. By adopting best practices, staying informed about emerging trends, and preparing for future threats, healthcare providers can better protect their patients' sensitive information.

FAQ
What caused the data breach in the French medical platform?
The breach was caused by unauthorized access through abnormal application request behavior, suggesting vulnerabilities in the system's security measures, as detailed by Voz.
How can healthcare providers prevent data breaches?
Healthcare providers can prevent breaches by implementing strong access controls, regular security audits, data encryption, staff training, and an incident response plan.
What are the future trends in healthcare cybersecurity?
Future trends include the use of AI and machine learning for threat detection, blockchain for secure data storage, and increased regulatory requirements.
Why is encryption important in healthcare IT?
Encryption protects sensitive data from unauthorized access by ensuring that even if data is intercepted, it cannot be read without the decryption key.
How can staff training improve cybersecurity in healthcare?
Training helps staff recognize and respond to cybersecurity threats, reducing the risk of breaches through human error or social engineering tactics.
What should be included in an incident response plan?
An incident response plan should include procedures for identifying, containing, and mitigating breaches, as well as communication strategies and recovery plans.
How does AI improve threat detection in healthcare?
AI can analyze large volumes of data to identify patterns and anomalies indicative of potential threats, allowing for quicker and more accurate threat detection.

Key Takeaways
- Over 15 million records were leaked in a French healthcare data breach, highlighting severe IT vulnerabilities, as reported by HIPAA Journal.
- Implementing robust access controls, encryption, and regular audits are critical for healthcare cybersecurity.
- AI and blockchain technologies are emerging as key tools in enhancing cybersecurity measures.
- Regular staff training can significantly reduce the risk of breaches through human error or social engineering.
- Future healthcare IT must adapt to stricter regulations and more advanced threat detection systems.
Related Articles
- AI Data Centers Could Reduce Power Draw on Demand [2025]
- Exploring the Consciousness Frontier: DMT, Alien Encounters, and Human Understanding [2025]
- Beat Weaver: A Rhythmic Odyssey Blending Amplitude and Thumper [2025]
- The Complex World of Leaks: Activision's Call of Duty Controversy [2025]
- The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]
- FCC Endorses Paramount and WBD Merger: A Simpler Path Forward [2025]
![Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]](https://tryrunable.com/blog/massive-data-breach-on-french-medical-platform-lessons-and-f/image-1-1772627656104.jpg)



