Introduction
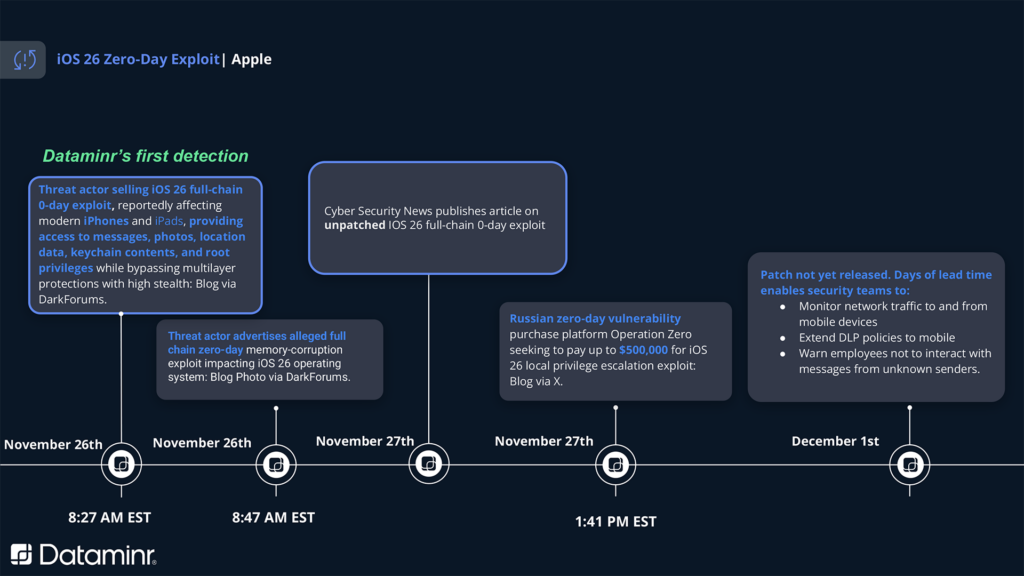
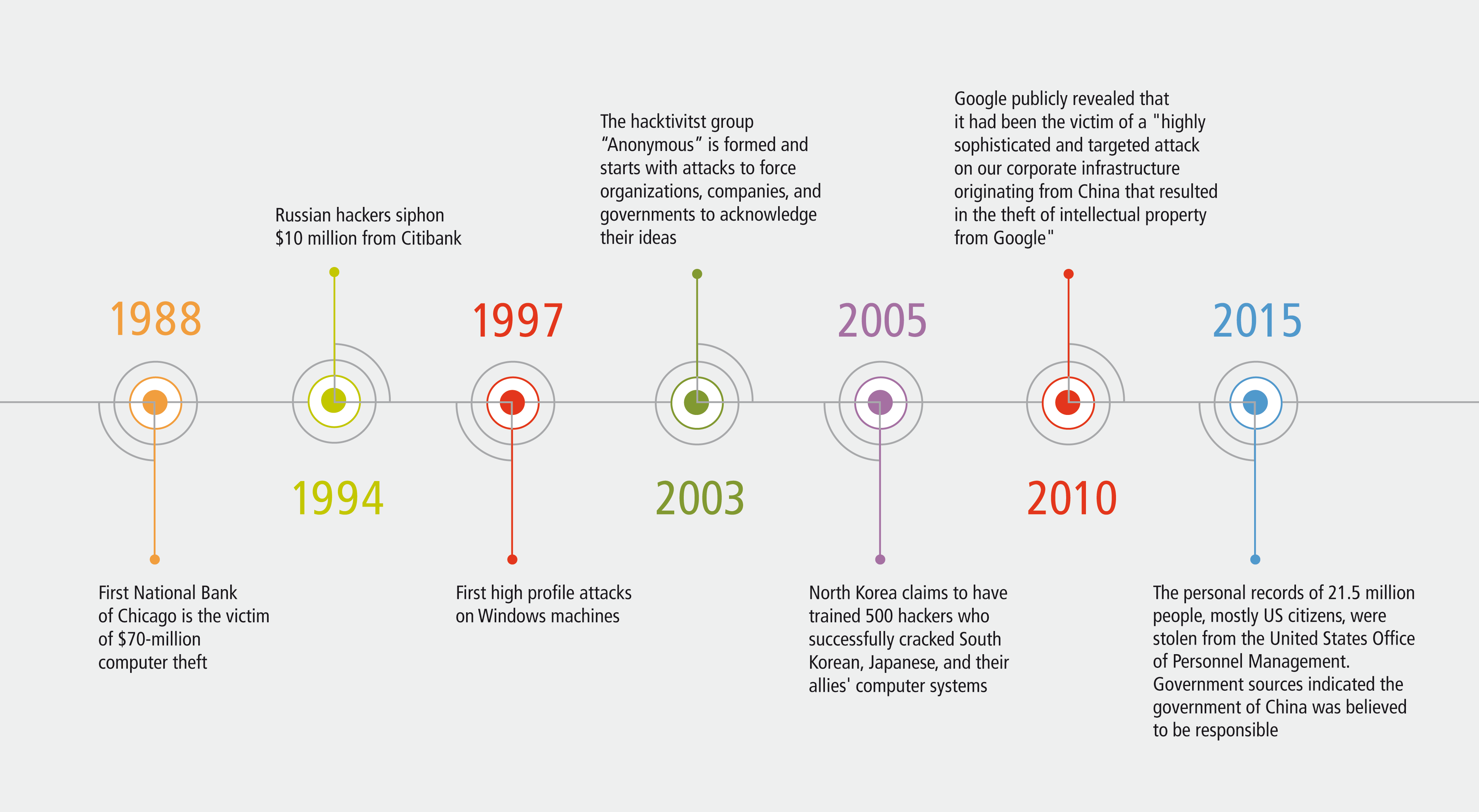
Last year, a series of shocking discoveries rocked the cybersecurity community: a suite of powerful government-designed hacking tools, initially intended for national security purposes, found its way into the hands of cybercriminals. This phenomenon highlights a growing trend where tools meant for protection are turned against their creators, posing significant threats to global cybersecurity. According to Nextgov, these tools have been obtained by foreign spies and cybercriminals, raising alarms across the globe.

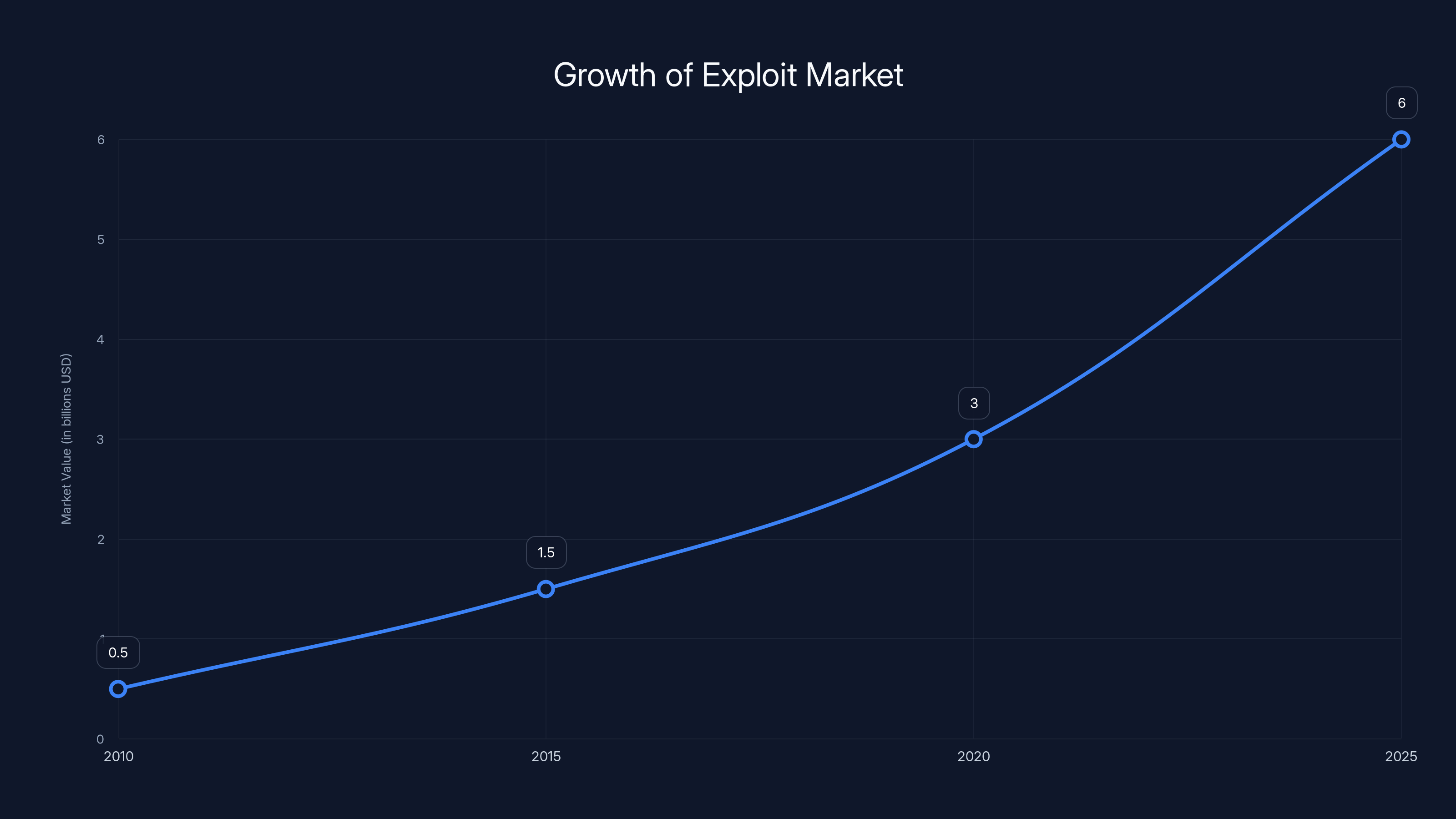
The market for cyber exploits has grown exponentially, with an estimated value increase from
TL; DR
- Government-grade hacking tools: Initially developed for state security, are now accessible to cybercriminals. TechCrunch reported on a US defense contractor who leaked such tools to Russia.
- Coruna exploit: A highly sophisticated tool initially used by governments is now being exploited by hackers, as detailed by Help Net Security.
- Global impact: Cyber attacks are becoming more sophisticated, targeting iPhones with older software versions, as noted by CyberScoop.
- Emerging markets for exploits: There is a growing market for second-hand exploits, increasing the risk of cybercrime.
- Future implications: The proliferation of these tools calls for urgent cybersecurity measures and international cooperation.
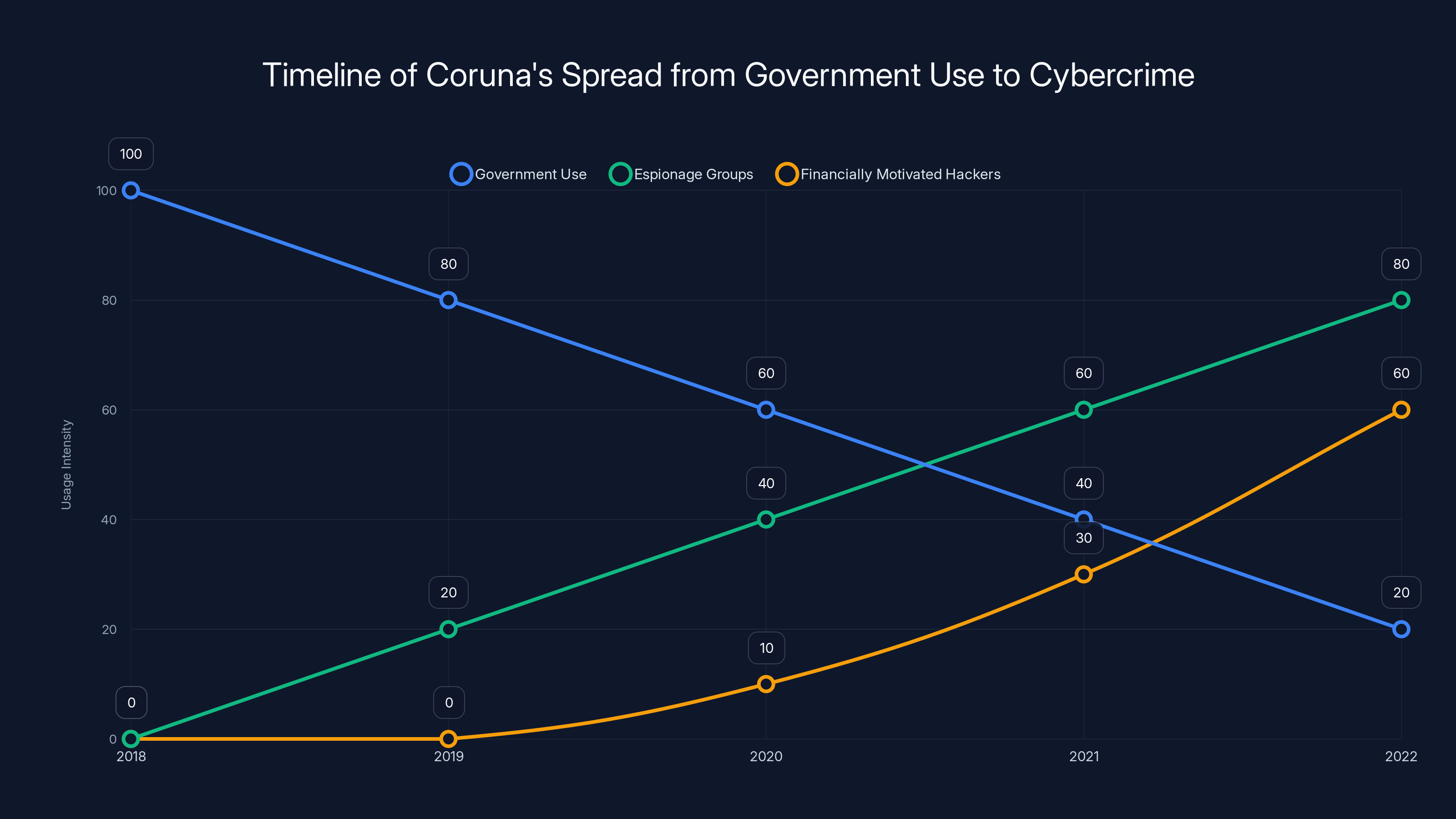
The Coruna exploit transitioned from government use to widespread adoption by espionage groups and financially motivated hackers from 2018 to 2022. Estimated data.
Understanding the Coruna Exploit
The Coruna exploit is a highly sophisticated piece of software initially designed for espionage by state actors. Its capabilities include infiltrating iPhones running older software versions, allowing attackers to access sensitive data, control device functionalities, and monitor user activities. Originally developed for surveillance by a government entity, it has since leaked into the broader cybercriminal ecosystem. iVerify has detailed the first known mass iOS attack using this exploit.
What Makes Coruna So Powerful?
- Sophisticated Code: Coruna's codebase is complex, allowing it to bypass many traditional security measures.
- Stealth Operations: It operates silently, making detection difficult.
- Wide Compatibility: Targets multiple iOS versions, particularly those no longer supported by regular updates.
The Transition from Government to Cybercrime
How Did the Leak Happen?
The exact means by which the Coruna exploit transitioned from government hands to the cybercriminal underworld remain unclear. However, several factors contribute to such leaks:
- Insider Threats: Employees or contractors with access to sensitive tools may leak or sell them.
- Cyber Espionage: Rival states or groups may steal these tools through sophisticated cyber operations.
- Market Demand: A lucrative market for exploits encourages the sale of government-developed tools.
Case Study: The Spread of Coruna
Initially detected in a government-sponsored espionage campaign, Coruna was later used by a Russian espionage group targeting Ukrainian users. It has since been adopted by financially motivated hackers in China, illustrating the exploit's widespread appeal and adaptability. This spread has been covered extensively by News.Az.
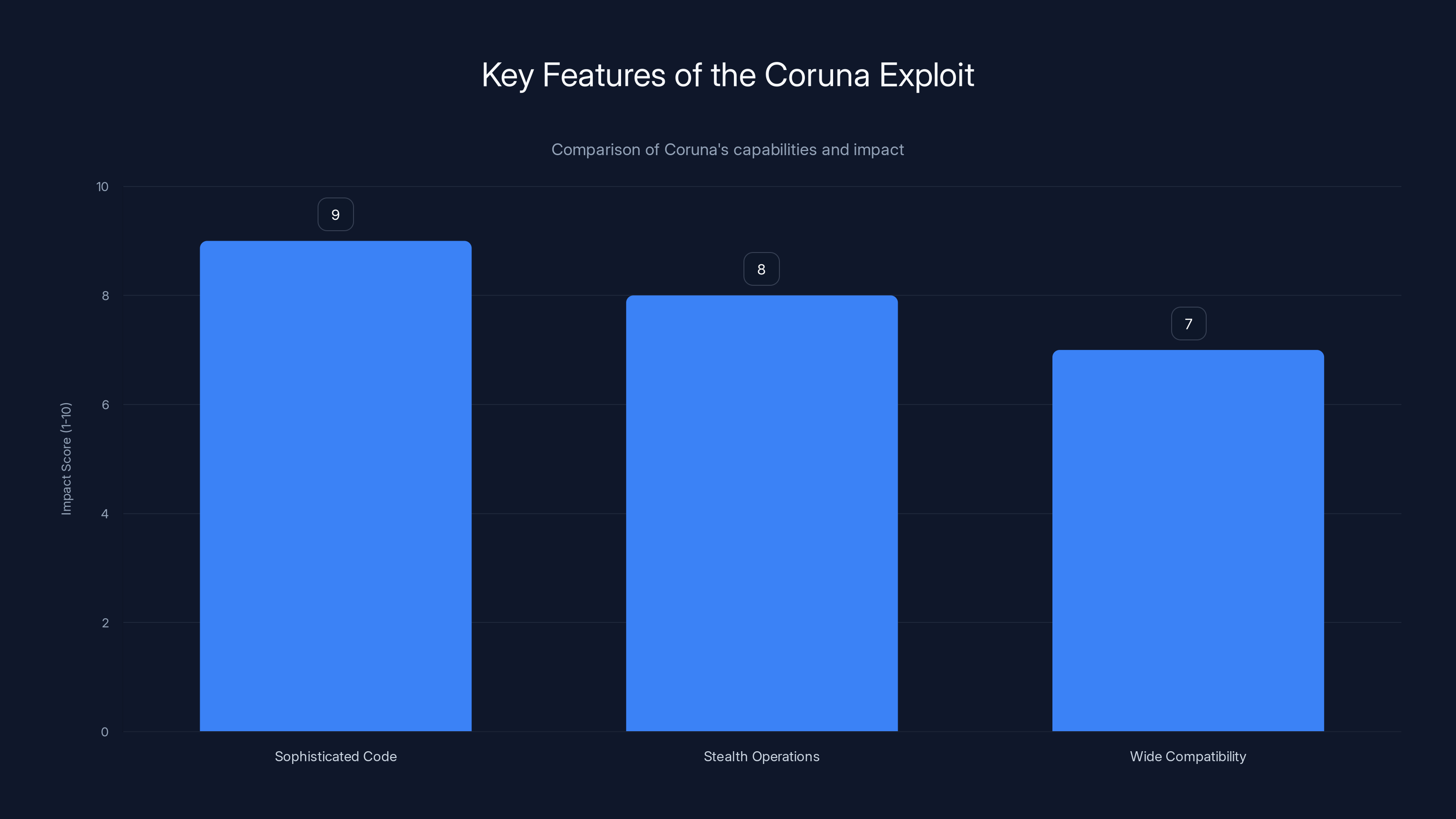
The Coruna exploit is highly effective due to its sophisticated code, stealth operations, and wide compatibility, scoring high on impact across these features. Estimated data based on typical exploit characteristics.
Implications for Cybersecurity
Increased Sophistication of Attacks
The availability of government-grade tools like Coruna increases the sophistication of cyber attacks. Criminals now have access to advanced technologies once limited to state actors, elevating the potential damage and scale of cyber incidents. Cybersecurity Ventures highlights the growing threat landscape in their reports.
Vulnerabilities in Older Systems
Many iPhones running outdated software are particularly vulnerable. Without regular updates, these devices become easy targets for exploits like Coruna. This issue highlights the importance of maintaining up-to-date security measures.
The Growing Market for Exploits
The thriving market for second-hand exploits poses a significant threat. Cybercriminals with financial motivations purchase these tools to extract more value, leading to a rise in financially motivated cybercrime. HIPAA Journal provides statistics on the impact of such breaches in the healthcare sector.

Best Practices for Protecting Against Exploits
Regular Software Updates
Keeping devices updated is the first line of defense against exploits. Manufacturers regularly release patches to address known vulnerabilities. Users should enable automatic updates to ensure their systems are protected.
# Example of enabling automatic updates on iOS
1. Open the **Settings** app.
2. Navigate to **General** > **Software Update**.
3. Tap **Automatic Updates**.
4. Toggle on **Download iOS Updates** and **Install iOS Updates**.
Use of Security Software
Installing reputable security software can provide an additional layer of protection. These tools can detect and neutralize threats before they cause harm.
User Education and Awareness
Educating users about the risks of outdated software and the importance of cybersecurity practices can greatly reduce the risk of exploitation.

Future Trends in Cybersecurity
Rise of AI in Cyber Defense
Artificial Intelligence (AI) is playing an increasingly vital role in cybersecurity. AI systems can quickly adapt to new threats, providing a dynamic defense against sophisticated exploits like Coruna.
International Cooperation
As cyber threats become more global, international cooperation is essential. Countries must work together to develop and enforce policies that prevent the misuse of government-developed tools.
Development of More Secure Systems
Manufacturers are under pressure to design more secure systems that can withstand sophisticated attacks. This includes adopting advanced encryption methods and robust security architectures.

Conclusion
The transition of government hacking tools into the hands of cybercriminals is a wake-up call for the global community. It underscores the need for robust cybersecurity measures, regular updates, and international cooperation to safeguard against increasingly sophisticated threats.
FAQ
What is Coruna?
Coruna is a sophisticated hacking tool initially developed for espionage by governments but now used by cybercriminals to exploit vulnerabilities in older iPhone software.
How do government tools end up with cybercriminals?
These tools can leak through insider threats, cyber espionage, or be sold on the black market due to high demand for exploits.
What can individuals do to protect themselves?
Regularly update software, use security software, and educate themselves about cybersecurity risks.
How is AI being used in cybersecurity?
AI is used to detect and respond to threats in real-time, providing a dynamic defense against sophisticated attacks.
Why is international cooperation important in cybersecurity?
Cyber threats are global, and international cooperation is necessary to enforce policies and prevent misuse of powerful hacking tools.
What are the future trends in cybersecurity?
The future of cybersecurity involves AI integration, international cooperation, and the development of more secure systems.
Key Takeaways
- Government-developed hacking tools like Coruna are now in the hands of cybercriminals, posing significant threats.
- Regular software updates and security software are crucial defenses against such exploits.
- The market for second-hand exploits is growing, increasing the risk of cybercrime.
- AI and international cooperation are key to future cybersecurity efforts.
- Individual awareness and education can significantly reduce the risk of exploitation.
Related Articles
- Digital Warfare: The Role of Cyber Operations in Modern Conflicts [2025]
- Navigating the Complexities of Modern Security: Fig Security's Revolutionary Approach [2025]
- How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
- A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals | WIRED
- Apple's March 2026 Unveilings: New MacBooks, iPhone 17E, and Beyond [2026]
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
![The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]](https://tryrunable.com/blog/the-rise-of-government-hacking-tools-in-cybercrime-a-deep-di/image-1-1772580842562.jpg)



