Understanding the Vercel Data Breach: Implications, Security Best Practices, and Future Directions [2025]
Last month, Vercel, a major player in the app and website hosting space, disclosed a significant security breach that exposed sensitive customer data. This incident highlights the persistent and evolving threats facing tech companies today. In this article, we’ll dive deep into the details of the Vercel data breach, explore its broader implications, and provide actionable insights on security best practices and future trends.
TL; DR
- Vercel Data Breach: Affected customer data due to a series of security lapses, including social engineering and malware as detailed by Trend Micro.
- Security Implications: Highlights the necessity for robust security protocols and employee training.
- Best Practices: Implement multi-factor authentication, regular audits, and data encryption.
- Common Pitfalls: Over-reliance on single-layer security measures can lead to vulnerabilities.
- Future Directions: Emphasize AI-driven security solutions and zero-trust architecture.
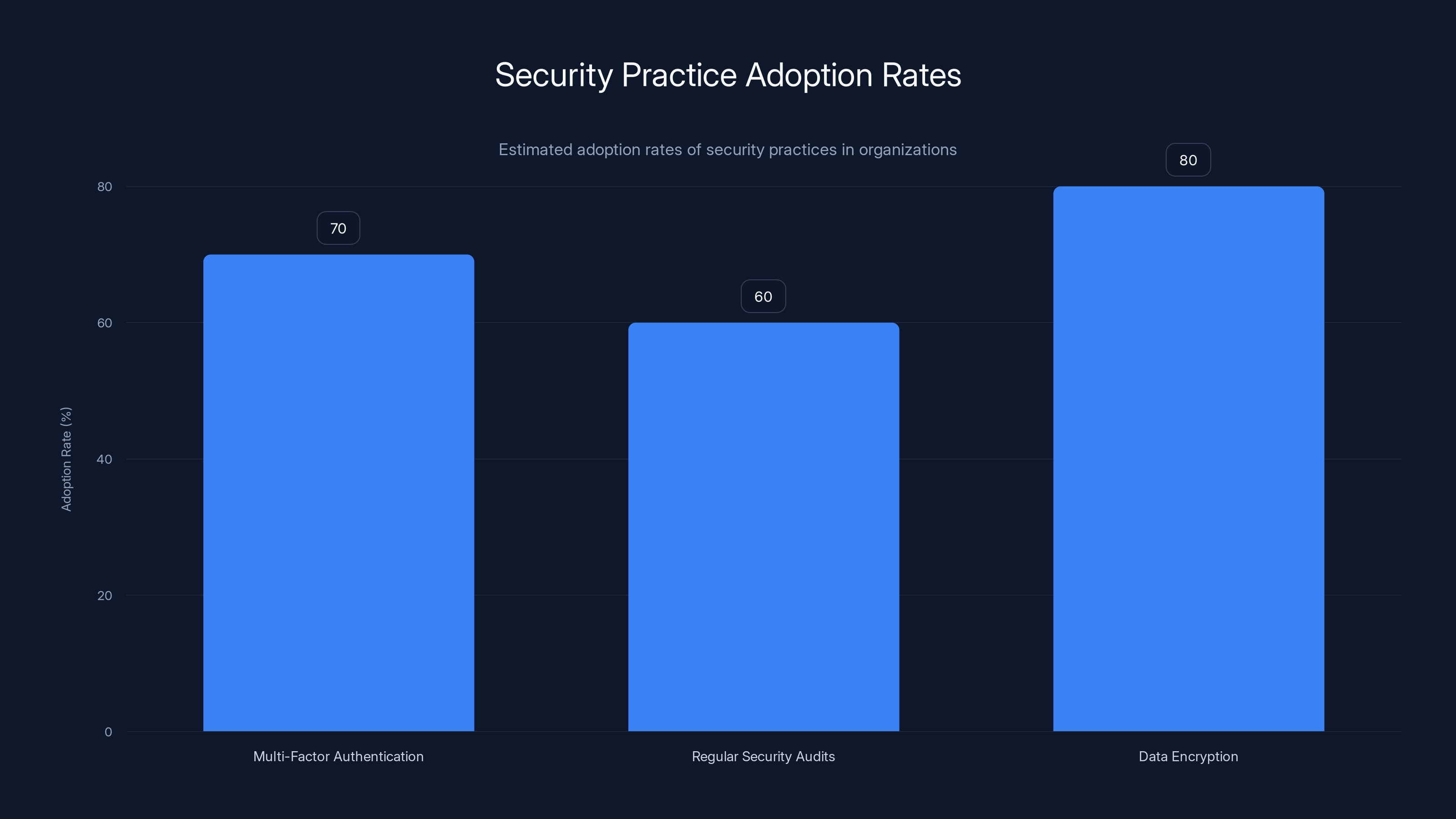
Data encryption is the most widely adopted security practice, with an estimated 80% adoption rate, followed by multi-factor authentication at 70%. (Estimated data)
The Vercel Data Breach: What Happened?
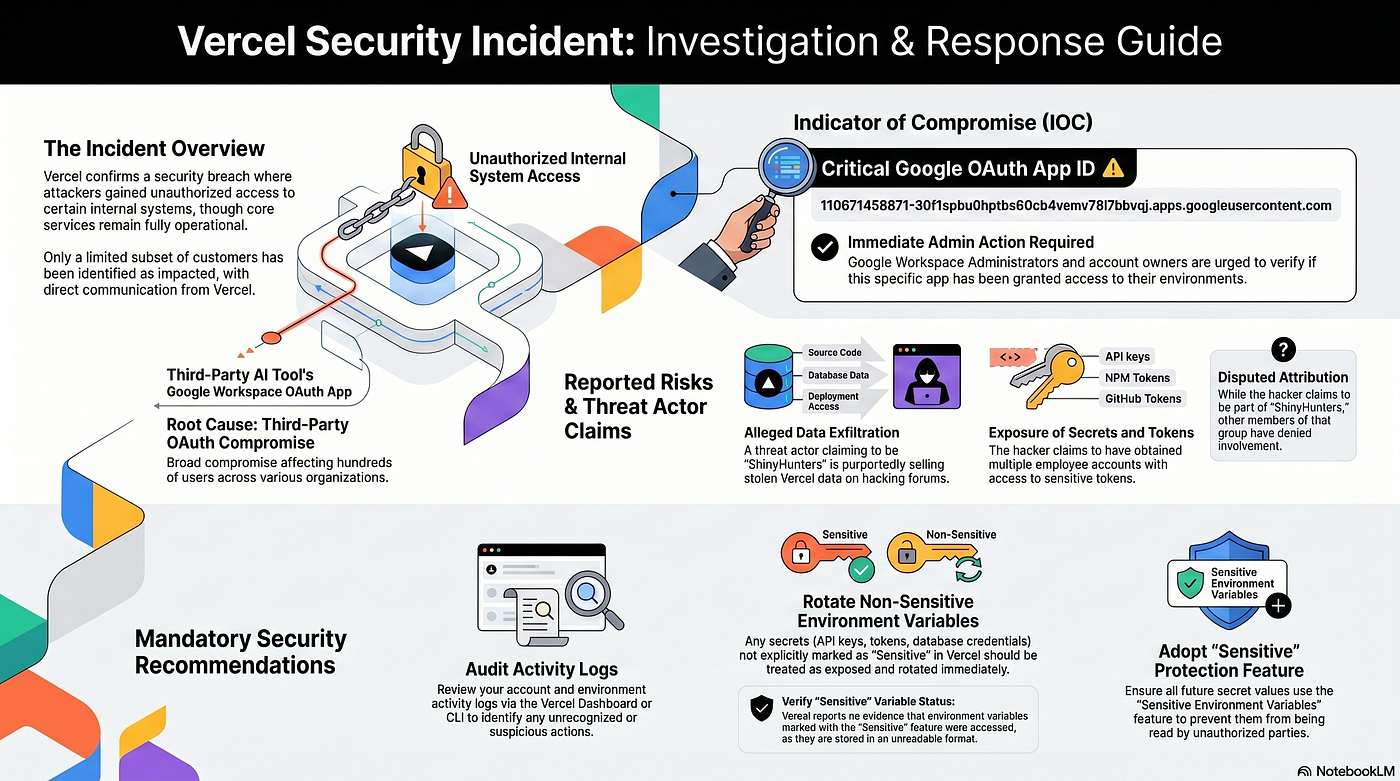
In early April 2025, Vercel publicly acknowledged a breach in its systems. Hackers accessed customer data before the company had even detected the breach. This incident underscores the vulnerabilities present even in well-regarded tech companies, as reported by Bleeping Computer.
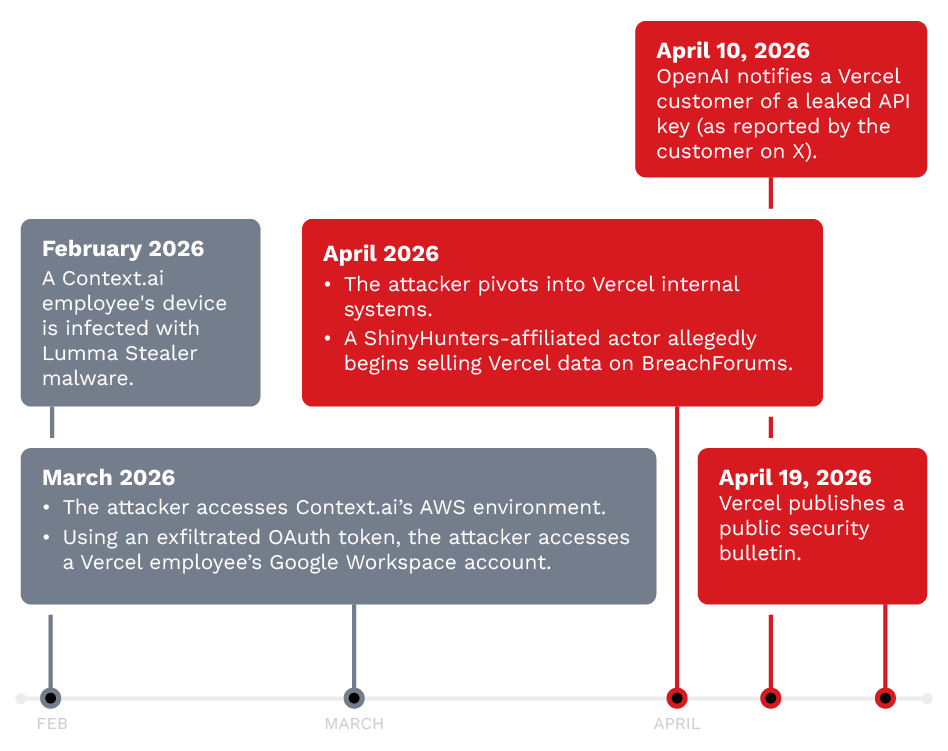
Timeline of Events
- Initial Breach: Late March, Vercel's internal systems were compromised.
- Detection: Early April, Vercel discovered the breach during routine security checks.
- Investigation: Expanded investigation revealed prior unauthorized access dating back months.
- Customer Notification: Affected customers were notified about the data exposure.
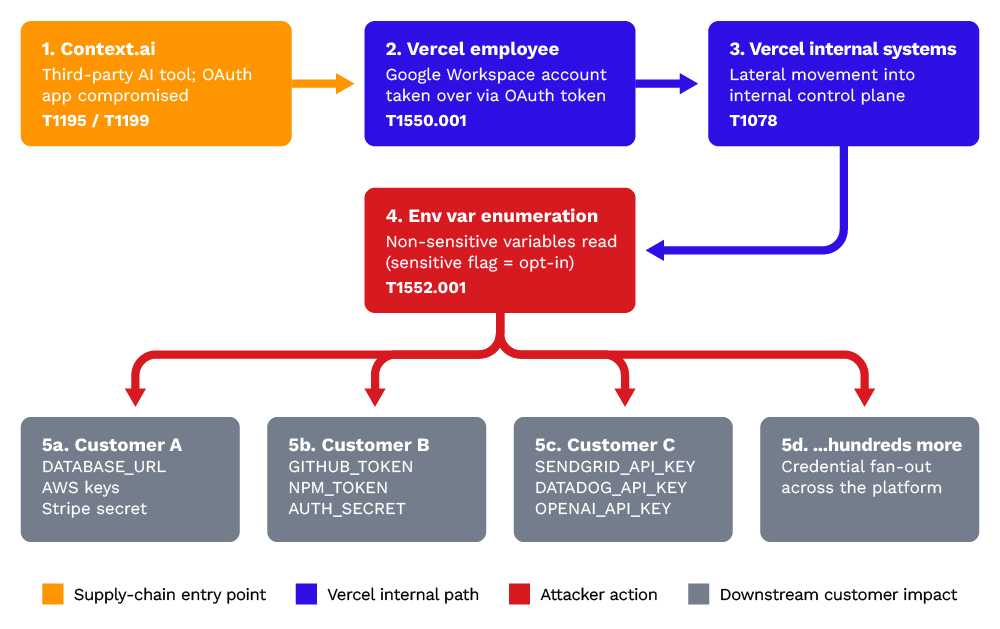
How the Breach Occurred
The breach involved several vectors, including social engineering, where attackers manipulated employees to gain sensitive information. Malware attacks were also a contributing factor, compromising systems and allowing unauthorized access, as detailed by Trend Micro.
The timeline illustrates the progression of the Vercel data breach, from initial compromise to customer notification. Estimated data based on reported events.
Implications of the Breach
This breach has far-reaching implications for Vercel and its customers, as well as for the wider tech industry.
Data Security Concerns
Customer Trust: Breaches erode trust in service providers, leading to reputational damage and potential loss of business, as noted by SecurityWeek.
Regulatory Compliance: Companies must adhere to data protection regulations like GDPR, and breaches can lead to hefty fines, as highlighted in Lexology.
Operational Disruption: Breaches can disrupt normal operations, leading to financial losses and recovery costs.
Best Practices for Enhancing Security
To mitigate the risks of similar breaches, organizations should adopt comprehensive security strategies.
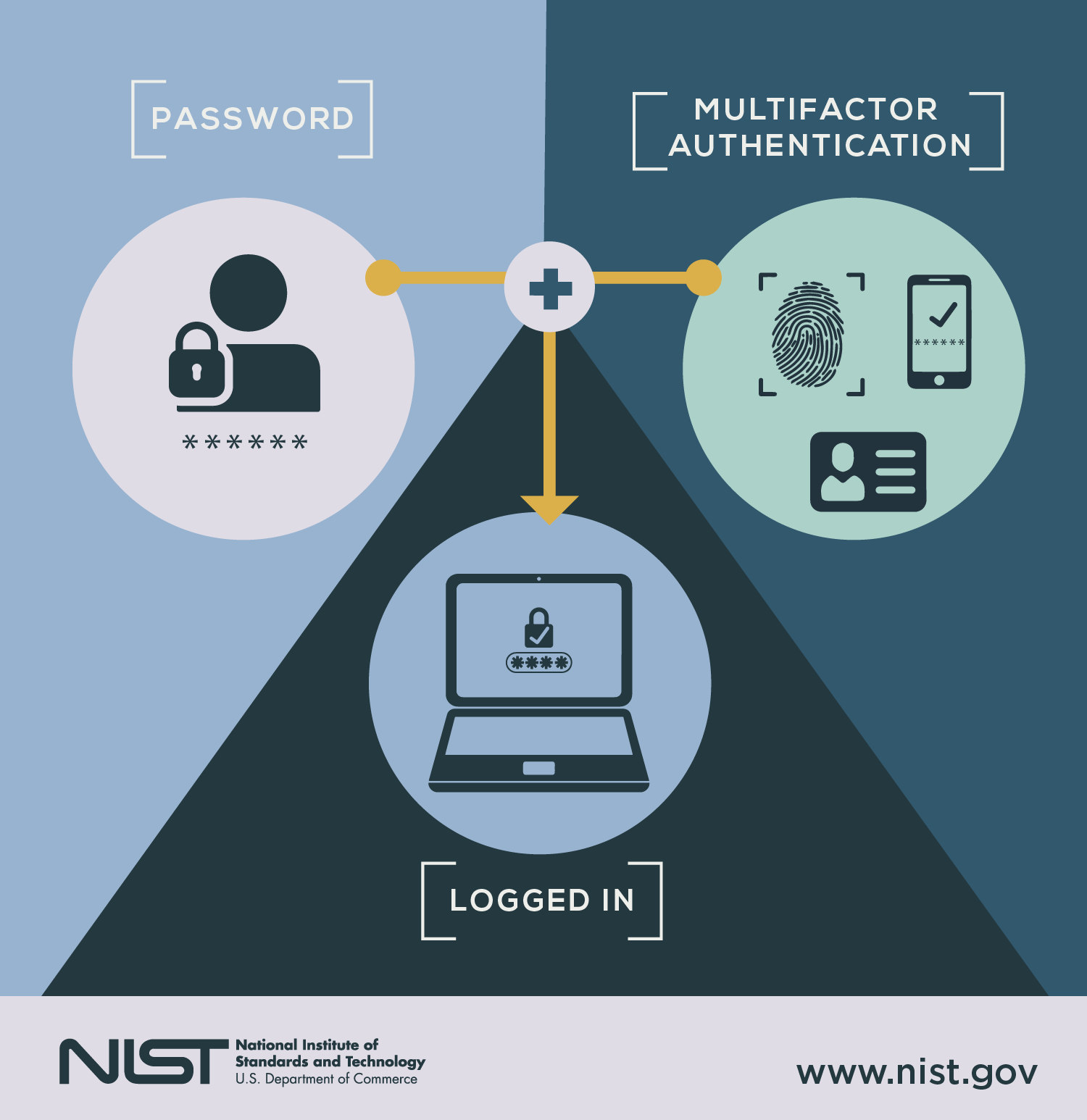
Multi-Factor Authentication (MFA)
Implementing MFA adds an extra layer of security, making it harder for attackers to gain unauthorized access.
- Implementation: Use a combination of passwords, biometrics, and one-time codes.
- Example: Google Authenticator or Duo Security for generating time-based codes.
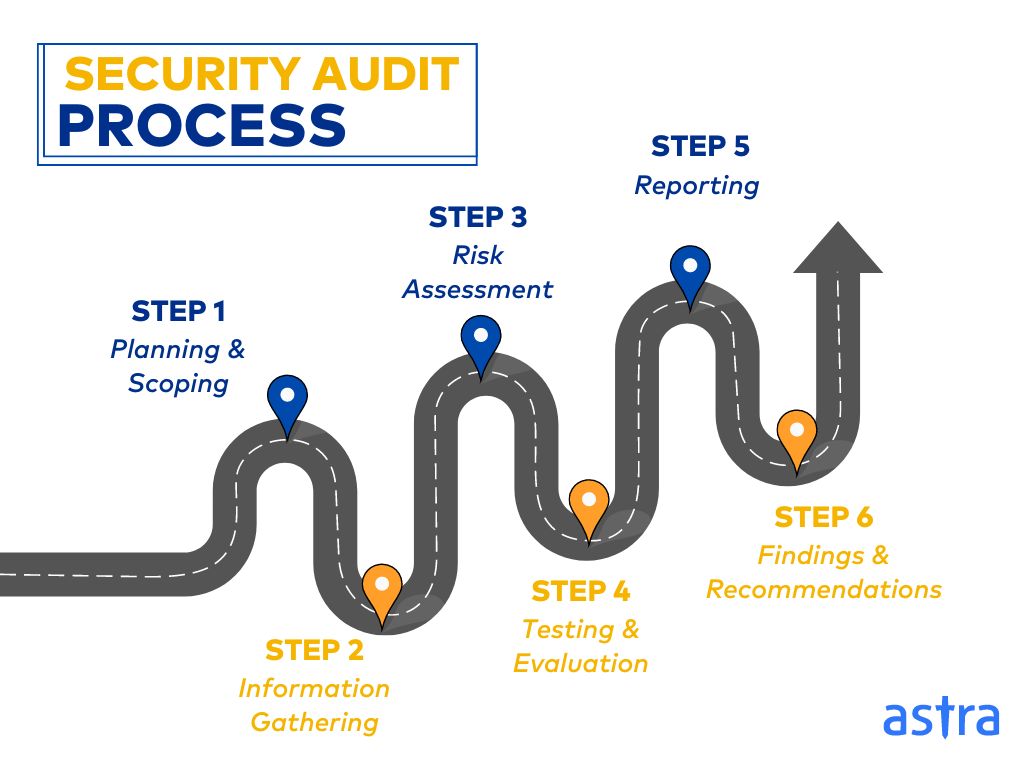
Regular Security Audits
Conducting regular audits helps identify and address potential vulnerabilities before they can be exploited.
- Frequency: Quarterly or bi-annual audits are recommended.
- Tools: Use automated vulnerability scanners like Nessus or Qualys.
Data Encryption
Encrypting data at rest and in transit ensures that even if data is intercepted, it remains unreadable without the decryption key.
- Methods: Use AES-256 encryption for data at rest; TLS for data in transit.
- Implementation: Ensure encryption keys are stored securely and access is limited.
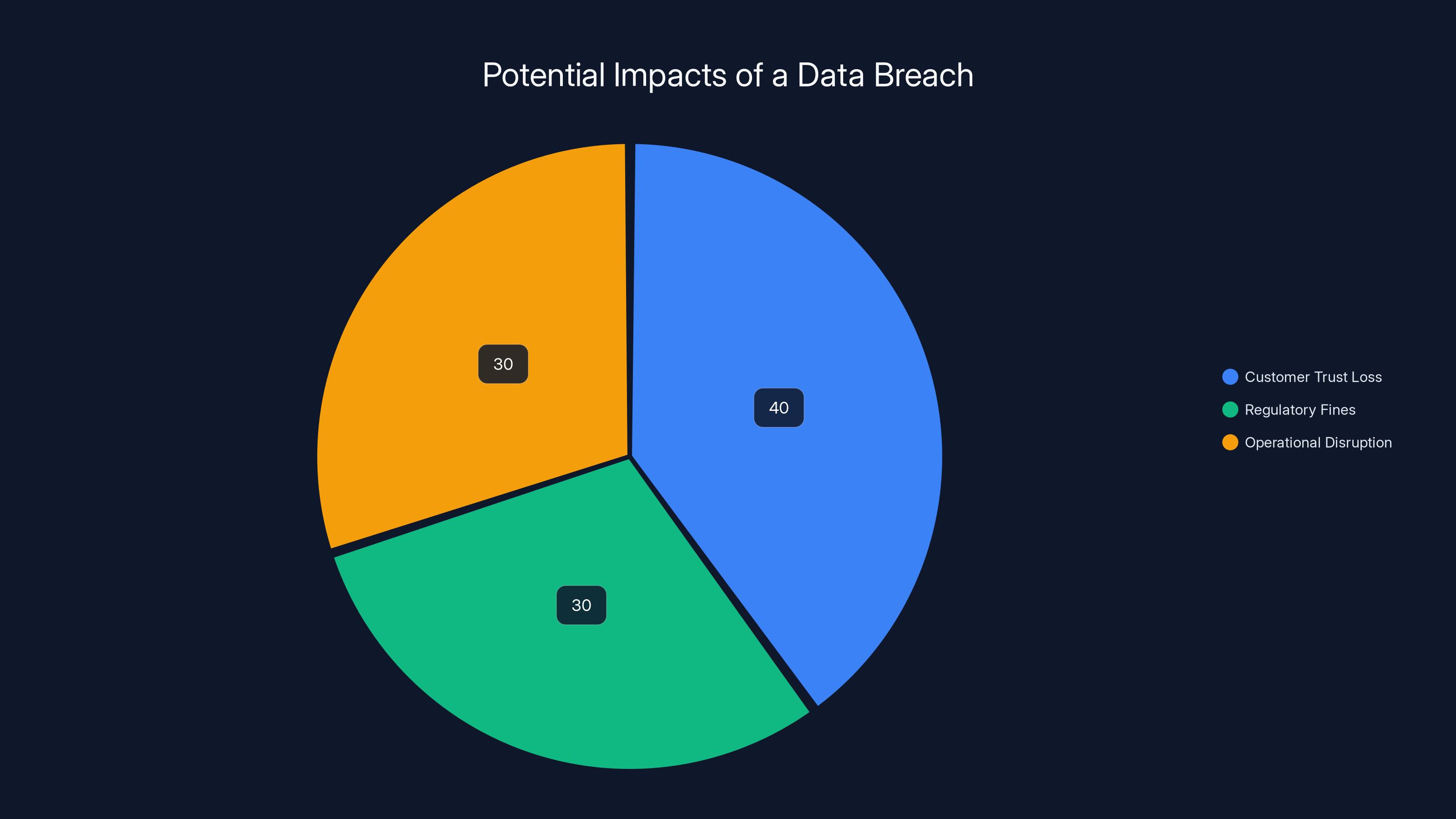
Estimated data shows that customer trust loss, regulatory fines, and operational disruption each significantly impact a company after a data breach.
Common Pitfalls in Data Security
Even with best practices, certain pitfalls can compromise security efforts.
Over-Reliance on Single-Layer Security
Relying solely on firewalls or antivirus software can create a false sense of security. A multi-layered approach is essential.
- Solution: Combine network security with endpoint protection and user education.
Inadequate Employee Training
Employees are often the weakest link in security. Without proper training, they may fall prey to phishing attacks or social engineering.
- Solution: Regular security training sessions and simulated phishing exercises.
Lack of Incident Response Plan
Without a clear incident response plan, companies may struggle to contain breaches and mitigate damage.
- Solution: Develop and regularly update a comprehensive incident response plan.

Future Trends in Cybersecurity
As threats evolve, so too must our approach to cybersecurity. Here are some trends to watch.
AI-Driven Security Solutions
AI can analyze vast amounts of data to detect anomalies and predict potential threats.
- Applications: Use AI for real-time threat detection and automated response.
- Example: Darktrace uses AI to identify and respond to cyber threats in real-time.
Zero-Trust Architecture
A zero-trust model assumes that threats could exist both inside and outside the network, requiring verification for every access request.
- Principles: Never trust, always verify. Limit access based on least privilege.
- Implementation: Segregate networks and use micro-segmentation for added security.
Cloud Security Posture Management (CSPM)
With the shift to cloud services, managing security postures in the cloud is critical.
- Tools: Solutions like Prisma Cloud or AWS Security Hub help ensure cloud environments are secure.

Recommendations for Organizations
To protect against breaches like the one experienced by Vercel, organizations should adopt a proactive approach to security.
Comprehensive Security Strategy
Develop a holistic security strategy that includes prevention, detection, and response measures.
- Components: Combine technical solutions with policy enforcement and user education.
Continuous Monitoring
Implement continuous monitoring to detect and respond to threats in real-time.
- Tools: SIEM solutions like Splunk or Sentinel One provide comprehensive monitoring and alerting.
Vendor Management
Evaluate and manage third-party vendors to ensure they adhere to security best practices.
- Assessment: Conduct regular audits and require compliance with security standards.
Conclusion
The Vercel data breach serves as a stark reminder of the ever-present threats in the digital landscape. By understanding the implications of such breaches and adopting best practices, organizations can better protect themselves and their customers. As technology evolves, so too must our approach to security—remaining vigilant and proactive in the face of new challenges.
FAQ
What is a data breach?
A data breach is an incident where unauthorized individuals gain access to confidential or sensitive information, often resulting in data exposure or theft, as explained by Consumer Affairs.
How does multi-factor authentication enhance security?
Multi-factor authentication adds an additional layer of security by requiring multiple forms of verification before granting access, making it harder for attackers to breach systems.
What are the benefits of implementing a zero-trust architecture?
Zero-trust architecture improves security by assuming that threats could come from anywhere, requiring verification for every access request and limiting privileges.
How can AI improve cybersecurity?
AI can analyze large volumes of data to detect anomalies and predict potential threats, enabling more effective and timely responses to security incidents, as noted by Palo Alto Networks.
What should a comprehensive incident response plan include?
An incident response plan should include clearly defined roles and responsibilities, communication protocols, and procedures for containing and mitigating security incidents.
Why is regular employee training important in cybersecurity?
Regular training helps employees recognize and respond to potential threats like phishing attacks, reducing the risk of human error leading to security breaches.
How does data encryption protect sensitive information?
Data encryption transforms information into unreadable text without the correct decryption key, ensuring that even if data is intercepted, it remains secure.
What role do security audits play in protecting against breaches?
Security audits help identify vulnerabilities and ensure that security measures are adequate and up-to-date, reducing the risk of breaches.
Key Takeaways
- Vercel's data breach underscores the need for robust security protocols and continuous monitoring.
- Multi-factor authentication is crucial for protecting against unauthorized access.
- AI-driven security solutions offer real-time threat detection and response capabilities.
- Zero-trust architecture enhances security by requiring verification for every access request.
- Comprehensive security strategies must include prevention, detection, and response measures.
Related Articles
- France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]
- The Hidden Risks of AI-Generated Passwords [2025]
- Understanding the Rising Threat of Hacktivist Attacks in the UK [2025]
- Understanding the FCC Router Ban: What's Running in Your Network? [2025]
- Why Passkeys Are the Future of Authentication [2025]
- The Silent Legacy of FTP Servers: Still Running and Still Vital [2025]
![Understanding the Vercel Data Breach: Implications, Security Best Practices, and Future Directions [2025]](https://tryrunable.com/blog/understanding-the-vercel-data-breach-implications-security-b/image-1-1776956842881.jpg)



