Navigating Encryption Challenges: VeraCrypt's Developer Faces Microsoft Account Lock [2025]
When it comes to data encryption, VeraCrypt has long been a trusted name among Windows users. However, the developer's ability to sign Windows drivers and bootloaders was suddenly revoked, creating a challenging situation for Mounir Idrassi, the developer behind VeraCrypt, when Microsoft locked his account. This unexpected turn of events could potentially impact thousands of users who rely on VeraCrypt for securing their data.
TL; DR
- Key Point 1: Microsoft locked VeraCrypt developer's account, impacting Windows boot processes.
- Key Point 2: VeraCrypt users may face boot-up issues if the account isn't reinstated.
- Key Point 3: Understanding encryption risks and mitigation strategies is crucial.
- Key Point 4: Proactive measures can safeguard encrypted data against disruptions.
- Bottom Line: Prepare for potential encryption software disruptions and explore alternative solutions.
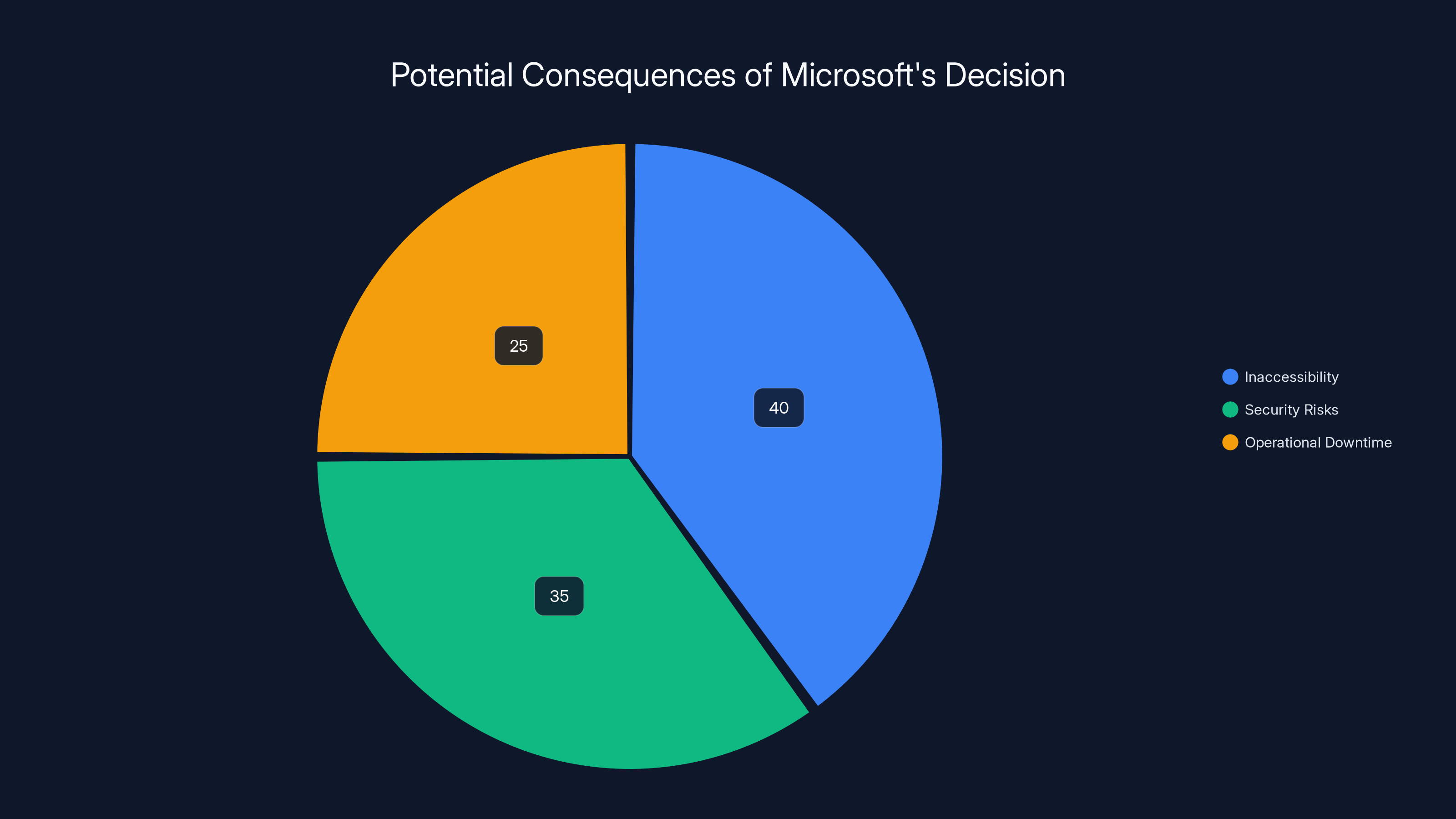
Estimated data shows inaccessibility as the most significant consequence, affecting 40% of users, followed by security risks and operational downtime.
The Role of VeraCrypt in Data Encryption
VeraCrypt is an open-source disk encryption software based on TrueCrypt. It provides enhanced security to the algorithms used for system and partitions encryption, making it immune to new developments in brute-force attacks.
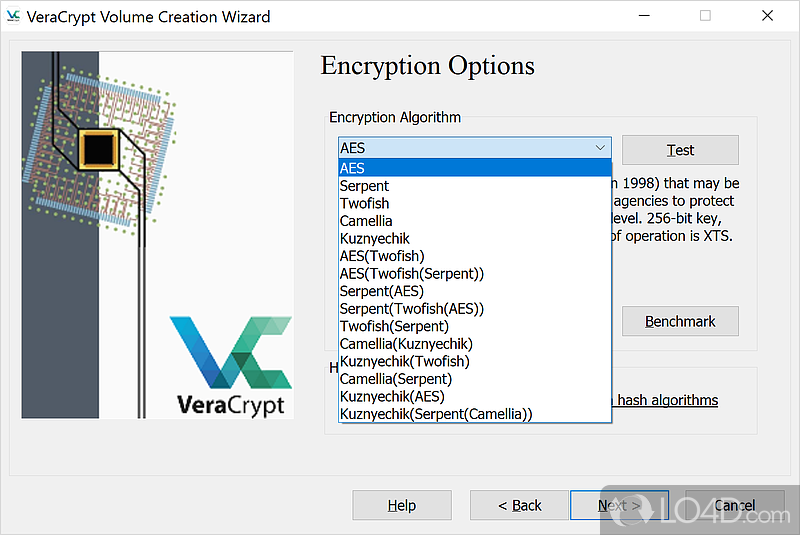
Core Features of VeraCrypt:
- Enhanced Security: Offers higher encryption security levels.
- Multiple Encryption Protocols: Supports AES, Serpent, and TwoFish.
- Hidden Volumes: Allows the creation of a hidden volume within another volume.
- Cross-Platform Support: Available on Windows, macOS, and Linux.
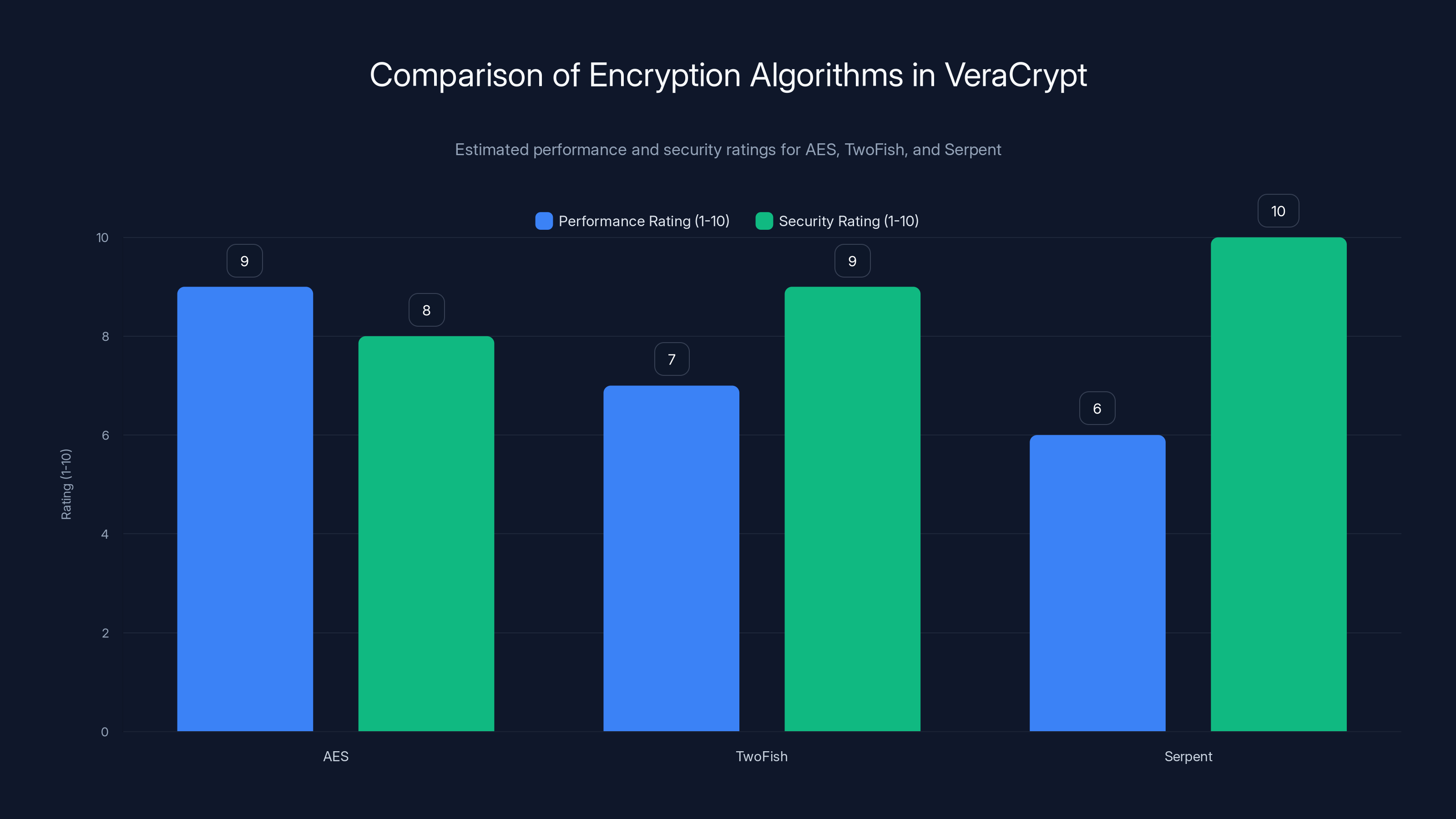
AES offers the best performance, while Serpent provides the highest security. Estimated data based on typical algorithm characteristics.
Understanding the Impact of Microsoft's Decision
The recent decision by Microsoft to lock Mounir Idrassi's account, which he used to sign Windows drivers, poses significant challenges for VeraCrypt users. Without the ability to update these drivers, users may encounter boot-up issues if their systems rely on them.
What This Means for Users
For those who have encrypted their systems with VeraCrypt, the inability to boot their computers can lead to significant downtime and potential data loss. This underscores the importance of understanding the risks associated with encryption software and how to mitigate them.
Potential Consequences:
- Inaccessibility: Users may not be able to access their data.
- Security Risks: Stalled security updates could expose systems to vulnerabilities.
- Operational Downtime: Businesses relying on VeraCrypt may face operational disruptions.

Best Practices for Managing Encrypted Systems
To ensure continued access to encrypted data, users can follow several best practices:
- Back Up Data Regularly: Regular backups ensure data can be restored if access is lost.
- Keep Software Updated: Ensure that all encryption software is up-to-date to avoid compatibility issues.
- Use Trusted Sources: Only download updates and software from official, trusted sources.
- Monitor System Updates: Be aware of any system updates that could affect encryption software.
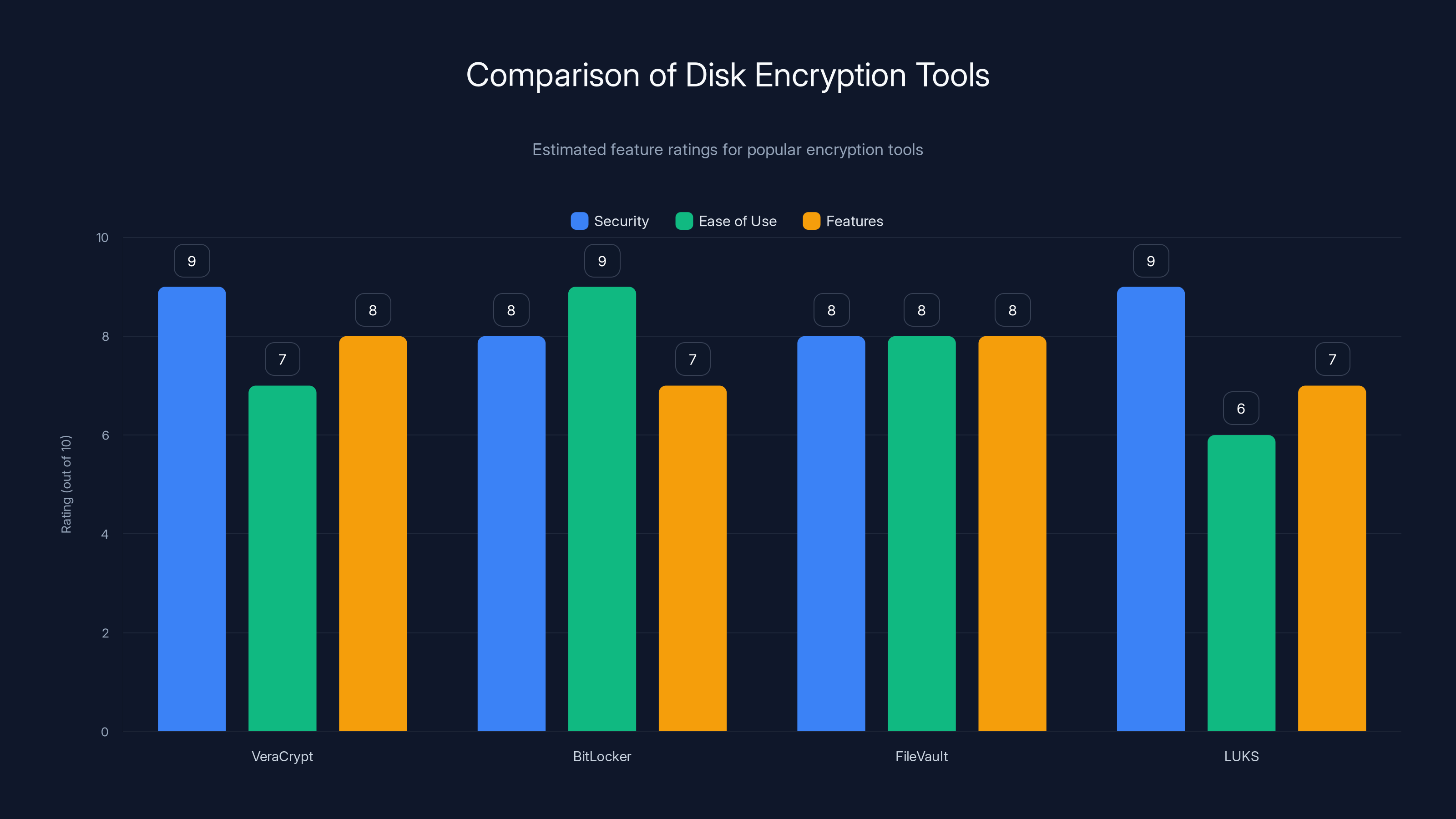
VeraCrypt and LUKS are estimated to offer the highest security, while BitLocker is noted for ease of use. Estimated data.
Common Pitfalls and How to Avoid Them
Encryption software like VeraCrypt offers robust security, but users can still encounter pitfalls. Here are common issues and how to avoid them:
- Improper Installation: Ensure the software is installed correctly to avoid configuration errors.
- Neglecting Updates: Always update to the latest version to patch vulnerabilities.
- Forgetting Passwords: Use a password manager to store complex passwords securely.

Technical Insights: Encryption Mechanics
Understanding the mechanics behind encryption can help users appreciate the importance of maintaining their software:
How VeraCrypt Works
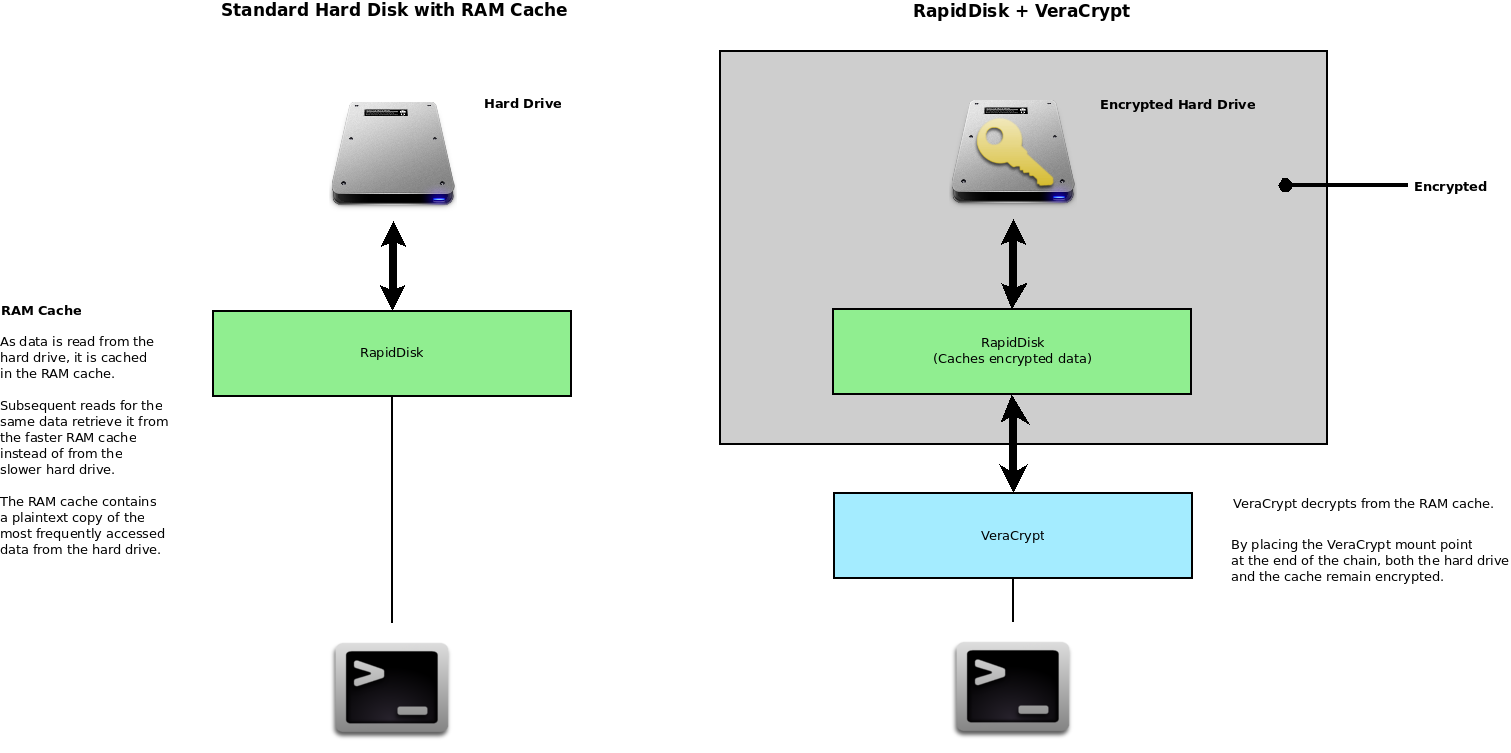
VeraCrypt encrypts entire partitions or storage devices, offering real-time encryption and decryption. It operates on-the-fly, meaning files are automatically encrypted right before they are saved and decrypted immediately after they are loaded.
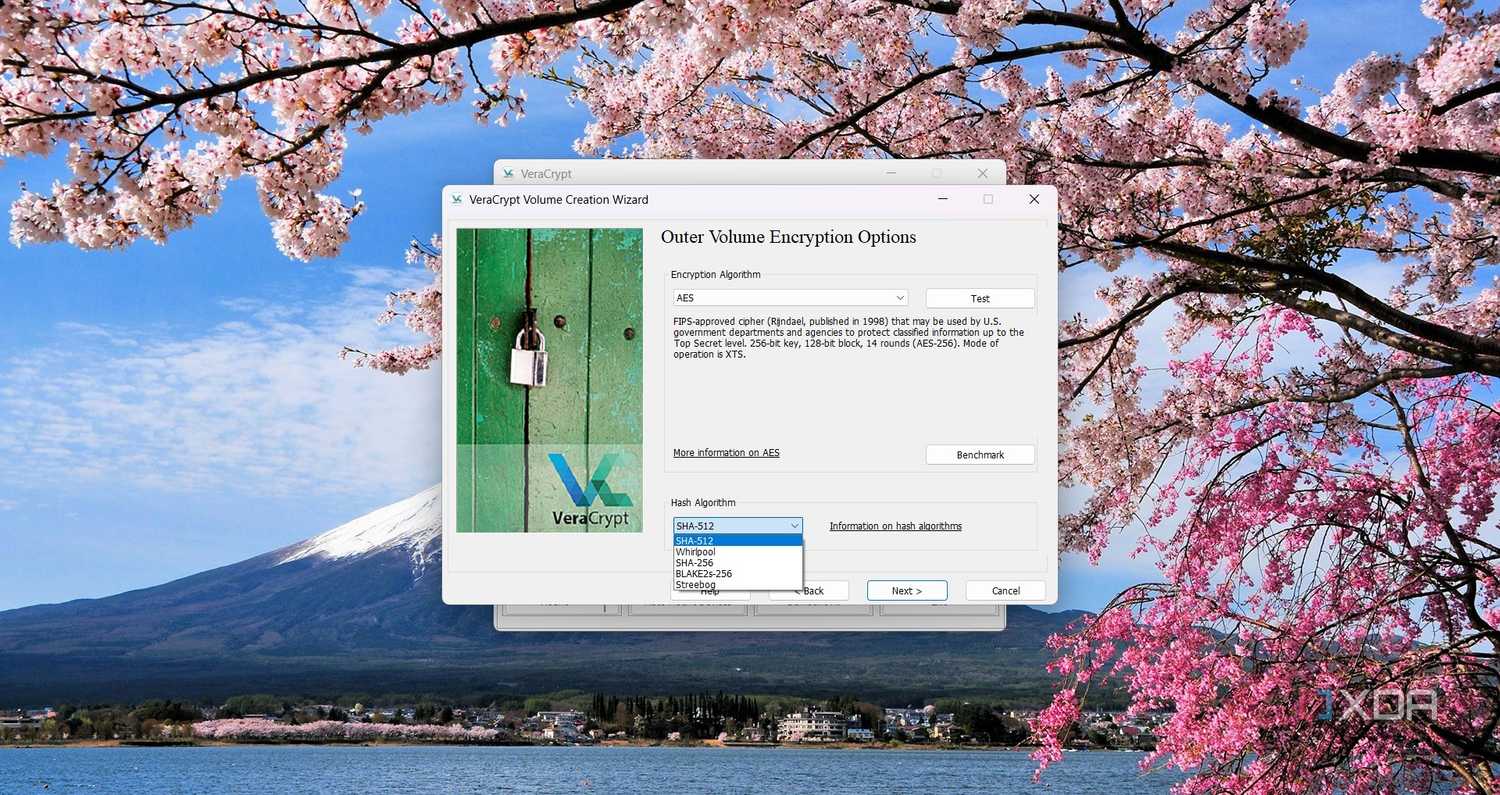
Encryption Algorithms:
- AES (Advanced Encryption Standard): Known for its speed and security.
- TwoFish: Offers a high level of security with variable-length keys.
- Serpent: Prioritizes security over speed, making it a reliable choice.
Implementation Guide
- Install VeraCrypt: Download and install the latest version from the official website.
- Create a Volume: Use VeraCrypt's wizard to create an encrypted volume.
- Select Encryption Algorithm: Choose from AES, Serpent, or TwoFish.
- Set a Strong Password: Ensure your password is complex and stored securely.
- Mount the Volume: Use VeraCrypt to mount and access your encrypted volume.

Future Trends in Encryption
As technology evolves, so do encryption methods and trends. Here are some future trends to watch:
- Quantum-Resistant Encryption: As quantum computing advances, new encryption methods are being developed to resist potential threats.
- AI-Enhanced Encryption: Artificial intelligence may enhance encryption by predicting and mitigating potential vulnerabilities.
- Decentralized Encryption Solutions: Blockchain technology could offer new ways to secure data in a decentralized manner.

Proactive Measures Against Account Locks
While the situation with VeraCrypt highlights the risks of relying on a single developer account for software updates, users can take proactive measures:
- Use Multiple Accounts: Developers should use multiple accounts to avoid single points of failure.
- Implement Account Recovery Options: Ensure account recovery options are in place to quickly restore access.
- Engage with Community Support: Leverage community forums and support for insights and solutions.

Conclusion
The locking of Mounir Idrassi's account by Microsoft serves as a reminder of the vulnerabilities inherent in digital security. By understanding encryption mechanics, adopting best practices, and staying informed on future trends, users can safeguard their data against potential disruptions.
Use Case: Automate your encryption updates and data backups with AI-powered solutions like Runable to ensure seamless security management.
Try Runable For Free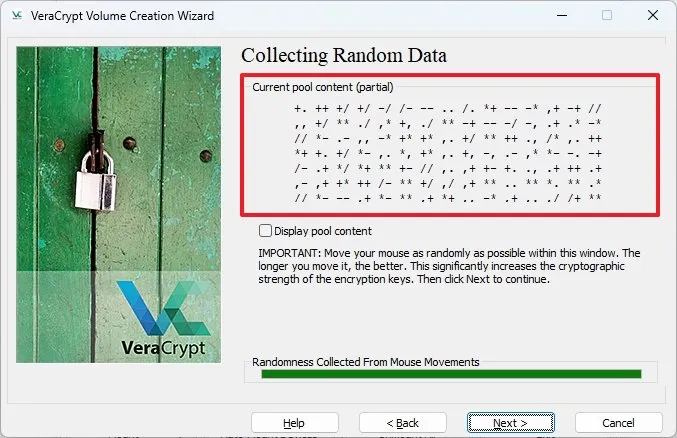
FAQ
What is VeraCrypt?
VeraCrypt is a free, open-source disk encryption software that enhances security for system and partitions encryption, making it resistant to brute-force attacks.
How does VeraCrypt work?
VeraCrypt encrypts data on-the-fly, meaning files are automatically encrypted before being saved and decrypted after being loaded, using algorithms like AES, Serpent, and TwoFish.
What are the benefits of using VeraCrypt?
Benefits include robust data protection, support for multiple encryption protocols, and the ability to create hidden volumes, enhancing privacy and security.
How can I safeguard my data if VeraCrypt is unavailable?
Regularly back up data, monitor updates, and consider alternative encryption tools or services that align with your security needs.
Why did Microsoft lock the developer's account?
Microsoft has not provided a specific reason for locking Mounir Idrassi's account, which he used to sign Windows drivers and updates.
What should I do if I encounter boot-up issues with VeraCrypt?
Check for updates on the VeraCrypt website, explore alternative boot options, and seek assistance from online communities or forums.
How can I stay updated on encryption trends?
Follow industry news, join encryption forums, and explore resources like Runable for insights into AI-driven security solutions.
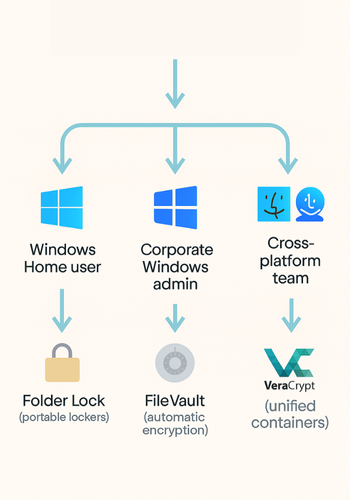
What are some alternatives to VeraCrypt?
Consider alternatives such as BitLocker for Windows, FileVault for macOS, and LUKS for Linux, each offering distinct features and security levels.
How does encryption protect data?
Encryption scrambles data, making it unreadable to unauthorized users, thus protecting sensitive information from theft or unauthorized access.
Key Takeaways
- Microsoft's account lock on VeraCrypt developer could disrupt users' access to encrypted data.
- Understanding encryption mechanics is crucial for maintaining data security.
- Proactive measures can mitigate risks associated with encryption software disruptions.
- Quantum-resistant encryption and AI-enhanced security are emerging trends.
- Regular data backups and using trusted sources are best practices for encryption management.
Related Articles
- The Exciting Start of 2026 for NordVPN: A Comprehensive Overview [2026]
- Unraveling Microsoft's Gradual Transition from the Control Panel to Settings [2025]
- Elon Musk's OpenAI Legal Battle: Aiming for Nonprofit Restoration [2025]
- Stolen Session Cookies: The Hidden Threat to Account Security [2025]
- Microsoft and Yobi: A New Era in AI-Driven Consumer Insight [2025]
- Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]
![Navigating Encryption Challenges: VeraCrypt's Developer Faces Microsoft Account Lock [2025]](https://tryrunable.com/blog/navigating-encryption-challenges-veracrypt-s-developer-faces/image-1-1775662462983.jpg)



