Introduction
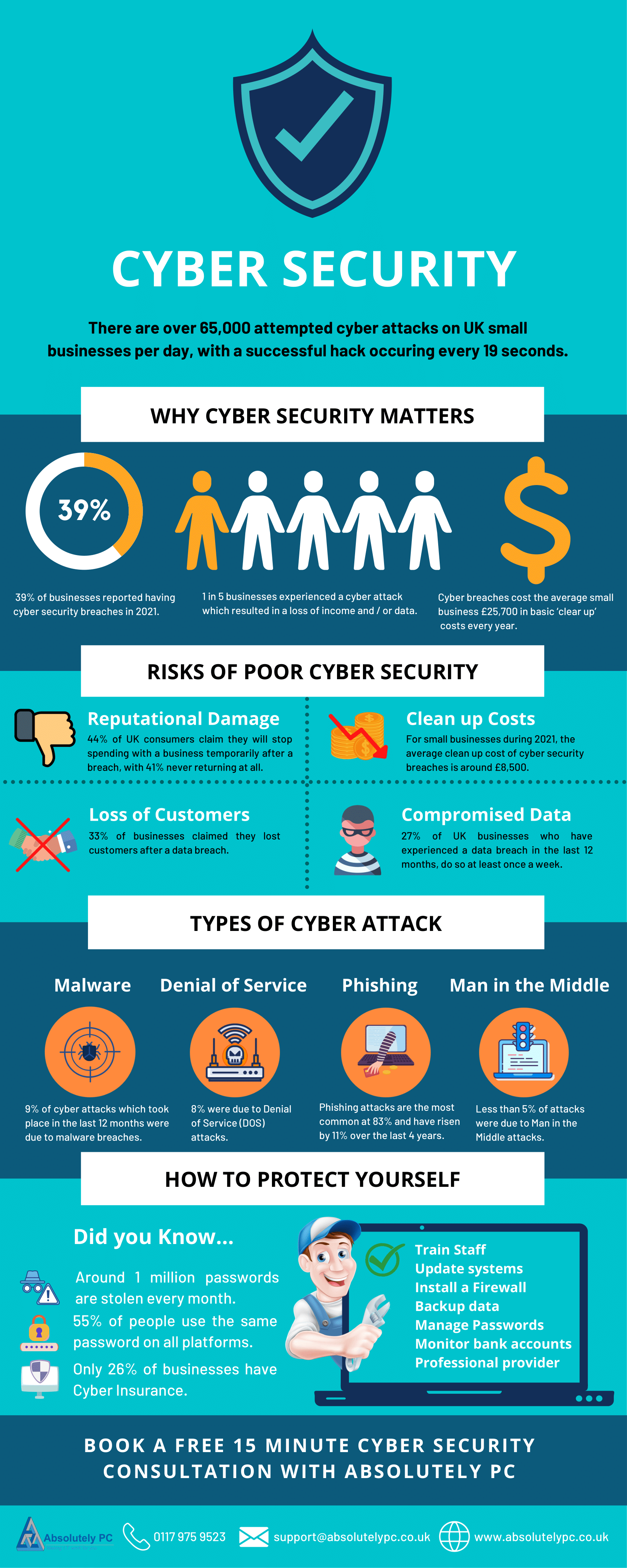
Last year, a mid-sized tech firm unwittingly opened the door to a massive data breach through a trusted vendor. The vendor had assured them of top-notch security with glowing promises, but the reality painted a different picture. This incident is not isolated; it's a growing trend. As cyber threats become more sophisticated, the doctrine of 'proof over promises' is emerging as a necessary shift in cybersecurity, as highlighted by the University of West Florida's Center for Cybersecurity and AI.
TL; DR
- Proof over promises: Shift from verbal assurances to evidence-based security measures.
- 51% of UK organizations: Reported breaches linked to third-party vendors in the past year, according to HIPAA Journal.
- Common vulnerabilities: Include outdated software and misconfigured access controls.
- Future trends: Emphasize continuous monitoring and real-time threat detection.
- Recommendation: Implement regular third-party security audits.

Continuous monitoring is rated as the most important strategy for implementing evidence-based security, closely followed by regular security audits. (Estimated data)
The Fallacy of Trust-Based Compliance
For years, cybersecurity relied heavily on trust-based compliance. Companies signed contracts, and vendors promised security standards without tangible proof. This model, while convenient, has shown cracks, especially when breaches often come from trusted third parties. In fact, 51% of UK organizations have reported breaches due to third-party vendors, highlighting a critical vulnerability, as noted in HIPAA Journal.
The Need for Evidence-Based Security
In an era where data breaches can cost millions and damage reputations, relying on promises is no longer viable. The shift towards evidence-based security involves demanding tangible proof of a vendor's security posture before engagement. This can include independent security audits, penetration testing results, and compliance certifications, as recommended by CIO's guide on compliance certifications.

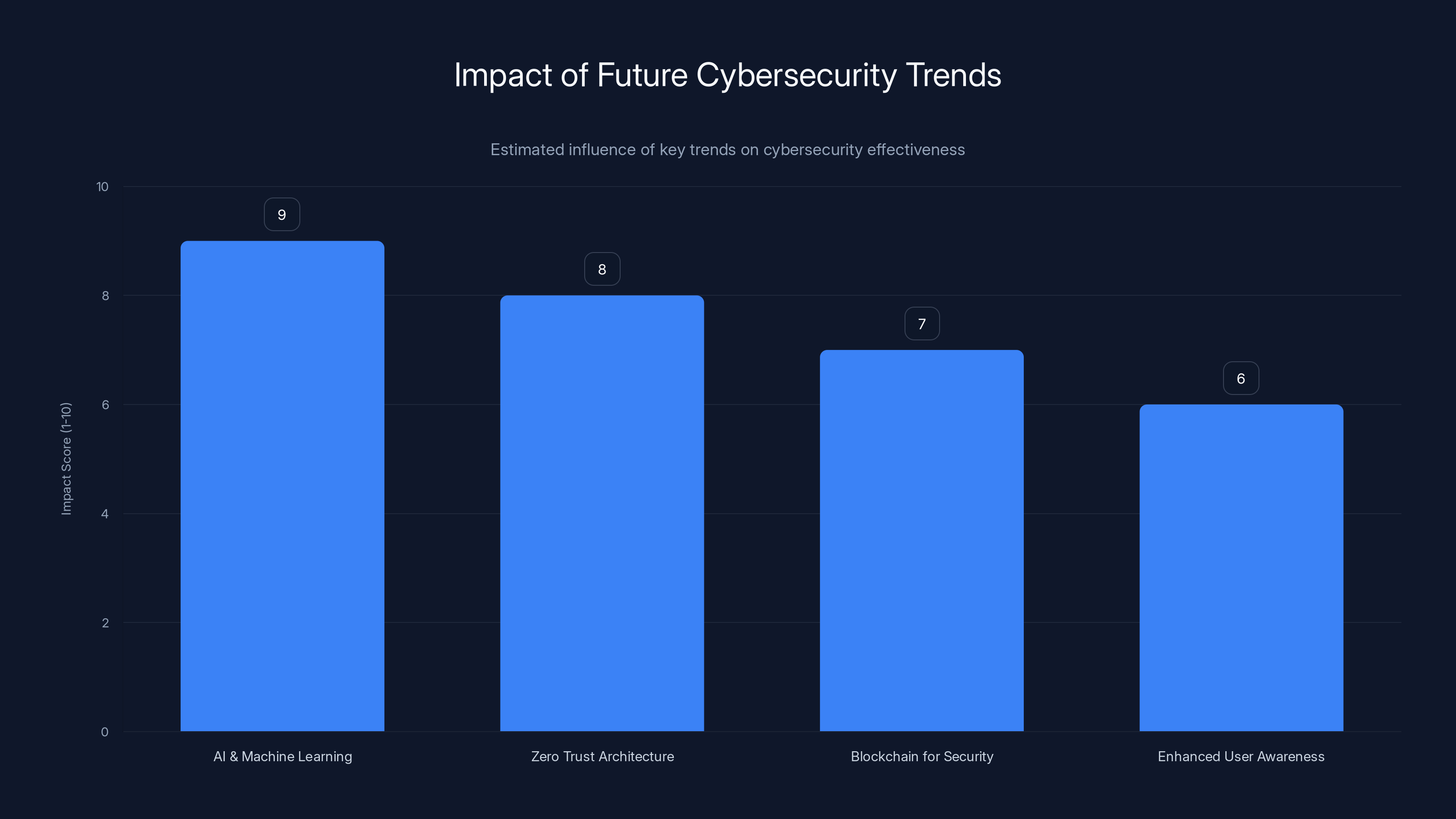
AI and Machine Learning are projected to have the highest impact on future cybersecurity, followed by Zero Trust Architecture. (Estimated data)
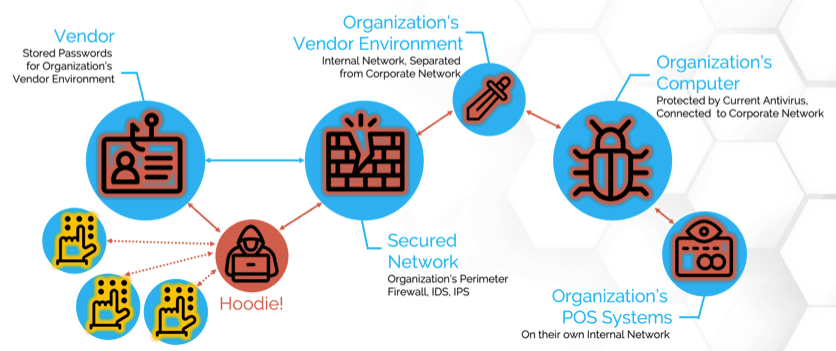
Understanding Common Cyber Threats
To appreciate why proof is essential, it's crucial to understand the common cyber threats faced today. These include:
- Phishing Attacks: Deceptive emails designed to steal credentials, as detailed in Simplilearn's cybersecurity tutorial.
- Ransomware: Malicious software that encrypts data until a ransom is paid, explained by ESET's blog on ransomware.
- Advanced Persistent Threats (APTs): Prolonged and targeted cyber attacks.
- Supply Chain Attacks: Compromising a vendor to attack the primary target, as highlighted by Group-IB's research on supply chain attacks.
Each of these threats exploits weaknesses that could be mitigated with proper security measures.
Implementing Evidence-Based Security
Transitioning to evidence-based security requires a strategic approach. Here's how organizations can implement it:
1. Conduct Regular Security Audits
Regular audits are essential. They provide a thorough examination of a vendor's security practices and help identify potential vulnerabilities, as advised by ITPro's insights on cybersecurity.
2. Demand Transparency from Vendors
Vendors should be transparent about their security measures. Request access to audit results and penetration test findings.
3. Adopt Continuous Monitoring
Implement systems that continuously monitor network traffic for suspicious activity. This proactive approach helps detect threats in real-time, as recommended by Maryland's new cyber policy.
4. Establish Clear Security Metrics
Set clear security metrics and benchmarks for vendors to meet. These should be aligned with industry standards such as ISO 27001 or NIST.

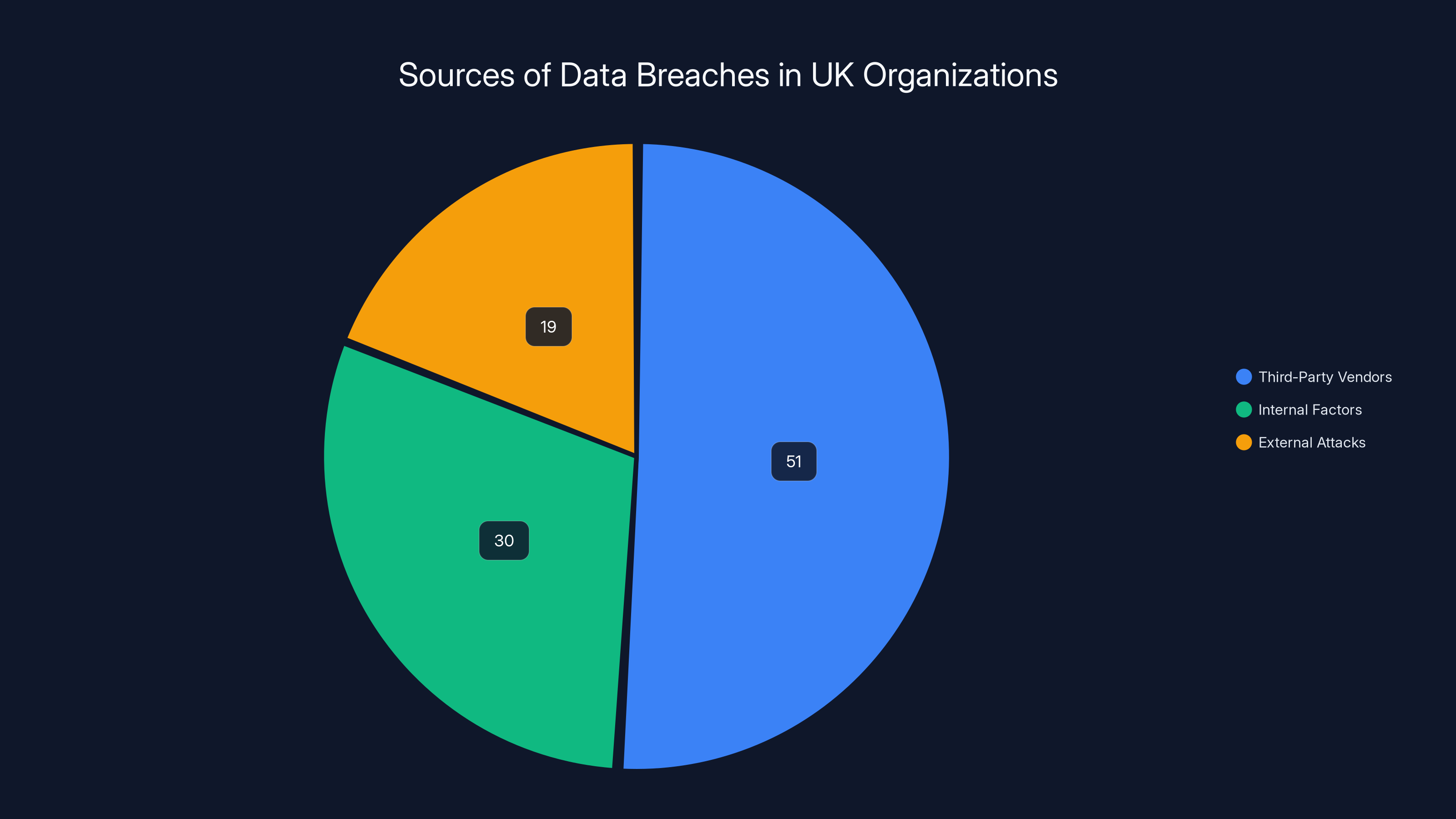
51% of UK organizations report breaches due to third-party vendors, emphasizing the need for evidence-based security. Estimated data for internal and external sources.
Common Pitfalls in Cybersecurity
Even with a solid cybersecurity strategy, pitfalls are inevitable. Here are some common ones and how to avoid them:
- Overconfidence in Technology: Relying solely on technology without regular human oversight can lead to missed threats.
- Ignoring Insider Threats: Employees can unintentionally or maliciously compromise security. Regular training can mitigate this risk, as suggested by Simplilearn's article on cybersecurity careers.
- Neglecting Software Updates: Outdated software is a common entry point for attackers. Regular updates are crucial.

Future Trends in Cybersecurity
The future of cybersecurity will be shaped by several trends:
1. AI and Machine Learning
AI and machine learning will play significant roles in threat detection and response. These technologies can analyze vast amounts of data quickly to identify patterns indicative of potential threats, as discussed in Press Gazette's report on AI in cybersecurity.
2. Zero Trust Architecture
Zero Trust is an architectural approach where no one inside or outside the network is trusted by default. This minimizes the attack surface and helps prevent unauthorized access.
3. Blockchain for Security
Blockchain technology can enhance security by providing immutable records of transactions, making it harder for attackers to alter data.
4. Enhanced User Awareness
As threats evolve, educating users about cybersecurity will remain a priority. Regular training on recognizing phishing attempts and safe internet practices will be crucial.

Recommendations for Organizations
To stay ahead in the cybersecurity game, organizations should:
- Implement Multi-Factor Authentication (MFA): This adds an additional layer of security beyond passwords.
- Conduct Regular Phishing Simulations: These help assess and improve employee readiness against phishing attacks.
- Partner with Reputable Cybersecurity Firms: These firms can provide expertise and tools that might be lacking internally.
Implementing a Cybersecurity Framework
Adopting a cybersecurity framework can guide organizations in securing their operations. The NIST Cybersecurity Framework is one such example, providing guidelines across five core functions: Identify, Protect, Detect, Respond, and Recover.
Steps to Implement
- Identify: Understand your assets and potential risks.
- Protect: Develop safeguards to ensure delivery of critical services.
- Detect: Implement the tools needed to identify security events.
- Respond: Have a plan to contain and mitigate the impact of security incidents.
- Recover: Develop the capacity to restore any capabilities or services that were impaired.
Conclusion
As cyber threats continue to evolve, the shift from promises to proof is not just a trend but a necessity. By adopting evidence-based security measures, organizations can protect themselves more effectively, ensuring that their systems and data remain secure against ever-evolving threats. It's time to demand more than just promises from vendors and hold them accountable with proof of their security capabilities.
Key Takeaways
- Shift from promises to proof in vendor security practices.
- 51% of UK organizations reported breaches via third parties.
- Continuous monitoring is crucial for real-time threat detection.
- AI and machine learning are key to future threat identification.
- Zero Trust minimizes network attack surfaces.
Related Articles
- Invisible Code in Supply-Chain Attacks: Unmasking the Threat [2025]
- SocksEscort Proxy Network Takedown: A Deep Dive [2025]
- Telus Digital's Massive Data Breach: An In-Depth Look [2025]
- The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]
- How the UK’s £180 Million Timing Investment Powers AI, 5G, and Autonomous Vehicles [2025]
- Identity Theft Protection Services: Do You Really Need One? [2025]
FAQ
What is Proof Over Promises: A New Doctrine for Cybersecurity [2025]?
Last year, a mid-sized tech firm unwittingly opened the door to a massive data breach through a trusted vendor
What does introduction mean?
The vendor had assured them of top-notch security with glowing promises, but the reality painted a different picture
Why is Proof Over Promises: A New Doctrine for Cybersecurity [2025] important in 2025?
This incident is not isolated; it's a growing trend
How can I get started with Proof Over Promises: A New Doctrine for Cybersecurity [2025]?
As cyber threats become more sophisticated, the doctrine of 'proof over promises' is emerging as a necessary shift in cybersecurity
What are the key benefits of Proof Over Promises: A New Doctrine for Cybersecurity [2025]?
- Proof over promises: Shift from verbal assurances to evidence-based security measures
What challenges should I expect?
- 51% of UK organizations: Reported breaches linked to third-party vendors in the past year
![Proof Over Promises: A New Doctrine for Cybersecurity [2025]](https://tryrunable.com/blog/proof-over-promises-a-new-doctrine-for-cybersecurity-2025/image-1-1773497022482.jpg)



