Quantum-Proofing the Web: Google's Mathematical Approach to Securing HTTPS [2025]
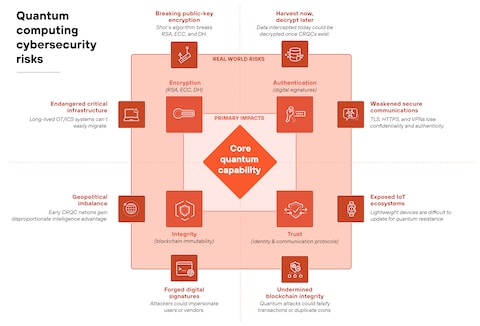
Quantum computing is no longer a concept confined to the realms of science fiction or academic research. With its rapid advancements, the potential of quantum computers to break traditional encryption methods has become a reality. In response, tech giants like Google are pioneering new ways to secure the internet. This article delves into the intricacies of Google’s approach to safeguarding HTTPS certificates against quantum threats using innovative mathematical strategies.
TL; DR
- Google's Approach: Google is employing advanced mathematical techniques to protect HTTPS certificates from quantum attacks.
- Quantum Threat: Quantum computers can potentially crack current encryption methods, including those used in HTTPS.
- Merkle Trees: Google uses Merkle Tree Certificates as a quantum-resistant solution.
- Implementation: The new certificates are significantly larger, posing transmission challenges.
- Future Outlook: Continuous advancements in quantum computing necessitate ongoing cryptographic innovation.
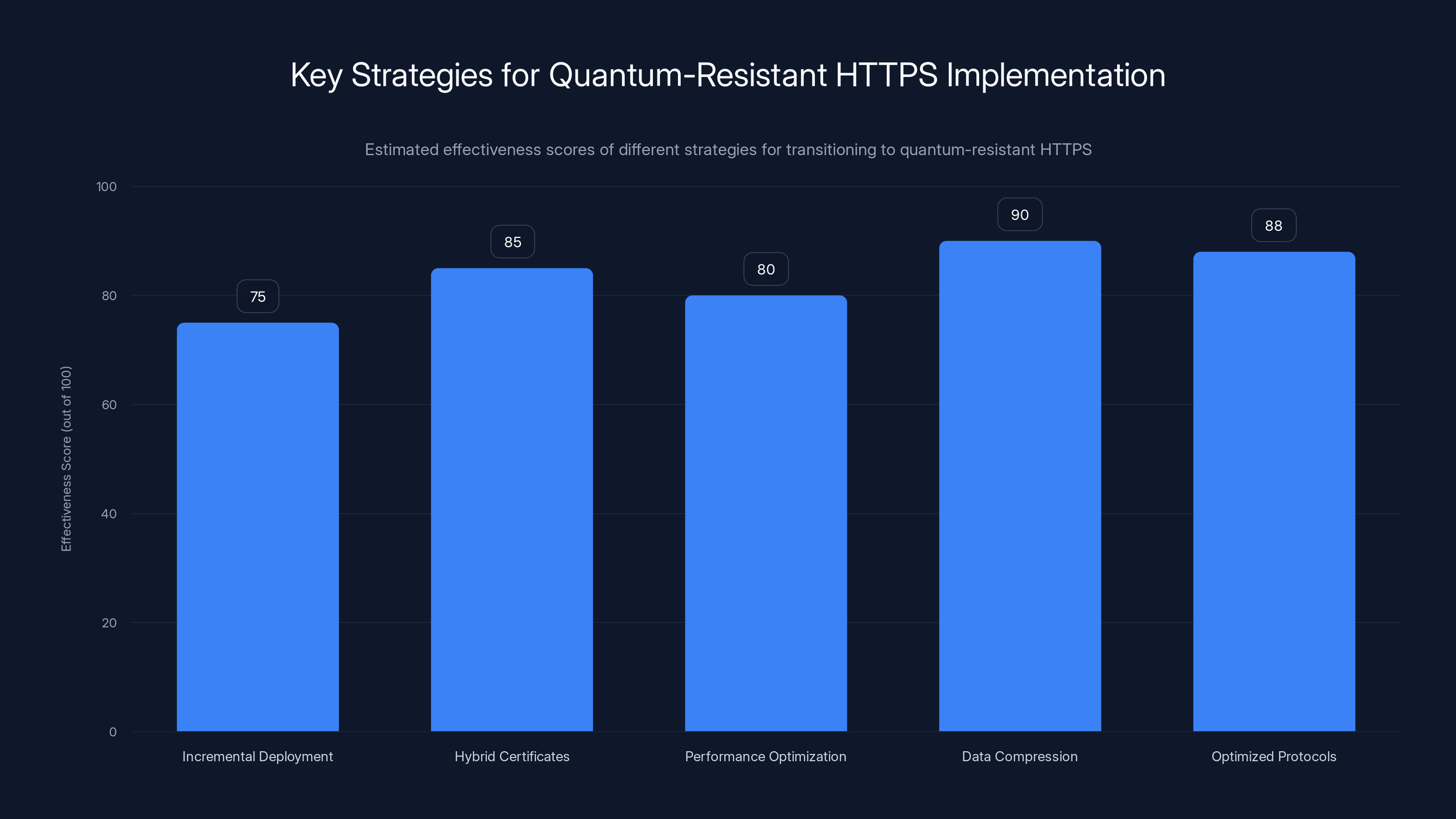
Hybrid certificates and data compression are estimated to be the most effective strategies for implementing quantum-resistant HTTPS, balancing security and performance. Estimated data.
The Quantum Threat to HTTPS
Understanding Quantum Computing
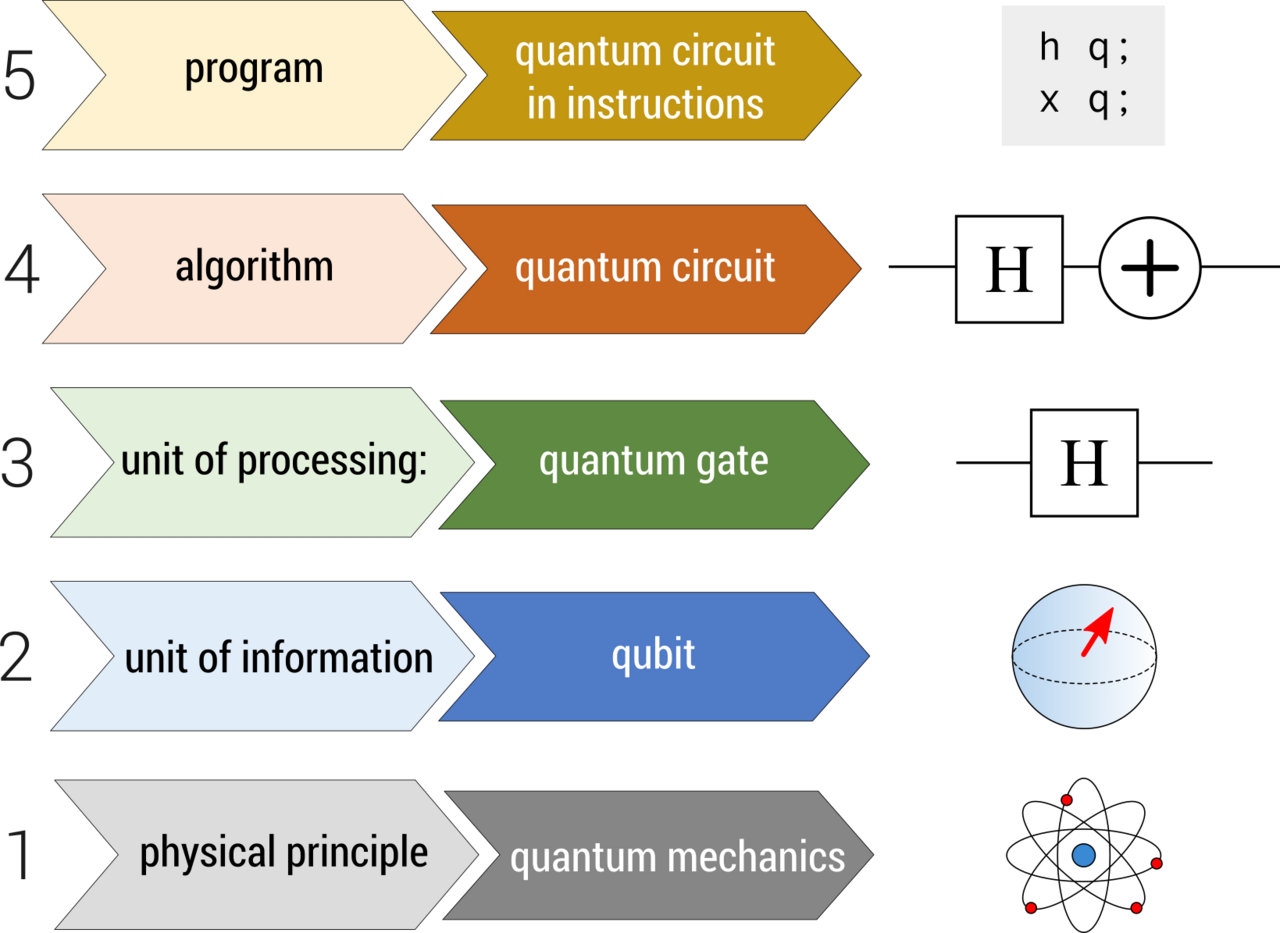
Quantum computing leverages the principles of quantum mechanics to perform calculations at unprecedented speeds. Unlike classical computers, which use bits as units of data (0s and 1s), quantum computers use qubits. These qubits can exist in multiple states simultaneously due to superposition, enabling them to process massive amounts of information quickly. This capability poses a significant threat to current cryptographic protocols.
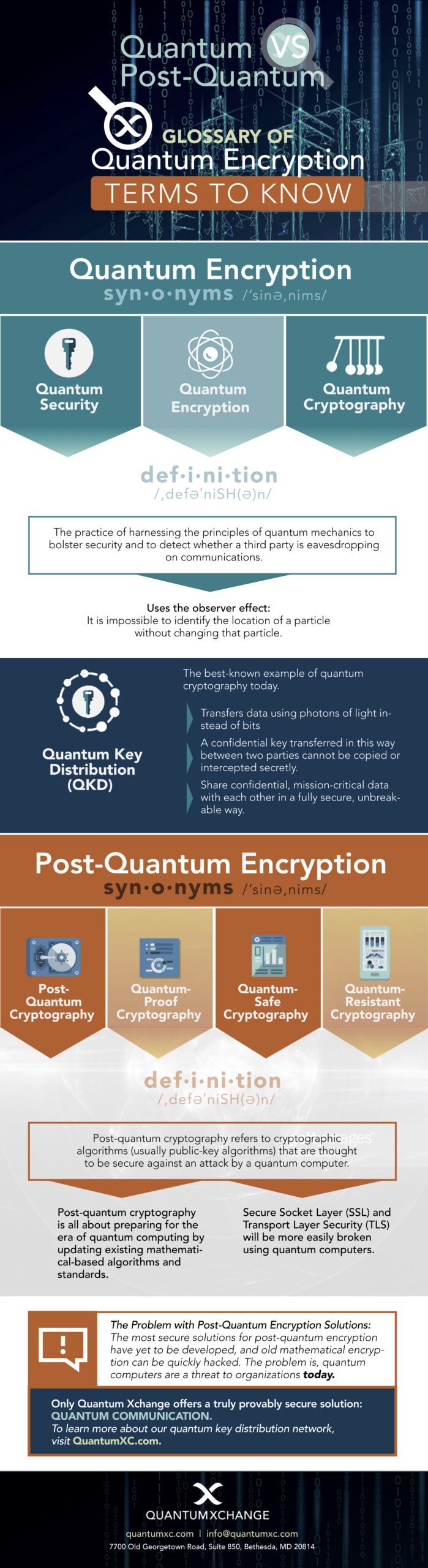
Why HTTPS is Vulnerable
Hypertext Transfer Protocol Secure (HTTPS) is the backbone of secure internet communications. It encrypts data between the user's browser and the website, ensuring privacy and data integrity. HTTPS relies on cryptographic algorithms like RSA and elliptic curve cryptography (ECC) to secure connections. However, with the advent of quantum computing, algorithms like Shor’s algorithm can efficiently factorize large numbers, rendering traditional encryption methods vulnerable.
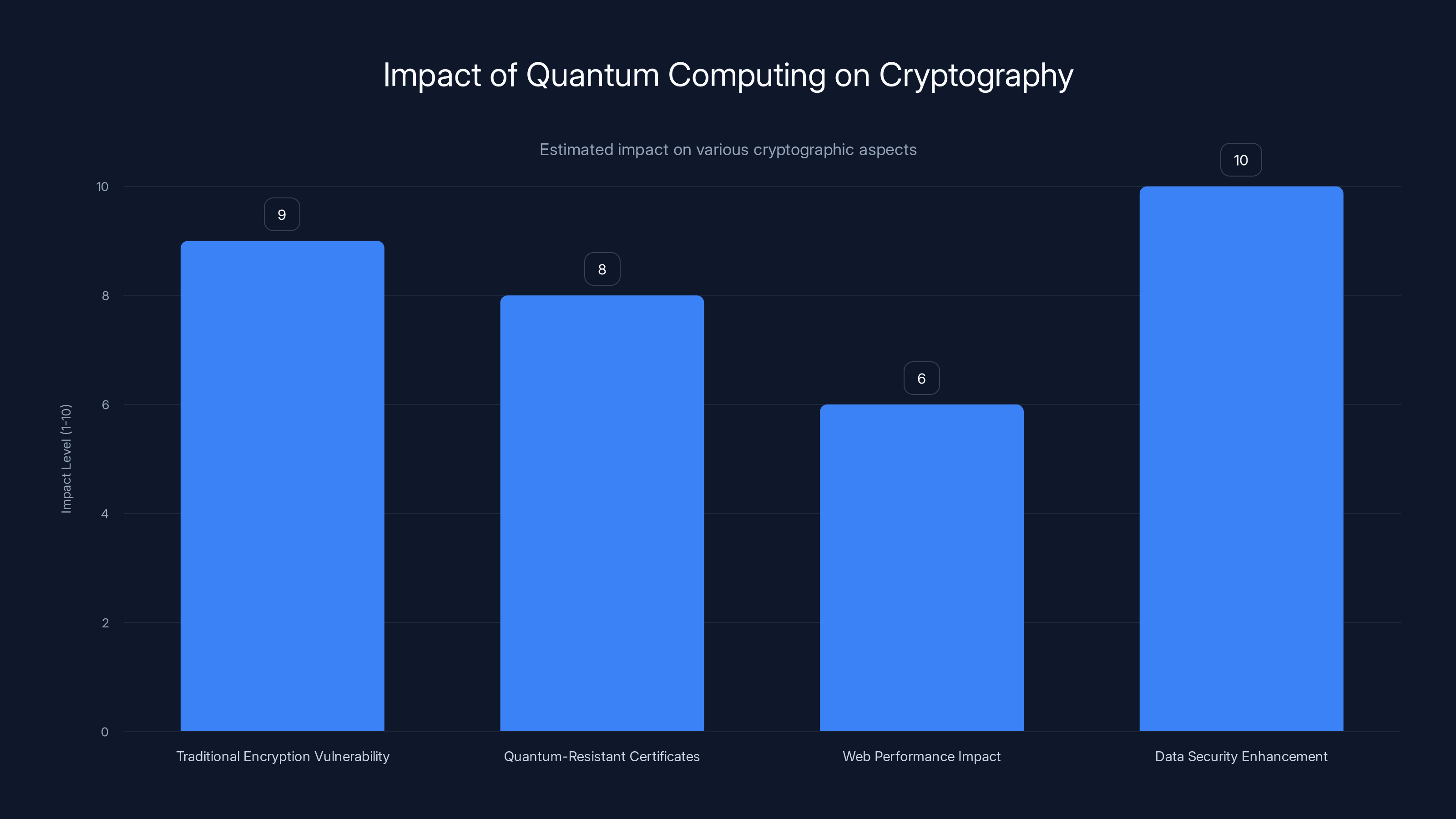
Quantum computing poses a high threat to traditional encryption (9/10), while quantum-resistant certificates offer strong security (8/10). Larger certificates slightly impact web performance (6/10), but significantly enhance data security (10/10). Estimated data.
Google's Quantum-Resistant Strategy
The Role of Merkle Trees
Google’s innovative solution involves the use of Merkle Tree Certificates. A Merkle tree is a data structure used in cryptographic applications to verify data integrity. It allows multiple pieces of data to be securely combined and verified with minimal computational power.
How Merkle Trees Work:
- Leaves: Each data point is a leaf node in the tree.
- Hashing: Each leaf node is hashed, and these hashes are combined to form the next level of the tree.
- Root Hash: The process continues until a single hash, known as the root hash, is produced.
Merkle trees provide a way to verify that a piece of data is part of a larger dataset without revealing the entire dataset. This feature is crucial for quantum-proofing HTTPS as it allows for efficient verification of larger data sizes required for quantum-resistant certificates.
The Challenge of Larger Certificates
Quantum-resistant cryptographic material is inherently larger. While traditional X.509 certificates are about 64 bytes, quantum-resistant certificates can be as large as 2.5 kilobytes. This increase poses a significant challenge in terms of data transmission and storage.
Practical Implementation of Quantum-Resistant HTTPS
Transition Strategies
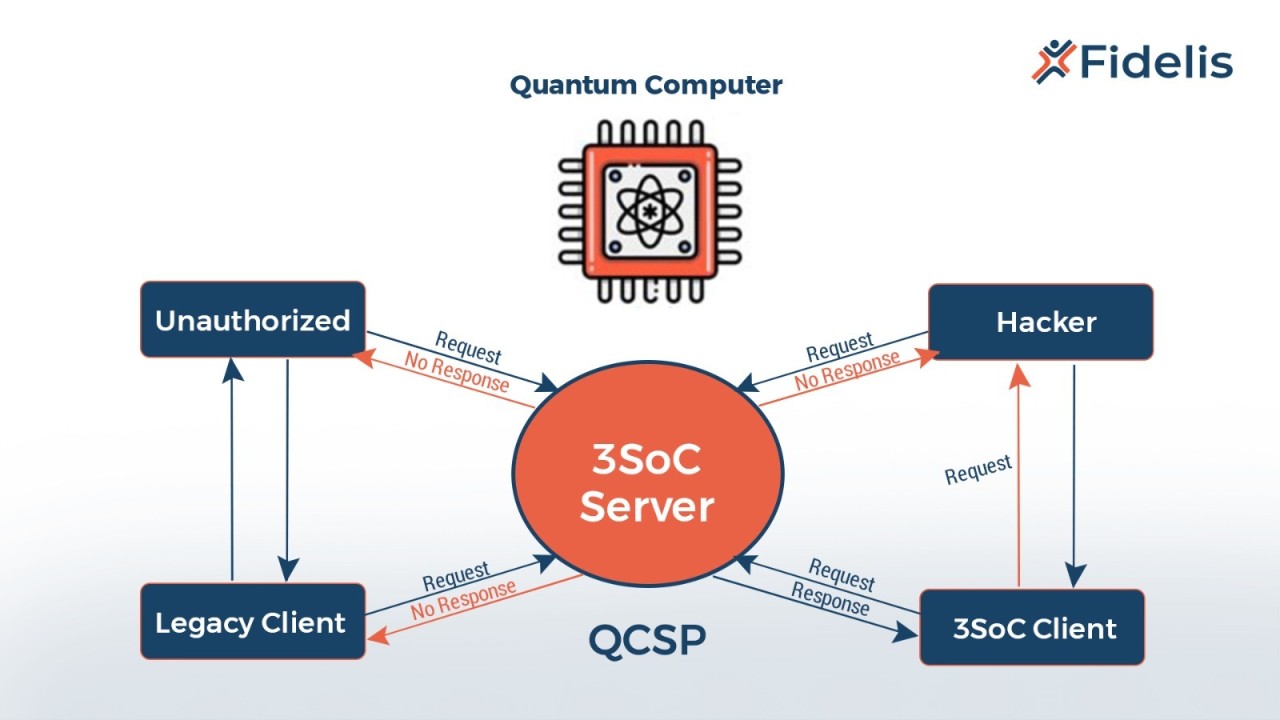
- Incremental Deployment: Gradually introduce quantum-resistant certificates alongside traditional ones to ensure compatibility and allow for testing.
- Hybrid Certificates: Use a combination of classical and quantum-resistant algorithms to balance performance and security during the transition phase.
- Performance Optimization: Implement compression techniques and optimize server infrastructure to handle the increased data size efficiently.
Overcoming Transmission Challenges
Google is exploring several methods to mitigate the transmission challenges posed by larger certificates:
- Data Compression: Efficient compression algorithms can significantly reduce the size of data transmitted.
- Optimized Protocols: Updating network protocols to handle larger data packets without significant latency increases.
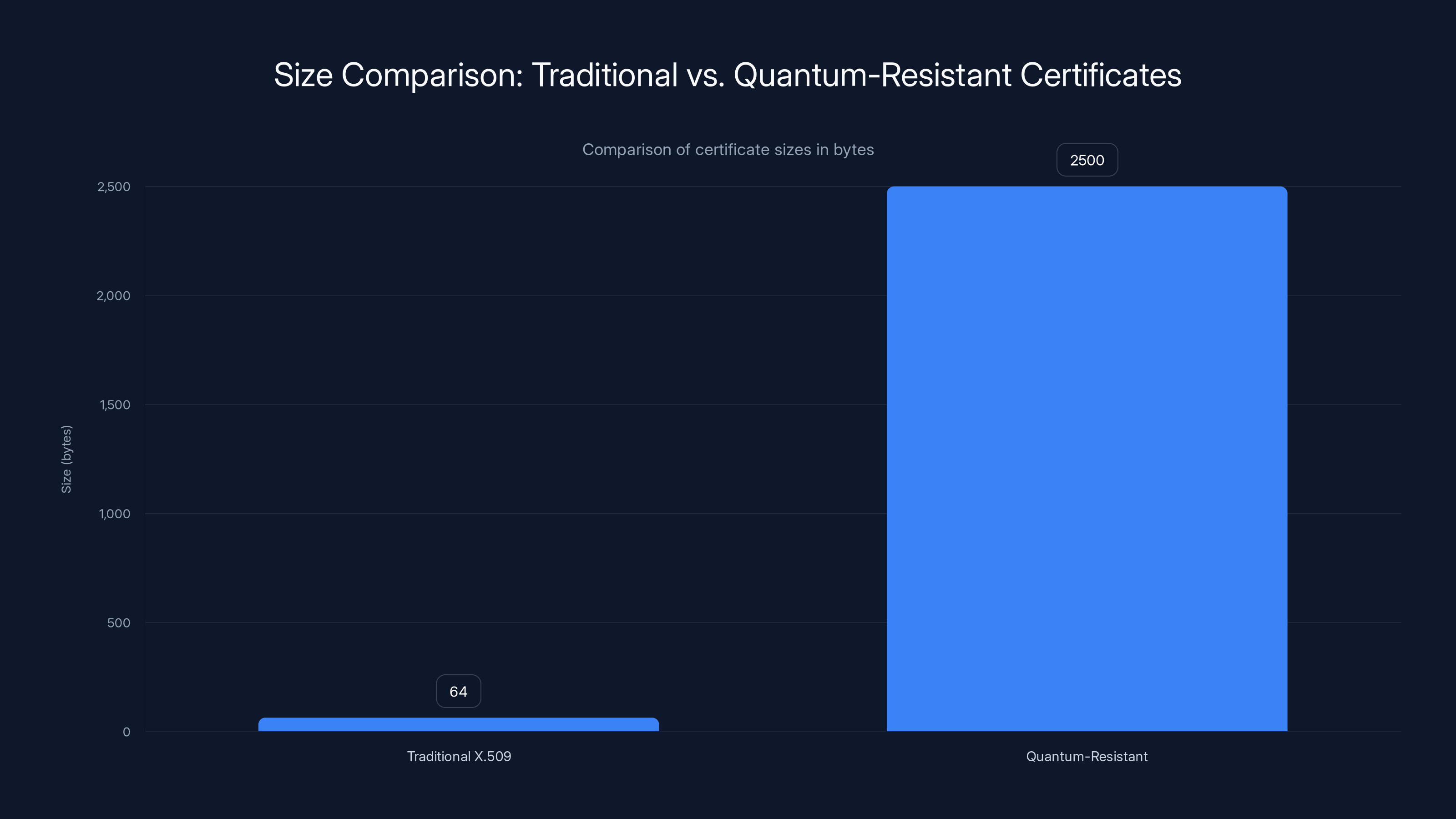
Quantum-resistant certificates are significantly larger, up to 2.5 kilobytes, compared to traditional 64-byte X.509 certificates, posing challenges in data transmission and storage.
Common Pitfalls and Solutions
Pitfall: Latency Issues
Solution: Employ Content Delivery Networks (CDNs) to distribute the load and reduce latency by caching certificates closer to users.
Pitfall: Compatibility Problems
Solution: Develop backward-compatible solutions that allow older systems to continue functioning while supporting new protocols.
Pitfall: Increased Costs
Solution: Optimize resource allocation and leverage cloud-based solutions to manage increased data processing requirements cost-effectively.
Future Trends in Quantum-Resistant Cryptography
Continual Evolution
The field of quantum computing and cryptography is rapidly evolving. As quantum processors become more powerful, cryptographic methods must also advance to stay ahead of potential threats.
Collaboration and Standardization
Global collaboration among tech companies, academic institutions, and standardization bodies is crucial for developing universally accepted quantum-resistant protocols. According to StateScoop, such collaborations are essential for addressing the challenges posed by quantum computing.
Recommendations for Organizations
- Stay Informed: Keep up with the latest developments in quantum computing and cryptography.
- Test and Implement Gradually: Begin testing quantum-resistant solutions in non-critical environments.
- Collaborate: Work with industry peers to share knowledge and best practices.
Conclusion
Google's initiative to quantum-proof HTTPS certificates is a significant step forward in securing the internet against future threats. As quantum computing continues to evolve, staying ahead in the cryptographic race will be crucial for maintaining data security and privacy. By leveraging advanced mathematical techniques like Merkle trees and planning for seamless transitions, organizations can protect themselves from the quantum threats of tomorrow.

FAQ
What is quantum computing?
Quantum computing uses qubits and principles of quantum mechanics to process information at speeds unattainable by classical computers.
How do Merkle trees work in cryptography?
Merkle trees secure data integrity by combining multiple data hashes into a single root hash, allowing efficient verification.
Why is HTTPS vulnerable to quantum computers?
Quantum computers can break traditional encryption algorithms like RSA and ECC using Shor’s algorithm.
What are quantum-resistant certificates?
These are larger cryptographic certificates designed to withstand attacks from quantum computers, ensuring data security.
How can organizations prepare for quantum threats?
Organizations should stay informed, test quantum-resistant solutions, and collaborate with industry peers to develop best practices.
What is Google’s role in quantum-proofing the internet?
Google is leading efforts to secure HTTPS certificates using advanced math, particularly through the use of Merkle Tree Certificates.
How do larger certificates affect web performance?
Larger certificates can increase latency and data transmission times, but solutions like data compression and optimized protocols can mitigate these effects.
What are the benefits of quantum-resistant cryptography?
Quantum-resistant cryptography ensures long-term data security against emerging threats from quantum computing advancements.

Key Takeaways
- Google is using Merkle Tree Certificates to quantum-proof HTTPS.
- Quantum computers pose a significant threat to current encryption methods.
- Quantum-resistant certificates are larger, requiring innovative transmission solutions.
- Organizations need to prepare for the quantum computing era with new cryptographic strategies.
- Continual cryptographic advancements are necessary to counter evolving quantum threats.
- Collaboration is key in developing standardized quantum-resistant protocols.
- Testing and gradual implementation of quantum-resistant solutions are recommended.
- Merkle trees provide efficient verification for larger cryptographic data.
Related Articles
- Debunking the Top Five Myths About Sovereign Cloud [2025]
- Understanding the Impact of Data Broker Breaches on Identity Theft [2025]
- Google's Opal: The New Blueprint for Building AI Agents in Enterprises [2025]
- How Virtual Photons Influence Superconductivity [2025]
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
- AI vs. the Pentagon: Killer Robots, Mass Surveillance, and Red Lines [2025]
![Quantum-Proofing the Web: Google's Mathematical Approach to Securing HTTPS [2025]](https://tryrunable.com/blog/quantum-proofing-the-web-google-s-mathematical-approach-to-s/image-1-1772242457618.jpg)




