Understanding the Impact of Data Broker Breaches on Identity Theft [2025]
In an era where information is more valuable than oil, data breaches have become alarmingly common. Data brokers, companies that collect and sell data on individuals, have found themselves at the center of this storm. A recent report highlights that breaches from data brokers have contributed to nearly $21 billion in identity-theft losses. This article delves deep into the mechanics of these breaches, their impact, and how both individuals and organizations can protect themselves.
TL; DR
- Data broker breaches have led to $21 billion in identity-theft losses, impacting millions.
- Sensitive data such as Social Security numbers and financial information are often compromised.
- Preventive measures include enhancing cybersecurity practices and regulatory compliance.
- Technological advancements like AI and blockchain offer promising solutions.
- Future trends indicate a shift towards stricter data privacy laws.

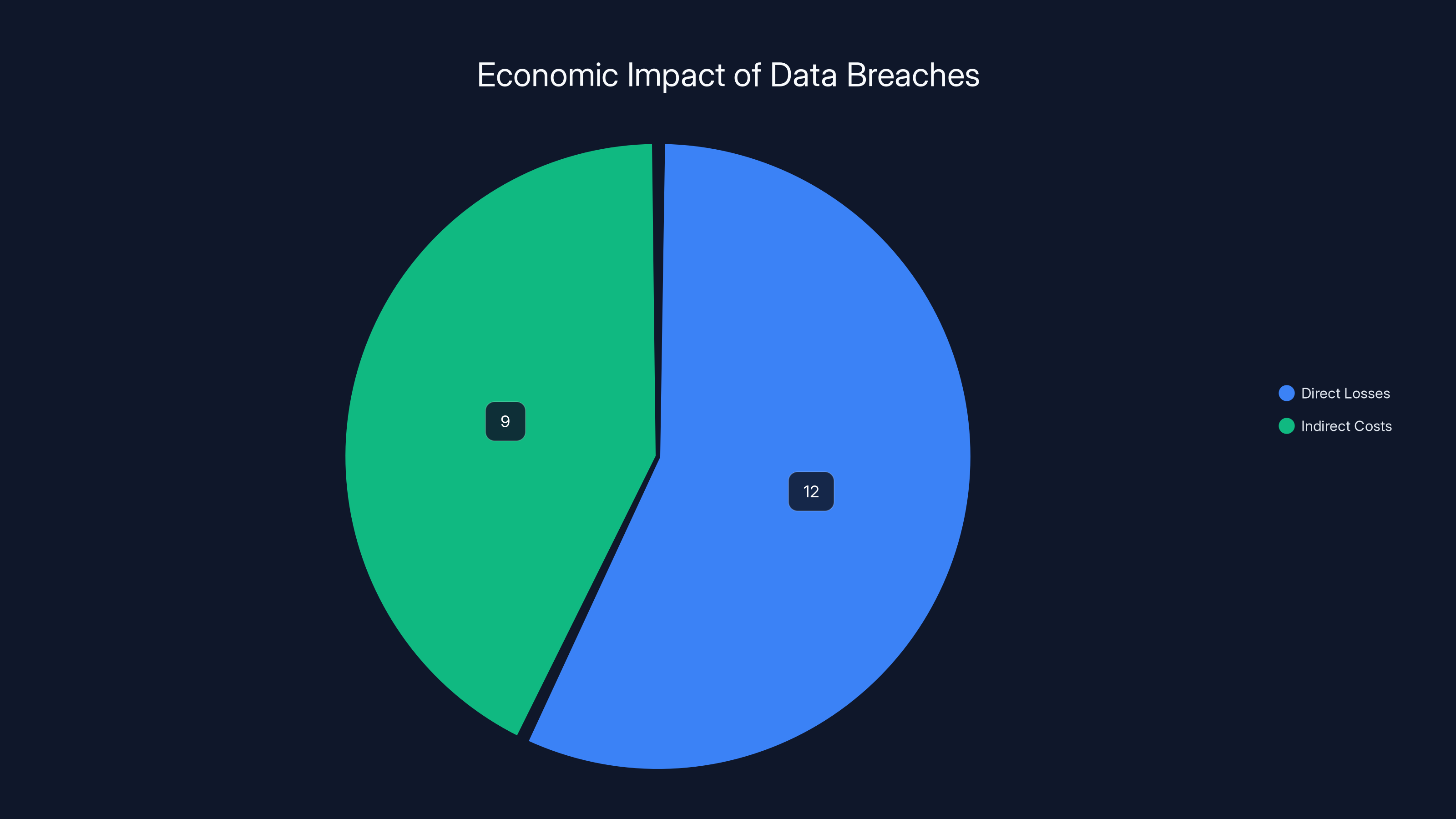
Direct losses, including stolen funds and identity restoration, account for
What Are Data Brokers?
Data brokers are entities that collect, analyze, and sell personal information. They gather data from various sources, including public records, social media, and online activities. This data is then sold to companies for marketing, research, or credit assessment purposes.
How Do Data Brokers Operate?
Data brokers use sophisticated algorithms to piece together profiles of individuals. They purchase data from multiple sources, including:
- Public records: Birth certificates, marriage licenses, and voter registrations.
- Online activities: Browsing history, social media interactions, and online purchases.
- Commercial sources: Retail transactions and loyalty card data.
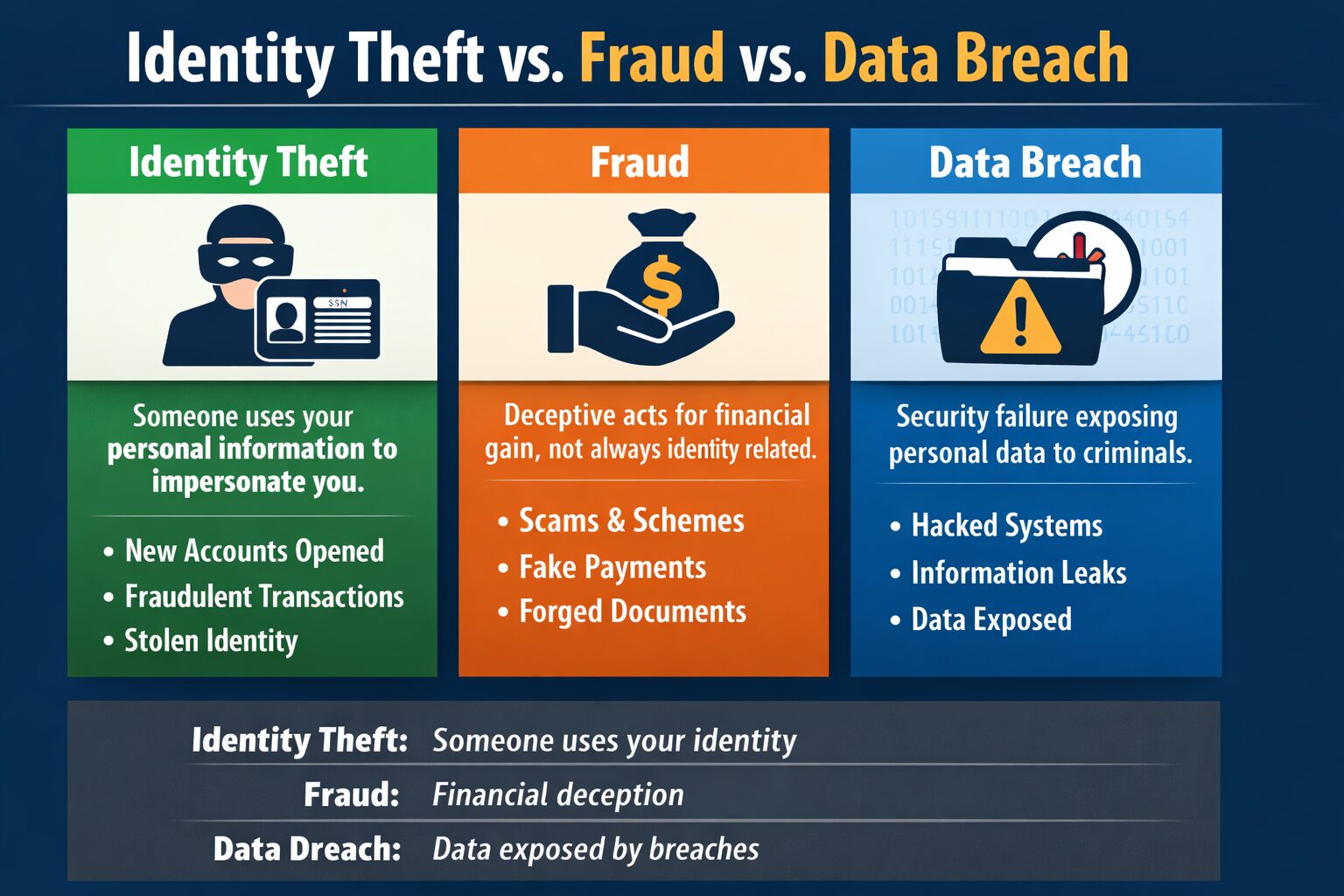
The Role of Data Brokers in Identity Theft
When data brokers are breached, the consequences can be severe. Hackers often target these companies because of the sheer volume and value of the data they hold. Once accessed, this information can be used for identity theft, leading to financial losses and personal distress.

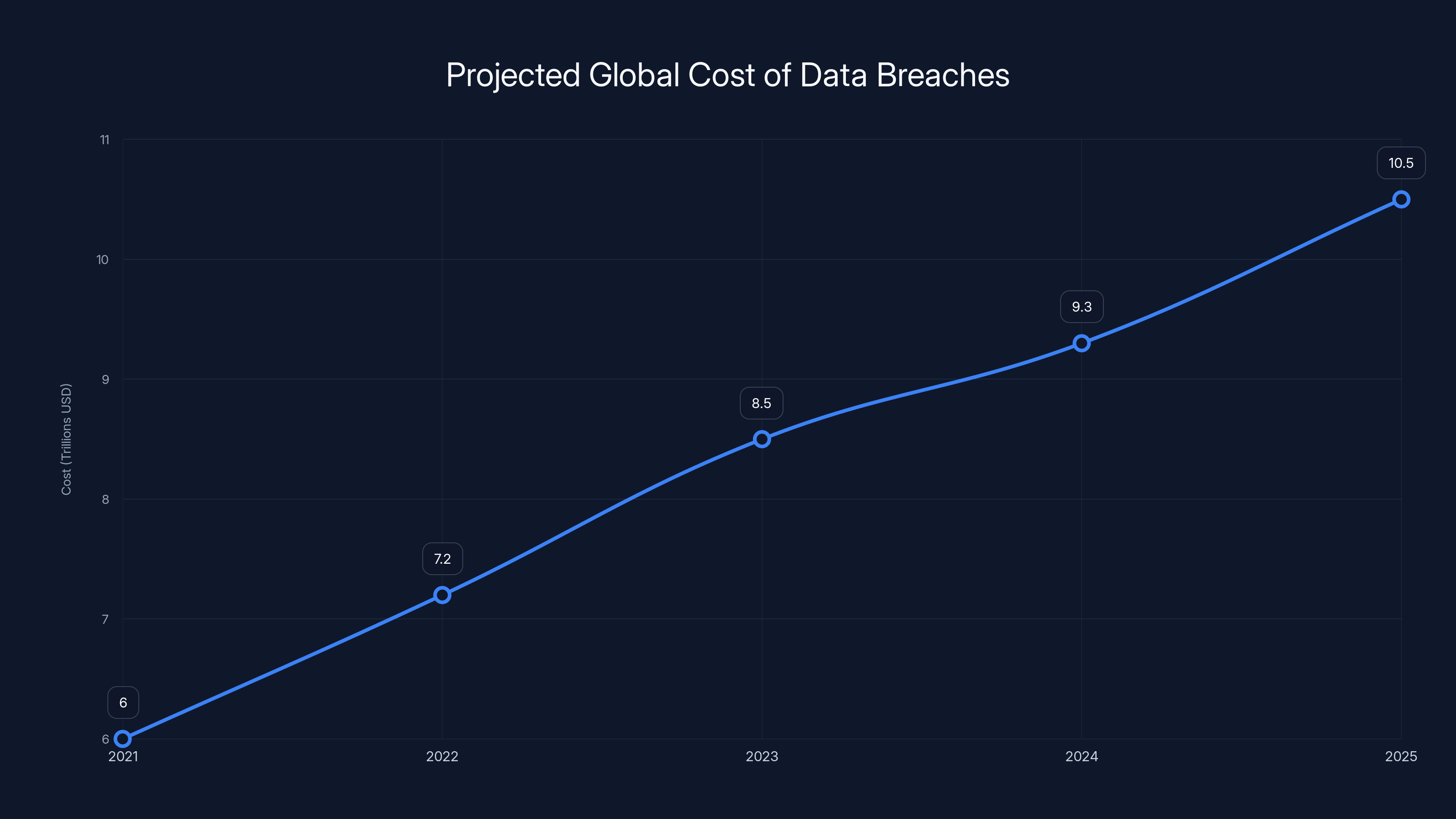
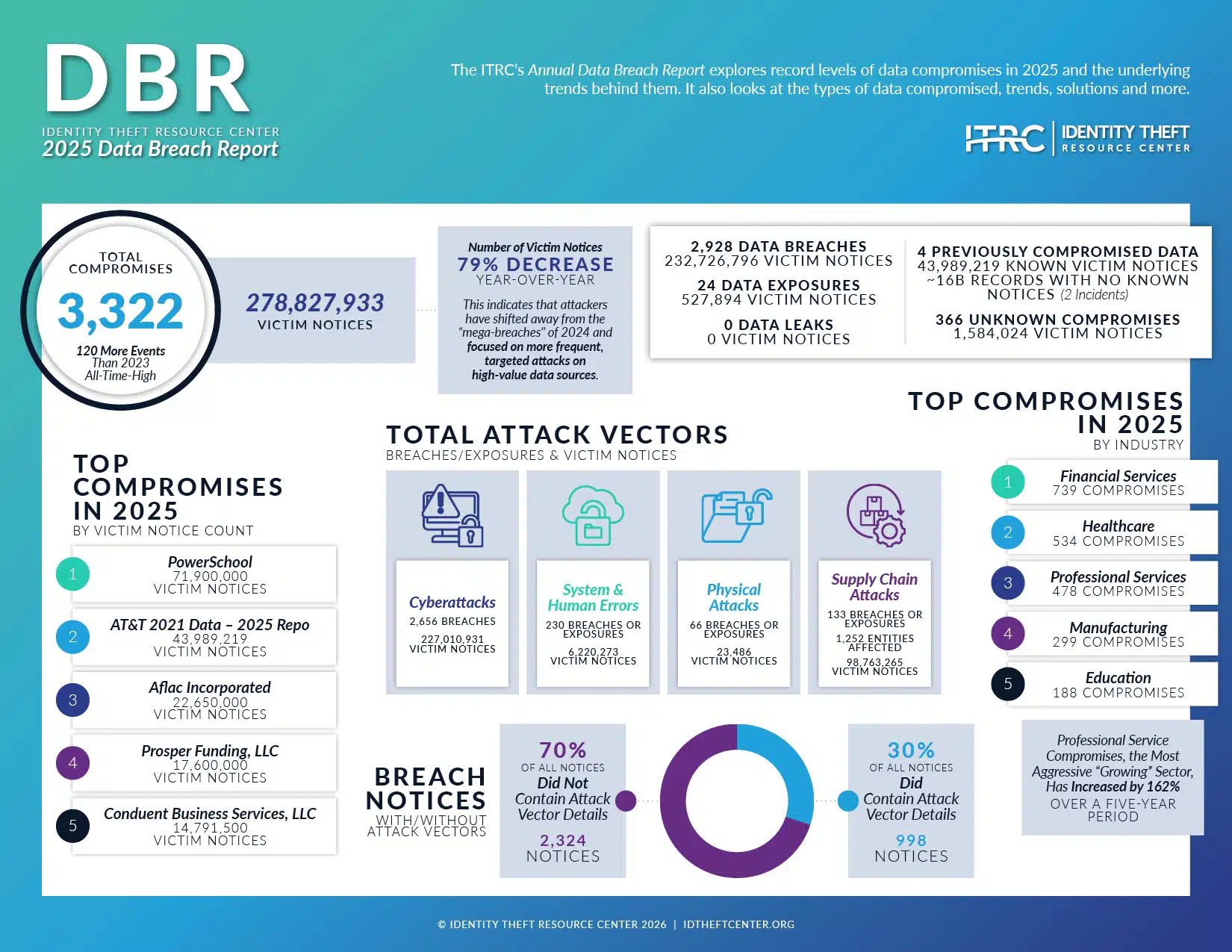
The global cost of data breaches is projected to rise significantly, reaching $10.5 trillion by 2025. Estimated data based on current trends.
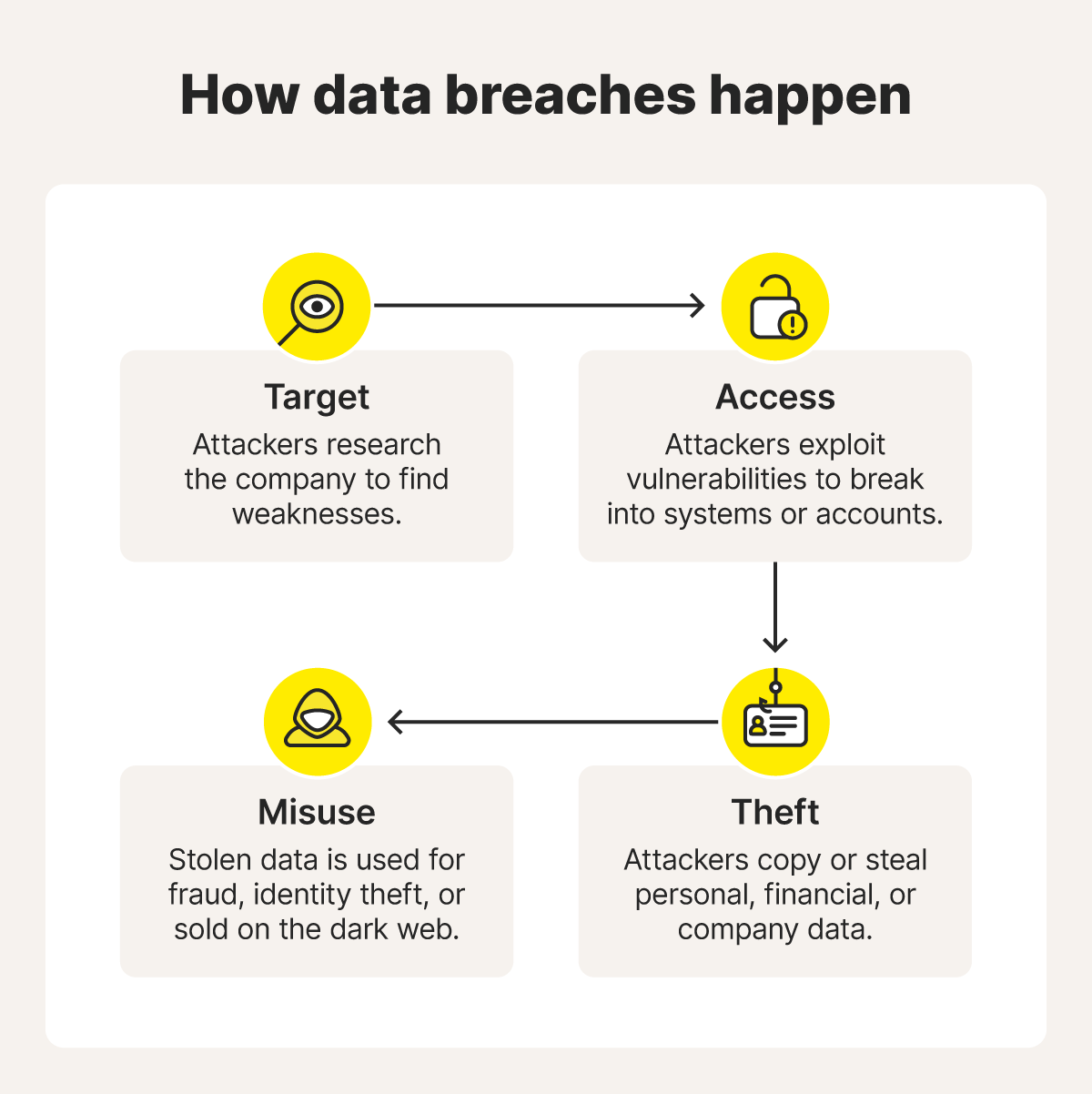
Anatomy of a Data Broker Breach
Understanding how breaches occur is crucial for prevention. Data breaches can result from various vulnerabilities, including weak security protocols, insider threats, or sophisticated cyberattacks.
Common Tactics Used by Hackers
- Phishing: Deceptive emails aimed at tricking employees into revealing login credentials.
- Malware: Malicious software used to gain unauthorized access to systems.
- SQL Injection: A code injection technique that exploits vulnerabilities in databases.
Case Study: The Impact of a Major Breach
In a high-profile case, a breach at a major data broker exposed millions of Social Security numbers and financial records. The aftermath included significant financial losses for individuals and legal repercussions for the company.
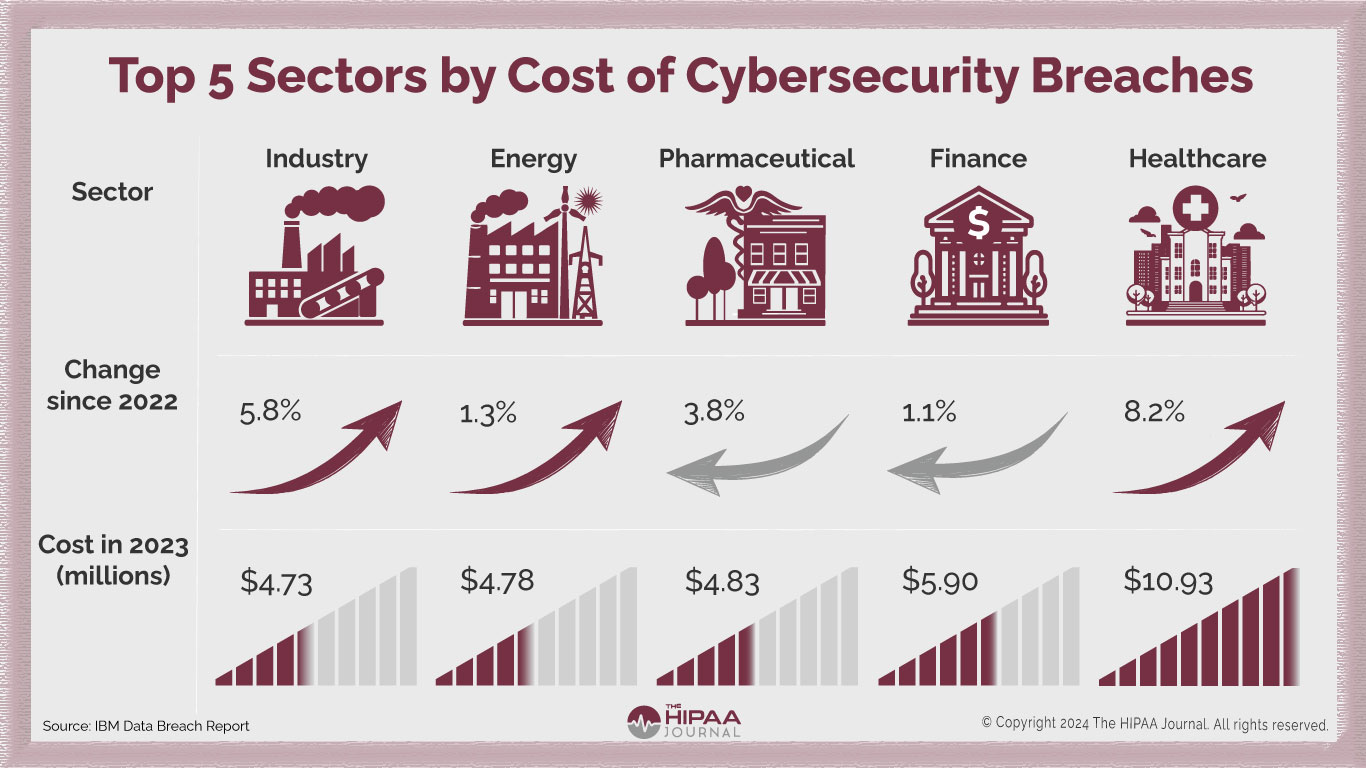
The Economic Impact of Data Broker Breaches
The financial implications of data broker breaches are vast. Beyond the $21 billion in identity-theft losses, businesses face legal fines, reputational damage, and a loss of consumer trust.
Cost Breakdown
- Direct losses: Stolen funds, fraudulent purchases, and identity restoration costs.
- Indirect costs: Legal fees, increased insurance premiums, and regulatory fines.

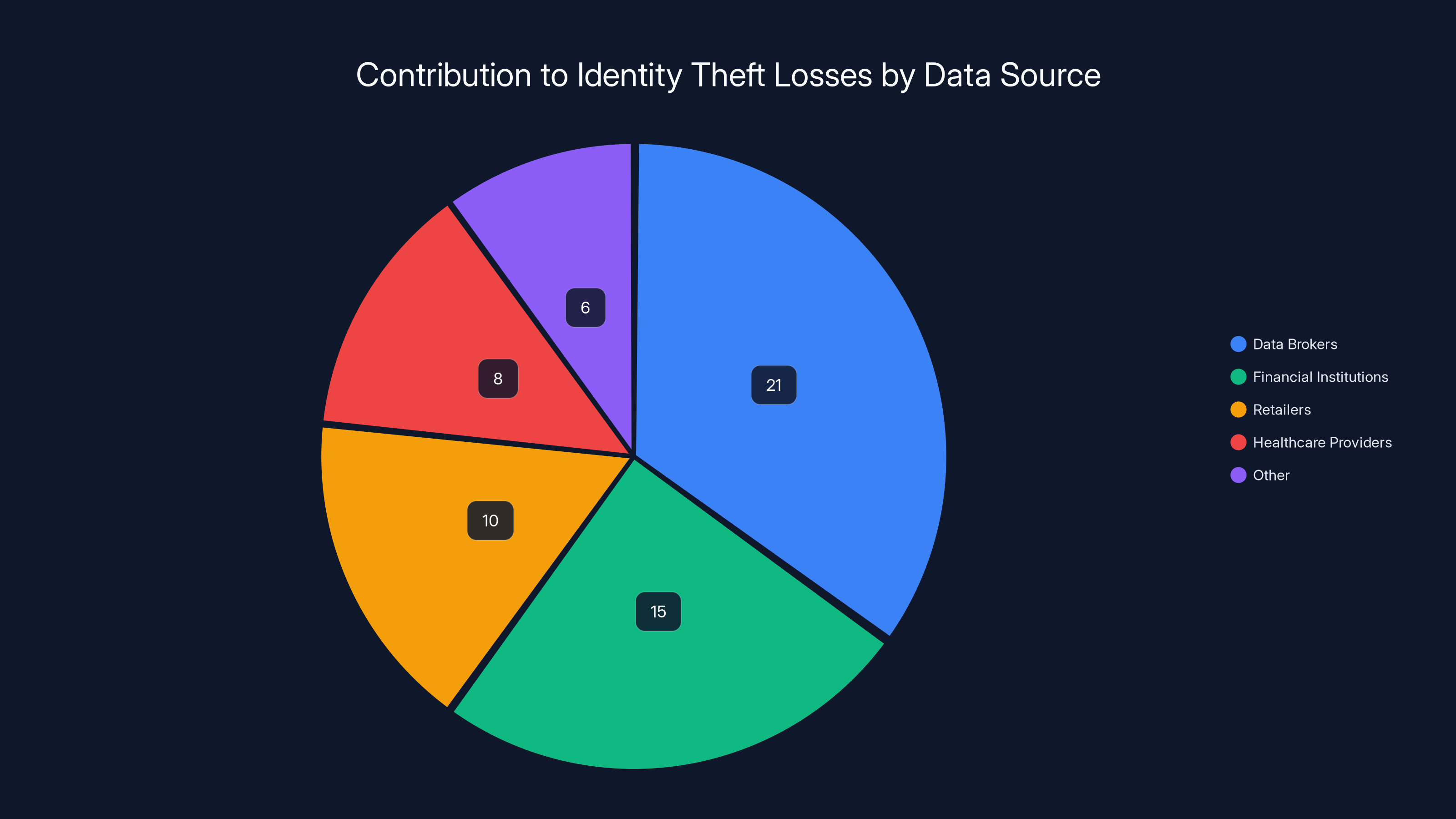
Data brokers are estimated to contribute the largest share of identity theft losses, highlighting their critical role in data security breaches. Estimated data.
Regulatory Landscape: Laws and Compliance
To combat the rise in data breaches, governments worldwide are implementing stricter data privacy laws. These regulations aim to hold companies accountable for protecting consumer data.
Key Regulations
- GDPR: The General Data Protection Regulation in the EU imposes heavy fines for non-compliance.
- CCPA: The California Consumer Privacy Act grants consumers more control over their personal information.
Best Practices for Data Protection
Organizations can implement several strategies to protect against data breaches:
- Encryption: Protects data by converting it into a code to prevent unauthorized access.
- Regular Audits: Periodic reviews of security protocols to identify vulnerabilities.
- Employee Training: Educating staff about cybersecurity risks and prevention techniques.
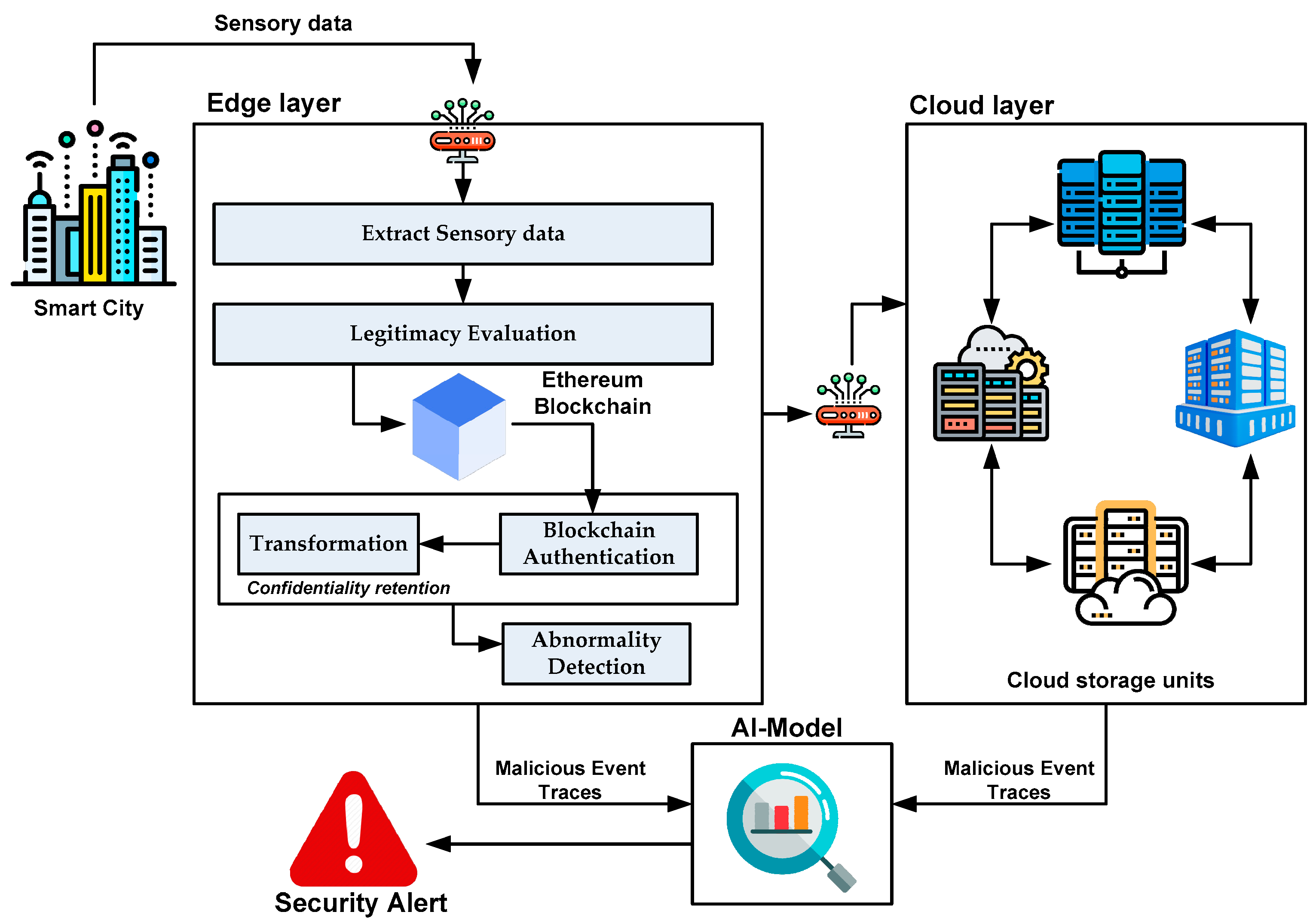
The Role of Technology in Preventing Breaches
Technological innovations are pivotal in enhancing data security. AI and blockchain technologies offer new avenues for protecting sensitive information.
How AI Can Help
AI algorithms can detect unusual patterns in data access and usage, providing early warnings of potential breaches. They can also automate threat detection and response.
Blockchain for Data Security
Blockchain's decentralized nature makes it inherently secure. By storing data in distributed ledgers, blockchain reduces the risk of unauthorized access.

Future Trends in Data Privacy and Security
As the digital landscape evolves, so do the threats and solutions. Future trends in data privacy include:
- Increased Regulation: More comprehensive data privacy laws and cross-border data transfer restrictions.
- Privacy-Enhancing Technologies: Tools like secure multi-party computation and homomorphic encryption.
- Consumer Empowerment: Tools allowing individuals to control their data footprints.
Practical Steps for Individuals
While organizations play a significant role in data protection, individuals can also take steps to safeguard their personal information.
Personal Security Measures
- Use Strong Passwords: Combine letters, numbers, and symbols for robust passwords.
- Monitor Financial Statements: Regularly check bank and credit card statements for unauthorized transactions.
- Identity Theft Protection Services: Consider services that monitor personal information for signs of fraud.

Conclusion
Data broker breaches pose a significant threat to both individuals and organizations. By understanding the mechanisms of these breaches and implementing robust security measures, we can mitigate the risks associated with identity theft. As technology and regulations evolve, staying informed and proactive is key to safeguarding personal and organizational data.
FAQ
What is a data broker?
A data broker is a company that collects personal information from various sources and sells it to other organizations for marketing, research, or credit assessment purposes.
How do data brokers contribute to identity theft?
When data brokers experience breaches, sensitive personal information such as Social Security numbers and financial data can be exposed, leading to identity theft.
What are some examples of data privacy regulations?
Examples include the General Data Protection Regulation (GDPR) in the EU and the California Consumer Privacy Act (CCPA) in the United States.
How can individuals protect their data?
Individuals can protect their data by using strong passwords, monitoring financial statements, and considering identity theft protection services.
What technologies help secure data?
AI and blockchain are two technologies that enhance data security by detecting anomalies and providing decentralized storage, respectively.
What are future trends in data privacy?
Future trends include increased regulation, privacy-enhancing technologies, and tools for consumer empowerment.

Key Takeaways
- Data broker breaches have led to $21 billion in identity-theft losses.
- Sensitive data like Social Security numbers are often compromised.
- AI and blockchain are promising technologies for data security.
- Stricter data privacy laws are being implemented worldwide.
- Individuals can protect themselves with strong passwords and monitoring financial statements.
- Future trends suggest increased consumer empowerment in data privacy.
Related Articles
- The Human Risk Reckoning: Evolving Security for an AI-Augmented Workforce [2025]
- Understanding the AirSnitch Attack: Wi-Fi Encryption Risks and Mitigation [2025]
- How Hackers Are Using AI to Exploit Security Flaws Faster Than Ever [2025]
- The Future of PayPal: Navigating Market Dynamics and Strategic Decisions [2025]
- How Chinese AI Chatbots Censor Themselves [2025]
- Maximizing Your Craft Space: The Compact Revolution of Cricut's Premier Cutting Machine [2025]
![Understanding the Impact of Data Broker Breaches on Identity Theft [2025]](https://tryrunable.com/blog/understanding-the-impact-of-data-broker-breaches-on-identity/image-1-1772188465400.jpg)



