Socks Escort Proxy Network Takedown: A Deep Dive [2025]
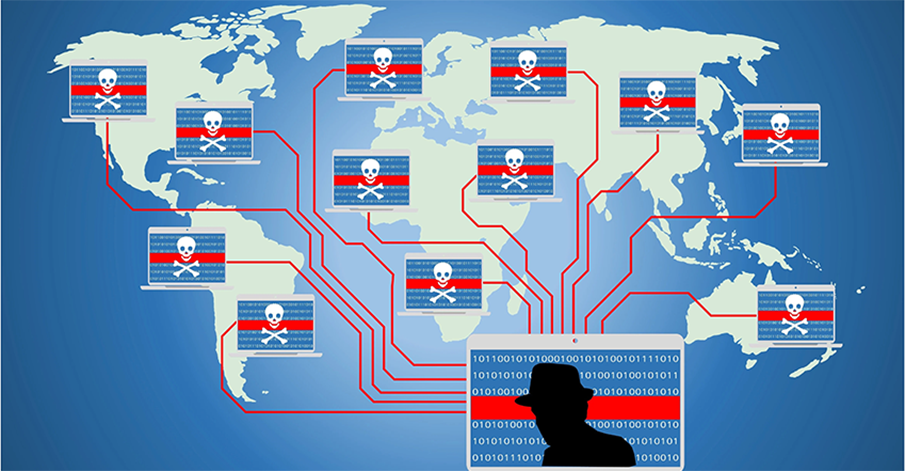
In a significant blow to cybercrime, an international task force led by the FBI recently dismantled the Socks Escort proxy network, a notorious operation that leveraged compromised IoT devices to facilitate illicit activities. Dubbed "Operation Lightning," this takedown not only curbed a major source of cybercriminal activity but also highlighted the vulnerabilities within our digital infrastructure. According to Europol, the operation was a collaborative effort involving multiple international law enforcement agencies.
TL; DR
- Operation Lightning: Dismantled the Socks Escort network, impacting over 369,000 devices globally, as reported by PCMag.
- Technical Exploit: Leveraged Linux malware to infiltrate and control IoT devices.
- Financial Impact: Seized $3.5 million in cryptocurrency connected to illegal activities, a figure highlighted by The Hacker News.
- Global Reach: Affected devices across 163 countries, underscoring the global nature of cyber threats, as noted by The Register.
- Future Implications: Encourages enhanced cybersecurity measures and international cooperation.

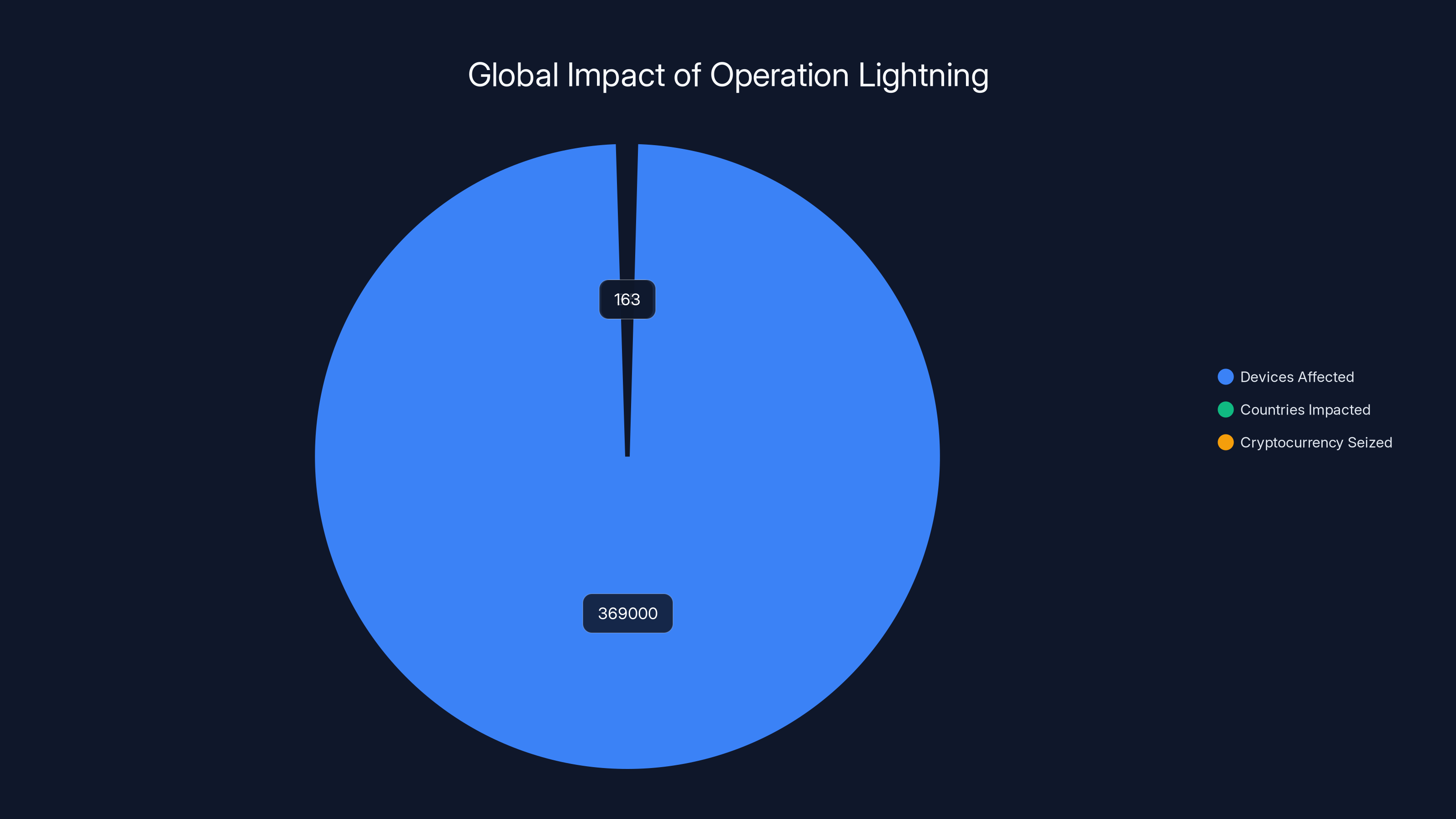
Operation Lightning dismantled a network affecting 369,000 devices across 163 countries and seized $3.5 million in cryptocurrency, highlighting the extensive reach and financial stakes of cyber threats.
Introduction
The world of cybersecurity is a perpetual cat-and-mouse game between attackers and defenders. The recent dismantling of the Socks Escort proxy network is a testament to this ongoing struggle. This network had been a thorn in the side of cybersecurity professionals for over a decade, exploiting vulnerabilities in IoT devices to create a vast proxy network that masked illegal activities.
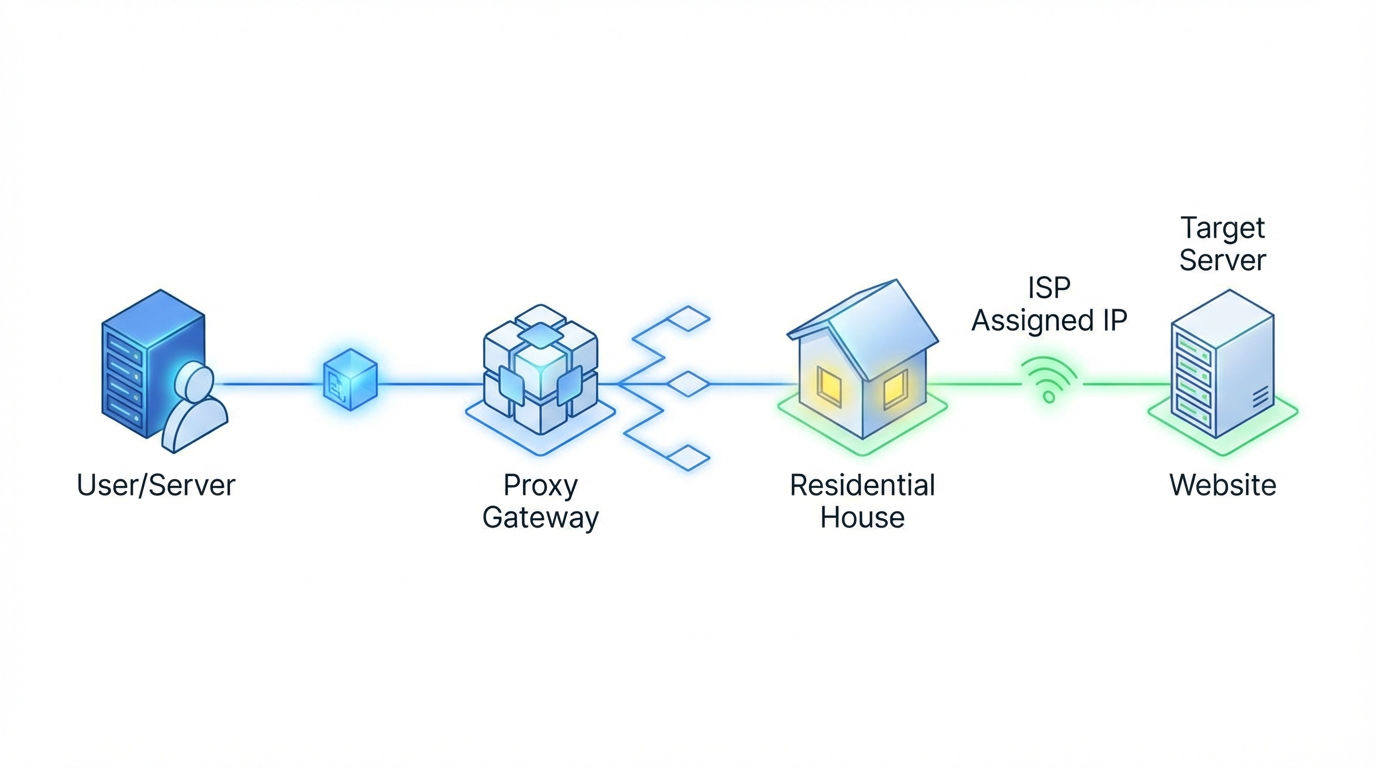
Understanding Residential Proxies
Residential proxies are a type of proxy server that uses real IP addresses assigned by Internet Service Providers (ISPs), making them appear as legitimate home users. This makes them particularly useful for hiding malicious activities, as they blend in with regular internet traffic.
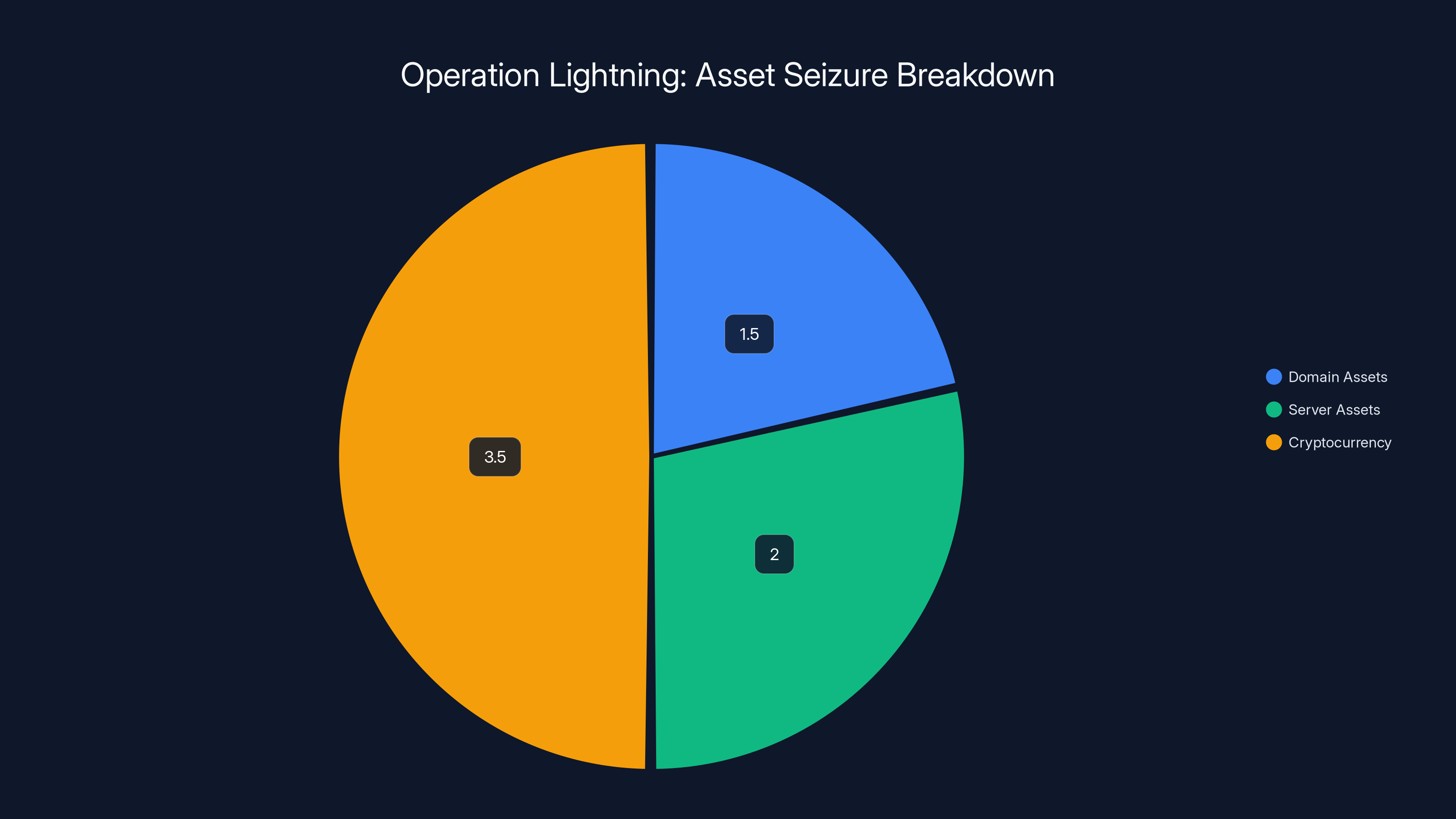
The operation led to the seizure of approximately $3.5 million in cryptocurrency, alongside domain and server assets, highlighting the financial impact of the takedown.
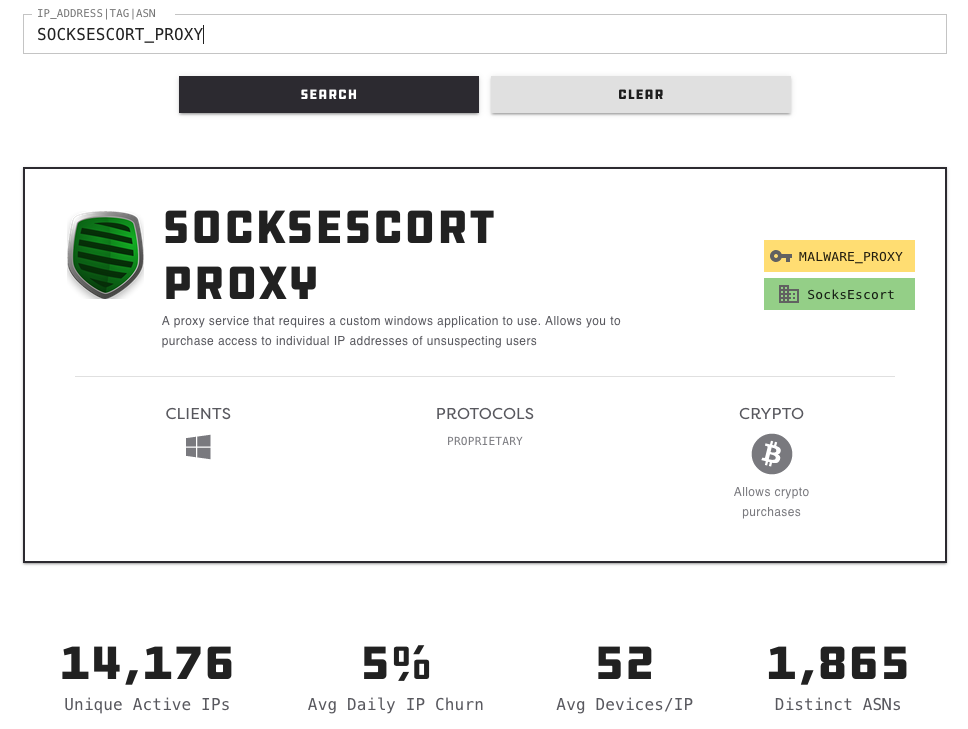
The Anatomy of the Socks Escort Network
The Socks Escort network was a sophisticated operation that compromised over 369,000 routers and IoT devices. These devices were infected with Linux-based malware, transforming them into unwitting participants in a global proxy network, as detailed by Europol.
Technical Details
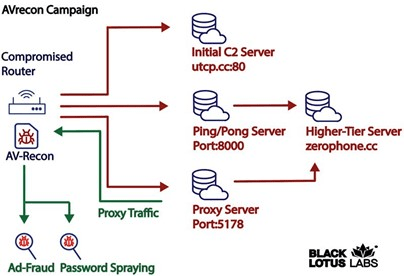
The malware used in the Socks Escort operation primarily targeted Linux-based systems, exploiting vulnerabilities within outdated firmware and poor security configurations commonly found in IoT devices. Once infected, these devices became part of a botnet, routing illicit traffic through legitimate IP addresses.
Key Characteristics of the Malware:
- Persistence Mechanisms: Implemented to survive reboots and firmware updates.
- Command and Control (C&C) Servers: Used to manage the botnet, issuing commands and collecting data.
- Dynamic IP Rotation: Regularly changed IP addresses to evade detection by cybersecurity measures.
Impact and Exploits
The Socks Escort network was used for a variety of nefarious purposes, including credential stuffing, DDoS attacks, and even click fraud. Its ability to mask origins made it highly sought after by cybercriminals looking to obscure their activities.

Operation Lightning: The Takedown
Coordinated by the FBI, Operation Lightning involved multiple international law enforcement agencies. The operation meticulously tracked the network's infrastructure, identifying key servers and the financial backbone supporting the operation, as reported by Europol.
Seizure and Shutdown
The takedown was executed in several stages:
- Domain Seizure: Law enforcement seized domains used by the Socks Escort network, disrupting its operation.
- Server Confiscation: Key servers were identified and confiscated to dismantle the network's core infrastructure.
- Financial Seizure: Approximately $3.5 million in cryptocurrency was seized, believed to be profits from illegal activities facilitated by the network, as highlighted by The Register.
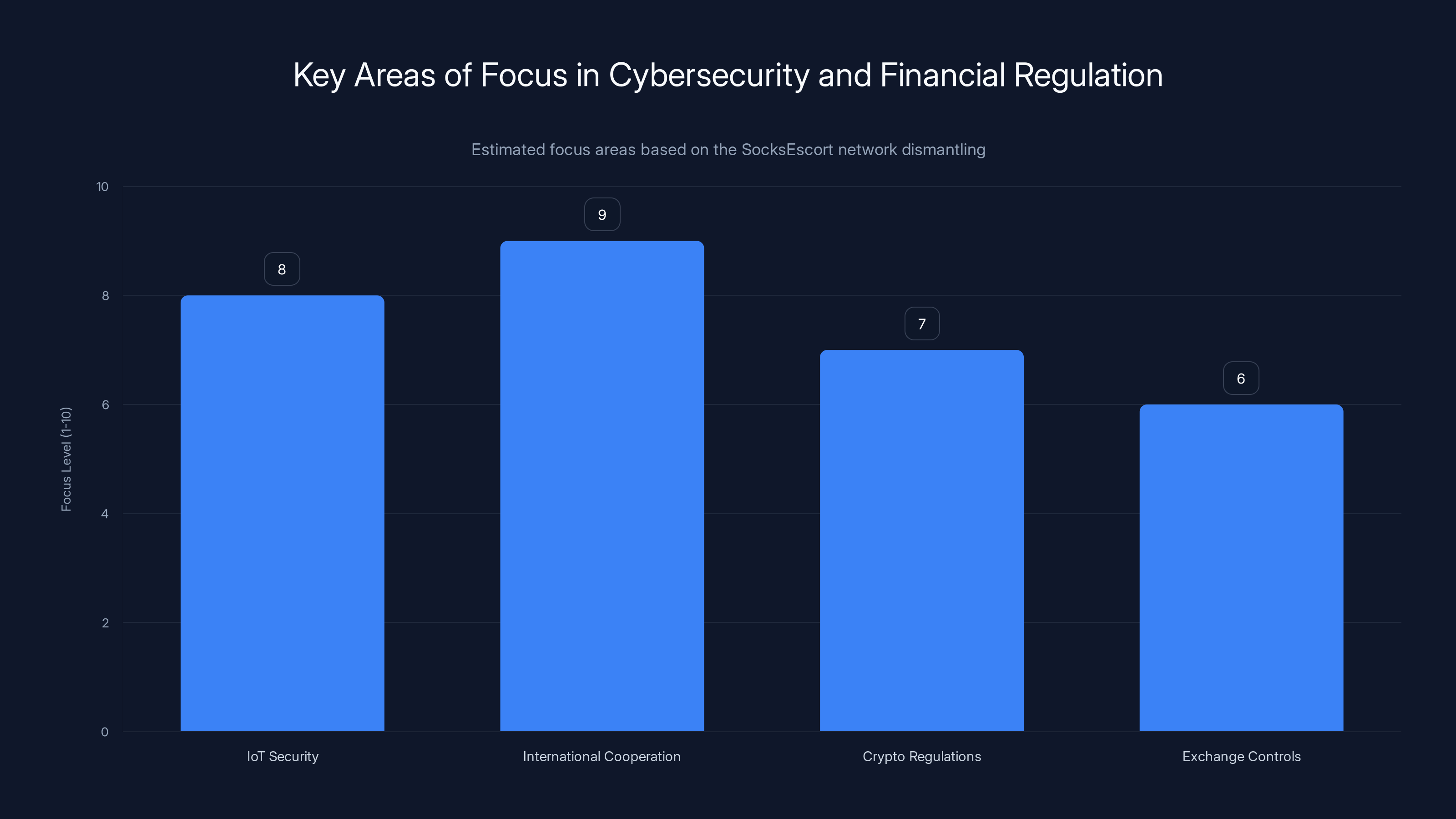
The dismantling of SocksEscort emphasizes enhanced IoT security, international cooperation, and stricter crypto regulations. Estimated data.
Technical and Financial Implications
The dismantling of the Socks Escort network has broader implications for both cybersecurity practices and financial regulations pertaining to cryptocurrencies.
Cybersecurity Lessons
Enhanced Vigilance: The operation highlights the need for improved security practices, particularly for IoT devices, which are often overlooked in security audits.
International Cooperation: Successful takedowns require collaboration across borders, illustrating the importance of international partnerships in cybersecurity.
Financial and Regulatory Impact
The seizure of cryptocurrency assets underscores the need for robust regulations in the crypto space to prevent its use in illicit activities. This operation may prompt regulatory bodies to tighten controls on cryptocurrency exchanges and transactions, as discussed by MEXC.
Best Practices for Mitigating IoT Threats
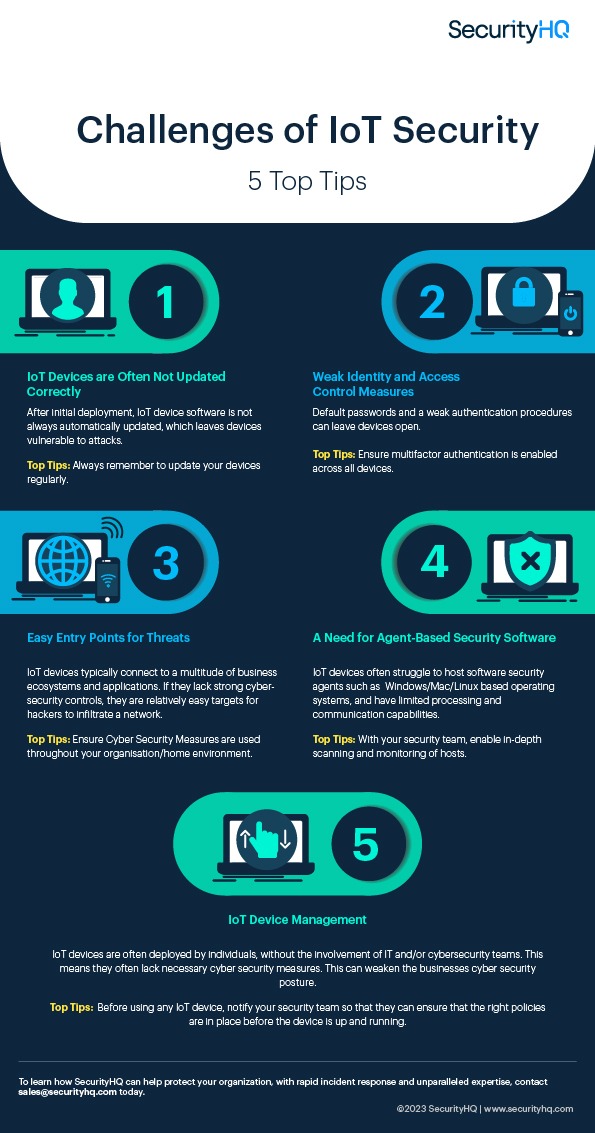
As IoT devices become increasingly prevalent, the need for robust security measures is more critical than ever. Here are some best practices for securing these devices:
- Regular Firmware Updates: Ensure all devices are running the latest firmware to protect against known vulnerabilities.
- Strong Authentication: Use complex passwords and enable two-factor authentication where possible.
- Network Segmentation: Isolate IoT devices on a separate network to contain potential breaches.
- Monitoring and Alerts: Implement monitoring tools to detect unusual patterns indicative of a compromise.
Common Pitfalls and Solutions
Despite best efforts, there are common pitfalls that organizations may encounter when securing IoT devices.
Pitfall: Lack of Awareness
Many users are unaware of the security risks associated with IoT devices, leading to poor security practices.
Solution: Conduct regular training sessions to educate users on the importance of IoT security and the steps they can take to protect their devices.
Pitfall: Inadequate Device Management
With the proliferation of IoT devices, managing them effectively becomes a challenge.
Solution: Deploy device management solutions that provide visibility and control over all IoT devices connected to the network.
Future Trends in Cybersecurity
As technology continues to evolve, so too do the methods employed by cybercriminals. Here are some trends to watch in the realm of cybersecurity.
Rise of AI-driven Attacks
Cybercriminals are increasingly using AI to automate and enhance their attacks, making them more sophisticated and harder to detect.
Enhanced Cyber Defense Mechanisms
To counteract the rise in sophisticated attacks, cybersecurity solutions are incorporating AI and machine learning to improve threat detection and response times.

Recommendations for Organizations
Organizations must stay ahead of cyber threats by adopting proactive security measures. Here are some recommendations:
- Invest in Advanced Threat Detection: Utilize AI-driven solutions to enhance threat detection capabilities.
- Strengthen Incident Response Plans: Regularly test and update incident response plans to ensure readiness in the event of a breach.
- Engage in Information Sharing: Participate in industry forums to share threat intelligence and collaborate on defense strategies.

Conclusion
The takedown of the Socks Escort proxy network marks a significant victory in the fight against cybercrime. However, it also serves as a stark reminder of the vulnerabilities that persist in our digital landscape. By embracing proactive security measures and fostering international cooperation, we can better protect our networks and devices from future threats.
FAQ
What was the Socks Escort proxy network?
The Socks Escort network was a malicious proxy network that used compromised IoT devices to route internet traffic, masking illegal activities.
How did the Socks Escort network operate?
It leveraged Linux malware to infiltrate IoT devices, turning them into part of a botnet that routed traffic through legitimate IP addresses.
What is Operation Lightning?
Operation Lightning was an international law enforcement effort led by the FBI to dismantle the Socks Escort network by seizing its infrastructure and financial assets.
How can IoT devices be secured?
Secure IoT devices by regularly updating firmware, using strong authentication, segmenting networks, and monitoring for unusual activity.
What are the implications of this takedown?
The takedown highlights the need for enhanced IoT security and international cooperation in combating cybercrime.
What are future trends in cybersecurity?
Expect an increase in AI-driven attacks and enhanced defense mechanisms incorporating AI and machine learning.

Key Takeaways
- Operation Lightning dismantled a major proxy network using compromised IoT devices.
- The network exploited Linux malware, highlighting IoT vulnerabilities.
- Seizure of $3.5 million in crypto emphasizes the financial scale of cybercrime.
- Global cooperation is crucial in tackling complex cyber threats.
- Organizations must adopt proactive security measures to protect IoT devices.
Related Articles
- Telus Digital's Massive Data Breach: An In-Depth Look [2025]
- The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]
- FBI Investigation: Malware Hidden in Steam Games [2025]
- Rocket Report: The Demand for Missile Interceptors and Artemis II's Bright Future [2025]
- Asus RT-BE92U: Unleashing the Power of Tri-Band Wi-Fi 7 for the Modern Home [2025]
- How Truecaller's New Feature Arms Families Against Scammers [2025]
![SocksEscort Proxy Network Takedown: A Deep Dive [2025]](https://tryrunable.com/blog/socksescort-proxy-network-takedown-a-deep-dive-2025/image-1-1773416124550.jpg)



