Telus Digital's Massive Data Breach: An In-Depth Look [2025]
Telus Digital, a major player in the Canadian technology and outsourcing sector, has recently confirmed a massive data breach that has sent ripples through the tech industry. The breach, allegedly perpetrated by the hacker group Shiny Hunters, resulted in the theft of nearly 1 petabyte of sensitive data. This article delves into the details of the breach, explores the implications for the industry, and provides insights into improving cybersecurity practices to prevent such incidents in the future.
TL; DR
- Massive Breach: Hackers allegedly stole nearly 1 petabyte of data from Telus Digital, as reported by Bleeping Computer.
- Shiny Hunters: This group claimed responsibility and attempted to extort $65 million according to TechRadar.
- Data Exposure: Sensitive customer information was compromised.
- Investigation Ongoing: Telus is working with law enforcement to investigate the breach.
- Cybersecurity Lessons: Highlights the importance of strong security measures and incident response plans.

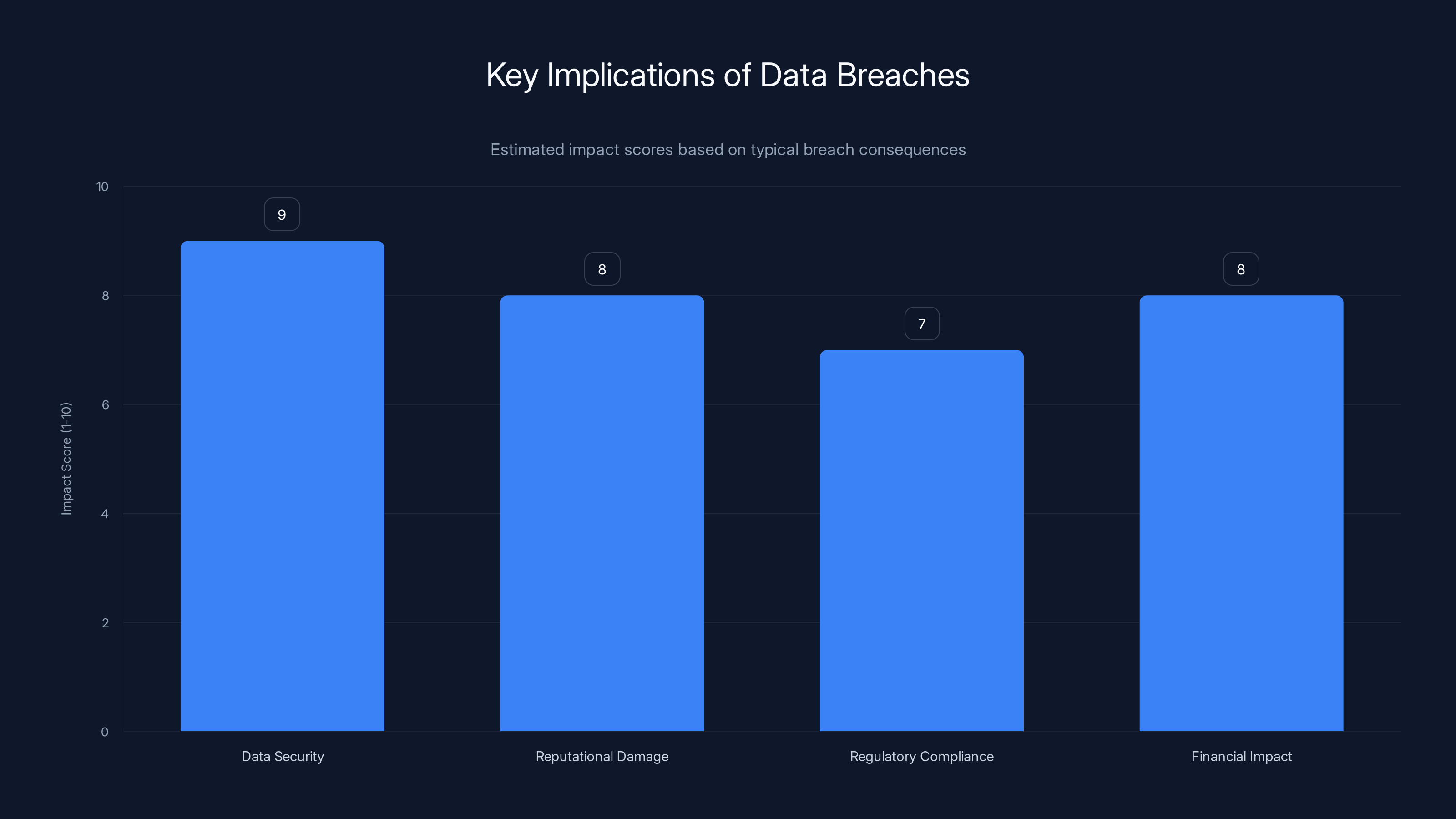
Data breaches significantly impact data security, reputation, compliance, and finances. Estimated data based on typical breach outcomes.
Understanding the Breach
In early 2026, whispers of a significant cybersecurity incident involving Telus Digital began circulating. Initially shrouded in mystery, the breach was later confirmed by the company, revealing that nearly 1 petabyte of data had been exfiltrated by the notorious hacker group, Shiny Hunters. For context, a petabyte is equivalent to 1,000 terabytes or about 1 million gigabytes. This staggering amount of data could include anything from sensitive customer information to proprietary company data.
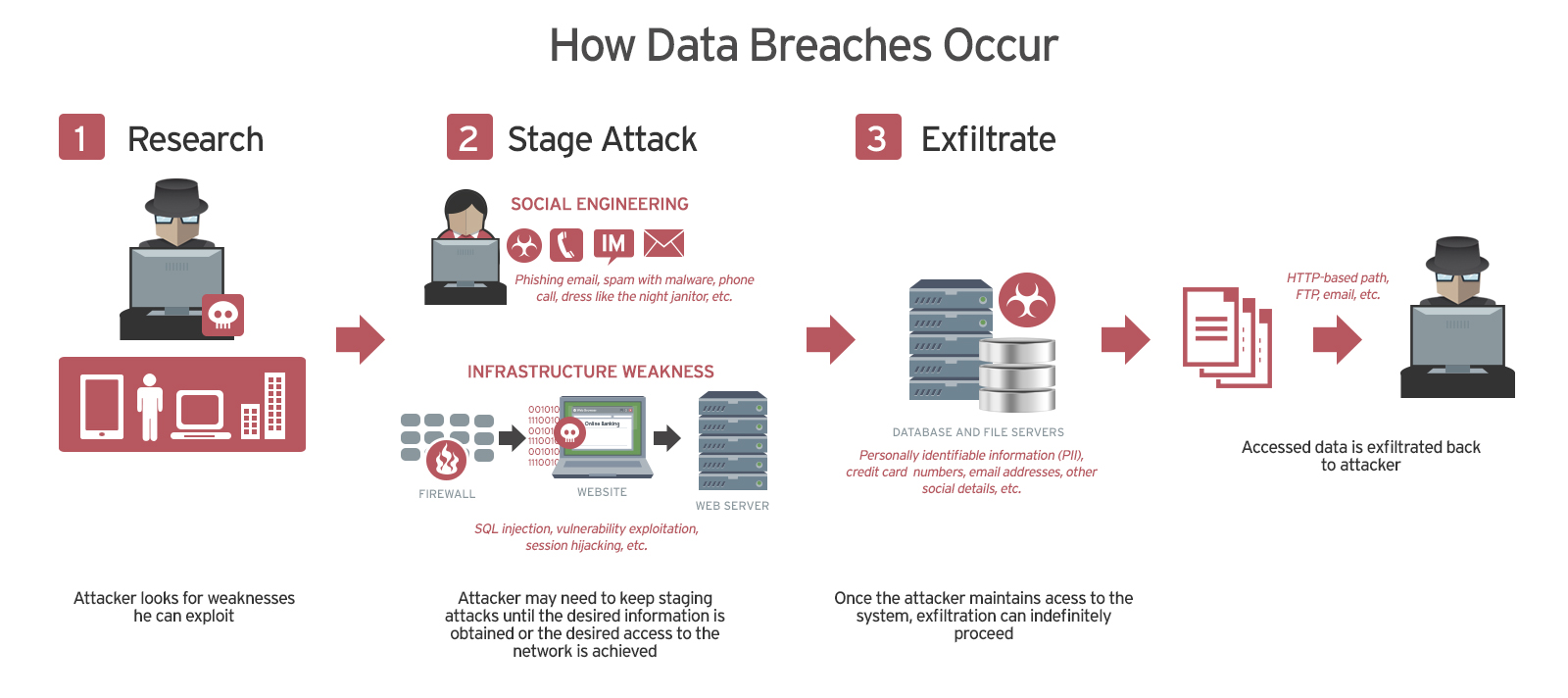
How the Breach Occurred
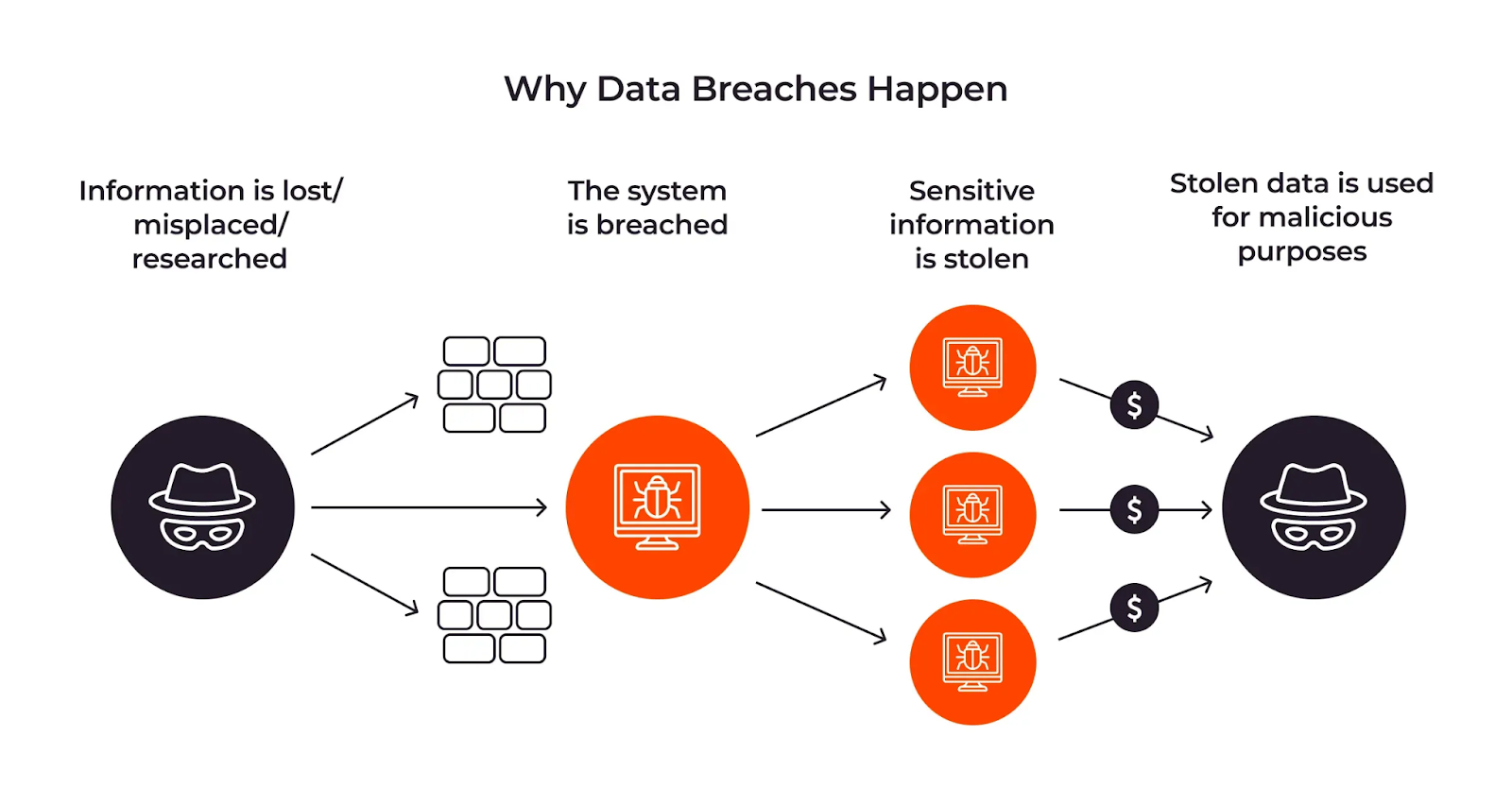
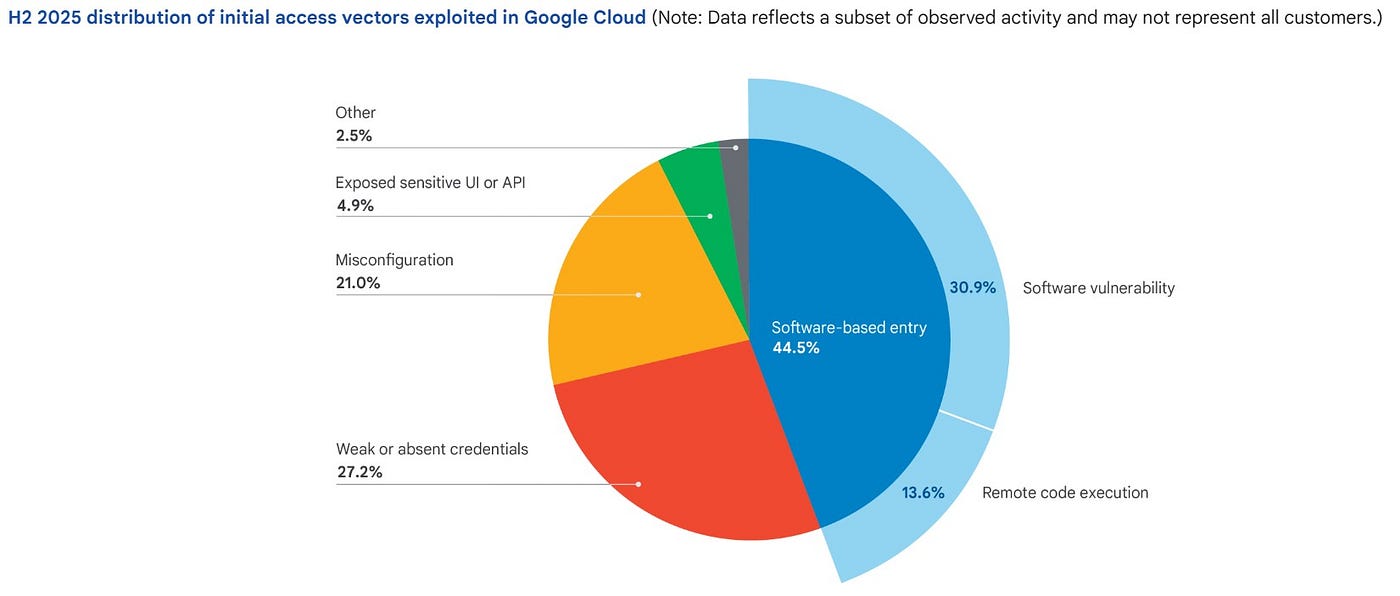
The breach reportedly involved the compromise of Google Cloud Platform (GCP) credentials, which allowed the hackers to siphon off a vast amount of data. Cloud services, while offering scalability and convenience, also introduce new security challenges. Misconfigured cloud settings, weak authentication mechanisms, or inadequate access controls can become entry points for malicious actors, as noted by Wiz.
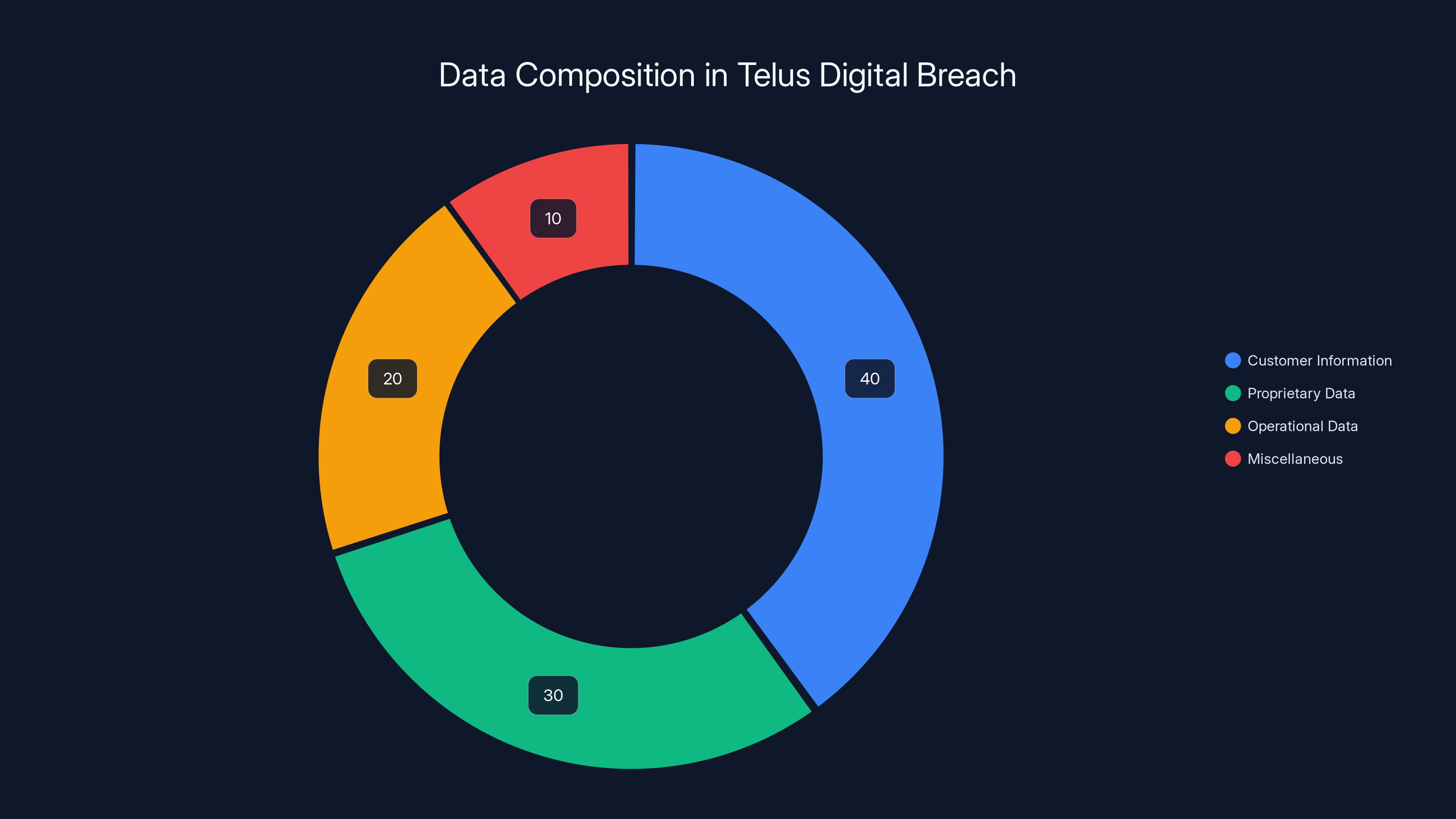
Estimated data composition from the Telus Digital breach shows a significant portion of customer information was compromised, highlighting the critical need for robust cloud security measures.
The Shiny Hunters: A Notorious Hacker Group
Shiny Hunters have been linked to multiple high-profile data breaches, targeting various organizations worldwide. Known for their aggressive tactics, they typically steal large volumes of data and demand hefty ransoms. In the case of Telus Digital, they attempted to extort $65 million in exchange for not releasing the stolen data, as detailed by Bleeping Computer.
The Modus Operandi
Shiny Hunters often exploit vulnerabilities in widely-used platforms, gaining unauthorized access through phishing attacks, exploiting zero-day vulnerabilities, or leveraging weak passwords. Once inside, they move laterally across the network to access critical data stores.
Implications of the Breach
The Telus Digital breach underscores several critical issues facing organizations today:
- Data Security: Companies must prioritize the protection of sensitive data, ensuring that robust encryption, access controls, and monitoring systems are in place.
- Reputational Damage: Breaches can severely damage a company's reputation, eroding customer trust and potentially leading to financial losses, as highlighted in a Wealth Management article.
- Regulatory Compliance: With data protection regulations becoming increasingly stringent, organizations must ensure compliance to avoid hefty fines.
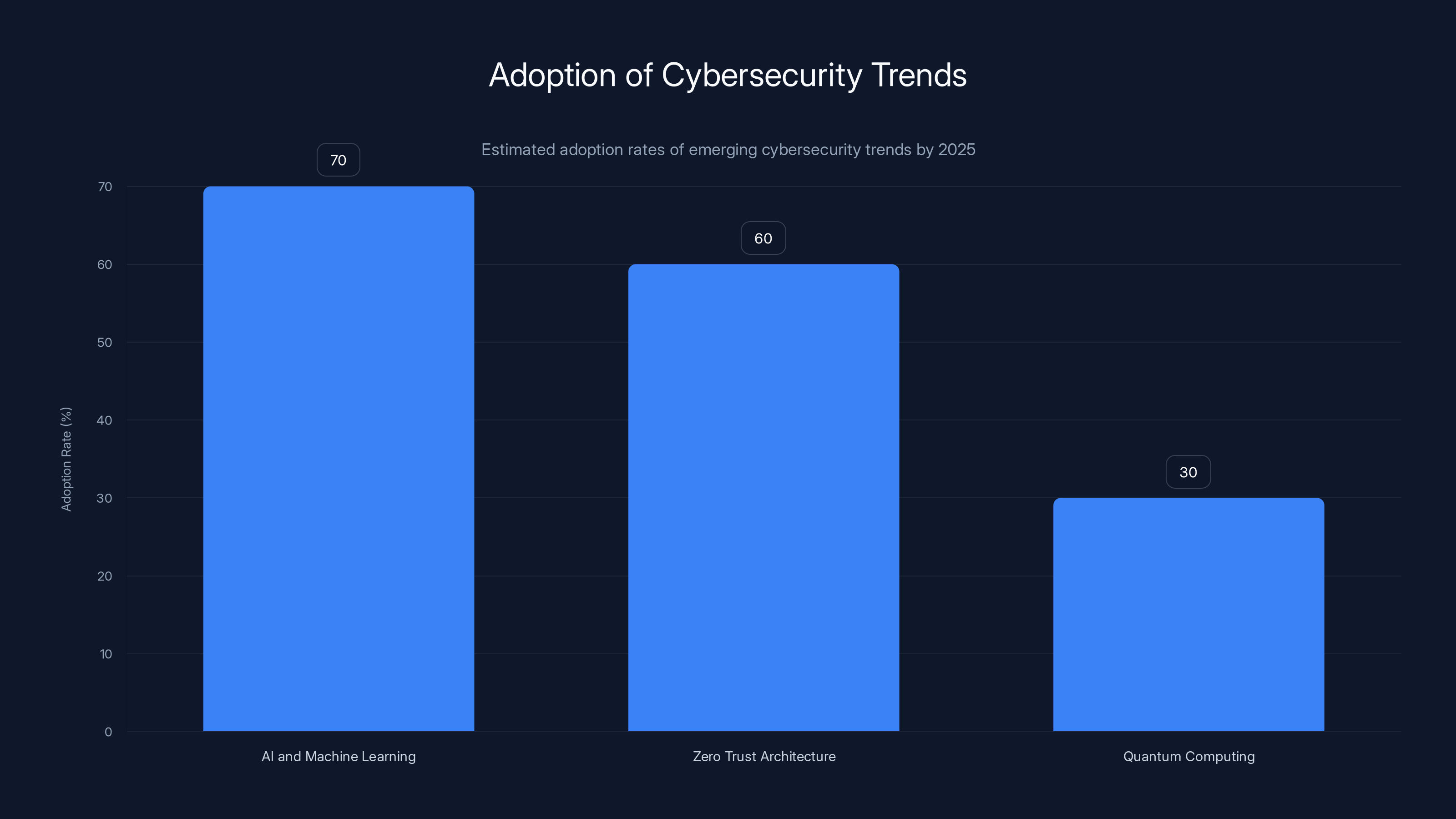
AI and Machine Learning are expected to have the highest adoption rate among emerging cybersecurity trends by 2025, followed by Zero Trust Architecture. Quantum Computing, while promising, is projected to have a lower adoption rate due to its nascent stage. (Estimated data)
Strengthening Cybersecurity Posture
In light of the Telus Digital breach, organizations should reassess their cybersecurity strategies. Here are some best practices to consider:
- Implement Multi-Factor Authentication (MFA): Requiring multiple forms of verification can significantly reduce the risk of unauthorized access.
- Regular Security Audits: Conducting regular security assessments can help identify vulnerabilities before they are exploited.
- Employee Training: Educating employees about phishing attacks and security best practices can create a more security-conscious workforce.
Common Pitfalls and Solutions
- Pitfall: Relying solely on passwords for authentication.
- Solution: Implement MFA to add an extra layer of security.
- Pitfall: Infrequent security updates.
- Solution: Automate updates and patches to ensure systems are always protected against the latest threats.
- Pitfall: Lack of incident response planning.
- Solution: Develop and regularly test incident response plans to ensure swift and effective action in the event of a breach.
Future Trends in Cybersecurity
As cyber threats evolve, so too must the strategies to combat them. Here are some trends to watch:
- AI and Machine Learning: These technologies are increasingly being used to detect and respond to threats in real-time, offering a more proactive approach to cybersecurity.
- Zero Trust Architecture: This security model, which assumes that threats can come from both outside and inside the network, is gaining traction as organizations look to bolster their defenses.
- Quantum Computing: While still in its infancy, quantum computing has the potential to revolutionize encryption and security protocols, requiring organizations to stay ahead of the curve.
Case Study: A Real-World Example
Consider a hypothetical organization, XYZ Corp., which faced a similar breach scenario. XYZ Corp. had neglected regular security audits, leaving outdated systems vulnerable. When they experienced a breach, they lacked a well-defined incident response plan, leading to delays in containing the attack and notifying affected customers.
Lessons Learned
- Proactive Security Measures: XYZ Corp. learned the importance of regular security audits and timely updates.
- Incident Response Planning: The breach highlighted the need for a comprehensive incident response plan, enabling quicker action and minimizing damage.
Conclusion
The Telus Digital breach serves as a stark reminder of the ever-present threat posed by cybercriminals. As organizations continue to adopt digital technologies, they must remain vigilant and proactive in their cybersecurity efforts. By implementing robust security measures, conducting regular audits, and staying informed about emerging threats, companies can better protect themselves and their customers from future breaches.
FAQ
What is a data breach?
A data breach is an incident where unauthorized individuals gain access to sensitive, protected, or confidential data, often leading to data theft or exposure.
How does multi-factor authentication work?
Multi-factor authentication requires users to provide two or more verification factors to gain access to a resource, such as a password and a code sent to their phone.
What are the benefits of a zero trust architecture?
Zero trust architecture enhances security by assuming that threats can exist both inside and outside the network, requiring strict verification for every access request.
How can organizations improve their incident response plans?
Organizations can improve their incident response plans by conducting regular drills, updating protocols based on new threats, and ensuring clear communication channels during an incident.
What role does AI play in cybersecurity?
AI can analyze large volumes of data to detect anomalies and potential threats in real-time, allowing for quicker and more effective responses to cybersecurity incidents.
How can companies protect customer data?
Companies can protect customer data by implementing strong encryption, access controls, and regular security audits to identify and mitigate vulnerabilities.
Why is employee training important in cybersecurity?
Employee training is crucial because human error is a common factor in security breaches. Educating employees on best practices can reduce the risk of accidental data exposure.
What should companies do after experiencing a data breach?
After a data breach, companies should follow their incident response plan, notify affected parties, investigate the breach thoroughly, and implement measures to prevent future incidents.
Key Takeaways
- Hackers allegedly stole nearly 1 petabyte of data from Telus Digital, as reported by Bleeping Computer.
- The breach was claimed by the hacker group ShinyHunters.
- Telus is investigating the breach with law enforcement.
- Companies must implement strong cybersecurity measures to protect data.
- Multi-factor authentication and regular audits can mitigate breach risks.
- AI and zero trust architecture are key trends in cybersecurity.
- Employee training is essential to reduce human error in security breaches.
- A well-defined incident response plan is critical for effective breach management.
Related Articles
- Understanding Cybersecurity Threats: Lessons from the Stryker Cyberattack [2025]
- The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]
- Google Acquires Wiz for $32 Billion: A Deep Dive into the Future of Cloud Security [2025]
- How Truecaller's New Feature Arms Families Against Scammers [2025]
- How ‘Handala’ Became the Face of Iran’s Hacker Counterattacks | WIRED
- Understanding WordPress Plugin Vulnerabilities: Protect Your Site [2025]
![Telus Digital's Massive Data Breach: An In-Depth Look [2025]](https://tryrunable.com/blog/telus-digital-s-massive-data-breach-an-in-depth-look-2025/image-1-1773412655149.jpg)



