The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]
Introduction
Last month, Stryker, a leading multinational medical device manufacturer, found itself at the center of a large-scale cyberattack. This incident not only disrupted their Windows network but also served as a wake-up call for organizations worldwide. In this comprehensive exploration, we'll dive into the attack's anatomy, its ramifications, and how businesses can safeguard against similar threats.

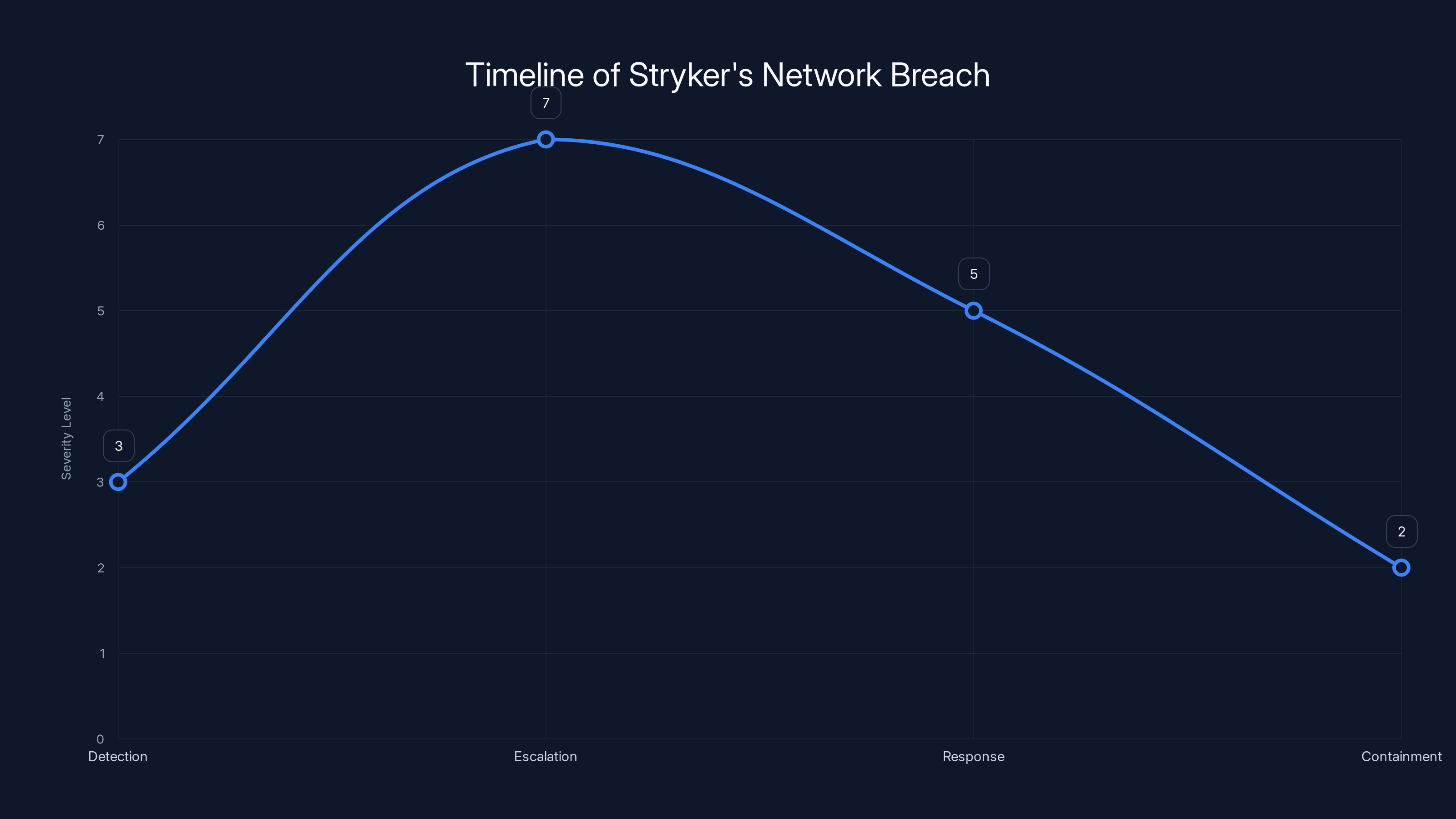
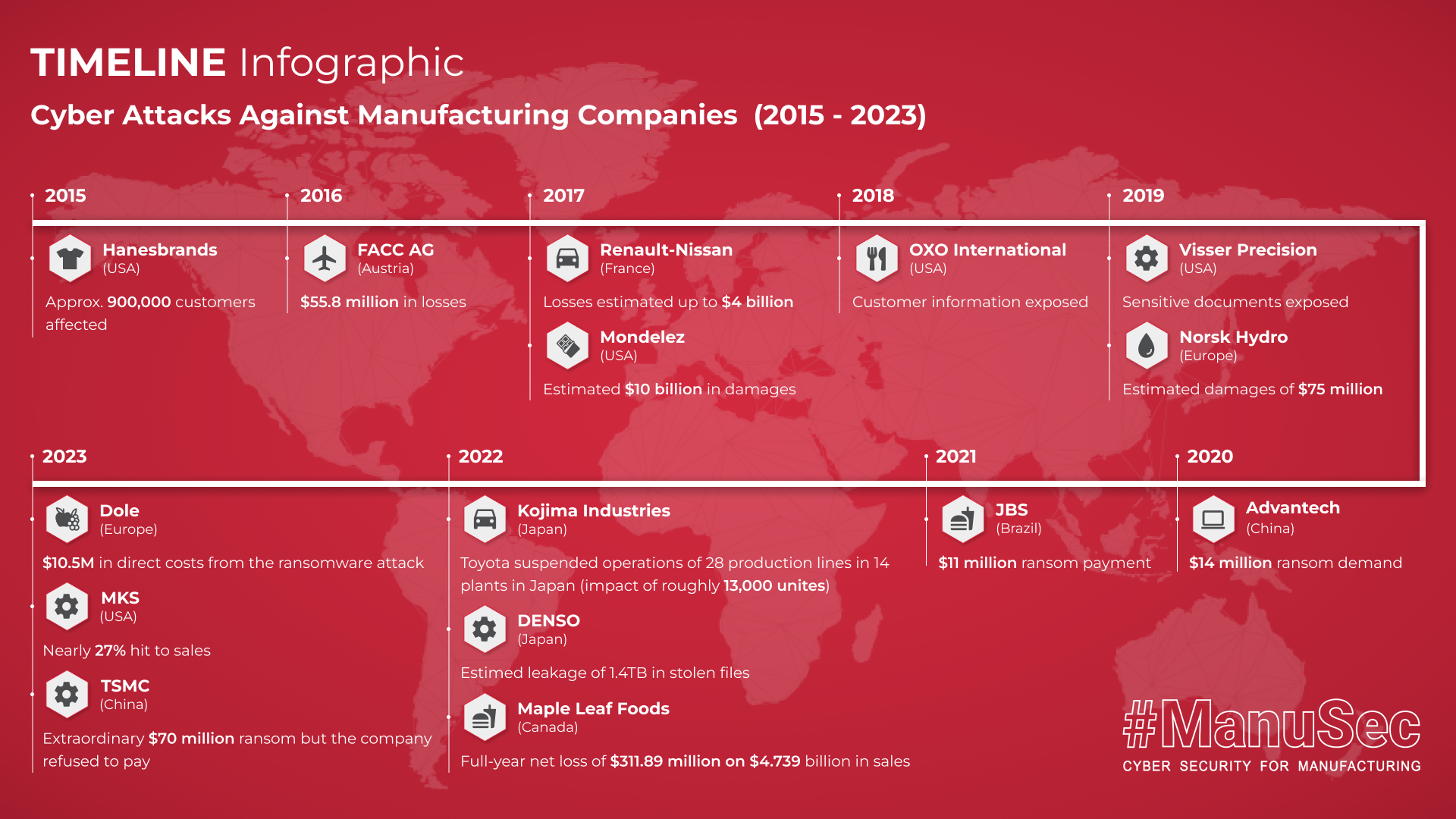
The timeline illustrates the escalation and containment of the attack, with severity peaking during system unresponsiveness. Estimated data based on typical attack progression.
TL; DR
- Immediate Impact: The attack crippled Stryker's Windows network, halting operations. According to The Wall Street Journal, the attack was suspected to be linked to Iranian interests.
- Attribution: A group linked to Iranian interests claimed responsibility. This was reported by The Record.
- Attack Vector: Initial indications suggest a sophisticated phishing campaign. Simplilearn explains that phishing is a common method used in such attacks.
- Current Status: Stryker is gradually restoring its network, with no ransomware detected, as noted by MedTech Dive.
- Future Recommendations: Enhanced cybersecurity measures are vital for prevention.
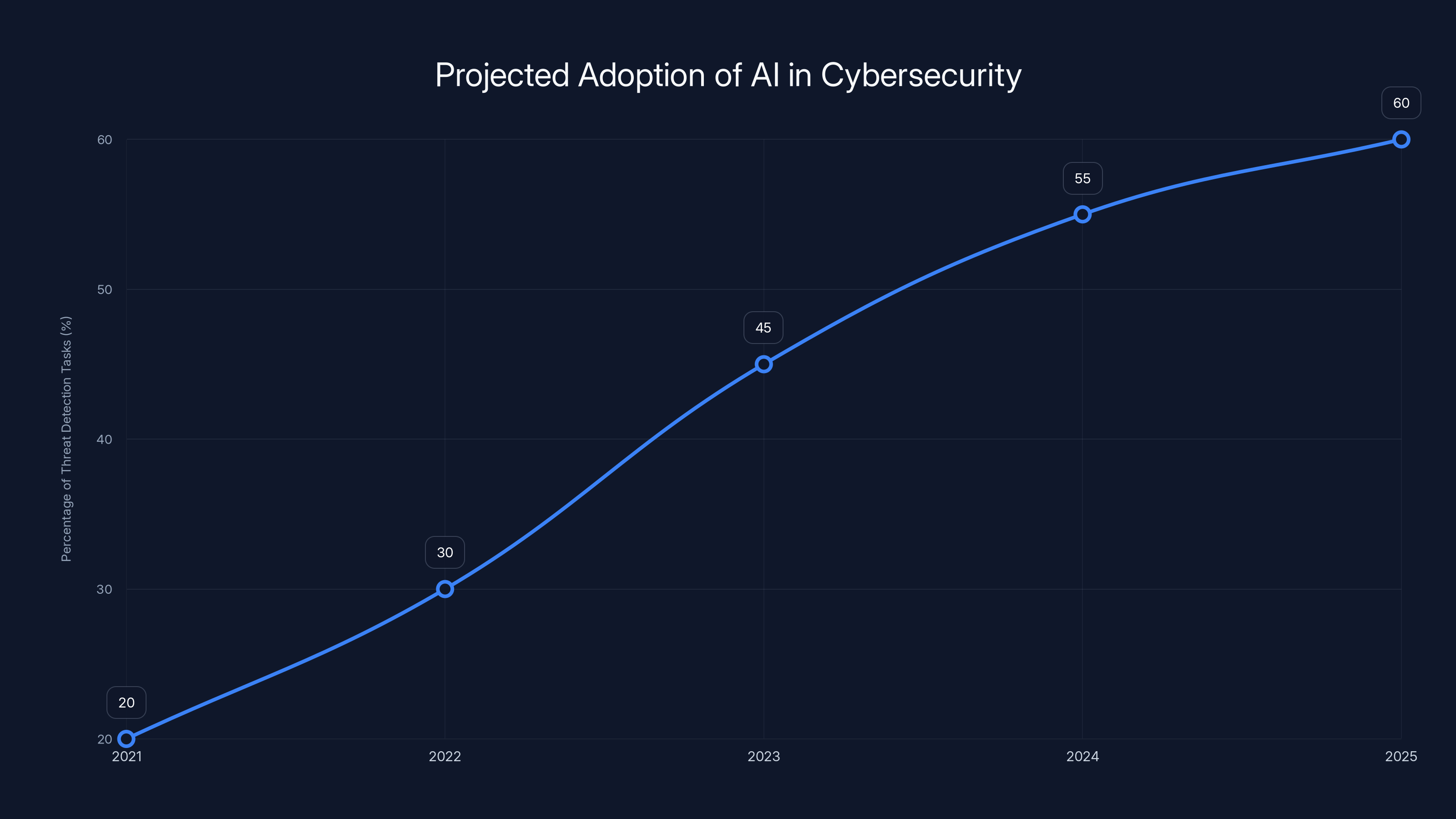
AI-driven security systems are projected to handle over 60% of threat detection tasks by 2025, indicating a significant shift towards AI in cybersecurity. Estimated data.
The Attack: What Happened?
On a seemingly ordinary day, Stryker's IT team detected unusual activity within their network. It quickly escalated into a full-blown crisis, with systems becoming inaccessible and operations grinding to a halt. While initial reports speculated about ransomware, Stryker clarified that there was no evidence supporting this claim, as reported by Irish Examiner.
Understanding the Attack Vector
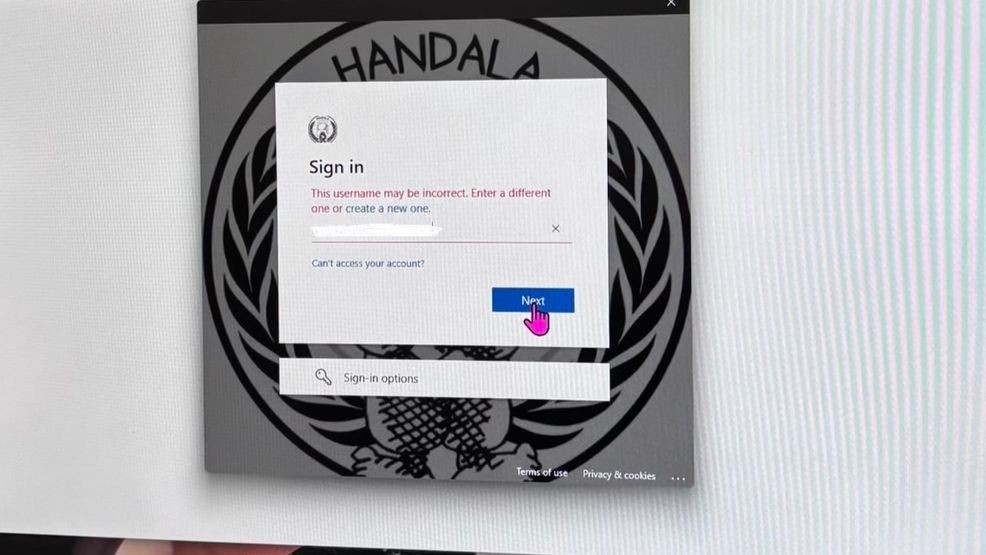
The attackers likely leveraged a phishing campaign, a common method for infiltrating networks. These campaigns often involve deceptive emails appearing to come from trusted sources, tricking employees into revealing credentials or downloading malware. Checkpoint highlights the increasing sophistication of phishing attacks in the age of AI.
A Timeline of the Attack
- Detection: Initial signs of the breach were observed through abnormal network traffic.
- Escalation: Systems across the Windows environment became unresponsive.
- Response: Emergency protocols were enacted, and cybersecurity teams were mobilized.
- Containment: Efforts focused on isolating the affected systems to prevent further spread.

Who Was Behind the Attack?
The cyberattack was attributed to a hacking group associated with Iranian interests. These groups are known for their complex and persistent attack strategies, often targeting industries critical to the economy or national security, as detailed by Krebs on Security.
Motives and Objectives
The motives behind such attacks can vary. In this case, the timing and target suggest a retaliatory measure following geopolitical tensions. Economic disruption and espionage are common objectives, aiming to undermine a company's operations or steal proprietary information, as reported by Bloomberg.


Implementing multi-factor authentication and regular employee training are among the most effective cybersecurity measures. Estimated data based on common practices.
The Aftermath: Current Status and Recovery Efforts
Stryker's Response
Stryker's immediate focus was on containing the breach and beginning recovery. The company worked closely with cybersecurity experts to assess the full scope of the attack and restore services, as noted by International Business Times.
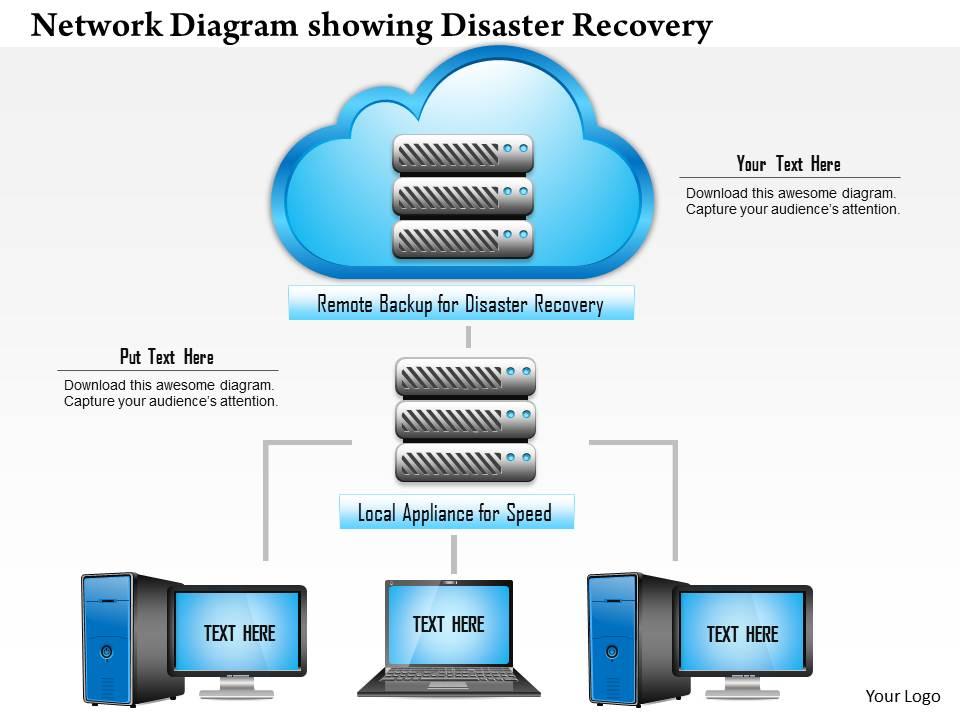
- Network Restoration: Gradual restoration of services was prioritized, starting with critical systems.
- Security Enhancements: New security protocols and monitoring systems were implemented to detect future threats.
Challenges in Restoration
Restoring a network post-attack is fraught with challenges. From ensuring data integrity to rebuilding trust with stakeholders, the process is complex and often lengthy. Cybersecurity Ventures emphasizes the importance of robust recovery plans in the face of increasing cyber threats.
Lessons Learned: Strengthening Cybersecurity
Best Practices for Organizations
- Employee Training: Regular training sessions can help employees recognize and avoid phishing attempts.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security, making unauthorized access more difficult.
- Incident Response Plan: Having a predefined plan allows for quicker, more organized responses to breaches.
Common Pitfalls and How to Avoid Them
- Neglecting Updates: Systems not regularly updated are more vulnerable to attacks.
- Weak Password Policies: Enforcing strong, unique passwords for all accounts is crucial.
- Over-reliance on Technology: While tools are essential, human vigilance is equally important.
Future Trends in Cybersecurity
The Rise of AI in Cyber Defense
Artificial Intelligence is becoming increasingly integral to cybersecurity. From threat detection to incident response, AI tools offer enhanced capabilities that can outpace traditional methods. IBM's X-Force Threat Index highlights the growing role of AI in combating cyber threats.
- Predictive Analysis: AI can analyze patterns to predict potential threats before they occur.
- Automated Responses: Quick, automated responses can mitigate the impact of an attack.
Recommendations for Organizations
- Invest in AI Technologies: Organizations should consider AI tools to enhance their cybersecurity posture.
- Regular Audits: Conduct frequent security audits to identify and address vulnerabilities.
- Stay Informed: Keeping up with the latest cybersecurity trends and threats is essential for proactive defense.
Conclusion
The attack on Stryker's Windows network serves as a stark reminder of the ever-present cyber threats facing organizations today. By understanding the intricacies of such attacks and implementing robust security measures, businesses can better protect themselves against future incidents.
FAQ
What type of attack targeted Stryker?
The attack on Stryker was a sophisticated breach involving a phishing campaign that disrupted their Windows network.
Who was responsible for the attack?
A hacking group with ties to Iranian interests claimed responsibility for the attack on Stryker.
How can organizations prevent similar attacks?
Organizations can prevent similar attacks by employing strong cybersecurity measures such as employee training, multi-factor authentication, and regular system updates.
What are the implications of such attacks?
Cyberattacks can lead to significant operational disruptions, financial losses, and reputational damage for affected organizations.
How important is AI in modern cybersecurity?
AI plays a crucial role in modern cybersecurity by enhancing threat detection and automating incident response to mitigate attack impacts.
What steps should companies take post-attack?
Post-attack, companies should focus on containment, recovery, and implementing new security protocols to prevent future breaches.
Key Takeaways
- Stryker's network was disrupted by a phishing attack attributed to Iranian interests.
- Immediate containment and recovery efforts were prioritized by Stryker.
- Employee training and strong password policies are essential for cybersecurity.
- AI tools enhance threat detection and response capabilities.
- Regular system updates and audits help prevent vulnerabilities.
Related Articles
- Understanding Cybersecurity Threats: Lessons from the Stryker Cyberattack [2025]
- How ‘Handala’ Became the Face of Iran’s Hacker Counterattacks | WIRED
- Asus Routers Hijacked to Power a Cybercrime Proxy Network: What We Know [2025]
- Unmasking BlackSanta: The Malware Targeting HR Departments [2025]
- Meta's New Scam Protection Features: Safeguarding Users in 2025
- Securing 6G Networks: Global Efforts and Future Trends [2025]
![The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]](https://tryrunable.com/blog/the-complex-cyberattack-on-stryker-s-windows-network-unravel/image-1-1773354886278.jpg)



