Understanding the Vercel Hack: Lessons and Best Practices [2025]
Introduction
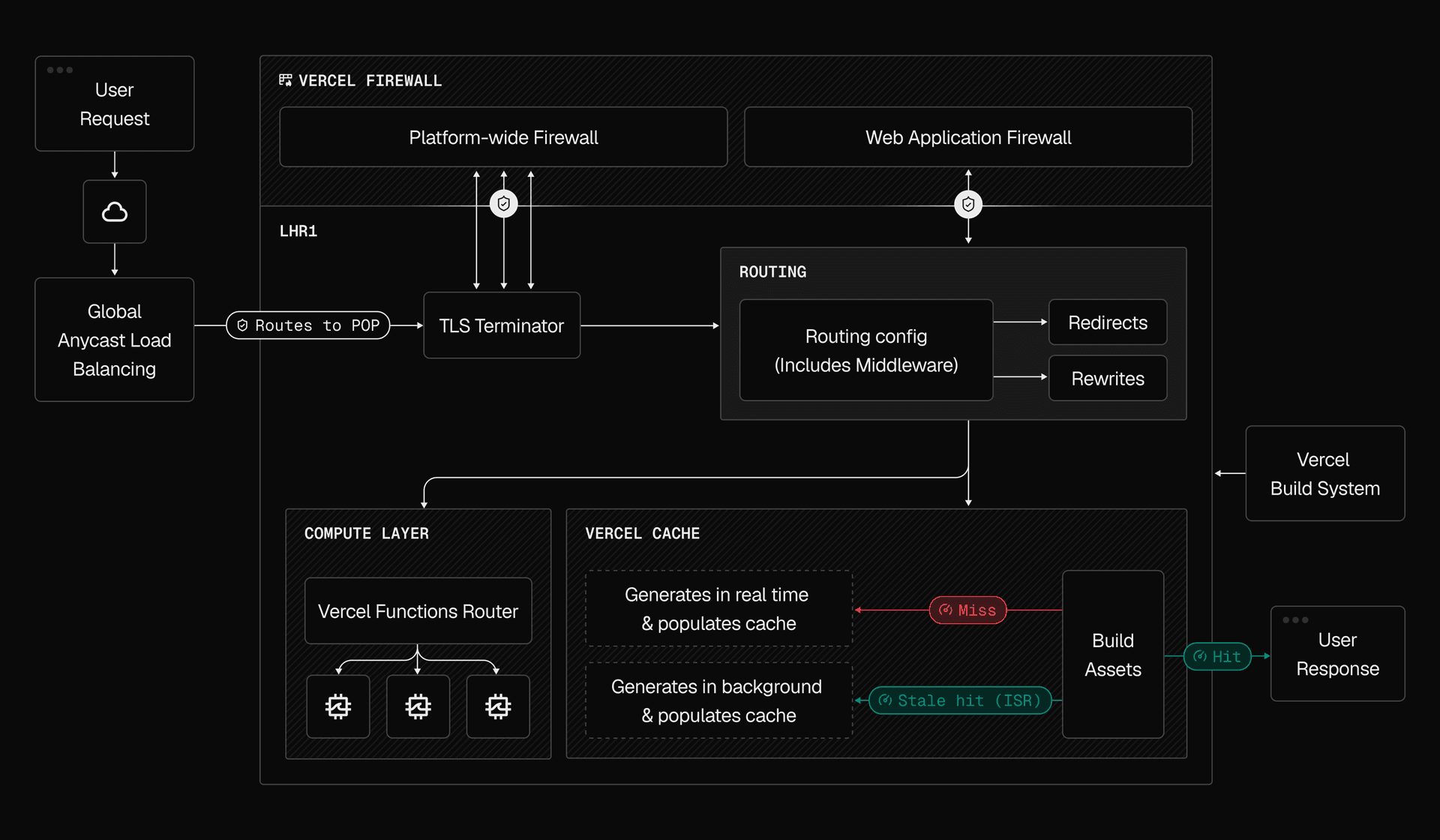
In an unexpected turn of events, the cloud development platform Vercel recently found itself at the center of a cybersecurity breach. As developers and organizations increasingly rely on platforms like Vercel for seamless deployment and hosting of web applications, this incident serves as a wake-up call for all stakeholders in the tech ecosystem. In this comprehensive guide, we’ll delve into the details of the Vercel hack, explore technical nuances, and offer actionable insights to safeguard your development environment.
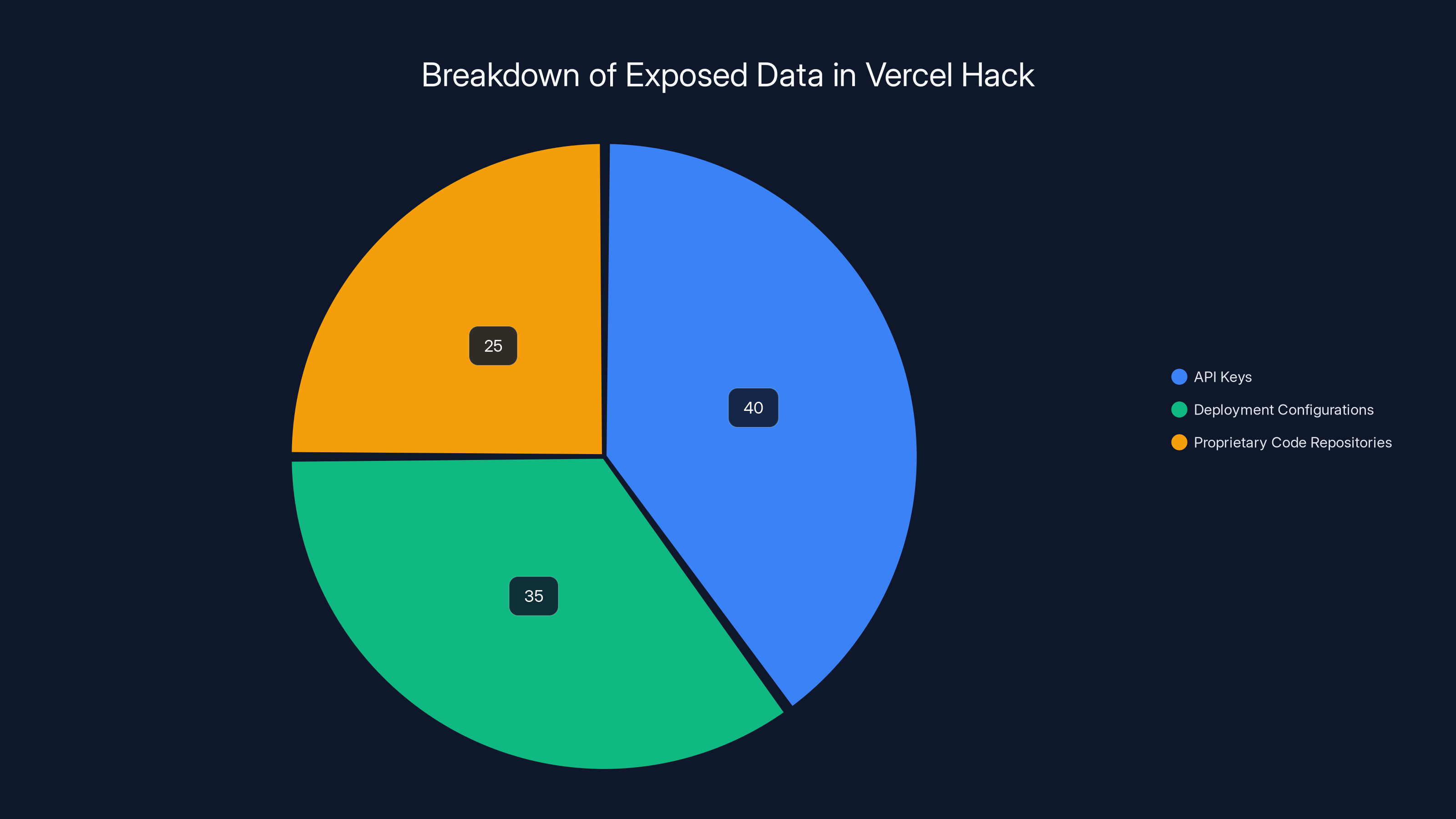
Estimated data suggests API keys were the most exposed, followed by deployment configurations and proprietary code repositories. Estimated data.
TL; DR
- Incident Overview: Vercel experienced a data breach, compromising sensitive user data and system integrity.
- Technical Breakdown: The attack exploited specific vulnerabilities in Vercel's API and authentication mechanisms.
- Security Best Practices: Implement multi-factor authentication and regular security audits to mitigate risks.
- Future Trends: Expect increased focus on zero-trust architecture and enhanced API security.
- Bottom Line: Proactive security measures and user awareness are critical to prevent such breaches.
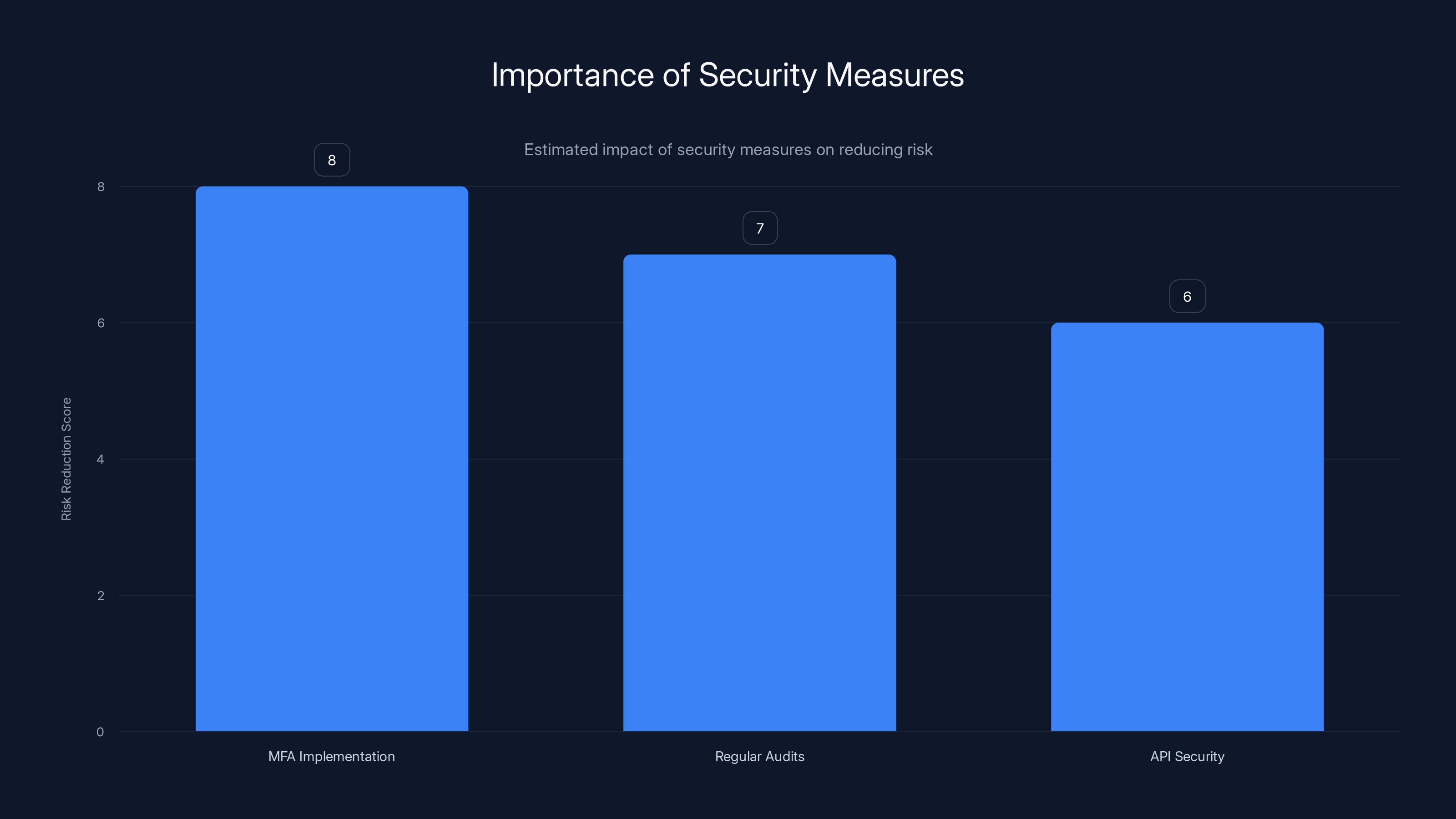
Implementing MFA, conducting regular audits, and enhancing API security can significantly reduce security risks. Estimated data based on typical impact.
The Vercel Hack: What Happened?
On a seemingly ordinary day, Vercel users began noticing unusual activity within their accounts. This was soon identified as a result of a sophisticated cyberattack that had managed to infiltrate Vercel's systems. The breach exposed sensitive user data, including API keys, deployment configurations, and potentially, proprietary code repositories.
How the Attack Unfolded
The attackers utilized a combination of social engineering and technical exploits to gain access to Vercel's internal systems. Initial reports suggest that phishing emails were used to obtain credentials from key personnel, which were then leveraged to bypass standard security protocols.
Once inside, the attackers exploited vulnerabilities in Vercel's API, allowing them to exfiltrate data and manipulate deployment scripts.
Technical Breakdown of the Breach
API Vulnerabilities
The core vulnerability lay within Vercel's API authentication mechanisms. The attackers identified a flaw in the token validation process, which permitted unauthorized access.
javascript// Example of flawed token validation
function validate Token(token) {
if (token.starts With('Bearer ')) {
return true; // Oversimplified check
}
return false;
}
Inadequate Monitoring
Vercel's monitoring systems failed to detect the anomalous behavior in time, highlighting the importance of robust logging and real-time alert systems.
Social Engineering Tactics
The attackers crafted convincing phishing emails, targeting Vercel employees with access to critical infrastructure. This underscores the need for continuous employee training in cybersecurity awareness.

Both setting up MFA on Vercel and conducting a security audit involve four key steps, highlighting the structured approach needed for effective security implementation.
Lessons Learned
Implement Multi-Factor Authentication (MFA)
MFA adds an additional layer of security by requiring users to present two or more verification factors. This simple step can significantly reduce the risk of unauthorized access.
Conduct Regular Security Audits
Regular security audits can help identify vulnerabilities before they are exploited. This includes penetration testing, code reviews, and configuration assessments.
Enhance API Security
Securing your API involves implementing stricter validation protocols and limiting access to critical endpoints.
javascript// Improved token validation
function validate Token(token) {
const token Parts = token.split(' ');
if (token Parts[0] === 'Bearer' && token Parts[1].length > 50) {
return verify Token Signature(token Parts[1]); // Ensure token integrity
}
return false;
}
Common Pitfalls and Solutions
Overlooking Social Engineering Threats
Many organizations underestimate the potency of social engineering attacks. Regular training and simulated phishing exercises can enhance employee vigilance.
Inadequate Incident Response Plans
An ineffective incident response plan can exacerbate the impact of a breach. Ensure your plan is well-documented, rehearsed, and updated regularly.
Neglecting Third-Party Security
Ensure that third-party services integrated with your platform adhere to stringent security standards. Conduct regular reviews and enforce compliance.
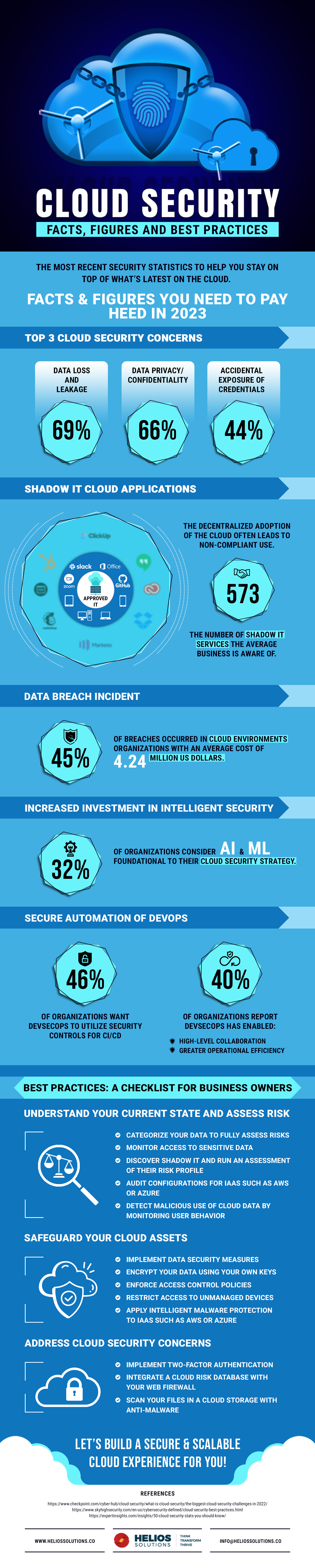
Future Trends in Cloud Security
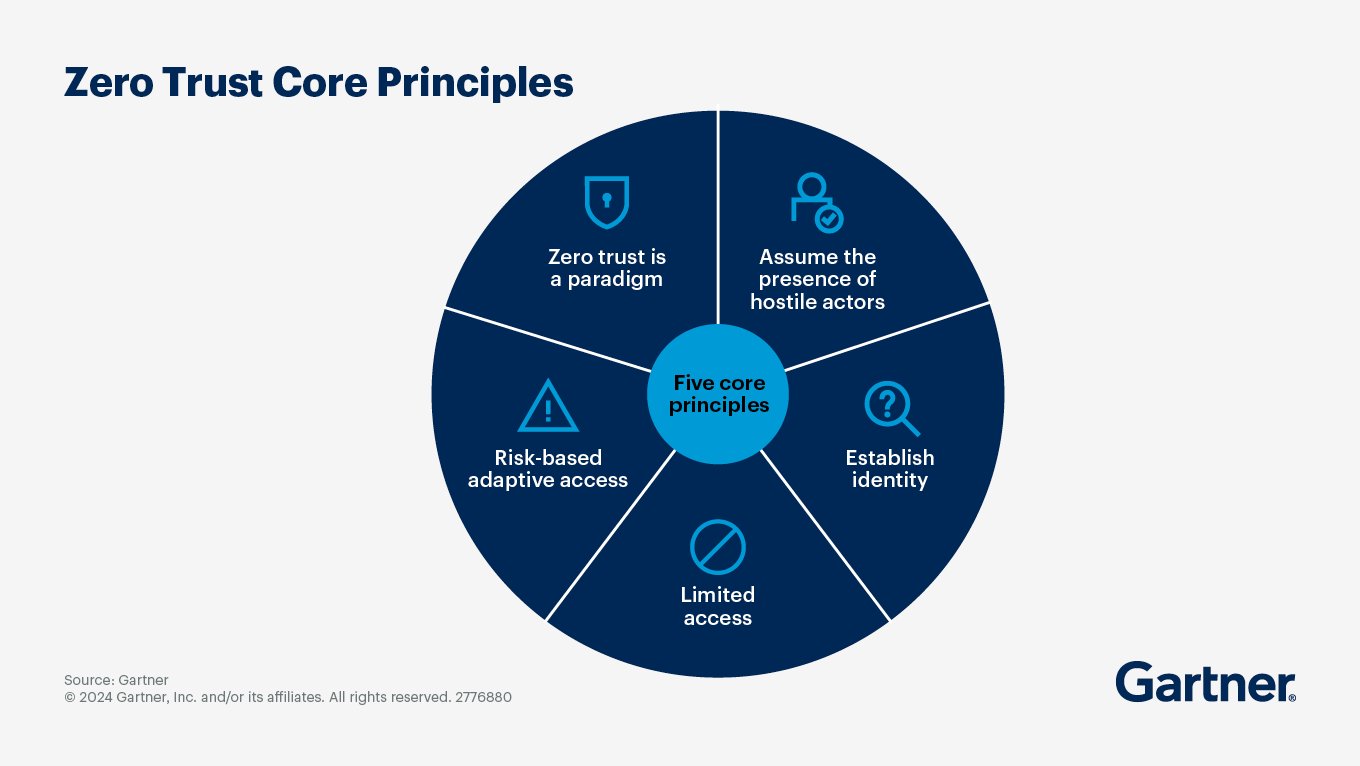
Adoption of Zero-Trust Architecture
Zero-trust architecture is gaining traction as a robust security model. It operates on the principle of "never trust, always verify," ensuring that every access request is thoroughly vetted.
Enhanced Focus on API Security
As APIs become increasingly critical to business operations, securing them will be a top priority. This includes adopting API gateways and implementing rate limiting.
AI-Driven Threat Detection
Artificial intelligence is revolutionizing threat detection, enabling systems to identify and respond to anomalies in real time.
Best Practices for Securing Your Cloud Environment
Strong Authentication Practices
- Implement MFA across all accounts
- Use OAuth 2.0 for secure authorization
- Regularly update authentication protocols
Comprehensive Access Management
- Adopt role-based access control (RBAC)
- Regularly review and update access permissions
- Implement just-in-time access for critical resources
Continuous Monitoring and Alerts
- Deploy real-time monitoring tools
- Set up alerts for suspicious activities
- Conduct regular log reviews
Regular Backups and Disaster Recovery
- Schedule automated backups
- Test disaster recovery plans
- Ensure data integrity and availability
Practical Implementation Guides
Setting Up MFA on Vercel
- Go to your Vercel account settings.
- Navigate to the Security tab.
- Enable Multi-Factor Authentication.
- Follow the setup instructions to link your authenticator app.
Conducting a Security Audit
- Identify critical assets and data.
- Perform a vulnerability assessment.
- Review code and configurations for security flaws.
- Implement remediation strategies for identified risks.
Conclusion
The Vercel hack serves as a stark reminder of the ever-present threats in the digital landscape. By adopting proactive security measures and fostering a culture of awareness, organizations can better protect themselves against similar incidents.
FAQ
What is Vercel?
Vercel is a cloud development platform that enables developers to deploy and host web applications with ease.
How did the Vercel hack occur?
Attackers used a combination of social engineering and API vulnerabilities to gain unauthorized access to Vercel's systems.
What are the consequences of the hack?
The breach exposed sensitive user data and highlighted the need for enhanced security measures within cloud platforms.
How can developers protect their Vercel accounts?
Implement multi-factor authentication, conduct regular security audits, and stay informed about the latest security threats.
What lessons can be learned from the Vercel hack?
The importance of robust authentication, continuous monitoring, and employee training in preventing security breaches.
What are the future trends in cloud security?
Expect a greater focus on zero-trust architecture, enhanced API security, and AI-driven threat detection.
This article provides a comprehensive analysis of the Vercel hack, offering insights into the technical aspects of the breach, best practices for securing cloud environments, and future trends in cybersecurity. By understanding and implementing these strategies, developers and organizations can better safeguard their digital assets.
Key Takeaways
- Vercel's breach highlights vulnerabilities in API authentication methods.
- Multi-factor authentication significantly reduces unauthorized access risks.
- Regular security audits help in identifying and mitigating potential threats.
- Zero-trust architecture will be a key focus for future cloud security.
- AI-driven threat detection is becoming crucial for real-time anomaly identification.
- Effective incident response plans are critical to minimizing breach impacts.
- Continuous employee training in cybersecurity awareness is essential.
- API security enhancements are vital as APIs become central to operations.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Inside Europol's Operation PowerOFF: A Game-Changer in Combating DDoS-for-Hire Services [2025]
- How Fashion Retailers Can Safeguard Customer Data: Lessons from Express's Security Flaw [2025]
- Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
- WordPress Plugin Security Attacks: Safeguarding Your Site [2025]
- Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]
![Understanding the Vercel Hack: Lessons and Best Practices [2025]](https://tryrunable.com/blog/understanding-the-vercel-hack-lessons-and-best-practices-202/image-1-1776629021047.png)



