The Evolution of Dark Web Monitoring: From Google's Exit to Nord VPN’s Latest Innovations [2025]
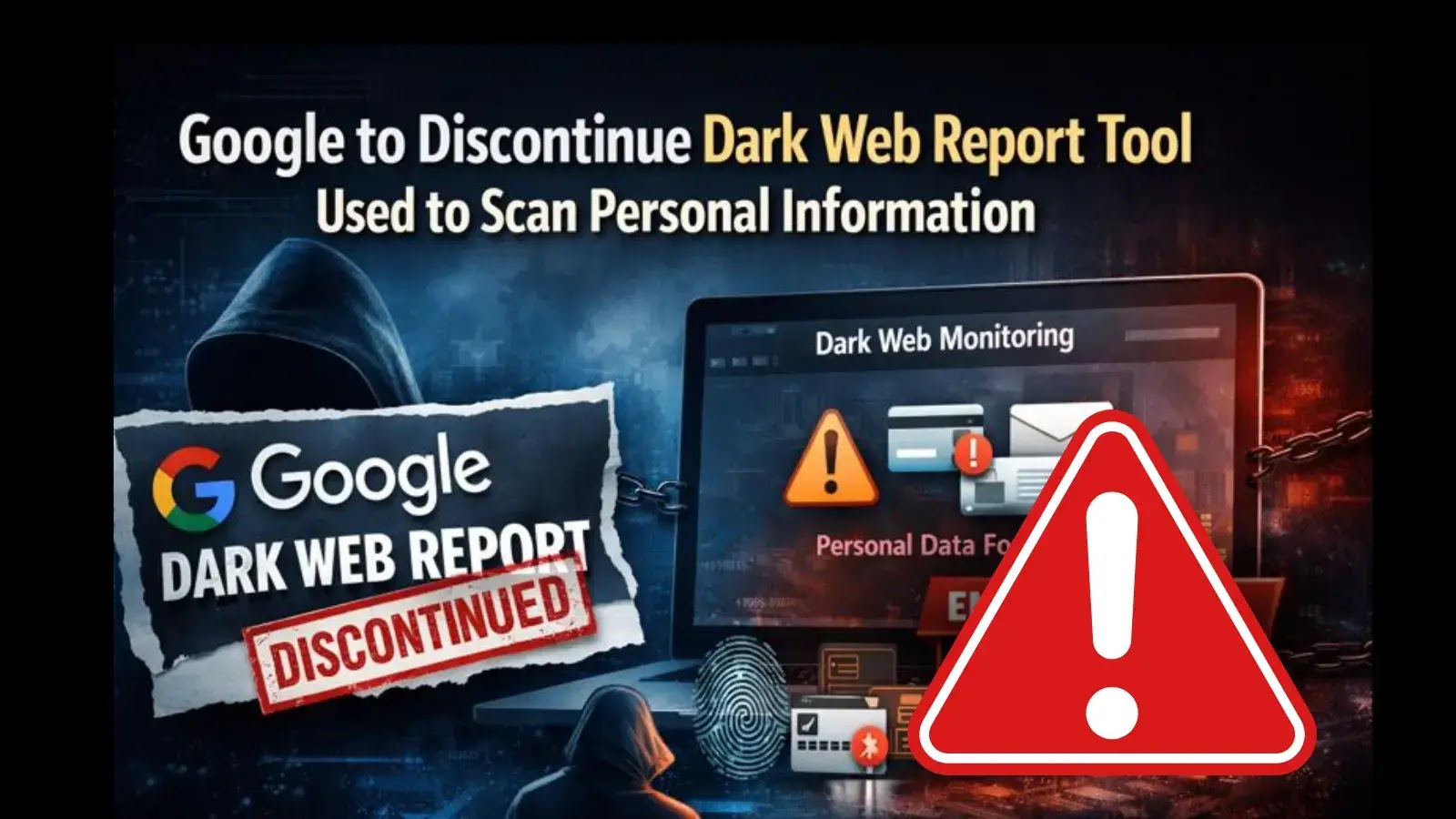
Last month, a startling announcement caught the cybersecurity community off guard: Google quietly discontinued its dark web scanner, a tool that had been part of its arsenal for users to monitor personal data leaks. But as one door closes, another opens. Enter Nord VPN, stepping up with a revamped tool designed to track your leaked data on the dark web. Let's dive into why Google pulled the plug and how Nord VPN is taking the reins.
TL; DR
- Google discontinued its dark web scanner, leaving a gap in the market for data breach detection.
- Nord VPN has launched an upgraded tool to monitor and protect leaked data on the dark web.
- Technical enhancements include real-time alerts and comprehensive data breach reports.
- Common pitfalls in dark web monitoring include false positives and incomplete data.
- Future trends point towards AI-driven predictive analytics in cybersecurity tools.
- Bottom Line: Nord VPN is leading the charge in user-friendly, effective dark web monitoring solutions.
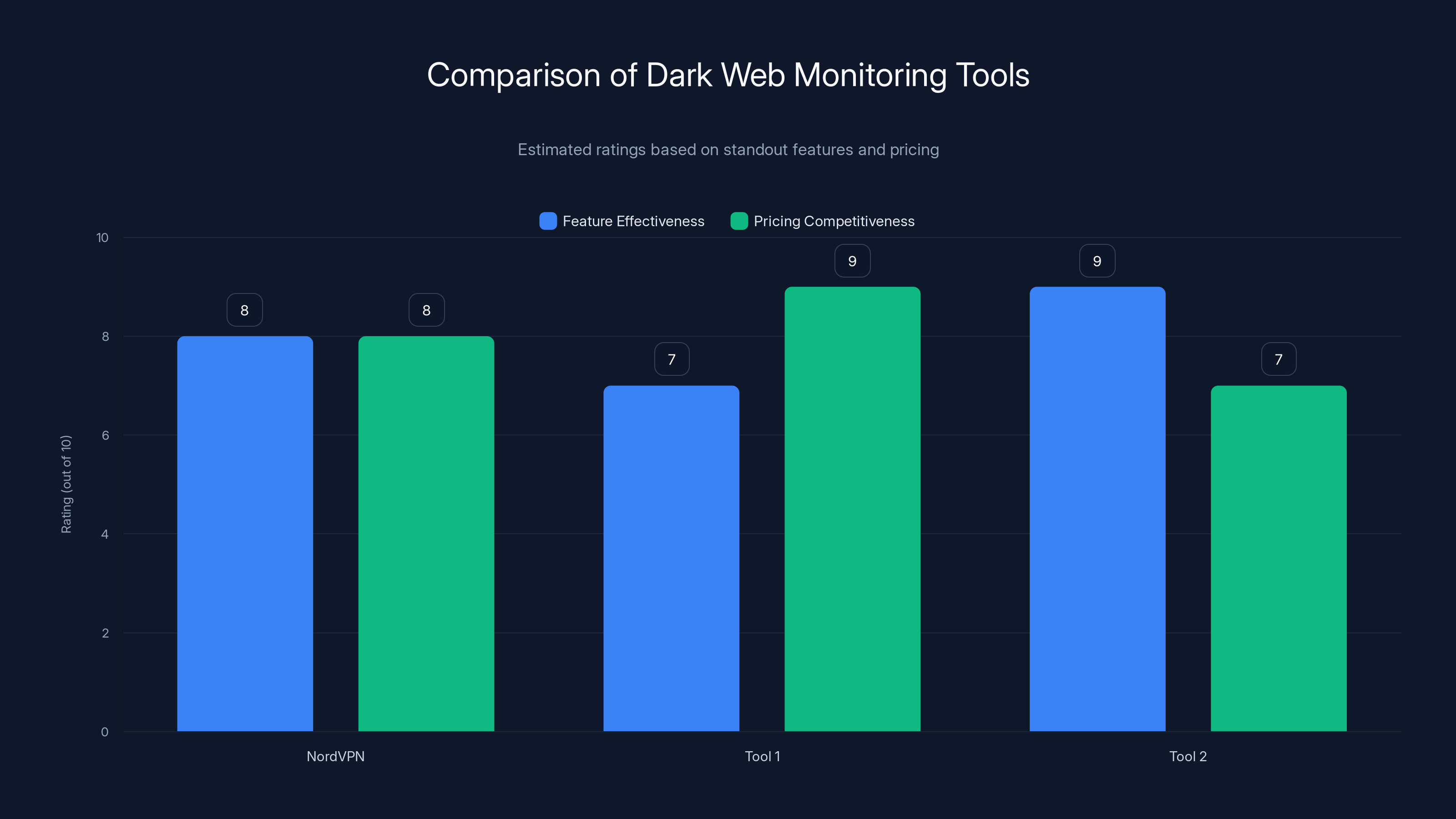
NordVPN and Tool 2 excel in feature effectiveness, while Tool 1 offers the most competitive pricing. Estimated data based on available features and pricing.
Why Did Google Kill Its Dark Web Scanner?
Google's decision to end its dark web scanning service puzzled many. The tool was part of its broader cybersecurity offerings under Google One, providing users with alerts if their personal information appeared in dark web listings. However, several factors likely influenced this move:
- Resource Allocation: Google often reallocates resources towards projects with greater strategic value. The dark web scanner might have been deemed less critical relative to other initiatives.
- Complexity of Dark Web Monitoring: The dark web is notoriously difficult to navigate due to its encrypted nature. Keeping track of ever-evolving threats requires constant updates and significant resources.
- Competition and Market Saturation: With numerous specialized companies providing similar services, Google may have decided that maintaining its own tool was not competitive.
Enter Nord VPN: The New Leader in Dark Web Monitoring
Nord VPN, a household name in cybersecurity, seized the opportunity to fill the void left by Google. Their upgraded dark web monitoring tool promises enhanced features and user-centric design, making it a formidable option for anyone concerned about data breaches.
Key Features of Nord VPN’s Tool
- Real-Time Alerts: Users receive immediate notifications if their data is found on the dark web.
- Comprehensive Breach Reports: Detailed insights into the nature of breaches, including data types and exposure levels.
- Ease of Use: A user-friendly interface that requires minimal technical expertise.
Real-World Use Case
Imagine this: A small business owner, Jane, uses Nord VPN’s tool to monitor her email and company domain. One night, she receives an alert that her email credentials have appeared on a hacker forum. Thanks to Nord VPN, Jane acts swiftly, changing her passwords and securing her accounts before any damage is done.
Pricing Context
Nord VPN offers this tool as part of its broader cybersecurity suite, available in plans starting at competitive rates. The pricing model is designed to be accessible to both individuals and businesses.
Integration and Ecosystem
Nord VPN integrates seamlessly with other security tools, providing a comprehensive shield against cyber threats. It supports integrations with popular password managers and security platforms.
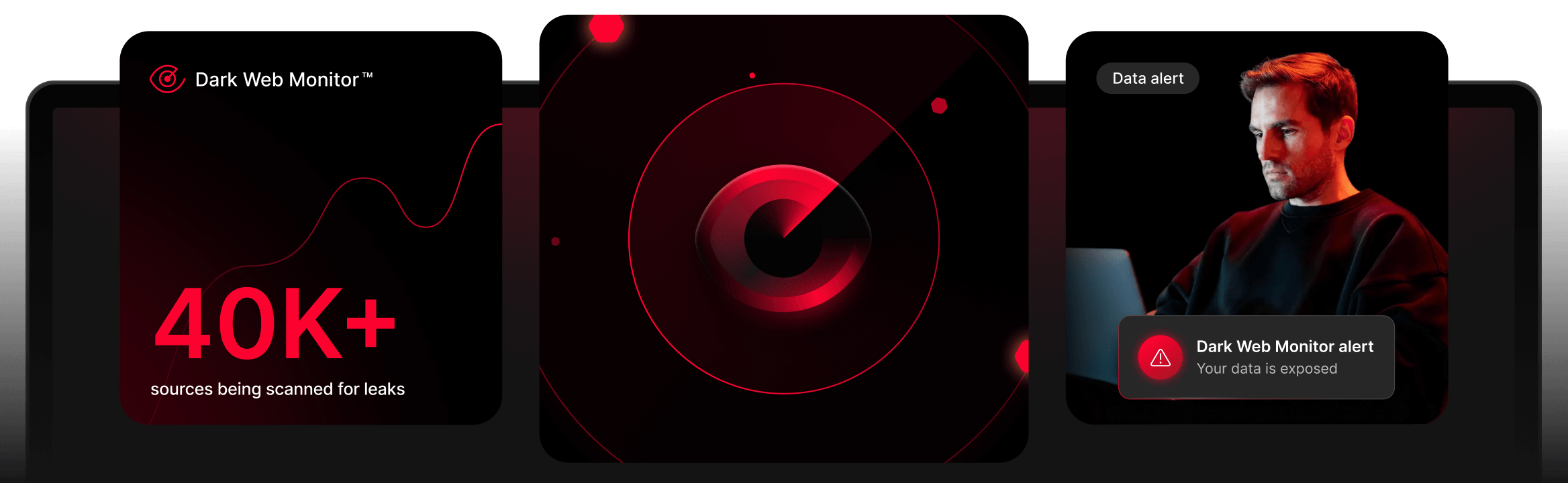
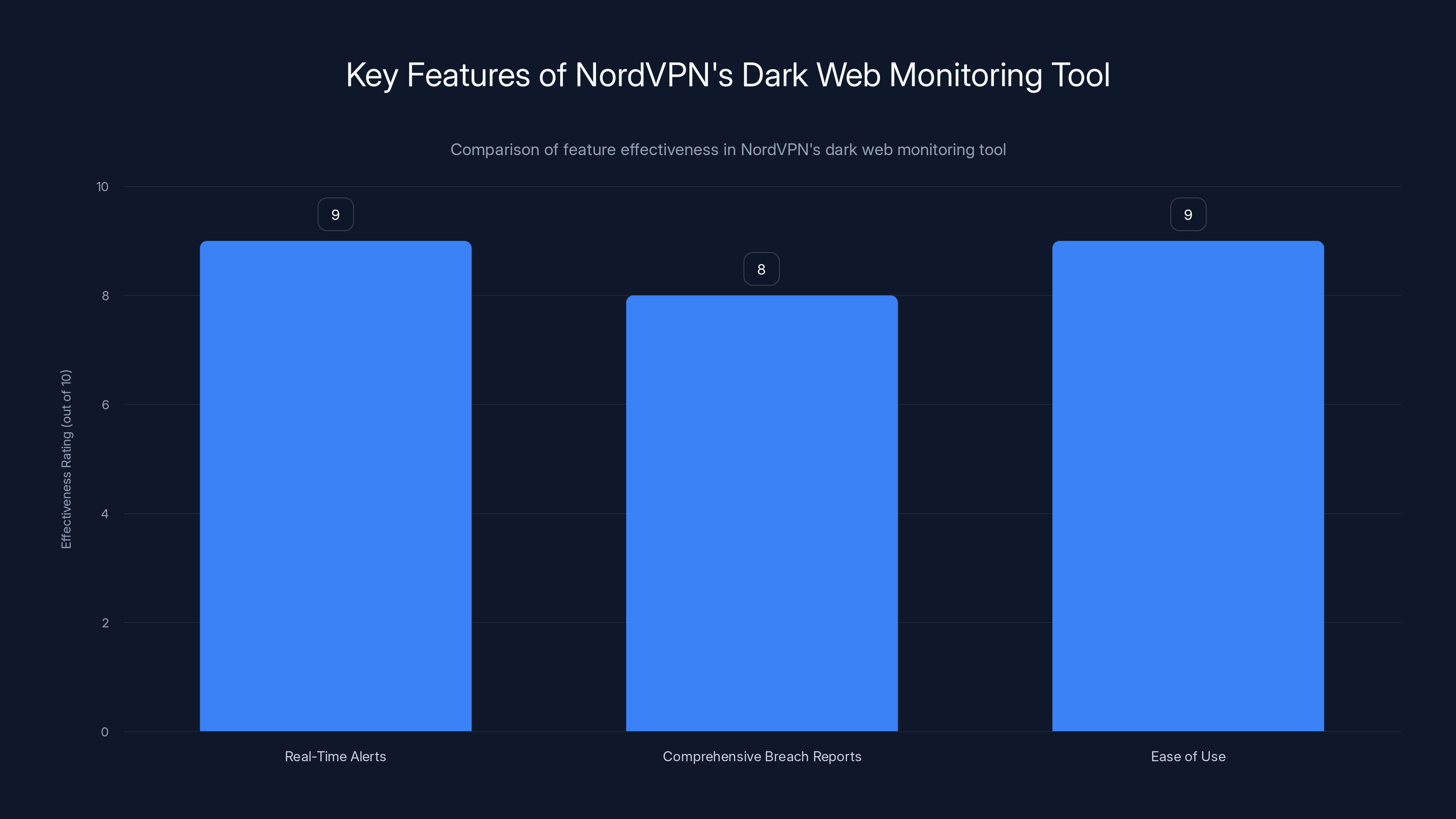
NordVPN's dark web monitoring tool excels in real-time alerts and ease of use, making it a top choice for cybersecurity needs. Estimated data based on feature descriptions.
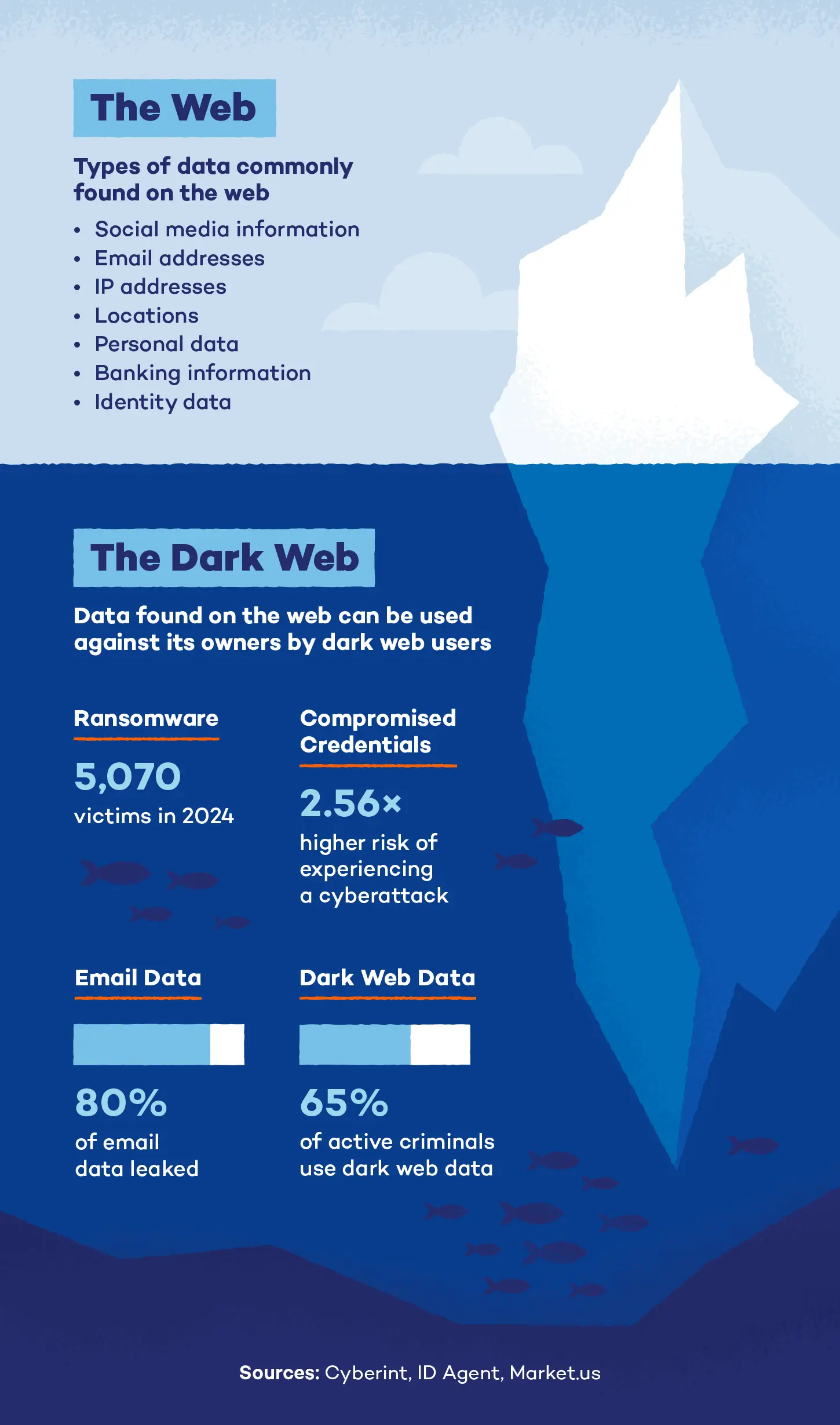
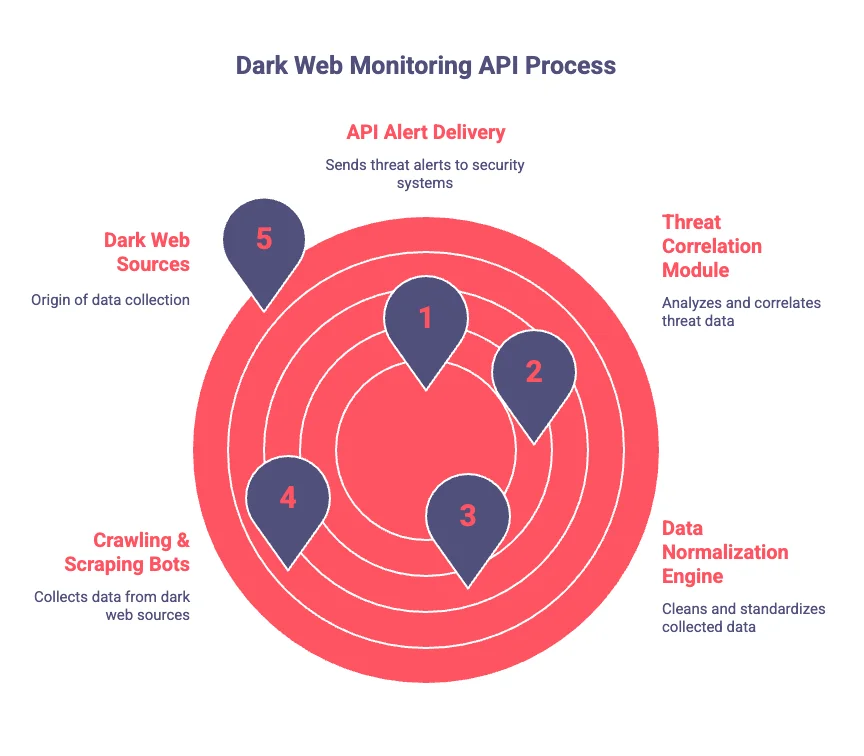
Technical Insights: How Dark Web Monitoring Works
Dark web monitoring tools like Nord VPN’s operate by scanning hidden parts of the internet where illegal activities often occur. Here's a breakdown of the technology:
- Data Collection: Continuous scanning of dark web entries, forums, and marketplaces for compromised data.
- Pattern Recognition: Advanced algorithms identify patterns and anomalies indicative of data breaches.
- Machine Learning: AI models predict potential threats based on historical data and current trends.
Best Practices for Using Dark Web Monitoring Tools
To maximize the effectiveness of dark web monitoring tools, users should adhere to the following best practices:
- Regularly Update Monitored Data: Ensure that all sensitive information, such as emails and domains, is consistently updated in the monitoring tool.
- Respond Swiftly to Alerts: Immediate action can prevent further compromise. Change passwords and enable two-factor authentication if alerted.
- Cross-Verify Alerts: Use multiple sources to confirm the legitimacy of alerts to avoid false positives.
Common Pitfalls and How to Avoid Them
Despite their benefits, dark web monitoring tools are not without challenges. Here are common pitfalls and solutions:
False Positives
Alerts are sometimes triggered by benign activity, causing unnecessary panic. To mitigate this:
- Calibrate Sensitivity: Adjust the tool's sensitivity settings to reduce false alarms.
- Educate Users: Inform users about the potential for false positives and how to handle them.
Incomplete Data Coverage
No tool can cover the entire dark web due to its vastness and constant evolution. Users should:
- Use Multiple Tools: Combine different monitoring tools for broader coverage.
- Stay Informed: Keep abreast of new threats and adjust monitoring criteria accordingly.
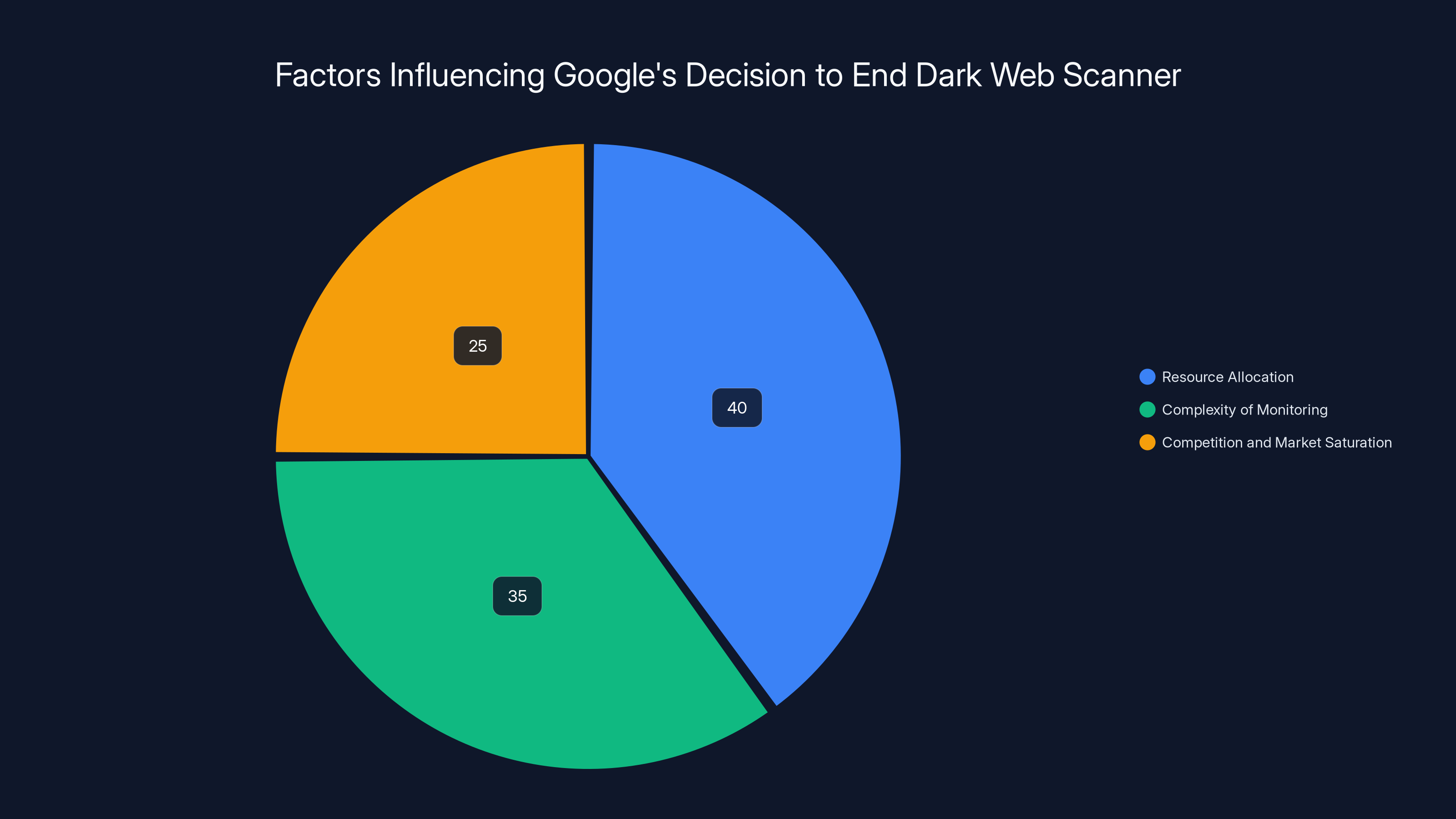
Estimated data suggests that resource allocation was the primary factor in Google's decision, followed by the complexity of monitoring and market competition.
Future Trends in Dark Web Monitoring
As technology evolves, so too will our tools for monitoring the dark web. Here are some trends to watch:
AI-Driven Predictive Analytics
Future tools will likely leverage AI to predict breaches before they occur, offering preemptive measures to safeguard data.
Enhanced User Personalization
Tools will become more tailored to individual needs, providing customized alerts and reports based on user behavior and preferences.
Integration with Io T Security
As Io T devices become more prevalent, dark web monitoring tools will expand their focus to include these devices, providing holistic security solutions.

Practical Implementation Guides
Implementing a dark web monitoring tool like Nord VPN’s involves several steps:
- Identify Key Assets: Determine which data points (emails, domains) need monitoring.
- Configure the Tool: Set up alerts and notifications according to your security needs.
- Integrate with Existing Security Measures: Ensure the tool complements your current cybersecurity framework.
- Test and Optimize: Regularly test the tool’s efficacy and make adjustments as necessary.

Conclusion: Nord VPN at the Forefront
With Google stepping back, Nord VPN has taken a bold step forward, offering a robust tool for safeguarding personal and corporate data. Their approach combines cutting-edge technology with user-centric design, making it a top choice for anyone serious about cybersecurity.
Use Case: Automate your data breach response by integrating Nord VPN’s alerts with your IT security protocols.
Try Runable For Free
FAQ
What is dark web monitoring?
Dark web monitoring involves tracking hidden parts of the internet for personal or compromised data, alerting users to potential breaches.
How does Nord VPN’s dark web tool work?
Nord VPN’s tool scans dark web forums and markets, sending real-time alerts when your data is found, allowing for quick protective measures.
What are the benefits of using a dark web monitoring tool?
Benefits include early breach detection, reduced risk of identity theft, and comprehensive data security insights, enhancing overall cybersecurity.
How can I avoid false positives in dark web monitoring?
Adjust the tool’s sensitivity settings and verify alerts through multiple sources to avoid unnecessary panic from false positives.
What future trends should I watch in dark web monitoring?
Look for AI-driven predictive analytics, enhanced personalization, and integration with Io T security as emerging trends in dark web monitoring.
Is Nord VPN’s tool suitable for businesses?
Yes, Nord VPN’s tool is designed for both individual and business use, offering scalable solutions and integrations with existing security systems.
Key Takeaways
- Nord VPN leads the market with its advanced dark web monitoring tool.
- Real-time alerts enhance user response times to breaches.
- AI and machine learning are pivotal in evolving cybersecurity tools.
- User-centric design makes tools accessible to non-experts.
- Integration capabilities with existing systems improve overall security.
- False positives remain a challenge but can be managed effectively.
- Future innovations will focus on predictive analytics and Io T security.
The Best Dark Web Monitoring Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Nord VPN | Comprehensive monitoring | Real-time alerts with detailed reports | Competitive plans |
| Tool 1 | Data breach insights | Multi-source verification | Free plan available; paid from $19.99/month |
| Tool 2 | Identity protection | AI-driven threat analysis | By request |
Quick Navigation:
- Nord VPN for comprehensive monitoring
- Tool 1 for data breach insights
- Tool 2 for identity protection

Related Articles
- Ericsson Data Breach: Analysis and Strategies [2025]
- Incredible 1000GB 5G Data SIM Deal [2025]
- The Ig Nobels: A New Chapter in Europe [2025]
- Project Hail Mary: A Deep Dive into Andy Weir's Sci-Fi Masterpiece [2025]
- Google's Gemini AI Revolutionizes Productivity with Docs, Sheets, and Slides [2025]
- Mastering Google's New Gemini AI Features in Docs, Sheets, Slides, and Drive [2025]
![The Evolution of Dark Web Monitoring: From Google's Exit to NordVPN’s Latest Innovations [2025]](https://tryrunable.com/blog/the-evolution-of-dark-web-monitoring-from-google-s-exit-to-n/image-1-1773162439189.jpg)



