Ericsson Data Breach: Analysis and Strategies [2025]
In today's interconnected digital landscape, data breaches have become a recurring concern for companies worldwide. The recent data breach at Ericsson US highlights the vulnerabilities associated with third-party vendors and the importance of robust cybersecurity measures. This article delves into the details of the breach, explores its implications, and provides actionable strategies for organizations to prevent similar incidents.
TL; DR
- Third-Party Vulnerabilities: The breach underscores the risks associated with third-party vendors handling sensitive data.
- Data Exposed: Compromised information includes sensitive customer data, such as Social Security Numbers and financial details.
- Immediate Actions: Ericsson has implemented measures to enhance security and provide affected individuals with identity protection services.
- Future Prevention: Emphasizes the need for comprehensive security audits and robust vendor management.
- Industry Trends: Predicts increased regulatory scrutiny and the adoption of advanced AI-driven security solutions.

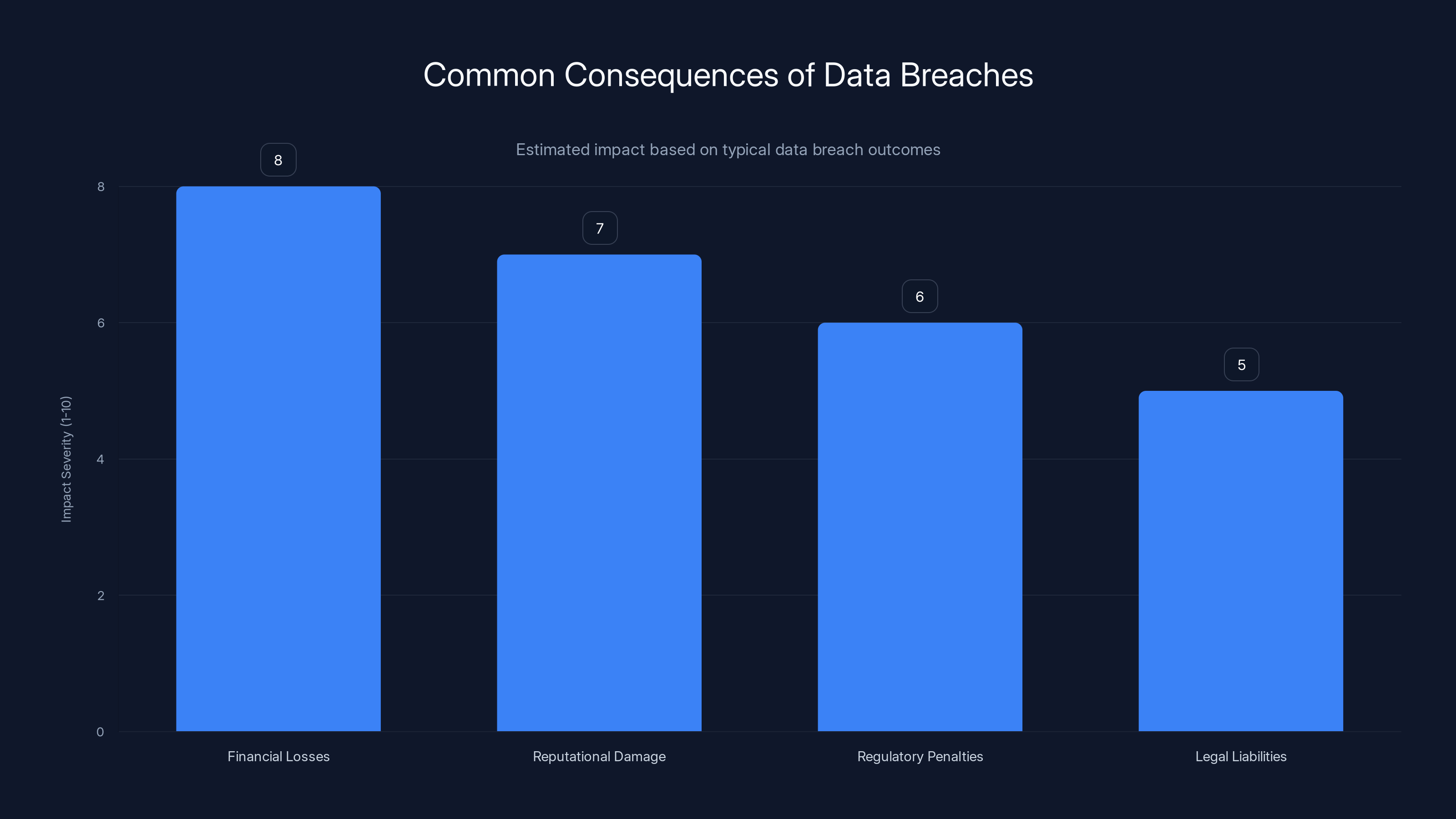
Financial losses and reputational damage are typically the most severe consequences of data breaches. (Estimated data)
Understanding the Breach
On April 28, 2025, Ericsson US detected a suspicious event indicating unauthorized access to its systems. An unidentified threat actor exploited vulnerabilities in a third-party vendor, leading to the exposure of sensitive customer data, including Social Security Numbers and financial information.
The Role of Third-Party Vendors
Third-party vendors are integral to business operations, offering specialized services and solutions. However, they also introduce potential vulnerabilities. In this case, the breach was facilitated through a third-party partner, highlighting the critical need for stringent vetting and continuous monitoring of vendors.
Key Takeaway: Businesses must implement rigorous vendor management programs, including regular audits and risk assessments, to mitigate potential security risks.
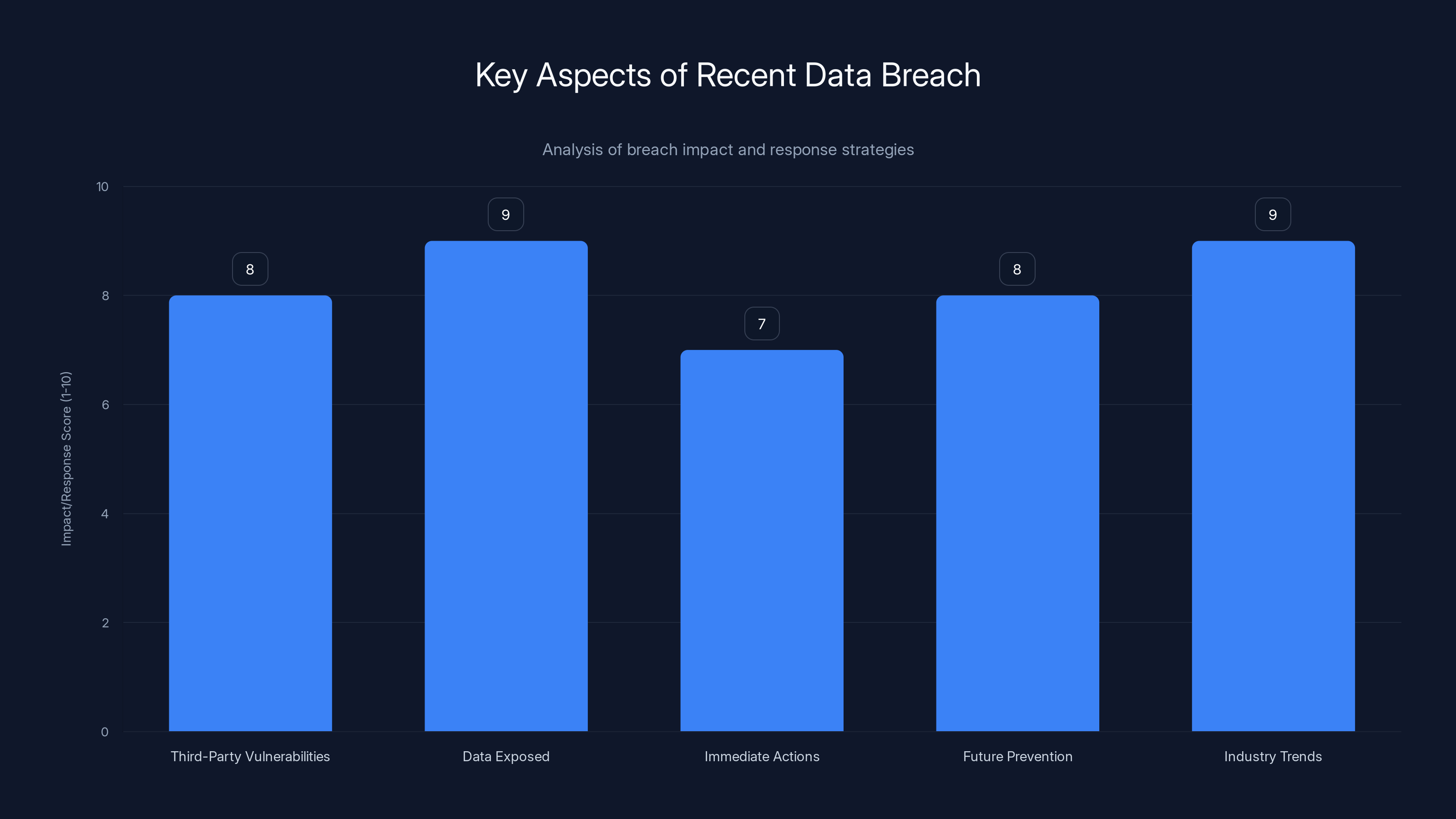
The breach highlights significant risks from third-party vendors and exposed sensitive data, prompting immediate actions and future prevention strategies. Estimated data.
Immediate Response and Mitigation
Upon identifying the breach, Ericsson took several immediate actions:
- Investigation and Containment: Engaged third-party security experts to investigate the breach and contain its impact.
- Notification: Informed affected individuals and regulatory bodies, including the FBI, to ensure transparency and compliance.
- Enhanced Security Measures: Implemented additional security protocols to prevent future breaches.
- Identity Protection: Offered free identity protection services to affected individuals to mitigate potential harm.
Practical Implementation Guide
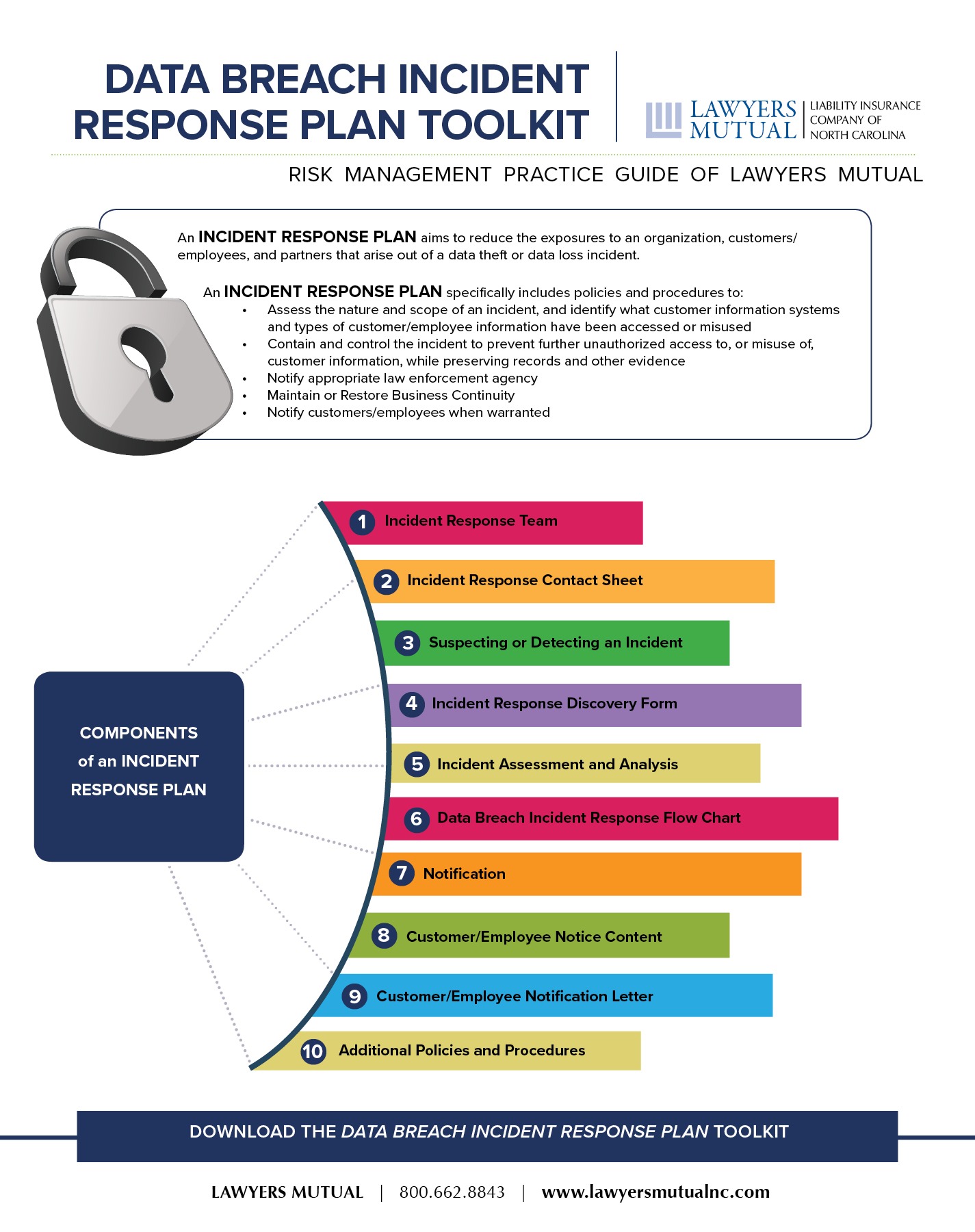
Organizations can adopt the following steps to enhance their breach response strategies:
- Develop a Comprehensive Incident Response Plan: This should include procedures for detection, containment, eradication, recovery, and communication.
- Conduct Regular Security Drills: Simulate breach scenarios to test the effectiveness of the response plan and ensure that all stakeholders are prepared.
- Leverage Advanced Threat Detection Tools: Utilize AI-driven solutions to identify and respond to threats in real time.
Common Pitfalls and Solutions
Pitfall 1: Overlooking Third-Party Risks
Many organizations fail to account for the security posture of their vendors, which can lead to significant vulnerabilities.
Solution: Establish a robust vendor management program that includes detailed security requirements in contracts and regular audits of vendor security practices.
Pitfall 2: Delayed Breach Detection
Delayed detection can exacerbate the impact of a breach.
Solution: Implement continuous monitoring solutions and threat intelligence feeds to identify potential breaches promptly.

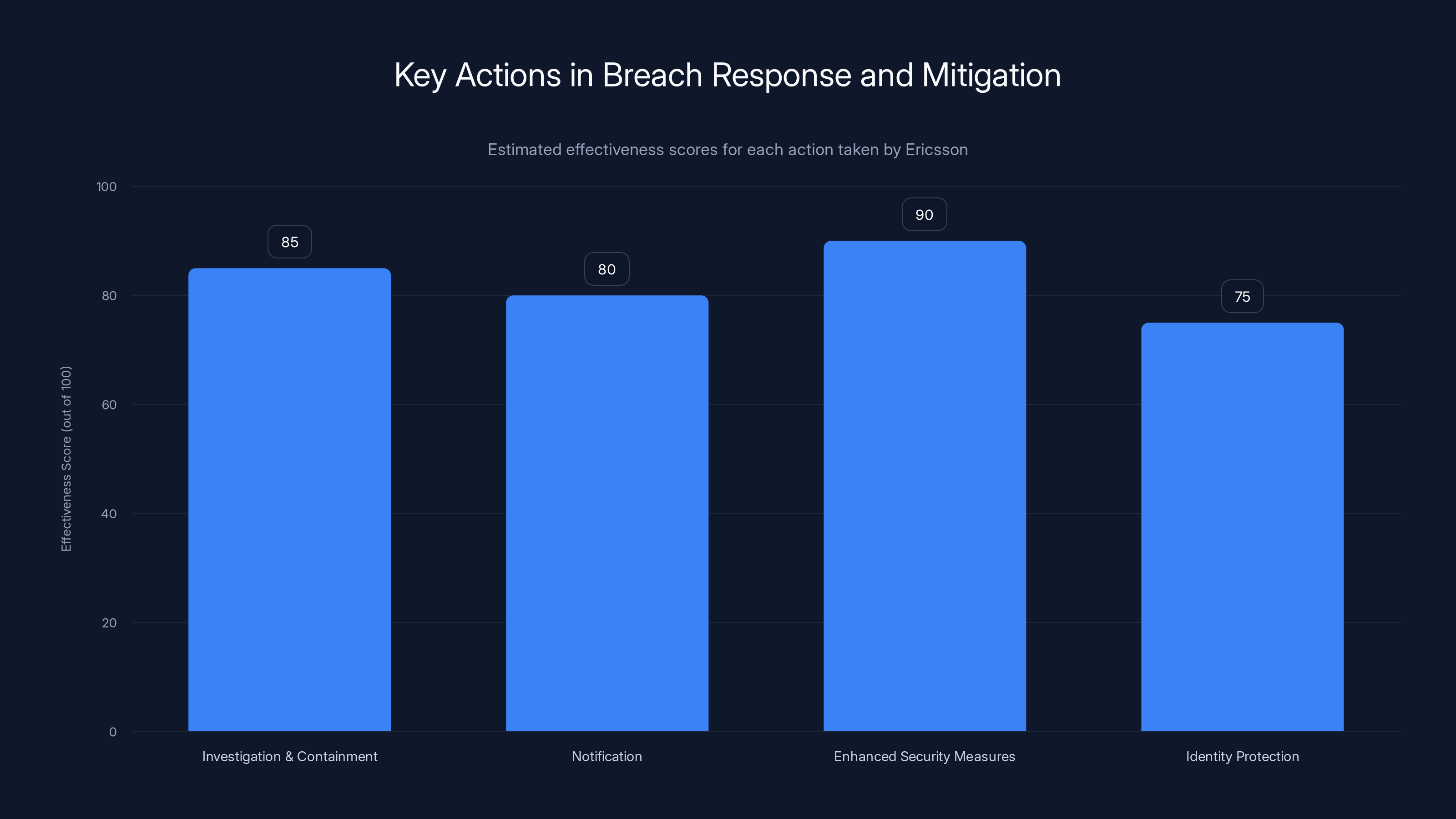
The chart estimates the effectiveness of Ericsson's immediate response actions, highlighting enhanced security measures as the most effective step. Estimated data.
Future Trends and Recommendations
Trend 1: Increased Regulatory Scrutiny
Regulators are intensifying their focus on data protection and privacy, imposing stricter requirements on organizations.
Recommendation: Stay informed about evolving regulations and ensure compliance by implementing comprehensive data protection policies.
Trend 2: Adoption of AI-Driven Security Solutions
AI and machine learning are revolutionizing cybersecurity by enabling organizations to detect and respond to threats more effectively.
Recommendation: Invest in AI-driven security solutions to enhance threat detection and automate response capabilities.

Conclusion
The Ericsson data breach serves as a stark reminder of the complexities and challenges associated with cybersecurity in the modern digital landscape. By understanding the implications of this breach and implementing robust security measures, organizations can better protect themselves against future incidents.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals access confidential data, often leading to the exposure or theft of sensitive information.
How can companies prevent data breaches?
Companies can prevent data breaches by implementing strong security measures, conducting regular audits, and employing advanced threat detection solutions.
What are the consequences of a data breach?
Consequences include financial losses, reputational damage, regulatory penalties, and potential legal liabilities.
How should companies respond to a data breach?
Companies should promptly investigate the breach, contain its impact, notify affected parties, and implement measures to prevent future incidents.
What role do third-party vendors play in data security?
Third-party vendors can introduce vulnerabilities, making it crucial for companies to vet and monitor their security practices closely.
What are the latest trends in cybersecurity?
Latest trends include the adoption of AI-driven security solutions, increased regulatory scrutiny, and a focus on proactive threat prevention.
How can individuals protect themselves after a data breach?
Individuals should monitor their financial accounts closely, utilize identity protection services, and change passwords regularly.
What is the significance of regulatory compliance in data security?
Regulatory compliance ensures that companies adhere to legal requirements for data protection, mitigating the risk of penalties and enhancing customer trust.
How does AI enhance cybersecurity?
AI enhances cybersecurity by enabling real-time threat detection, automating response processes, and providing predictive analytics to anticipate potential threats.
What measures did Ericsson take following the breach?
Ericsson engaged security experts, notified regulatory bodies and affected individuals, implemented enhanced security protocols, and offered identity protection services.
Key Takeaways
- Third-party vulnerabilities can lead to significant data breaches.
- Prompt and transparent response is crucial in mitigating breach impact.
- Implementing robust vendor management programs is essential.
- AI-driven security solutions enhance threat detection and response.
- Regulatory compliance is increasingly important in data protection.
Related Articles
- The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
- Trump's Cyber Strategy: A New Era for U.S. Cyber Power [2025]
- Protecting Your Business from POS Malware Attacks [2025]
- OpenAI's Acquisition of Promptfoo: Securing AI Agents for the Future [2025]
- Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
![Ericsson Data Breach: Analysis and Strategies [2025]](https://tryrunable.com/blog/ericsson-data-breach-analysis-and-strategies-2025/image-1-1773153504965.jpg)



