Understanding SMS Blasting: The Hidden Threat and How to Protect Against It [2025]
Last month, Toronto made headlines when police arrested a crew responsible for a massive SMS blasting operation. This incident highlights the growing threat of SMS-based cyberattacks and the urgent need for awareness and preventive measures, as detailed by TechCrunch.
TL; DR
- SMS Blasting Defined: Malicious mass text messaging to steal sensitive data.
- Toronto Incident: First known SMS blaster operation in Canada, affecting thousands, as reported by Inside Towers.
- Impact: Disrupted communications and threatened emergency services, as noted by Tom's Hardware.
- Protection Tips: Use spam filters, verify messages, and educate users.
- Future Outlook: Enhanced security protocols and legislation are needed.
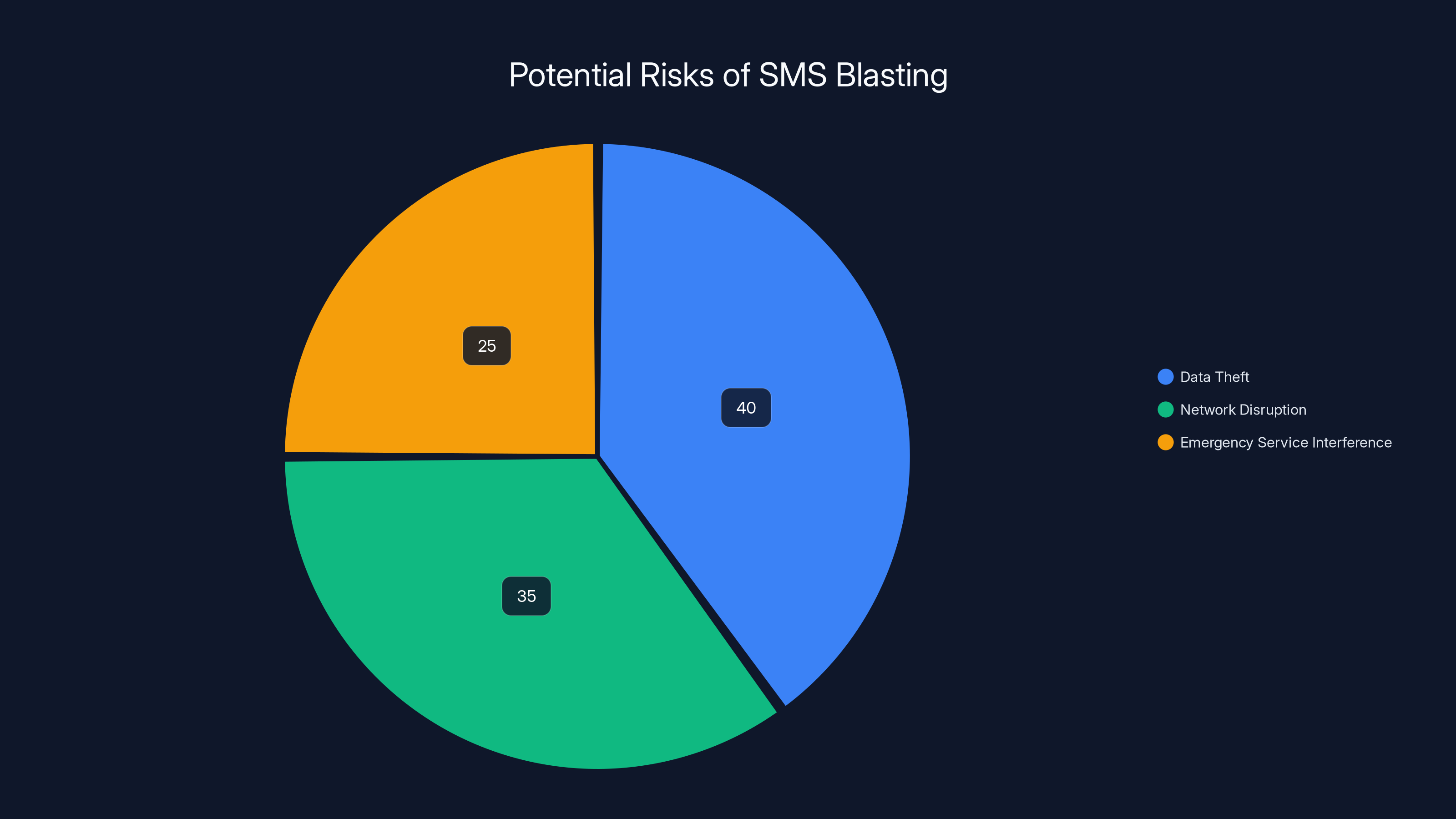
Estimated data shows data theft as the most significant risk of SMS blasting, followed by network disruption and emergency service interference.
The Rise of SMS Blasting
What is SMS Blasting?
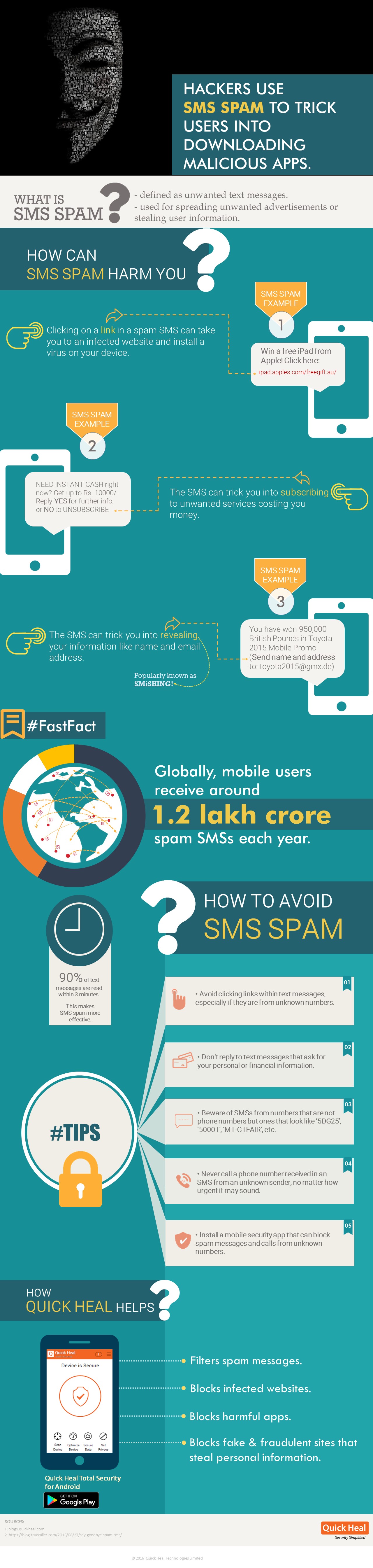
SMS blasting refers to the practice of sending a large volume of text messages to numerous recipients simultaneously. While this technique can be used for legitimate marketing, malicious actors often exploit it for phishing attacks, aiming to steal sensitive information like passwords and banking credentials, as explained by Help Net Security.
The Toronto Incident: A Case Study
In November 2025, Toronto police unveiled an SMS blasting scheme that targeted thousands across the city. This case is notable as the first known instance of such an operation in Canada. The perpetrators used a uniquely built SMS blaster to send spam messages, disrupting cellular networks and potentially interfering with emergency services, as detailed by Toronto Police Service.
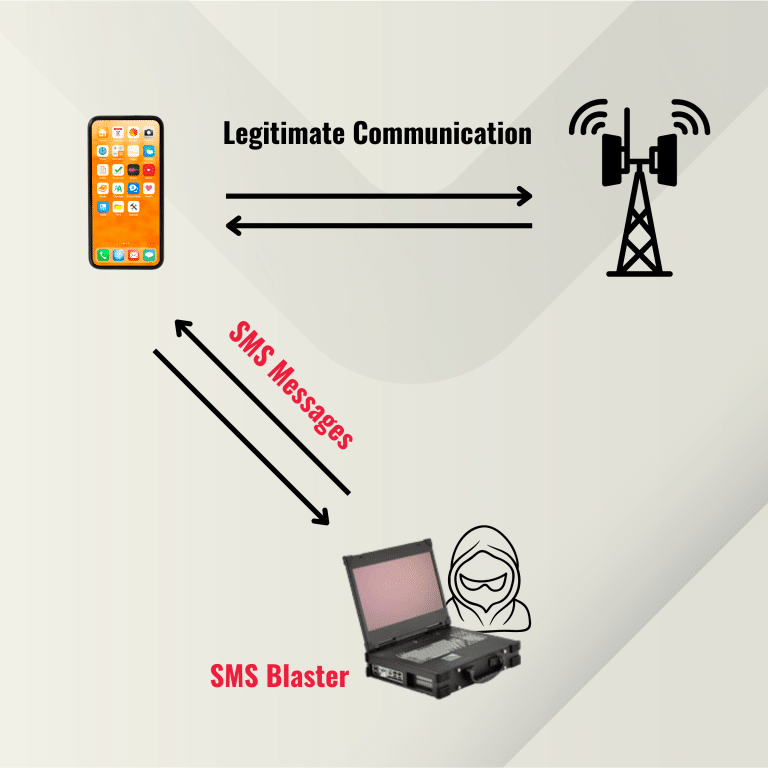
How SMS Blasters Work
Technical Breakdown
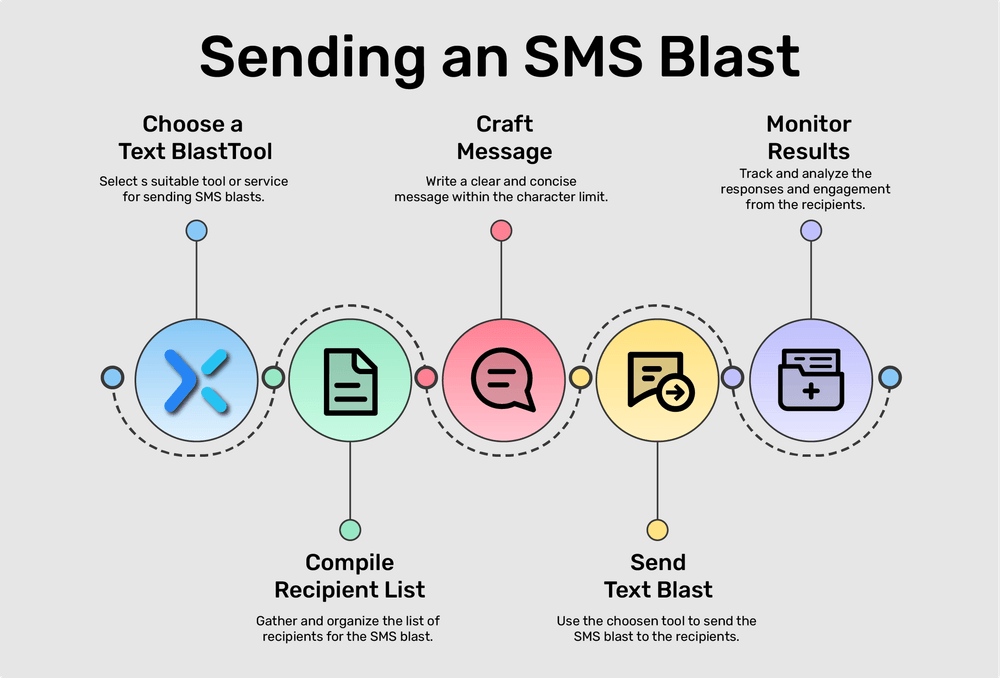
SMS blasters typically consist of hardware and software components designed to automate the mass sending of messages. The hardware may include a computer or a dedicated device equipped with SIM cards from various carriers. The software is used to manage and execute the messaging campaigns, as described by The Hacker News.
Key Components:
- GSM Modem: Connects to cellular networks to send messages.
- SIM Cards: Multiple cards to evade carrier restrictions.
- Automation Software: Manages contact lists and message scheduling.
Example of an SMS Blaster Setup
A typical setup might involve a laptop connected to a GSM modem. The software interface allows the user to input message content, target phone numbers, and schedule the dispatch. Some advanced systems can even customize messages based on recipient data, increasing the chances of success in phishing attempts, as noted by Gizmodo.
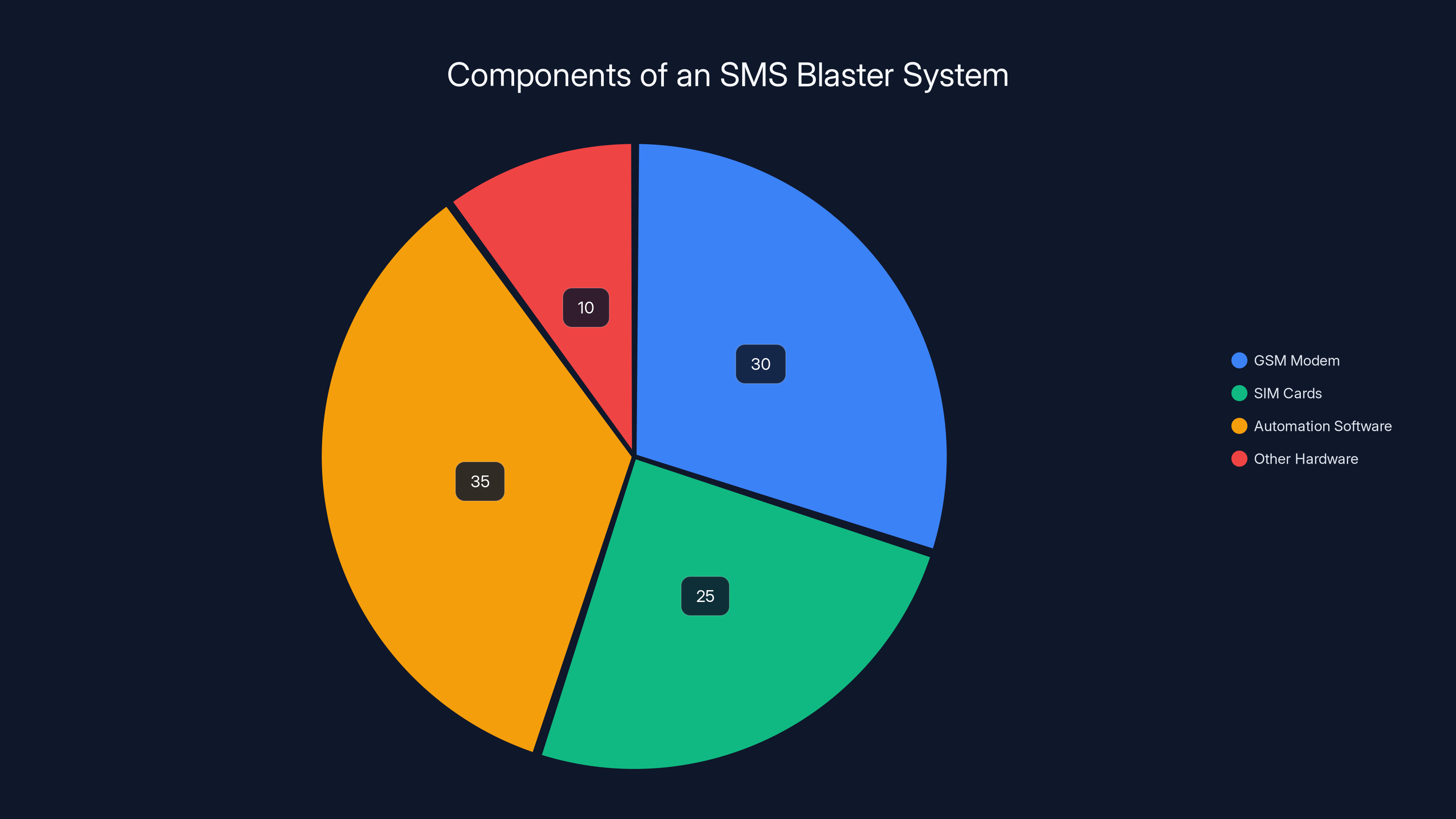
The pie chart illustrates the estimated distribution of key components in an SMS blaster setup, with automation software and GSM modems being the most significant parts. Estimated data.
The Dangers of SMS Blasting
Impact on Individuals and Infrastructure
The Toronto case demonstrated several potential risks associated with SMS blasting:
- Data Theft: Victims may unknowingly provide personal information through phishing links.
- Network Disruption: Saturated networks can lead to delayed or failed message delivery.
- Emergency Service Interference: Overloaded networks could hinder 911 responses, as highlighted by Tom's Hardware.
Real-World Consequences
Imagine receiving a text claiming to be from your bank, urging you to verify your account information via a link. This common phishing tactic exploits the trust people place in SMS communication, making it a potent tool for cybercriminals, as discussed by Brevo.
Protecting Against SMS Blasting
Best Practices for Individuals
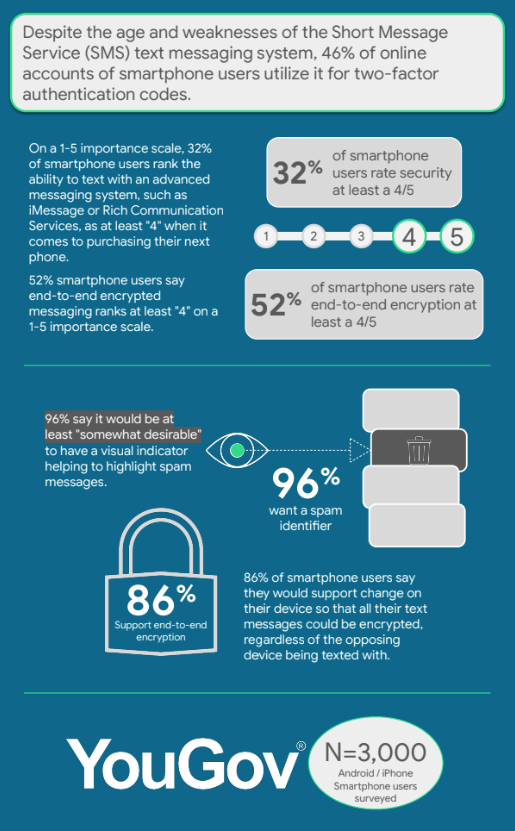
- Verify Message Authenticity: Always double-check the sender's information and avoid clicking on links from unknown sources.
- Use Spam Filters: Enable spam protection on your phone to automatically block suspicious messages.
- Educate Yourself and Others: Awareness is a powerful tool. Understand common phishing tactics and share this knowledge with friends and family, as recommended by The Hacker News.
Organizational Measures
- Implement Robust Security Protocols: Regularly update and patch systems to close vulnerabilities.
- Monitor Network Traffic: Use analytics to detect unusual activity that may indicate an ongoing attack.
- Educate Employees: Conduct regular training sessions on cybersecurity best practices, as advised by ABS-CBN News.

Common Pitfalls and Solutions
Pitfall: Overreliance on Technology
While technology plays a crucial role in defense, human vigilance remains essential. Employees should be encouraged to report suspicious activity immediately.
Solution: Comprehensive Security Culture
Foster a culture of security awareness within organizations. Encourage proactive behavior and continuous learning to stay ahead of potential threats, as emphasized by Toronto Police Service.
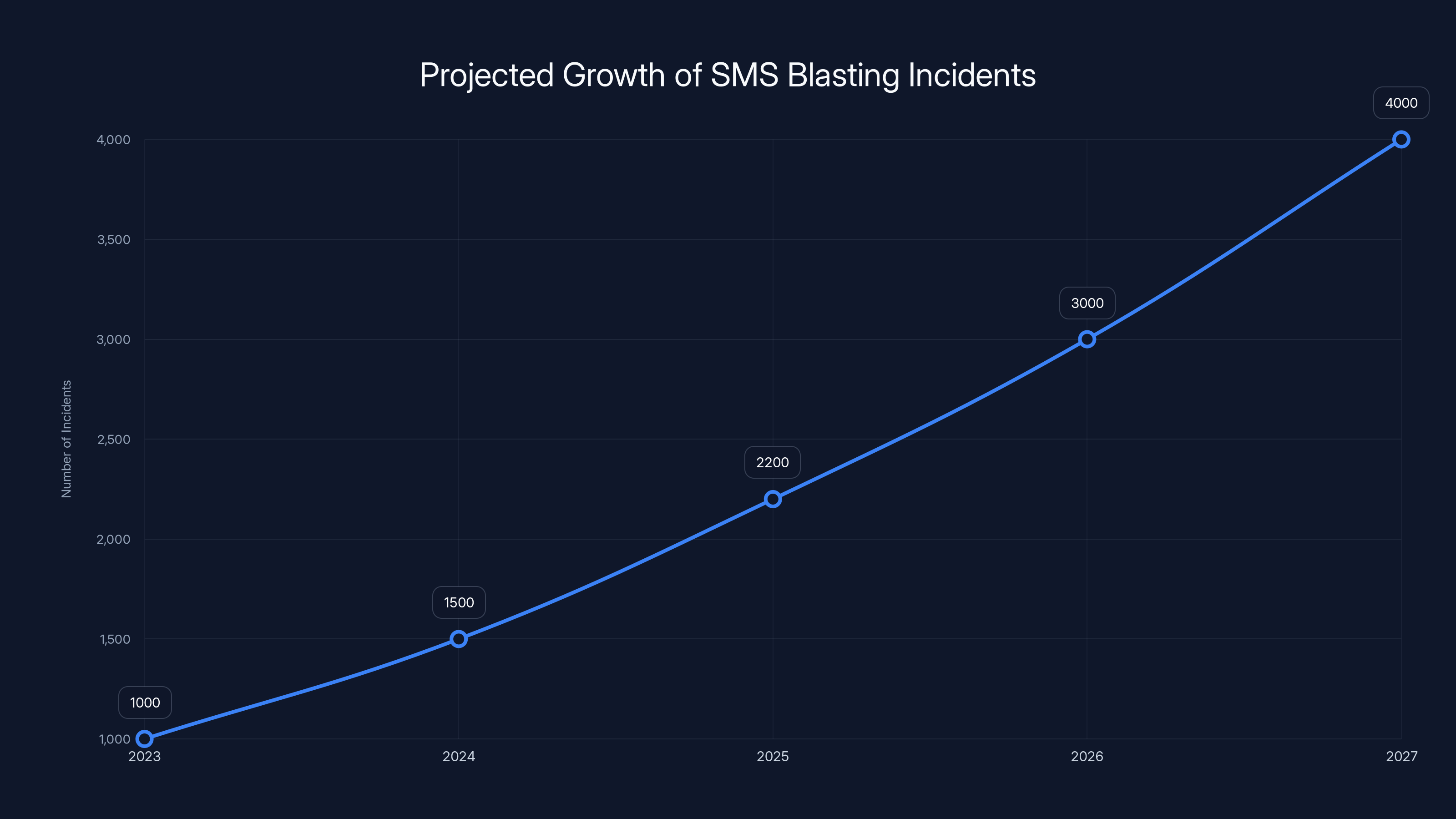
The projected growth of SMS blasting incidents suggests a significant increase, highlighting the need for enhanced cybersecurity measures. (Estimated data)
Future Trends and Recommendations
Advancements in Security Technology
Emerging technologies like AI and machine learning are expected to enhance threat detection capabilities. These tools can analyze patterns and identify anomalies more effectively than traditional methods, as noted by Inside Towers.
Legislative Measures
Governments worldwide are recognizing the need for stricter regulations on telecommunication practices. Future legislation may impose harsher penalties on cybercriminals and mandate stronger security measures from telecom providers, as discussed by Gizmodo.
Conclusion
The arrest of the SMS blaster crew in Toronto serves as a wake-up call to the growing threat of SMS-based attacks. By understanding the mechanics of SMS blasting and implementing robust security measures, individuals and organizations can better protect themselves against these malicious activities, as highlighted by Help Net Security.
FAQ
What is SMS blasting?
SMS blasting is the practice of sending a large volume of text messages to numerous recipients simultaneously, often used for malicious purposes like phishing.
How does SMS blasting work?
It involves hardware and software components designed to automate mass messaging, often including a GSM modem and multiple SIM cards.
What are the dangers of SMS blasting?
Risks include data theft, network disruption, and interference with emergency services.
How can individuals protect against SMS blasting?
Verify message authenticity, use spam filters, and educate yourself on common phishing tactics.
What should organizations do to mitigate SMS blasting threats?
Implement robust security protocols, monitor network traffic, and educate employees on cybersecurity best practices.
What future trends can help combat SMS blasting?
Advancements in AI and machine learning for threat detection, along with stricter legislative measures, will play key roles in combating SMS blasting.
Key Takeaways
- Understanding SMS Blasting: A critical threat to cybersecurity that requires awareness and prevention.
- Toronto Case Study: Highlighted the impact of SMS blasting on individuals and infrastructure.
- Protection Measures: Include verifying messages, using spam filters, and educating users.
- Technological Advancements: AI and machine learning promise improved threat detection.
- Legislative Action: Stricter regulations are needed to deter cybercriminals.
Tags
"SMS blasting", "cybersecurity", "phishing", "Toronto incident", "network security", "spam filters", "telecommunication laws", "cybercrime prevention", "AI in security", "data protection"

Category
Cybersecurity

Related Articles
- Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]
- Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
- Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]
- How Canada Uses Canary Traps for Election Security: An In-Depth Analysis [2025]
- Revamping Enterprise Networks for AI Transformation: A Decade-Old Overhaul [2025]
- The Rise of Vibe-Coded Apps: A New Frontier in Cybersecurity [2025]
![Understanding SMS Blasting: The Hidden Threat and How to Protect Against It [2025]](https://tryrunable.com/blog/understanding-sms-blasting-the-hidden-threat-and-how-to-prot/image-1-1778166375142.jpg)



