The Internet's Trust Dilemma: Why Identity Verification Must Evolve [2025]
In today’s digital landscape, trust is a currency we can’t afford to lose. Yet, the internet is rife with challenges that undermine this very essence. From fraudulent activities to data breaches, the digital realm poses significant threats to both individual and corporate identities. So, how do we navigate this complex web of trust issues? The answer lies in evolving our approach to identity verification, making it portable, secure, and universally recognized.
TL; DR
- Identity verification is crucial: Ensuring trust online is imperative for both businesses and users. According to Microsoft's security insights, identity security is becoming a critical focus in modern cyber defense.
- Portable identities: Digital identities need to be recognized across platforms to improve user experience and security. The self-sovereign identity market is expected to grow significantly, highlighting the demand for portable identity solutions.
- Technical challenges: Current systems are fragmented and often insecure, leading to increased vulnerabilities. Cyberattacks on manufacturers demonstrate the risks associated with fragmented identity systems.
- Future trends: Blockchain and decentralized identifiers (DIDs) are paving the way for more robust identity systems. As noted by Samsung's advancements in AI and blockchain, these technologies are crucial for future identity solutions.
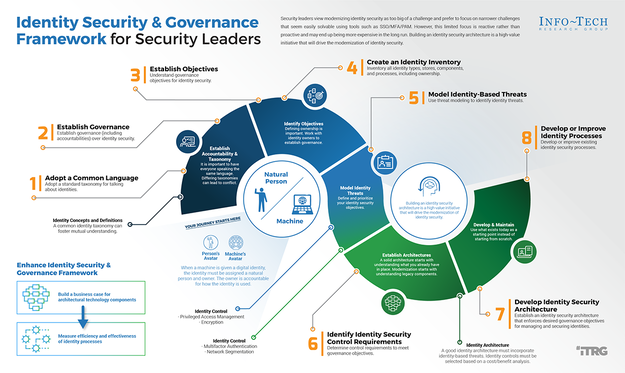
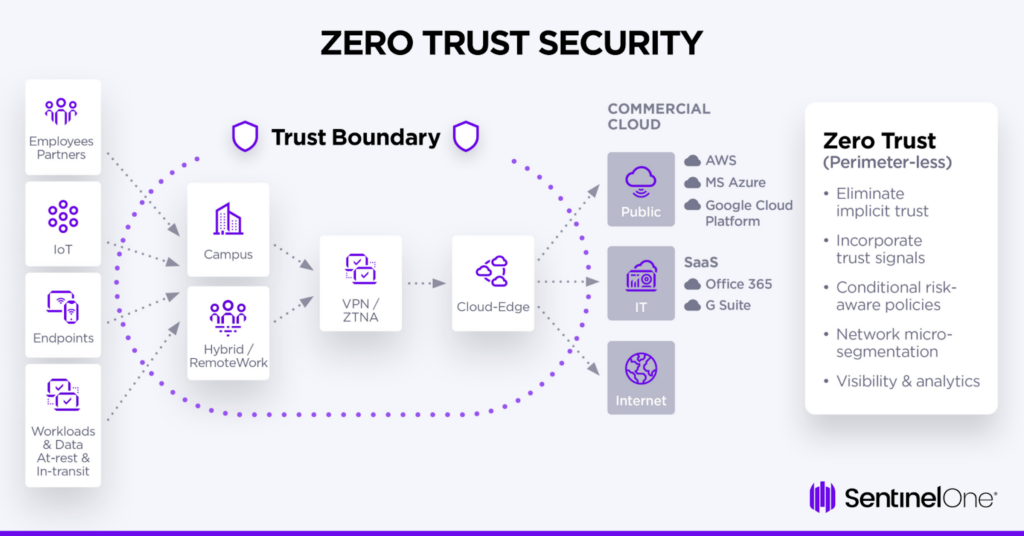
- Best practices: Implementing multi-factor authentication and zero-trust architectures can mitigate risks. Microsoft's zero-trust model offers a framework for enhancing security.
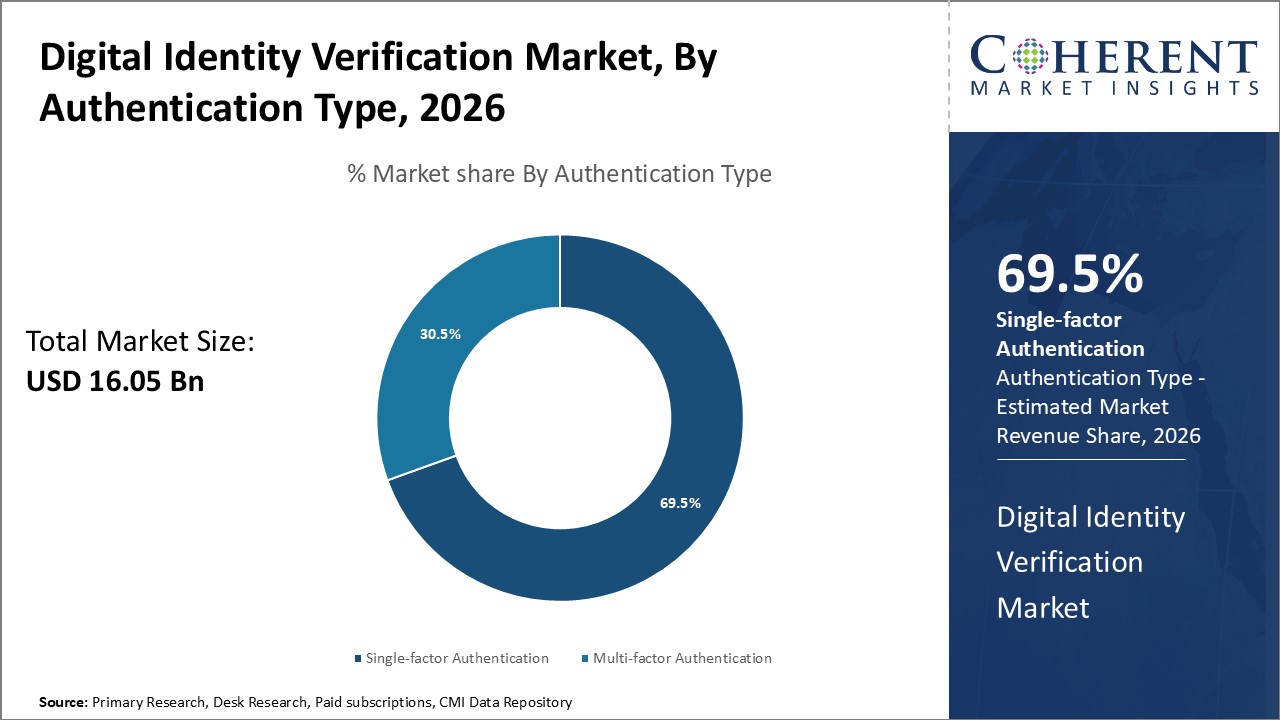
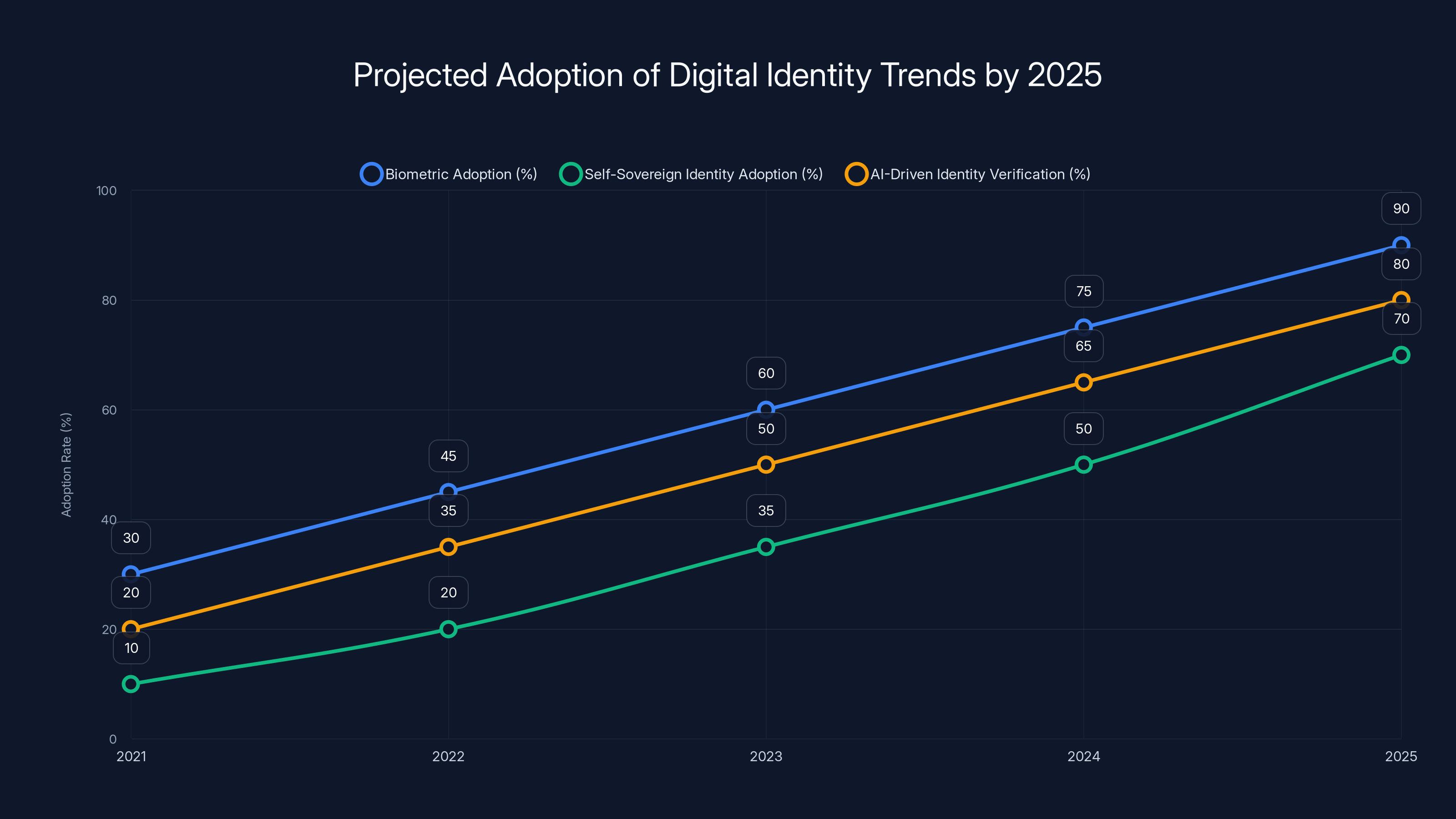
By 2025, biometric and AI-driven identity verification are projected to become standard, with self-sovereign identity also seeing significant adoption. (Estimated data)
The Current State of Digital Identity
The internet was not designed with identity in mind. This oversight has led to a patchwork of verification systems, each with its vulnerabilities and limitations. From social media platforms to banking apps, each service requires its form of identity proof, often leading to inconsistent security measures.
Fragmentation and Its Consequences
The lack of a unified identity system means users often juggle multiple passwords and verification methods. This fragmentation not only burdens users but also opens doors for security breaches. For instance, a breach in one platform can potentially compromise a user's identity across others due to reused passwords or similar security questions. Dark web monitoring tools have highlighted how easily compromised credentials can be exploited.

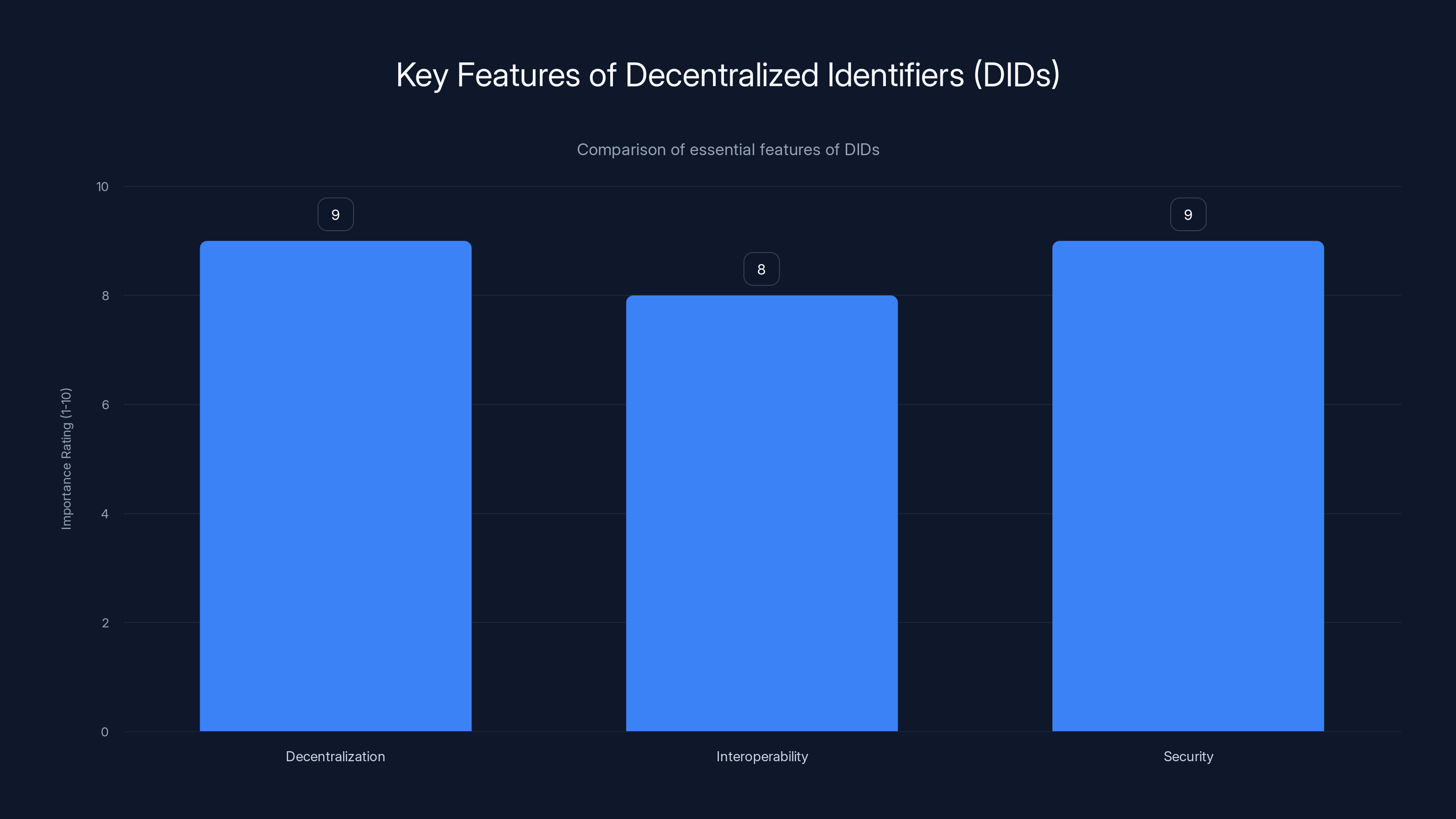
Decentralized Identifiers (DIDs) are highly rated for decentralization and security, making them a robust choice for digital identity management. Estimated data based on typical feature importance.
Why Portable Identities Are Essential
Imagine walking into a bank, only to be asked to prove your identity from scratch each time. This is essentially what happens online daily. Portable identities would allow users to carry their verified credentials across platforms, reducing friction and enhancing security.
Benefits of Portable Identities
- Seamless User Experience: Users can log in to services without repeatedly entering credentials.
- Enhanced Security: Verified credentials reduce the risk of identity theft.
- Reduced Costs: Businesses save on resources spent managing identity systems. The launch of workforce communities demonstrates the cost-saving potential of streamlined identity solutions.

Technical Frameworks for Digital Identity
The challenge of creating a portable identity system lies in its technical complexity. Here are some frameworks and technologies that could revolutionize digital identity:
Decentralized Identifiers (DIDs)
DIDs are a new type of identifier that allows individuals to manage their digital identities independently. Unlike traditional identifiers, such as email addresses, DIDs are not tied to any centralized registry, identity provider, or certificate authority.
Key Features of DIDs:
- Decentralization: No single point of failure or control.
- Interoperability: Compatible with various platforms and services.
- Security: Cryptographically secure, reducing the risk of unauthorized access.
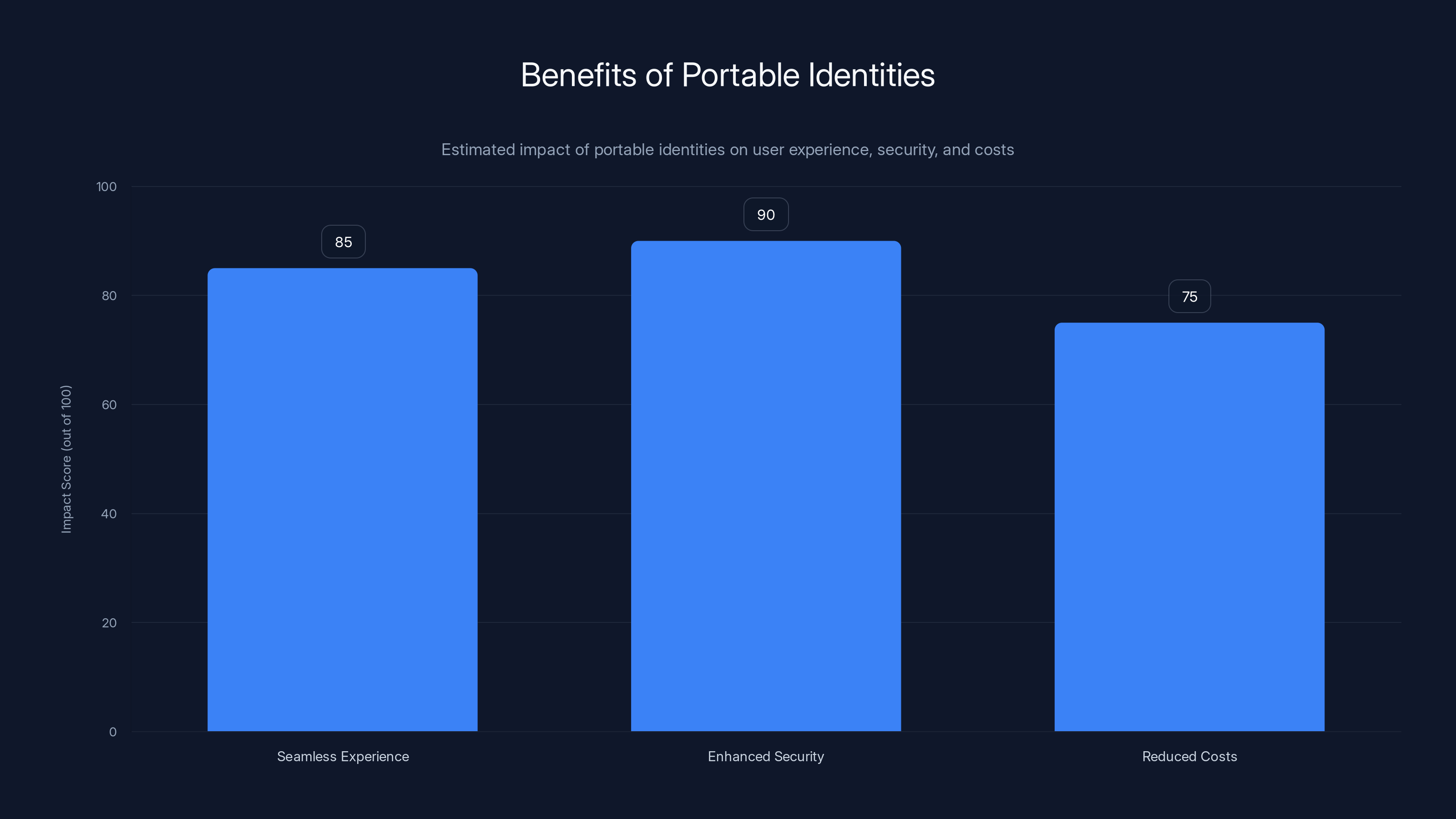
Portable identities significantly enhance user experience and security, while also reducing costs for businesses. (Estimated data)
Implementing Secure Identity Systems
To effectively implement secure identity systems, a multi-layered approach is essential. Here are some best practices:
Multi-Factor Authentication (MFA)
MFA requires users to provide two or more verification factors to gain access to a resource, such as an application or an online account.
Benefits of MFA:
- Increased Security: Even if one factor is compromised, unauthorized access is prevented.
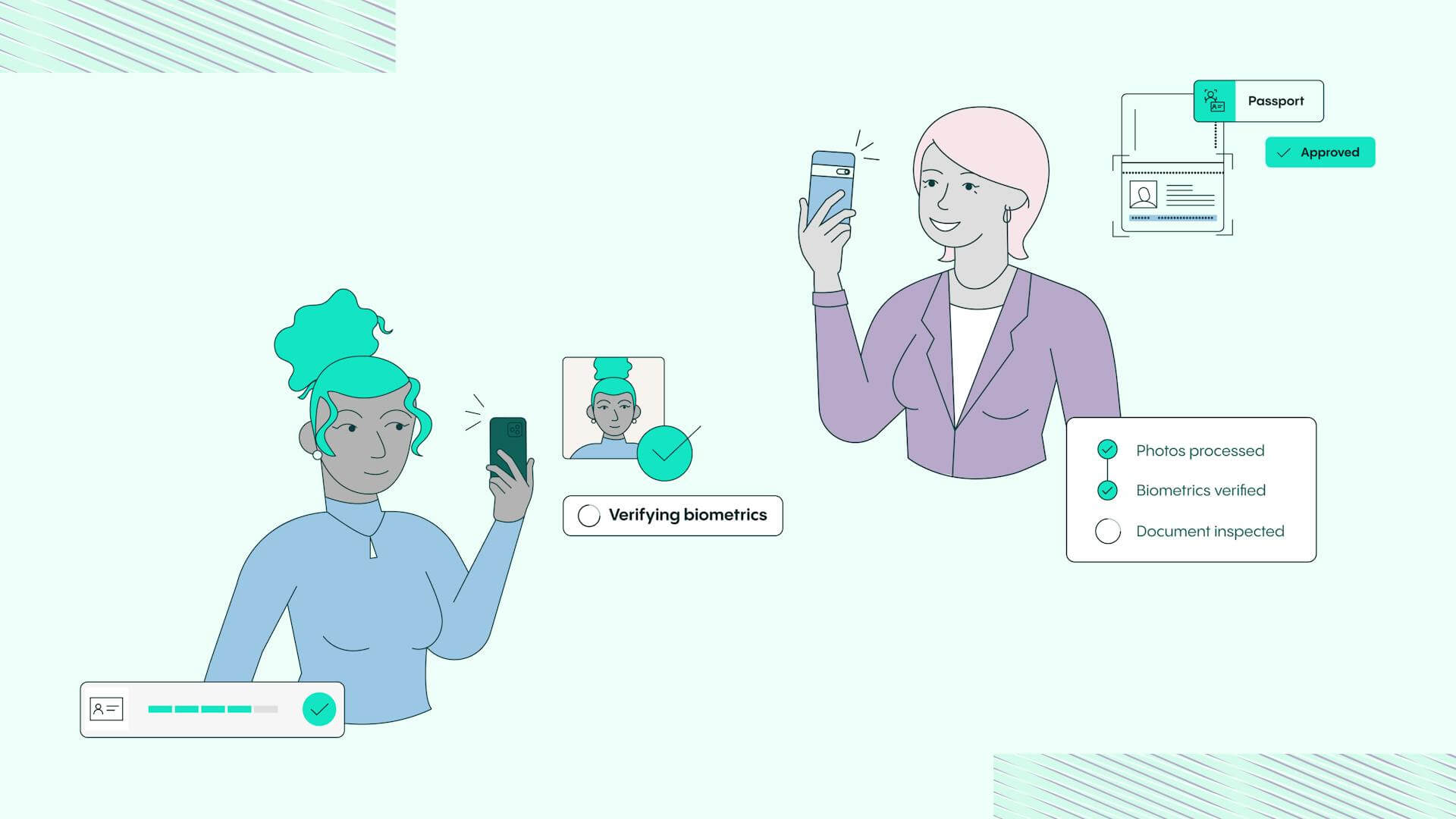
- User Trust: Builds user confidence in the security of their data. Biometric verification solutions are increasingly being adopted to enhance trust.
Zero-Trust Architecture
In a zero-trust model, trust is never assumed and must be continually verified. This approach is crucial for preventing unauthorized access and minimizing potential breaches.
Components of Zero-Trust:
- Micro-Segmentation: Dividing networks into small segments to prevent lateral movement by attackers.
- Least Privilege Access: Users have only the permissions they need to perform their tasks.
Overcoming Common Pitfalls
Despite the benefits, implementing portable identity systems comes with challenges. Here are common pitfalls and how to overcome them:
Privacy Concerns
Users are often wary of how their data is used and shared. Ensuring transparency and providing users with control over their data is paramount. The exploitation of identity verification in tax refund fraud highlights the importance of robust privacy measures.
Scalability Issues
As services grow, so does the complexity of managing identities. Solutions must be scalable, ensuring they can handle increased loads without compromising performance.
Case Studies: Real-World Implementations
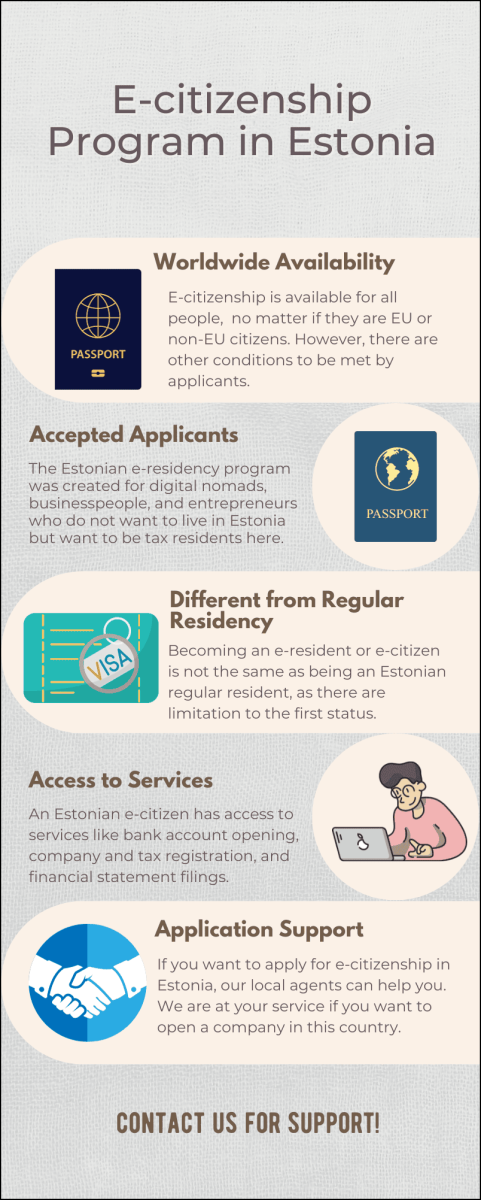
Estonia’s e-Residency Program
Estonia has pioneered digital identity with its e-Residency program, allowing individuals to establish a government-backed digital identity and access services within the EU.
Impact:
- Economic Growth: Attracted entrepreneurs and businesses to the EU.
- Security: Reduced fraud through a robust verification process.
The Blockchain Approach
Companies are leveraging blockchain technology to create secure and immutable identity systems. The transparency and decentralization offered by blockchain make it an ideal candidate for identity verification.
Example:
- Civic: Uses blockchain to secure user identity data and provide access to services without revealing personal information.
Future Trends and Predictions
Looking ahead, the landscape of digital identity is set to evolve with several key trends:
Increased Adoption of Biometrics
Fingerprint and facial recognition technologies are becoming standard for identity verification, offering a layer of security that is difficult to replicate or forge. The Saudi Arabia biometrics market is a testament to the growing reliance on biometric solutions.
Rise of Self-Sovereign Identity
Users will have greater control over their digital identities, deciding what information to share and with whom.
AI and Machine Learning in Identity Verification
AI will play a significant role in analyzing behaviors and patterns to detect fraudulent activities in real-time.
Practical Implementation Guide
Step-by-Step Guide to Implementing a Portable Identity System
- Assess Current Systems: Evaluate existing identity verification processes and identify areas for improvement.
- Choose a Framework: Decide on the technology that best fits your needs, such as DIDs or blockchain.
- Pilot and Test: Implement a pilot program to test the system's efficacy and gather feedback.
- Iterate and Scale: Refine the system based on feedback and scale to accommodate more users and services.
Common Challenges and Solutions
- Interoperability: Ensure that the chosen system can integrate with existing platforms and services.
- User Education: Educate users on the benefits and functionalities of the new system to enhance adoption.
- Regulatory Compliance: Stay informed about regulations affecting digital identity to ensure compliance.

Conclusion: Building a Trustworthy Digital Future
The internet’s trust issues are not insurmountable. By embracing portable identities and leveraging cutting-edge technologies, we can create a more secure and user-friendly digital landscape. Businesses must prioritize identity verification as a core component of their operations, ensuring trust remains at the heart of the internet.
FAQ
What is portable identity?
Portable identity refers to a digital identity that can be used across multiple platforms without the need for repeated verification. This concept aims to simplify user experience and enhance security.
How does decentralized identity work?
Decentralized identity uses technologies like blockchain to allow users to control their digital identities independently. This approach removes the need for centralized authorities and enhances privacy and security.
What are the benefits of multi-factor authentication?
Multi-factor authentication enhances security by requiring users to provide multiple forms of verification. This reduces the risk of unauthorized access and builds user trust in digital services.
How can businesses implement secure identity systems?
Businesses can implement secure identity systems by adopting technologies like DIDs, MFA, and zero-trust architectures. Regular audits and updates to these systems further enhance security.
Why is identity verification important for online transactions?
Identity verification is crucial for ensuring the legitimacy of online transactions. It helps prevent fraud, protects user data, and maintains trust in digital services.
What role does AI play in identity verification?
AI enhances identity verification by analyzing user behaviors and patterns to detect fraudulent activities. Its ability to process large amounts of data quickly makes it an invaluable tool for maintaining security.
Key Takeaways
- Identity verification is essential for maintaining trust online.
- Portable identities can simplify user experiences and enhance security.
- Decentralized identifiers and blockchain are key technologies for secure identity systems.
- Multi-factor authentication and zero-trust architectures are best practices for identity security.
- The future of identity includes self-sovereign identity and AI-driven verification.
Related Articles
- Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]
- Google Unveils AI-Generated Avatars for YouTube Shorts [2025]
- The Analog Renaissance: Why Smartwatches Are Losing Their Cool [2025]
- Hackers Exploiting WhatsApp and Cloud Tools for Silent Computer Takeovers [2025]
- Understanding the Debate Over Age Verification for Online Content [2025]
- Beware: How Hackers Exploit LinkedIn's Job Alerts to Steal Your Login Details [2025]
![The Internet's Trust Dilemma: Why Identity Verification Must Evolve [2025]](https://tryrunable.com/blog/the-internet-s-trust-dilemma-why-identity-verification-must-/image-1-1775817268103.jpg)



