Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]
The recent breach of the Los Angeles Police Department's (LAPD) sensitive files stored in the city attorney's system is a stark reminder of the vulnerabilities that still plague our digital infrastructures. With over 337,000 files stolen, including personnel and internal affairs data, the incident has raised significant concerns about data security, privacy, and the measures needed to prevent such breaches in the future.
TL; DR
- Significant Breach: Over 337,000 LAPD files were stolen, exposing sensitive personnel and internal affairs information.
- Vulnerability Highlighted: The breach underscores the need for robust cybersecurity measures in public sector systems.
- Immediate Actions: Agencies must adopt multi-layered security protocols to protect sensitive data.
- Long-term Strategy: Implementation of zero-trust architectures and continuous monitoring is crucial.
- Bottom Line: Proactive cybersecurity measures are essential to protect public data from future breaches.
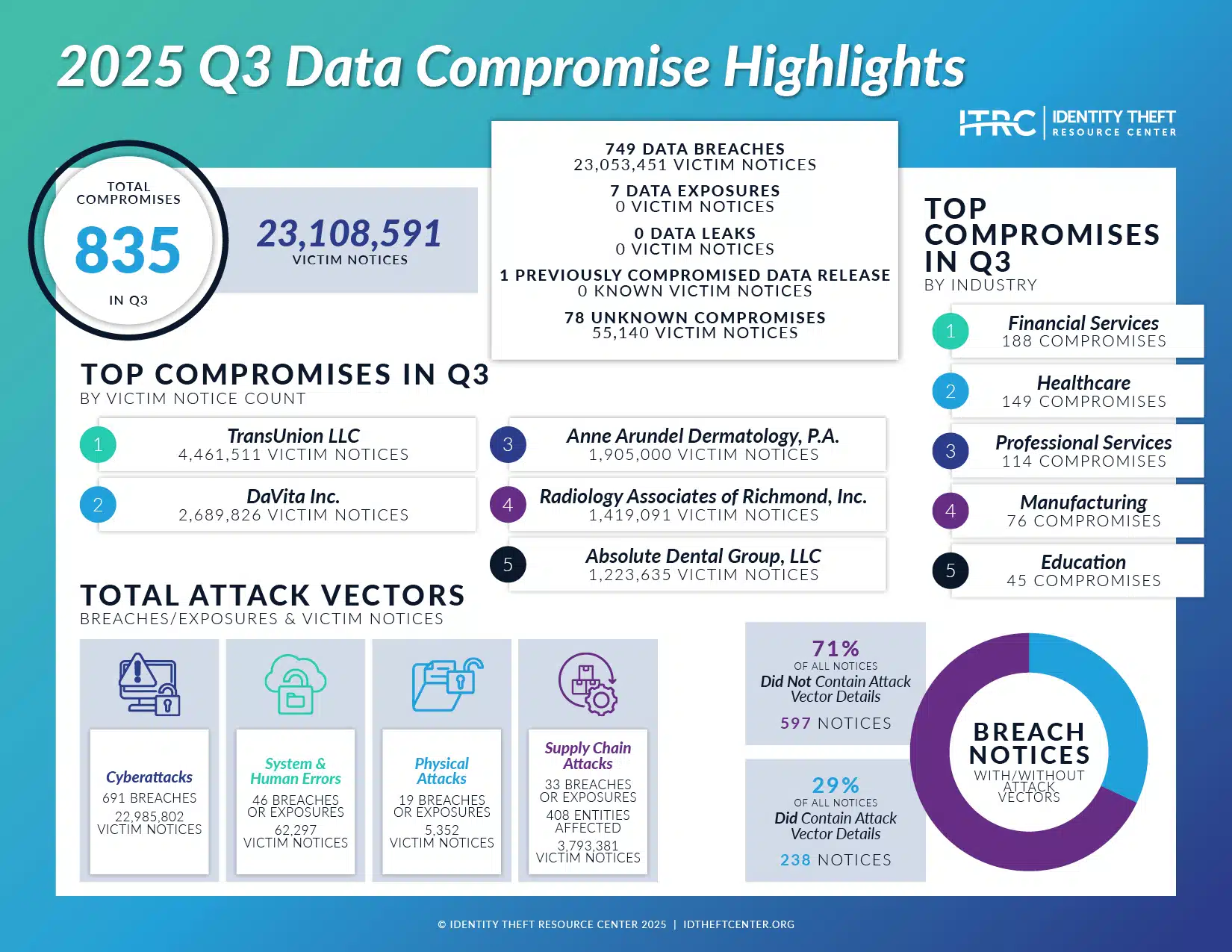
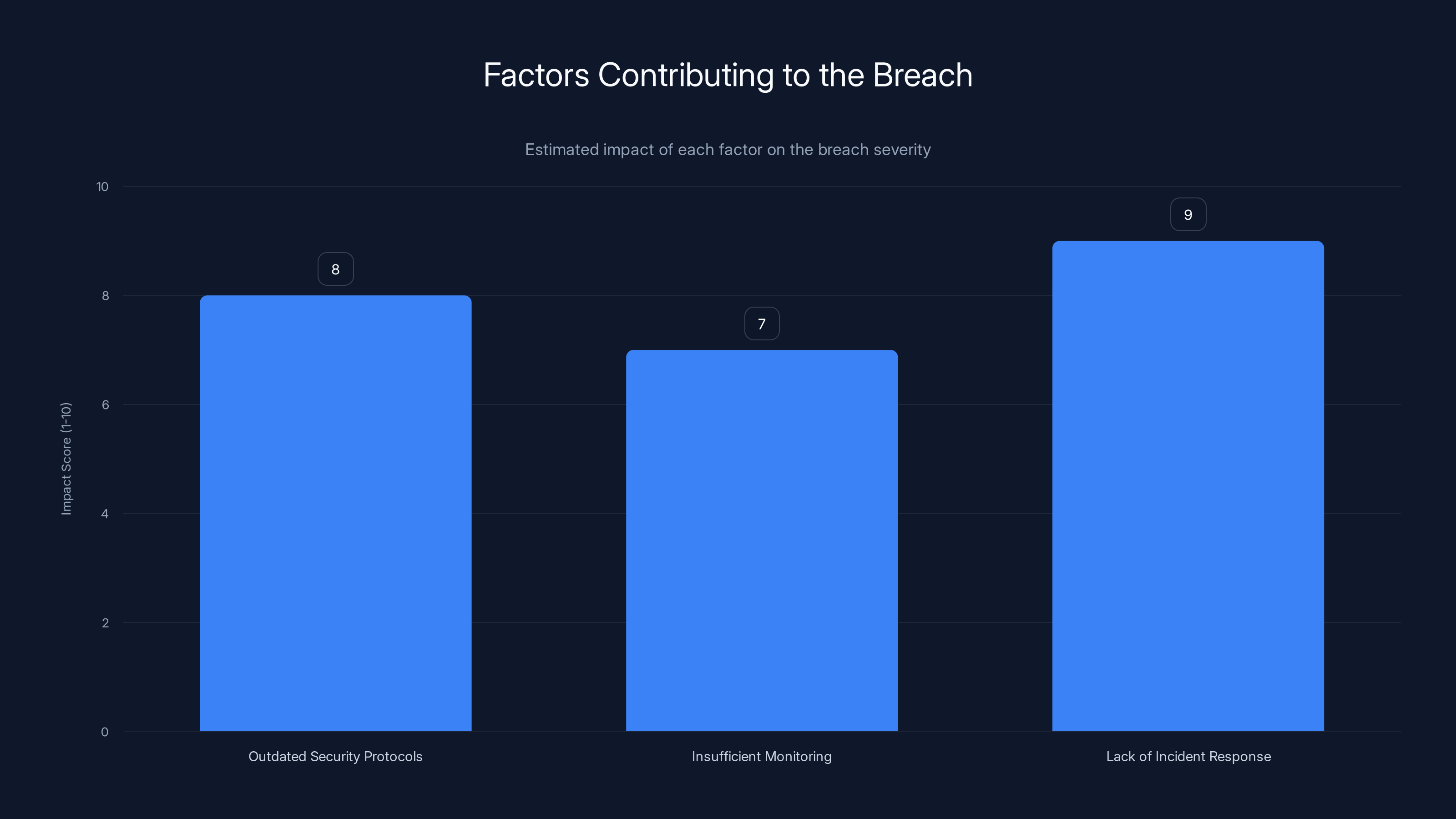
Estimated data shows that outdated security protocols, insufficient monitoring, and lack of incident response significantly contributed to the breach, with impact scores of 8, 7, and 9 respectively.
The Scope of the Breach
In the latest incident, a group known as "World Leaks" managed to infiltrate the LA City Attorney’s Office systems, accessing a trove of sensitive LAPD files. These files included personal details of officers, internal communications, and confidential reports. The breach not only jeopardized individual privacy but also posed a risk to ongoing investigations and the overall integrity of the LAPD.
How Did It Happen?
The breach was a result of a combination of factors, including outdated security protocols, insufficient monitoring, and the lack of a comprehensive incident response plan. Hackers exploited these vulnerabilities to gain unauthorized access.
- Outdated Security Protocols: Many public sector systems still rely on antiquated security measures that are ill-equipped to handle modern cyber threats.
- Insufficient Monitoring: Without real-time monitoring, unusual activities go unnoticed, allowing hackers to exploit systems undetected.
- Lack of Incident Response: A delayed response can exacerbate the impact of a breach, highlighting the importance of having a robust incident response plan.
Immediate Consequences
The immediate fallout from the breach included the exposure of sensitive data, potential harm to ongoing investigations, and a loss of public trust. The LAPD and the city attorney’s office had to quickly address these issues to mitigate further damage.

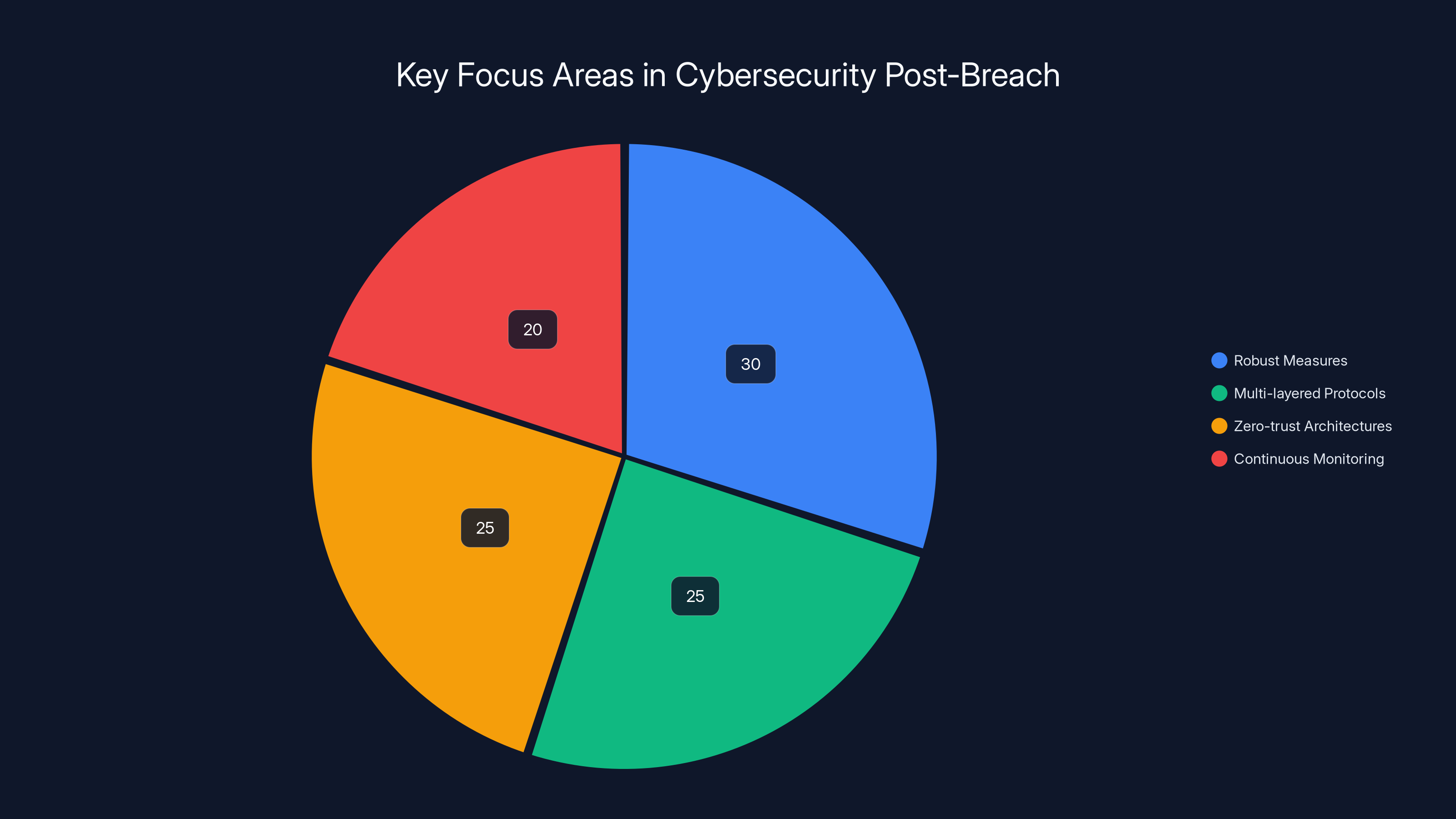
Following the LAPD data breach, the focus on robust cybersecurity measures is estimated to be 30%, with multi-layered protocols and zero-trust architectures each at 25%, and continuous monitoring at 20%. Estimated data.
Cybersecurity Measures: What Should Be Done?
In response to such breaches, it is critical that public sector entities adopt comprehensive cybersecurity strategies. Here are some essential measures:
Multi-Layered Security Protocols
Implementing a multi-layered approach to security can help in creating a robust defense against cyber threats. This includes:
- Firewalls and Intrusion Detection Systems (IDS): Act as the first line of defense, blocking unauthorized access.
- Encryption: Ensures that even if data is accessed, it remains unreadable to unauthorized users.
- Access Controls: Limit access to sensitive information based on user roles and need-to-know basis.
Zero-Trust Architecture
A zero-trust architecture assumes that threats could arise from within and outside the network. This model requires verification for every request as though it originates from an open network.
- Micro-Segmentation: Divides the network into smaller, isolated segments to contain breaches.
- Continuous Verification: Regularly checks user identities and access privileges.
Continuous Monitoring and Threat Intelligence
Proactive monitoring and threat intelligence can help in the early detection of potential threats.
- Real-Time Monitoring: Utilizing advanced tools to continuously monitor network traffic and identify suspicious activities.
- Threat Intelligence Platforms: Collect and analyze data from various sources to predict and prevent cyber threats.
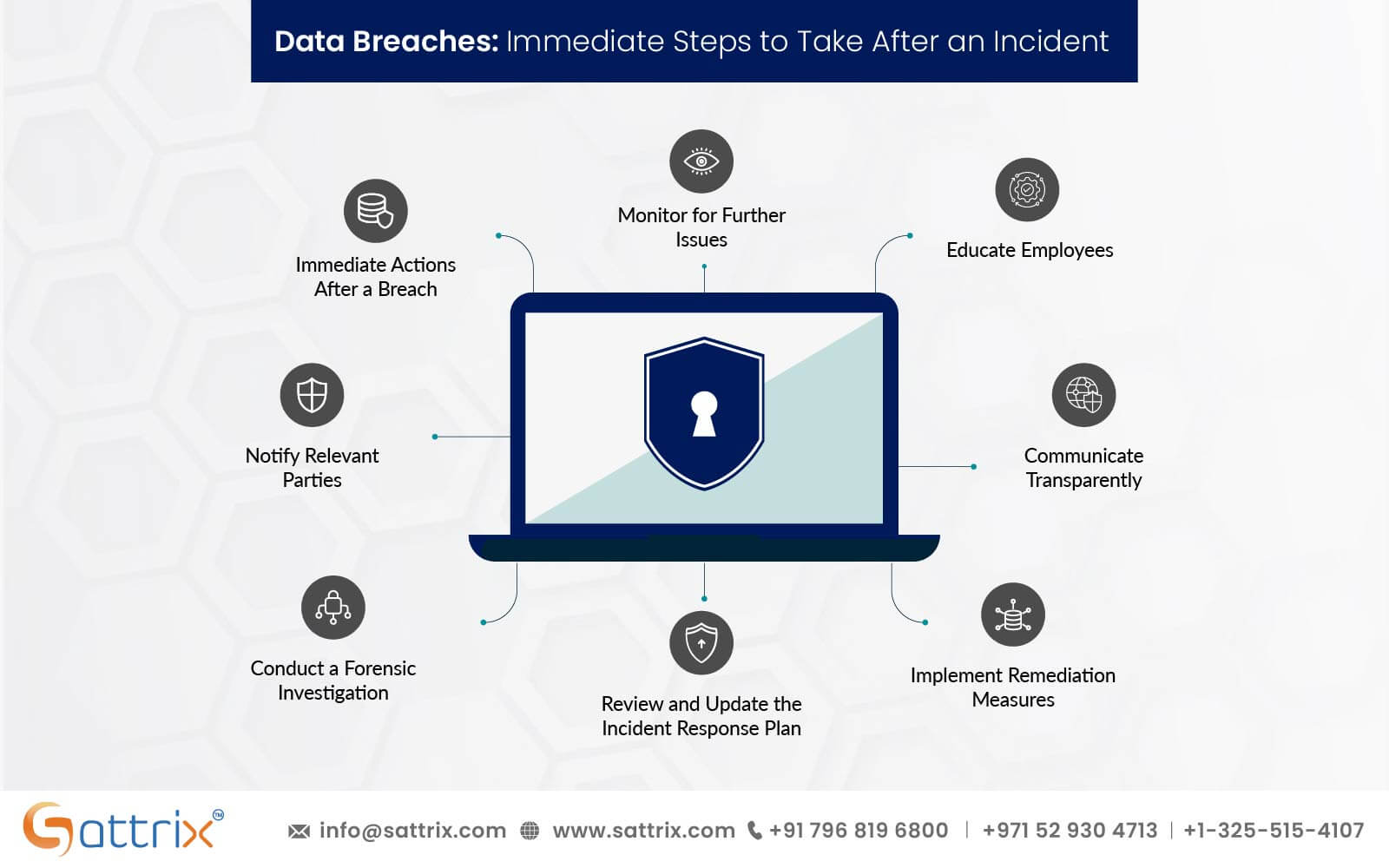
Incident Response and Recovery Plans
Having a well-defined incident response plan ensures a swift and effective reaction to breaches.
- Incident Response Teams: Comprise of cybersecurity experts ready to act immediately upon detection of a breach.
- Regular Drills and Training: Conducting regular simulations to prepare teams for real-world scenarios.
Best Practices in Data Security
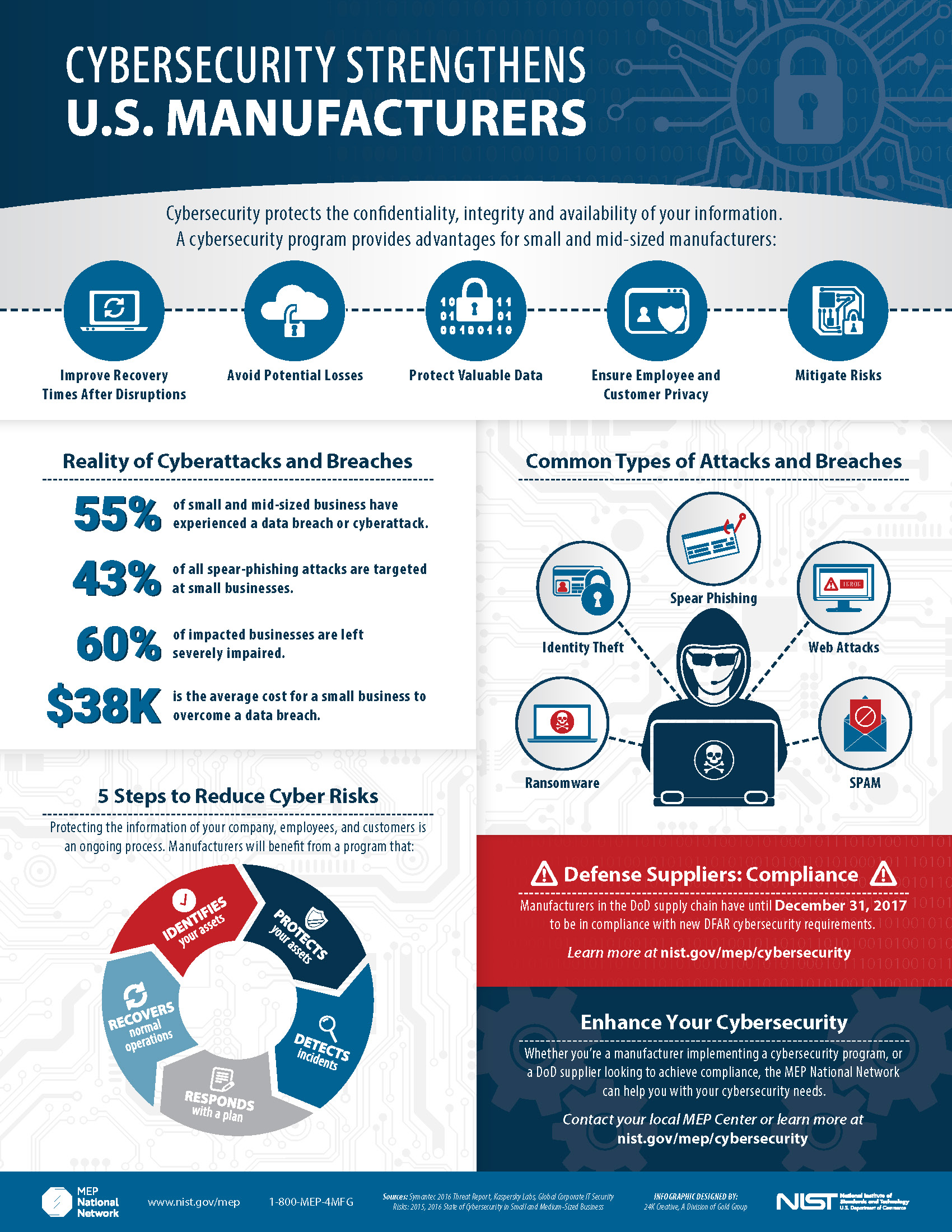
To further bolster data security, organizations should adhere to best practices that have been proven effective:
- Regular Updates and Patch Management: Ensures that all systems and applications are up-to-date with the latest security patches.
- Employee Training and Awareness: Educates staff on identifying and mitigating cyber threats.
- Data Minimization: Reduces the amount of sensitive data collected and retained, minimizing exposure.

Robust security protocols and embracing new technologies are rated as the most important measures for building a secure future. Estimated data.
Common Pitfalls and How to Avoid Them
Despite the best intentions, organizations often fall into common cybersecurity pitfalls. Here’s how to avoid them:
Over-Reliance on Technology
While technology is crucial, over-reliance can lead to complacency. Human oversight and strategic planning are equally important.
Inadequate Funding and Resources
Cybersecurity requires investment in both technology and personnel. Underfunding can leave systems vulnerable.
Failure to Adapt
Cyber threats evolve rapidly. Organizations must be agile and ready to adapt their strategies to new threats.

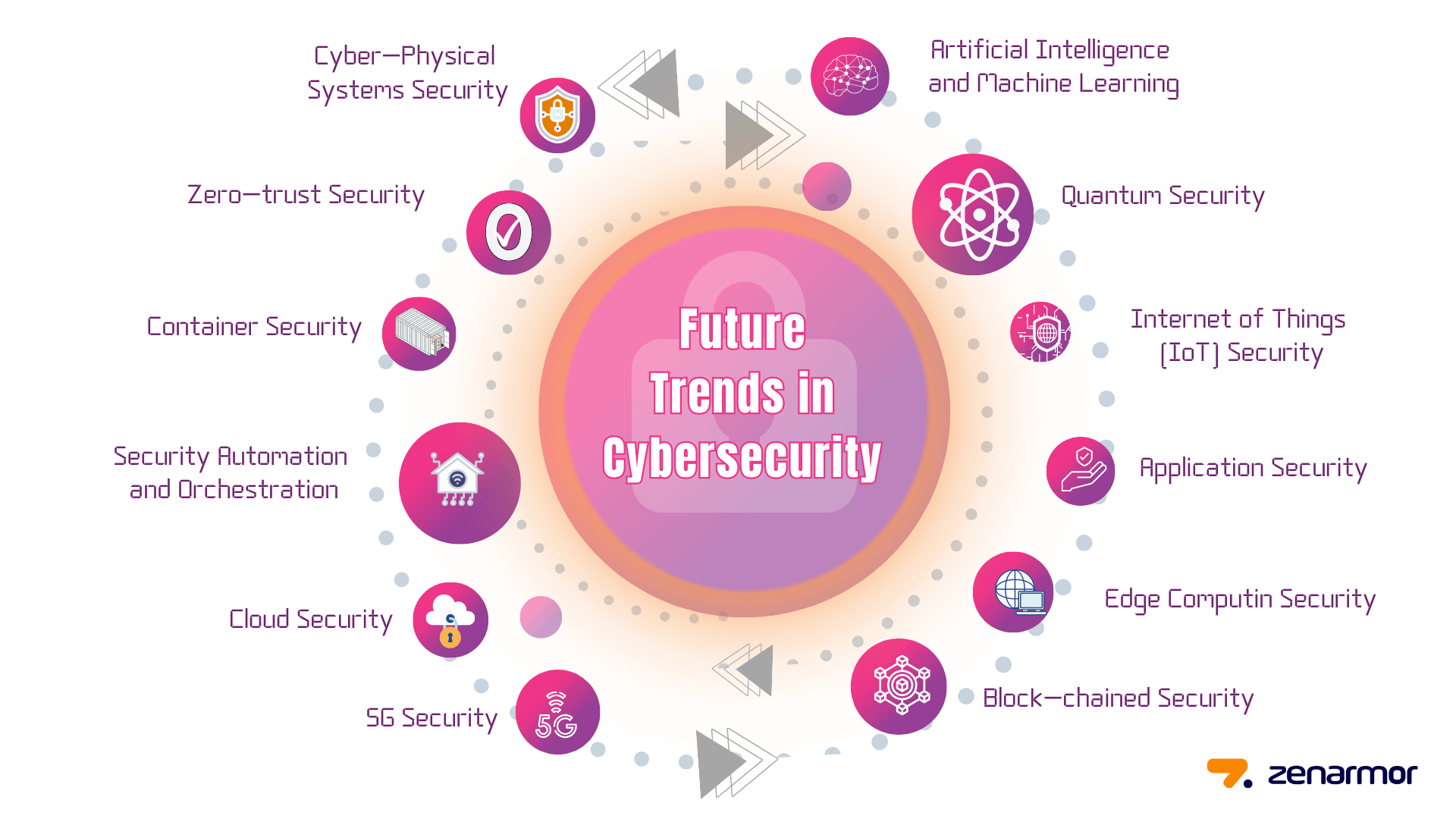
Future Trends in Cybersecurity
As cyber threats continue to evolve, so too must the approaches to combating them. Here are some trends to watch:
Artificial Intelligence and Machine Learning
AI and machine learning are increasingly being used to predict and respond to cyber threats in real-time.
- Automated Threat Detection: AI-driven tools can analyze vast amounts of data to identify threats that would be missed by human analysts.
Blockchain for Data Security
Blockchain technology offers a decentralized approach to data security, making it more difficult for hackers to alter data.
Biometric Authentication
Biometrics provide a more secure form of authentication compared to traditional passwords.
- Facial Recognition: Becoming increasingly common in both public and private sectors.
Conclusion: Building a Secure Future
The LAPD data breach serves as a wake-up call for organizations to reassess and strengthen their cybersecurity measures. By implementing robust security protocols, embracing new technologies, and fostering a culture of security awareness, organizations can better protect themselves against future threats.
It's imperative that both public and private sectors work together to share knowledge and resources, ensuring a more secure digital landscape for all.
Use Case: Automate your security alert management with AI to reduce response times.
Try Runable For FreeFAQ
What is a data breach?
A data breach is an incident where unauthorized individuals gain access to confidential data, potentially compromising privacy and security.
How does zero-trust architecture enhance security?
Zero-trust architecture enhances security by requiring verification for every access request, regardless of its origin, reducing the risk of unauthorized access.
What are the benefits of continuous monitoring?
Continuous monitoring provides real-time insights into network activities, enabling early detection and response to potential threats, thereby minimizing damage.
How can AI improve cybersecurity?
AI can improve cybersecurity by automating threat detection and response, analyzing large datasets for anomalies, and reducing the time taken to identify breaches.
Why is employee training important in cybersecurity?
Employee training is crucial as it equips staff with the knowledge to recognize and respond to potential threats, reducing the likelihood of successful cyber attacks.
What role does encryption play in data security?
Encryption ensures that even if data is accessed by unauthorized individuals, it remains unreadable, thereby protecting sensitive information.
How does blockchain enhance data security?
Blockchain enhances data security by providing a decentralized and tamper-proof ledger, making it difficult for hackers to alter data.
What should be included in an incident response plan?
An incident response plan should include procedures for detecting, responding to, and recovering from breaches, along with designated response teams and regular training exercises.
Why is data minimization important?
Data minimization reduces the amount of sensitive information collected and retained, limiting exposure and potential damage in the event of a breach.
How can public and private sectors collaborate on cybersecurity?
Public and private sectors can collaborate by sharing threat intelligence, resources, and best practices, enhancing collective security and resilience against cyber threats.
Key Takeaways
- Over 337,000 LAPD files were stolen, highlighting severe security vulnerabilities.
- Organizations must adopt multi-layered security protocols to protect sensitive data.
- Zero-trust architectures and continuous monitoring are crucial for future security.
- AI and blockchain technologies offer promising advancements in cybersecurity.
- Public and private sectors need to collaborate on cybersecurity strategies.
Related Articles
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]
- The Alinto Data Breach: Lessons in Cybersecurity for Enterprises [2025]
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
- Mac Malware Defense: Safeguarding Against Evolving Threats [2025]
![Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]](https://tryrunable.com/blog/understanding-the-lapd-data-breach-lessons-and-future-safegu/image-1-1775759811149.jpg)



