The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]
In the digital age, the landscape of cyber hacking has evolved dramatically. Traditionally, cyber-attacks were primarily driven by financial motivations. However, a shift is occurring where hackers increasingly seek clout and recognition over cash. This article delves into this trend, exploring the motivations behind modern cyber-attacks, the methods employed, and how individuals and organizations can protect themselves.
TL; DR
- Clout over Cash: Modern hackers often prioritize reputation and influence within hacking communities over financial gain.
- Diverse Motivations: Cyber-attacks today are motivated by political, social, and ideological reasons beyond mere monetary theft, as highlighted in a recent study on lone actors.
- Evolving Tactics: Attack methods now include sophisticated techniques like ransomware, DDoS attacks, and supply chain compromises, as reported by IBM X-Force.
- Increased Frequency: The frequency of cyber-attacks is rising, affecting both small businesses and large enterprises, according to CYFIRMA's intelligence report.
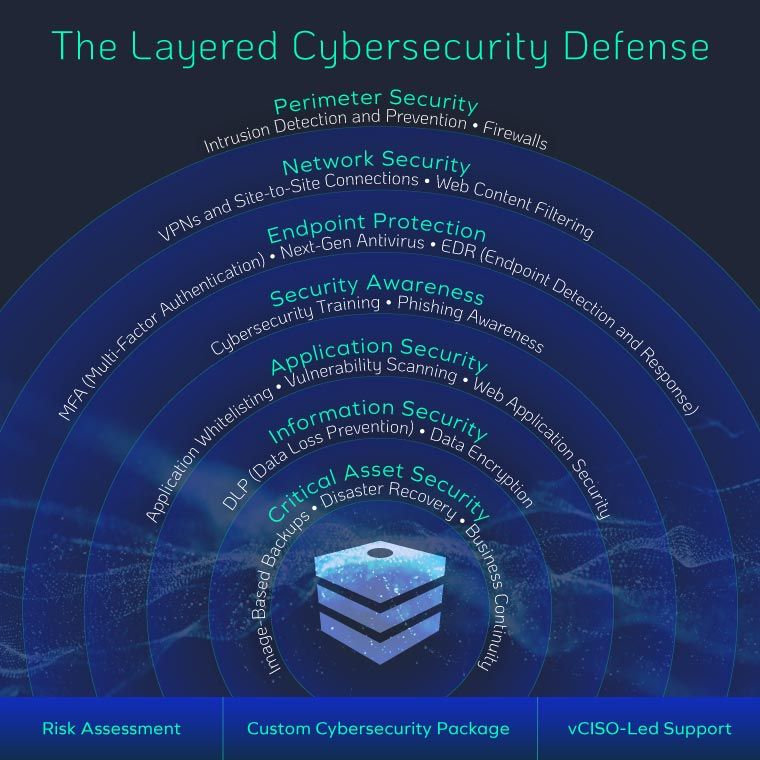
- Enhanced Defense Strategies: Organizations must adopt advanced cybersecurity measures to counteract these evolving threats, as discussed in the San Diego Business Journal.
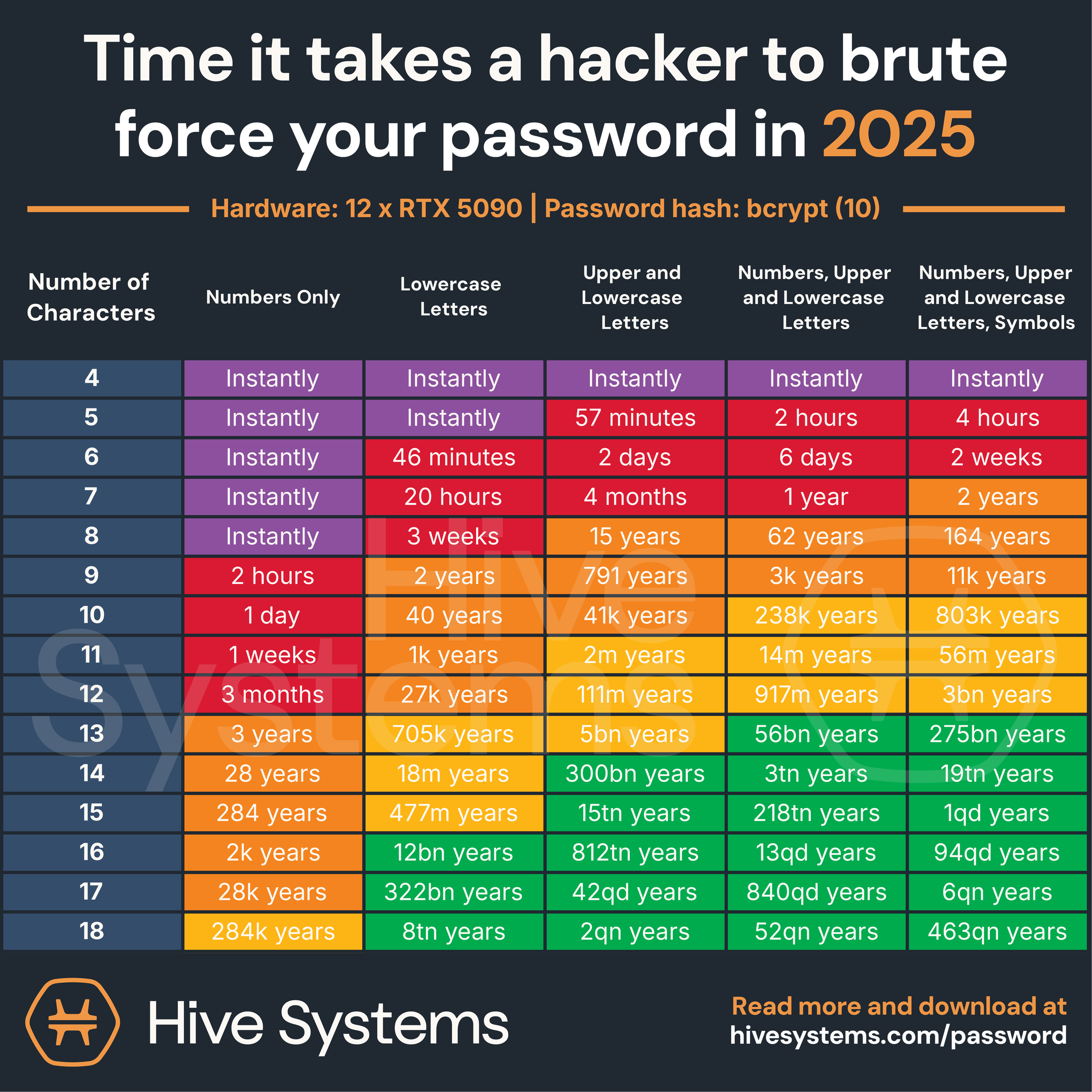
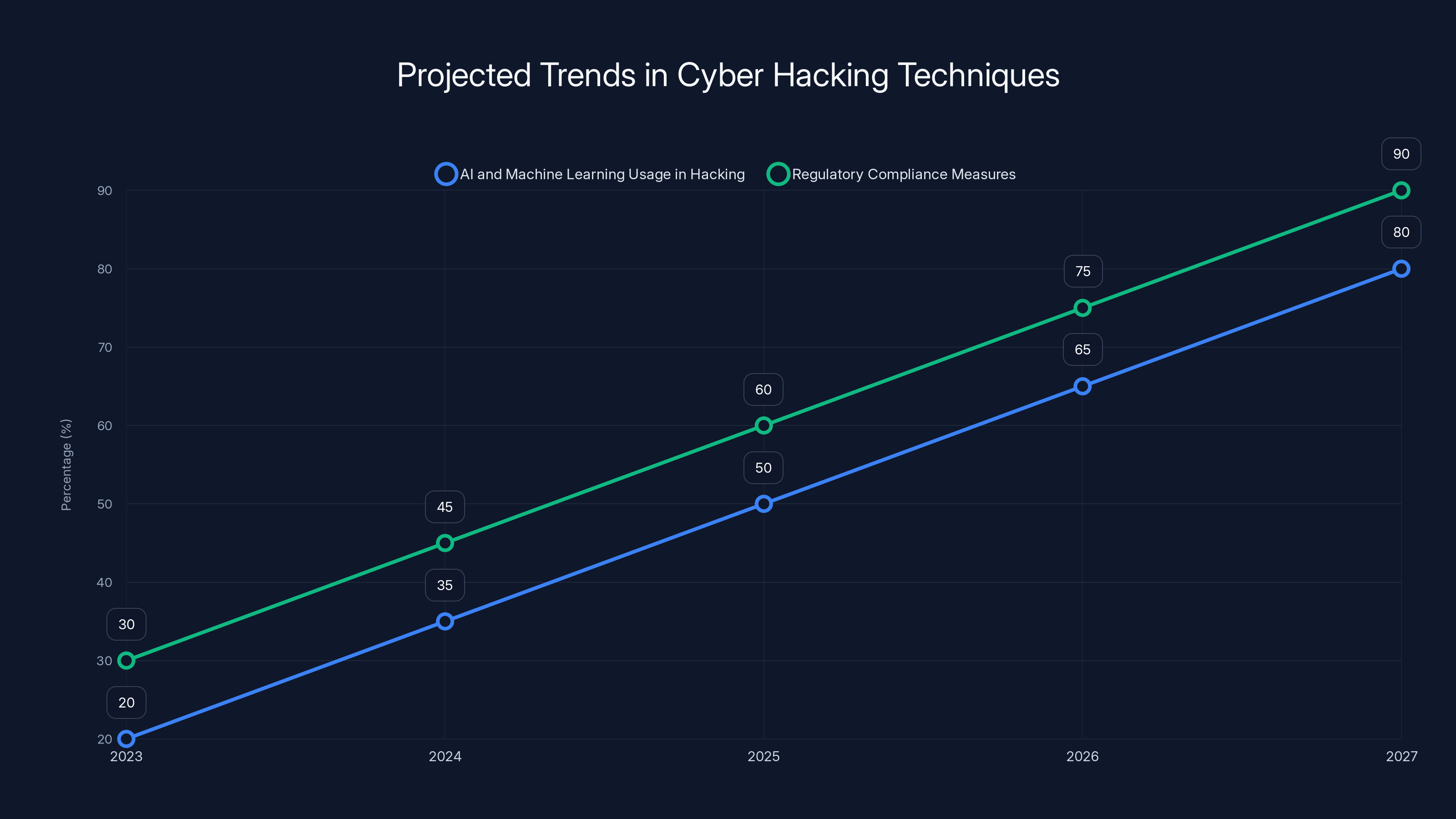
The use of AI and machine learning in cyber hacking is projected to increase significantly, alongside growing regulatory compliance measures. Estimated data based on current trends.
Understanding the Modern Cyber Hacker
The Shift to Clout and Recognition
In recent years, the profile of the typical cyber hacker has changed. While financial gain remains a significant driver, many hackers now seek clout—recognition and status within their communities. This shift is evident in the rise of hacktivist groups and individuals who prioritize the impact and notoriety of their attacks over direct financial rewards.
Example: Groups like Anonymous have gained fame not just for their hacking prowess but for their ability to disrupt and influence public opinion and political outcomes.
Psychological Motivations
The desire for clout is often linked to psychological motivations such as the thrill of the challenge, the satisfaction of outsmarting security systems, and the prestige of being recognized as a top hacker. For many, the prestige associated with high-profile hacks is more valuable than any monetary reward.

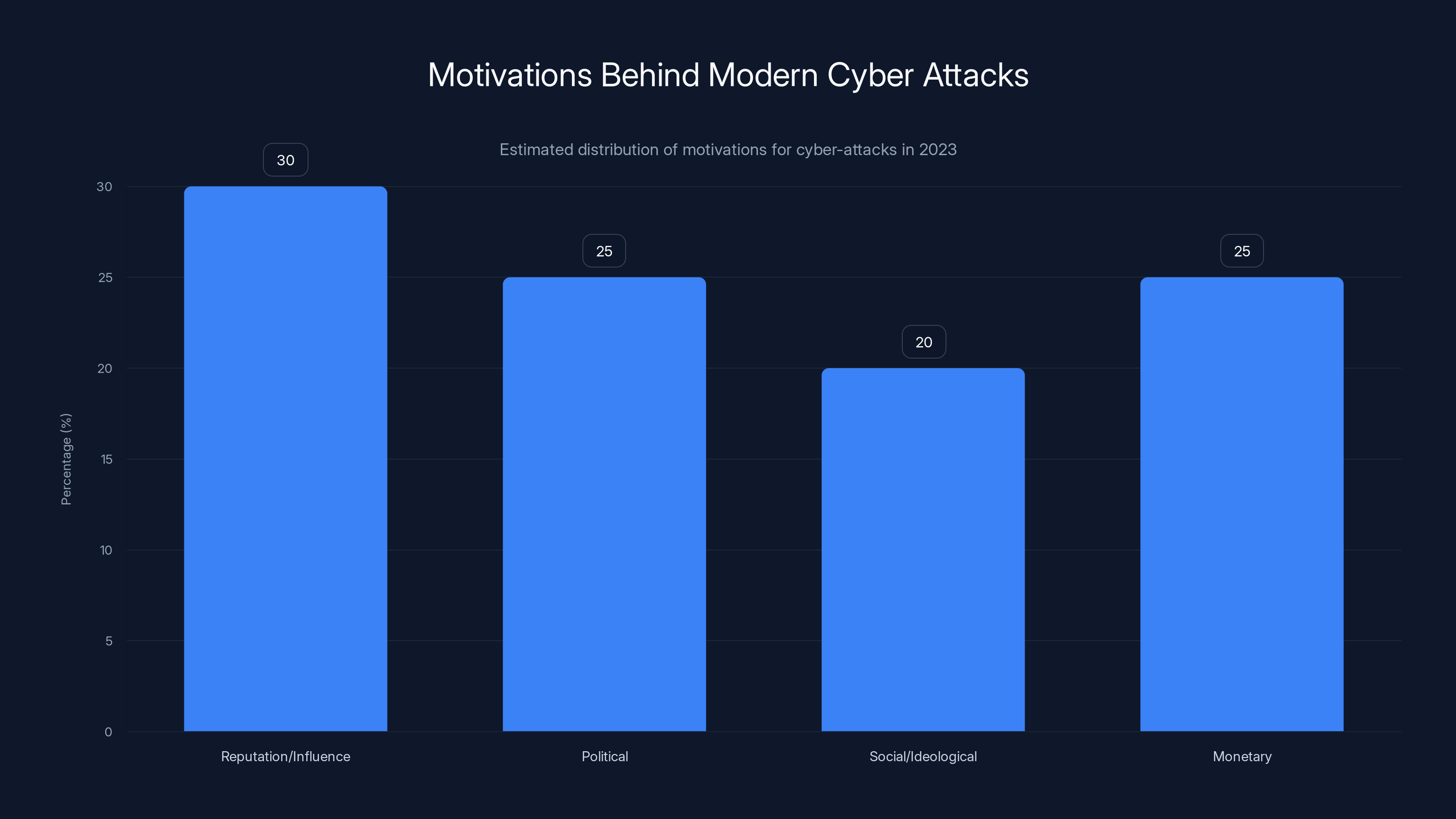
Modern hackers are increasingly driven by reputation and influence, with political and social motivations also significant. Estimated data.
Methods and Tactics Employed by Modern Hackers
Ransomware Attacks
Ransomware has become a favored tool among hackers seeking notoriety. These attacks not only demand ransom from victims but also generate media coverage, as noted in Cybersecurity Ventures' report.
Real-World Example: The Wanna Cry attack in 2017 affected hundreds of thousands of computers worldwide, bringing widespread attention to the hackers responsible.
Distributed Denial of Service (DDoS) Attacks
DDoS attacks are used to overwhelm and cripple websites or networks. They are often employed by hackers seeking to make a statement or demonstrate their capabilities.
Technical Insight: DDoS attacks leverage botnets—networks of compromised computers—to flood a target with traffic.
Supply Chain Attacks
Supply chain attacks involve compromising a supplier to infiltrate a larger target. This method is increasingly popular due to the complexity and potential impact, as demonstrated by the IBM X-Force report.
Case Study: The Solar Winds attack in 2020 showed how supply chain vulnerabilities can lead to widespread breaches.

Protecting Against Evolving Cyber Threats
Implementing Advanced Security Protocols
Organizations need to adopt a multi-layered security approach to defend against sophisticated attacks. This includes:
- Endpoint Detection and Response (EDR): Continuously monitors and responds to threats at endpoints.
- Network Segmentation: Limits the spread of malware by isolating different segments of a network.
- Regular Software Updates: Ensures that all systems are patched with the latest security updates.
Enhancing Employee Awareness
Human error remains a significant vulnerability. Regular training can help employees recognize phishing attempts and other social engineering attacks.
Best Practice: Conduct simulated phishing exercises to test and improve employee response to potential threats.
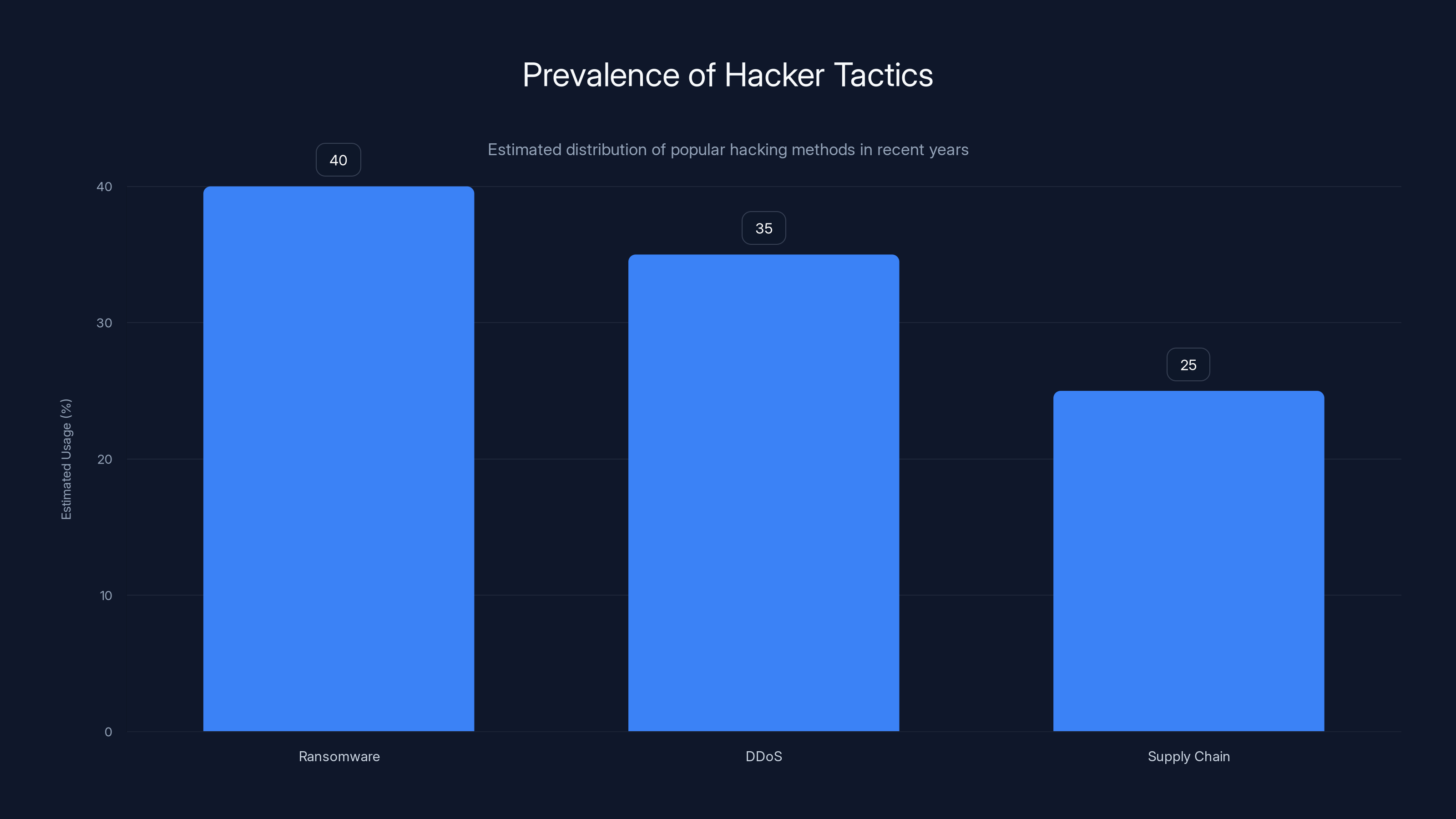
Ransomware attacks are estimated to be the most prevalent method used by hackers, followed by DDoS and supply chain attacks. Estimated data based on recent trends.
Future Trends in Cyber Hacking
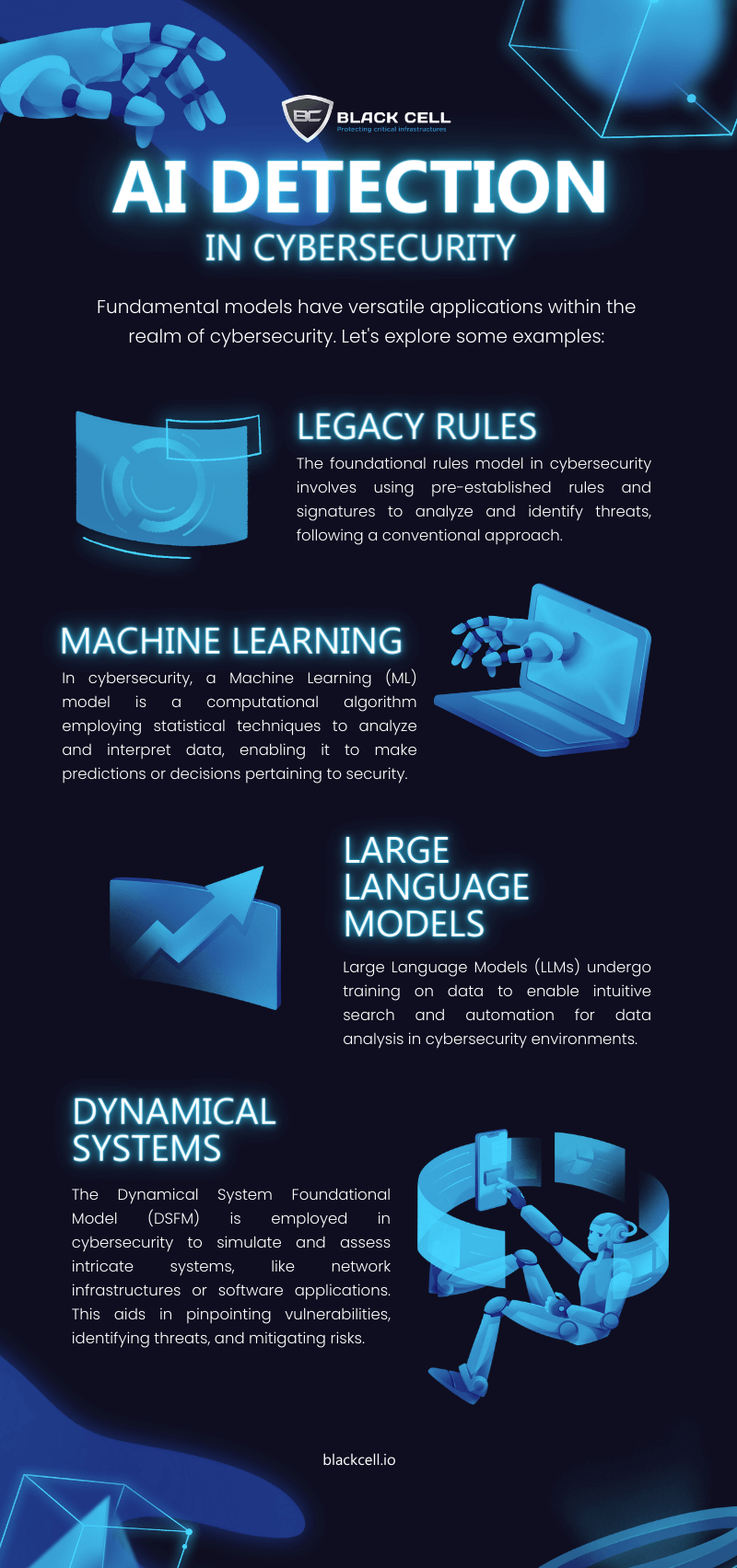
Rise of AI and Machine Learning
Hackers are increasingly using AI and machine learning to automate attacks and improve their effectiveness. These technologies can analyze vast amounts of data to identify vulnerabilities faster than traditional methods.
Expert Quote: “AI is a double-edged sword in cybersecurity—it can enhance defenses but also empower attackers.” — Bruce Schneier
Increased Regulation and Compliance
Governments are implementing stricter regulations to enhance cybersecurity standards. Compliance with frameworks like GDPR and CCPA is becoming mandatory for businesses operating in affected regions, as highlighted in HIPAA Journal's report.
Impact: Non-compliance can result in hefty fines and legal repercussions, emphasizing the importance of robust cybersecurity practices.
Common Pitfalls and Solutions
Overreliance on Traditional Security Measures
Many organizations still rely heavily on outdated security measures, making them vulnerable to advanced attacks.
Solution: Invest in next-generation security tools that provide real-time threat intelligence and automated response capabilities.
Lack of Incident Response Planning
Without a well-defined incident response plan, organizations struggle to respond effectively to breaches.
Solution: Develop and regularly update an incident response plan that includes steps for identification, containment, eradication, and recovery.
Conclusion: Embracing a Proactive Cybersecurity Posture
The rise of hackers who value clout over cash presents new challenges for cybersecurity. As their tactics evolve, so must our defenses. By understanding the motivations and methods of modern hackers, organizations can better protect themselves from becoming the next headline.
Bottom Line: To stay ahead in the cybersecurity arms race, continuous adaptation and proactive defense strategies are essential.
FAQ
What drives modern cyber hackers?
Modern cyber hackers are often motivated by clout and recognition within their communities, in addition to financial gain.
How have cyber-attack methods evolved?
Cyber-attack methods have become more sophisticated, including techniques like ransomware, DDoS attacks, and supply chain compromises.
How can organizations protect against modern cyber threats?
Organizations can protect themselves by implementing advanced security protocols, enhancing employee awareness, and regularly updating their incident response plans.
What role does AI play in cyber hacking?
AI is used by hackers to automate and enhance attacks, but it also offers potential for improving cybersecurity defenses.
Why is regulation important in cybersecurity?
Regulation ensures that organizations adhere to cybersecurity standards, protecting data and reducing the risk of breaches.
What are common pitfalls in cybersecurity?
Common pitfalls include overreliance on traditional security measures and lack of an effective incident response plan.
Key Takeaways
- Hackers are increasingly motivated by clout and recognition over financial gain.
- Cyber-attack methods continue to evolve, with a focus on sophisticated techniques.
- Organizations must adopt advanced security protocols to combat modern threats.
- AI is both a tool for attackers and a potential defense mechanism.
- Regulation and compliance play critical roles in enhancing cybersecurity standards.
Related Articles
- Cyber-Resilience for the Modern Data Center: Strategies and Best Practices [2025]
- Databricks' Strategic Acquisition: A Deep Dive Into Lakewatch and AI Security [2025]
- Inside the World of Cyber Espionage: How Iranian Hackers Exploit Telegram for Global Data Breaches [2025]
- Exposing the Visibility Gap: Unleashing the Full Potential of Agentic SOC [2025]
- How Biometric Authentication Can Tackle Bot Problems on Social Platforms [2025]
- The Future of Online Privacy: Age Checks and VPN Regulations [2025]
![The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]](https://tryrunable.com/blog/the-rise-of-the-cyber-hacker-does-clout-matter-more-than-cas/image-1-1774452883352.jpg)



