Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]
The landscape of enterprise security has evolved dramatically over the past few decades. Where firewalls and antivirus software once sufficed, businesses now face a complex array of threats that demand more sophisticated defenses. The rise of cyber threats, insider threats, and the need for compliance have made intelligence and investigative capabilities crucial for protecting enterprise assets. In this article, we'll explore the reasons behind this shift and how organizations can implement these capabilities effectively.
TL; DR
- Evolving Threat Landscape: Cyber threats are more sophisticated, requiring advanced intelligence.
- Insider Threats: These are on the rise, necessitating robust investigative tools.
- Regulatory Compliance: Intelligence assists in meeting compliance requirements.
- Proactive Defense: Shifting from reactive to proactive security measures.
- Future Trends: AI and machine learning will enhance investigative capabilities.

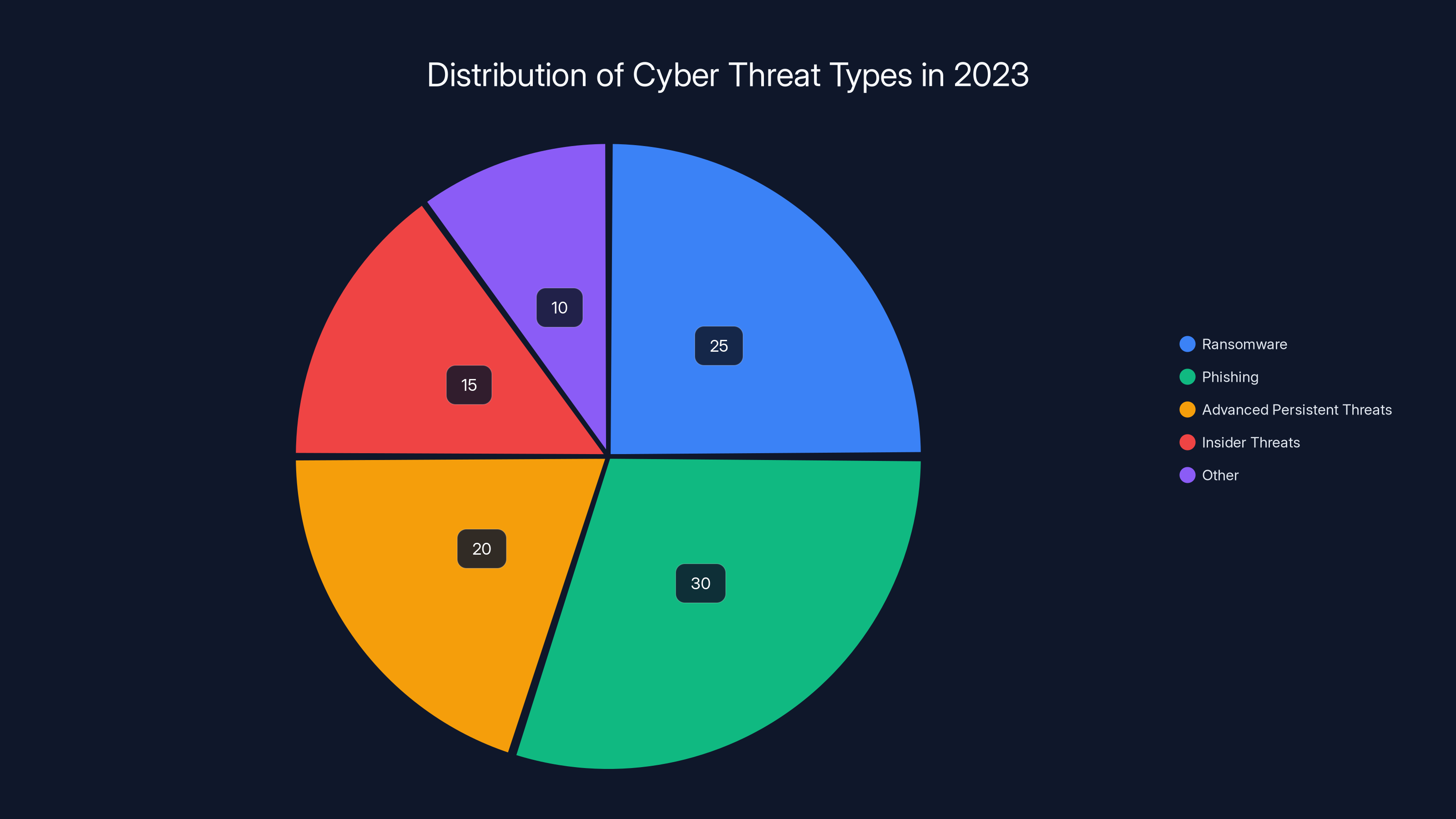
Phishing attacks are the most prevalent, accounting for 30% of threats, followed by ransomware at 25%. Insider threats are significant at 15%. Estimated data.
The Evolving Threat Landscape
In the past, enterprise security focused primarily on perimeter defenses. However, the nature of threats has evolved. Cyber attackers are more sophisticated, and their tactics constantly change. As noted by Cybersecurity Ventures, cybercrime is expected to cost the world $10.5 trillion annually by 2025.
Cyber Threats
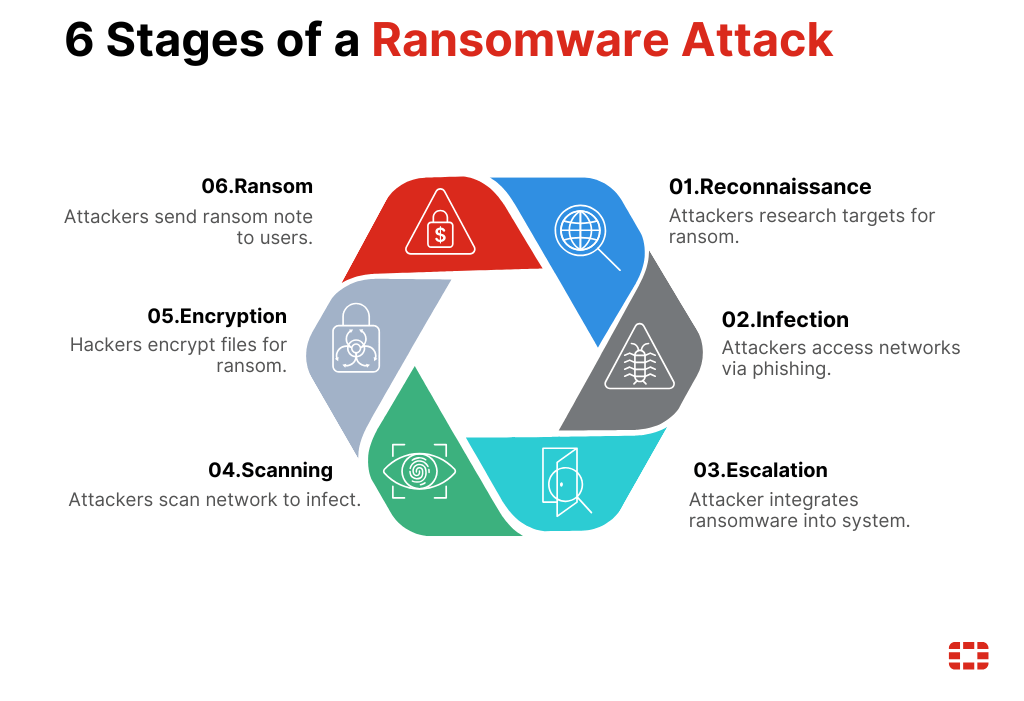
Cyber threats today are not just about viruses and worms. They include ransomware, phishing attacks, and advanced persistent threats (APTs). These threats are often orchestrated by well-funded cybercriminal groups or even nation-states. This evolution necessitates a proactive approach to security. According to IBM's insights, AI-driven threats are becoming increasingly prevalent, requiring organizations to adapt quickly.
Example: In 2021, the Colonial Pipeline ransomware attack highlighted the vulnerabilities in critical infrastructure, emphasizing the need for advanced threat intelligence.
Insider Threats
Insider threats are becoming more prevalent and dangerous. According to the Ponemon Institute, insider threats account for 60% of all data breaches. Employees or contractors with access to sensitive information can cause significant damage, whether intentionally or accidentally.
Example: An employee at a financial institution unintentionally leaked sensitive customer data due to a phishing attack, demonstrating the need for robust internal controls and monitoring.
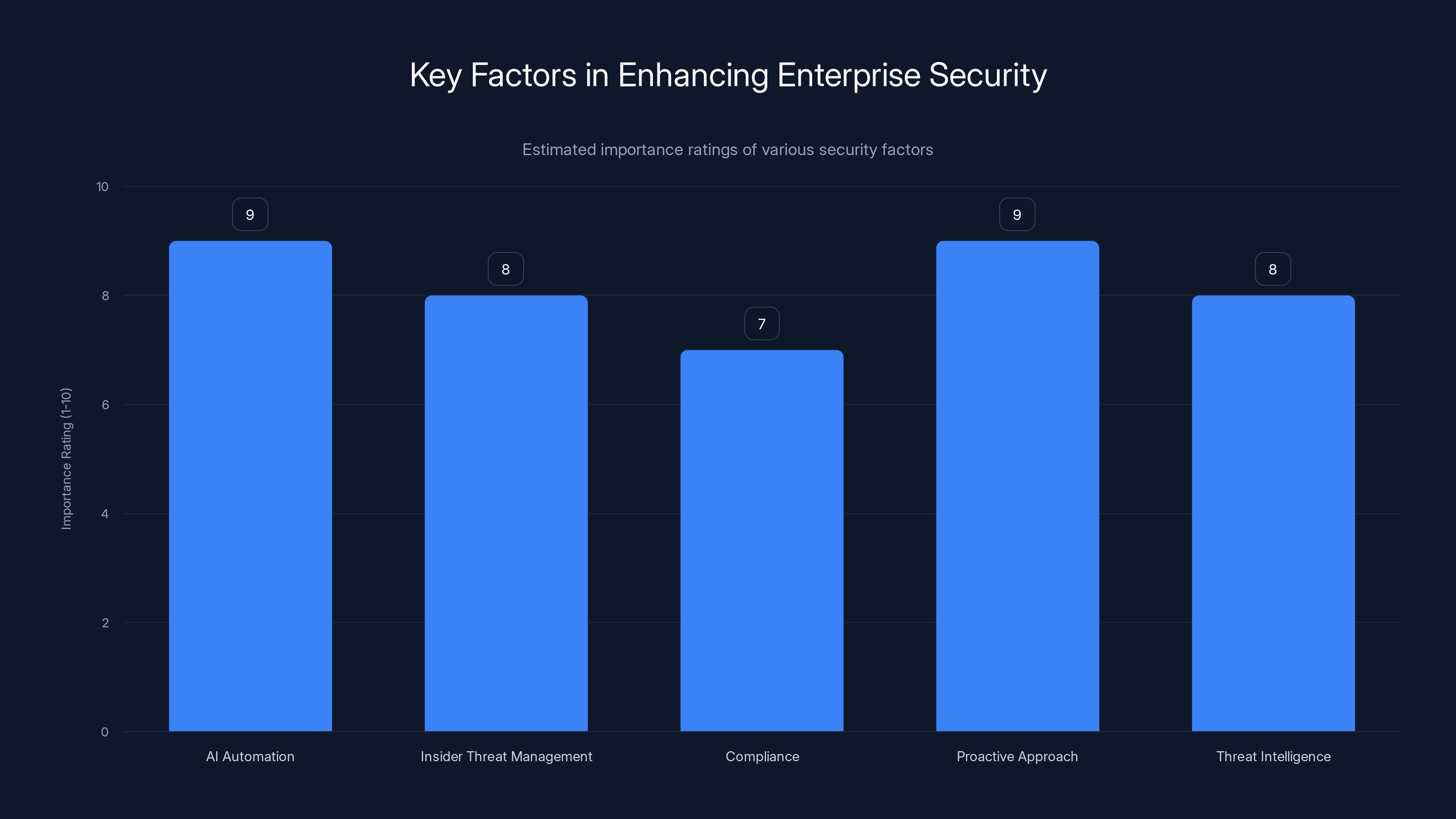
AI automation and a proactive approach are rated highest in importance for enhancing enterprise security. (Estimated data)
The Role of Intelligence in Enterprise Security
Intelligence in the context of enterprise security refers to the collection and analysis of information to anticipate, identify, and respond to threats. This intelligence can be gathered from a variety of sources, including:
- Threat Intelligence Feeds: These provide real-time data on emerging threats and vulnerabilities.
- Behavioral Analysis: Monitoring user behavior to detect anomalies that may indicate a breach.
- Open Source Intelligence (OSINT): Utilizing publicly available information to identify potential threats.
Best Practices for Implementing Intelligence Capabilities
- Integrate Threat Intelligence Platforms: Use platforms like Recorded Future to gather and analyze threat data.
- Conduct Regular Security Audits: Frequent audits can identify vulnerabilities before they are exploited.
- Collaborate with Industry Peers: Sharing threat intelligence across industries can improve overall defense.

Investigative Capabilities: The Need for In-Depth Analysis
Investigative capabilities involve analyzing incidents post-occurrence to understand their nature, impact, and origin. This helps in preventing future occurrences by refining security measures.
Key Elements of an Effective Investigative Framework
- Incident Response Teams: Dedicated teams to handle security incidents promptly.
- Forensic Tools: Tools like En Case for digital forensics and evidence collection.
- Comprehensive Logging: Maintaining detailed logs is essential for post-incident analysis.

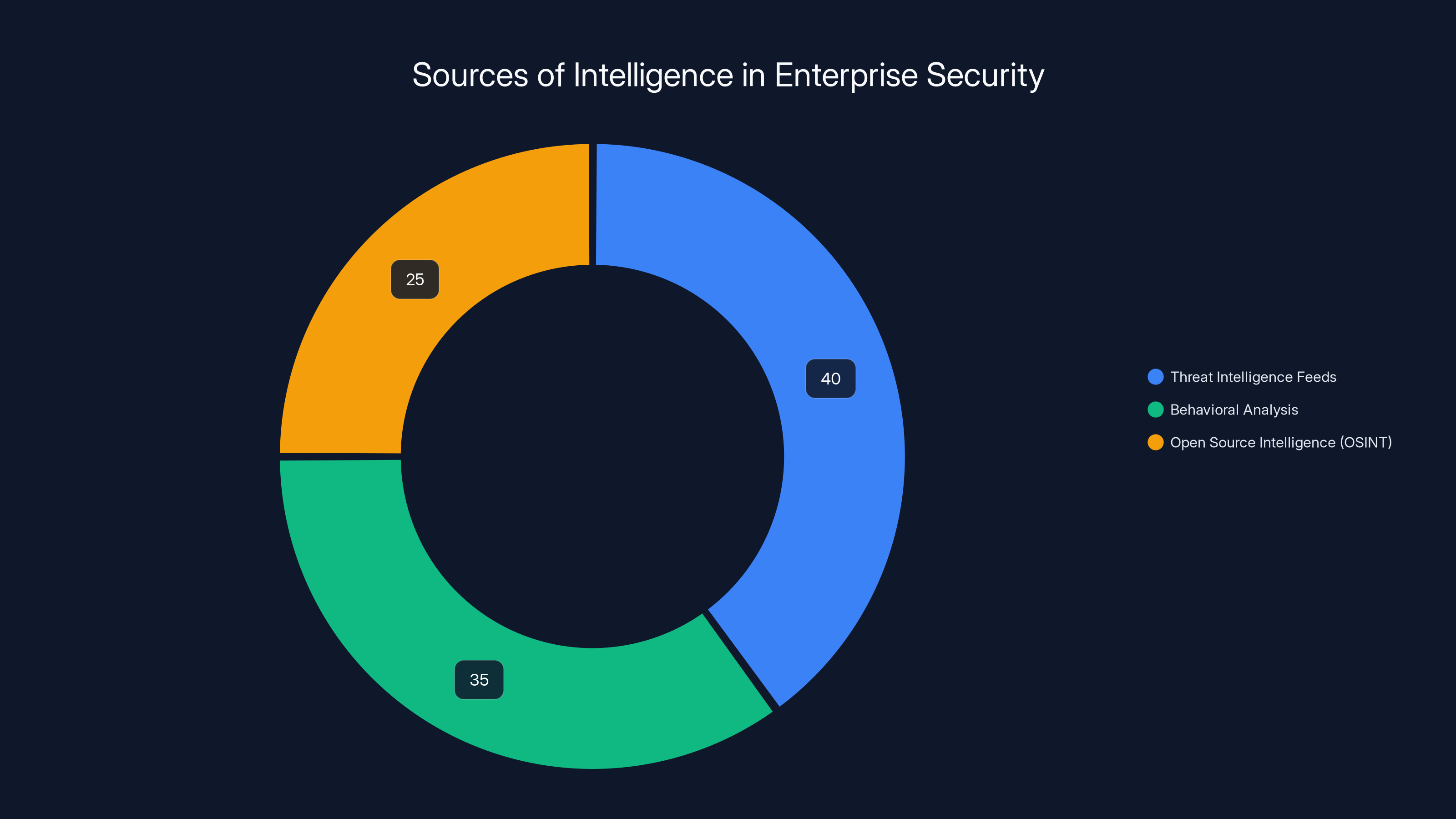
Threat Intelligence Feeds are estimated to contribute the most to enterprise security intelligence, followed by Behavioral Analysis and OSINT. (Estimated data)
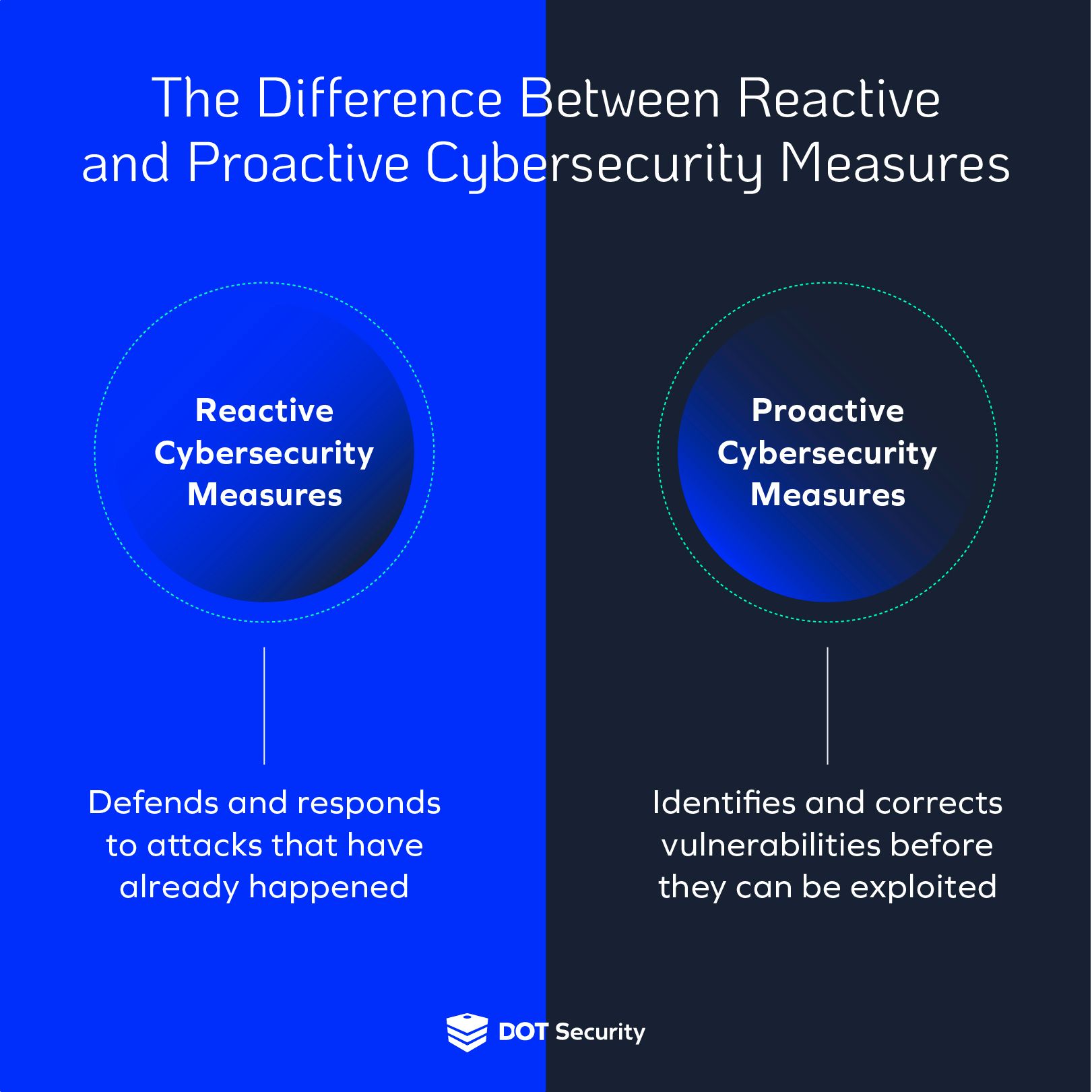
Proactive vs. Reactive Security
Traditionally, security measures were reactive, addressing threats as they arose. Today, a proactive approach is essential, leveraging intelligence to anticipate threats before they occur.
Transitioning to Proactive Security
- Adopt a Risk-Based Approach: Focus resources on the most significant threats.
- Utilize Predictive Analytics: Predictive tools can forecast potential security incidents.
- Implement Continuous Monitoring: Real-time monitoring to detect and mitigate threats instantly.
The Role of AI and Machine Learning
AI and Machine Learning are transforming enterprise security by enhancing both intelligence and investigative capabilities. These technologies can process vast amounts of data quickly, identifying threats and anomalies that human analysts might miss.
AI-Driven Security Solutions
- Automated Threat Detection: AI can identify and respond to threats in real-time.
- Behavioral Analytics: Machine learning models analyze user behavior to detect deviations.
- Predictive Modeling: AI predicts potential threats based on historical data.
Example: Darktrace uses AI to detect threats in real-time, reducing response times and minimizing damage.
Regulatory Compliance and Security Intelligence
Regulations such as GDPR, HIPAA, and CCPA require organizations to protect sensitive data. Intelligence capabilities help in achieving compliance by ensuring that security measures meet regulatory standards.
Compliance Best Practices
- Data Classification: Identify and classify data to apply appropriate security measures.
- Regular Compliance Audits: Conduct audits to ensure ongoing compliance.
- Employee Training: Educate employees on compliance requirements and security best practices.

Common Pitfalls and Solutions
Pitfalls
- Overreliance on Technology: Technology alone cannot solve all security challenges.
- Lack of Skilled Personnel: A shortage of skilled security professionals can hinder implementation.
- Inadequate Incident Response Plans: Without a plan, responses to incidents can be delayed.
Solutions
- Balance Technology and Human Expertise: Use technology to enhance, not replace, human intelligence.
- Invest in Training: Provide ongoing training for security personnel.
- Develop Comprehensive Incident Response Plans: Ensure plans are well-documented and regularly updated.

Future Trends in Enterprise Security
Looking ahead, several trends are likely to shape the future of enterprise security:
- Increased Use of Blockchain: Blockchain can enhance data integrity and security.
- Expansion of Zero Trust Architecture: This approach assumes that threats could be internal or external, requiring verification at every stage.
- Growth of Managed Security Services: Outsourcing security to specialized firms will become more common.
Conclusion
Intelligence and investigative capabilities are no longer optional in enterprise security. They are essential for defending against sophisticated threats and ensuring compliance with regulations. By embracing these capabilities and staying ahead of trends, organizations can better protect their assets and maintain trust with customers and partners.
FAQ
What is enterprise security intelligence?
Enterprise security intelligence involves gathering and analyzing data to protect against security threats. It includes threat intelligence, behavioral analysis, and more.
How does AI enhance security?
AI enhances security by automating threat detection and analysis, improving response times, and predicting potential threats through machine learning.
What are insider threats?
Insider threats are security risks posed by employees or contractors with access to sensitive information. They can be intentional or accidental.
Why is compliance important in security?
Compliance ensures that organizations adhere to legal standards for data protection, avoiding fines and reputational damage.
What are some common security pitfalls?
Common pitfalls include overreliance on technology, lack of skilled personnel, and inadequate incident response plans.
How can organizations improve their security posture?
Organizations can improve security by adopting a proactive approach, investing in training, and implementing comprehensive incident response plans.
What future trends will impact enterprise security?
Future trends include the increased use of blockchain, expansion of zero trust architecture, and growth of managed security services.
How can threat intelligence be integrated into security strategies?
Threat intelligence can be integrated by using platforms that provide real-time data, conducting regular audits, and collaborating with industry peers.
Key Takeaways
- Evolving threats demand advanced intelligence and investigative capabilities.
- Insider threats are a growing concern, comprising 60% of breaches.
- AI and machine learning enhance threat detection and response times.
- Compliance with regulations like GDPR is crucial for data protection.
- Future trends include blockchain, zero trust, and managed security services.
Related Articles
- Google's Landmark Discovery: AI-Generated Zero-Day Exploit [2025]
- AI Agents in Healthcare and Manufacturing: Overcoming Enterprise IAM Challenges [2025]
- Digg's Return: Aggregating AI News in a New Era [2025]
- Hollywood's New Frontier: AI Training Over TV Production [2025]
- The Anthropic-xAI Partnership: Unpacking the Implications for AI and Cloud Computing [2025]
- Smartphone Security Risks and Solutions [2025]
![Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]](https://tryrunable.com/blog/why-intelligence-and-investigative-capability-are-essential-/image-1-1778580248905.jpg)



