The VPN Industry's Unpreparedness: A Deep Dive into Tech Radar's Findings [2025]
In an era where online security is not just a preference but a necessity, Virtual Private Networks (VPNs) have become a go-to solution for many. However, recent findings by Tech Radar suggest that a significant portion of the VPN market is ill-equipped to handle the responsibilities that come with modern cybersecurity demands. Let's explore why this is the case, alongside practical advice and best practices for VPN users and providers alike.
TL; DR
- Key Point 1: Many VPNs lack robust encryption, leaving users vulnerable to cyber threats. As noted by Tech Radar, the concept of "military-grade encryption" is often misleading.
- Key Point 2: Transparency issues plague the industry, with unclear data policies. An investigation revealed that over 75% of Android VPNs fail basic transparency tests.
- Key Point 3: User education on VPN capabilities and limitations is inadequate.
- Key Point 4: The future of VPNs lies in AI-driven security enhancements.
- Bottom Line: VPN providers need to innovate and educate to remain relevant and trustworthy.
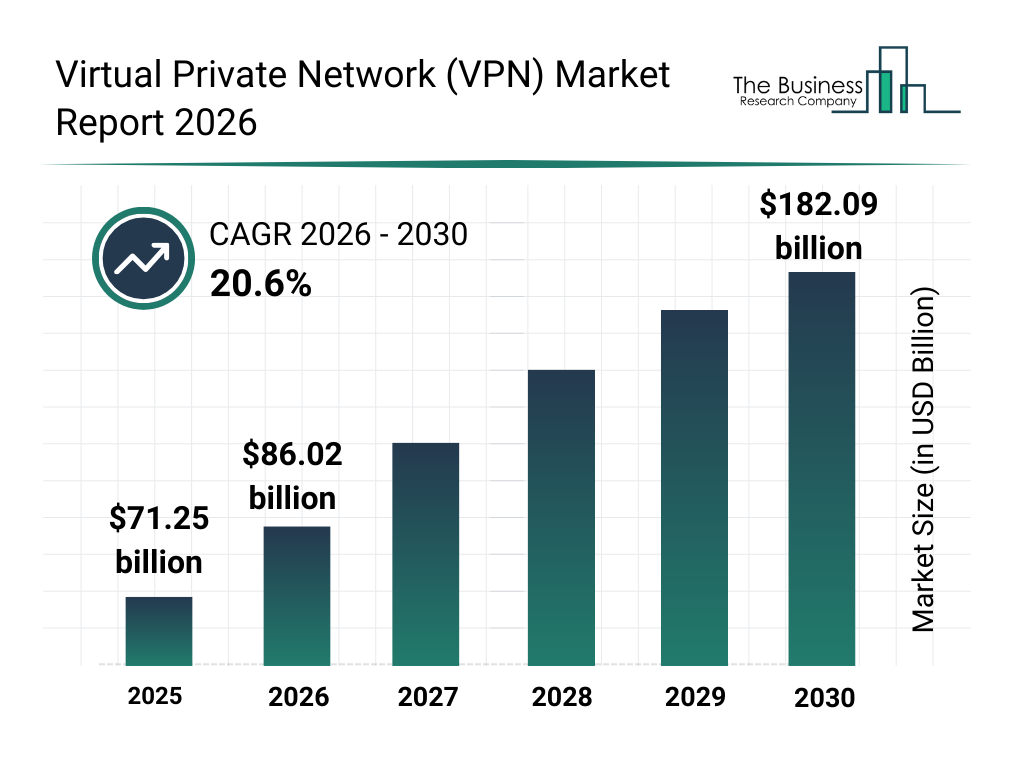
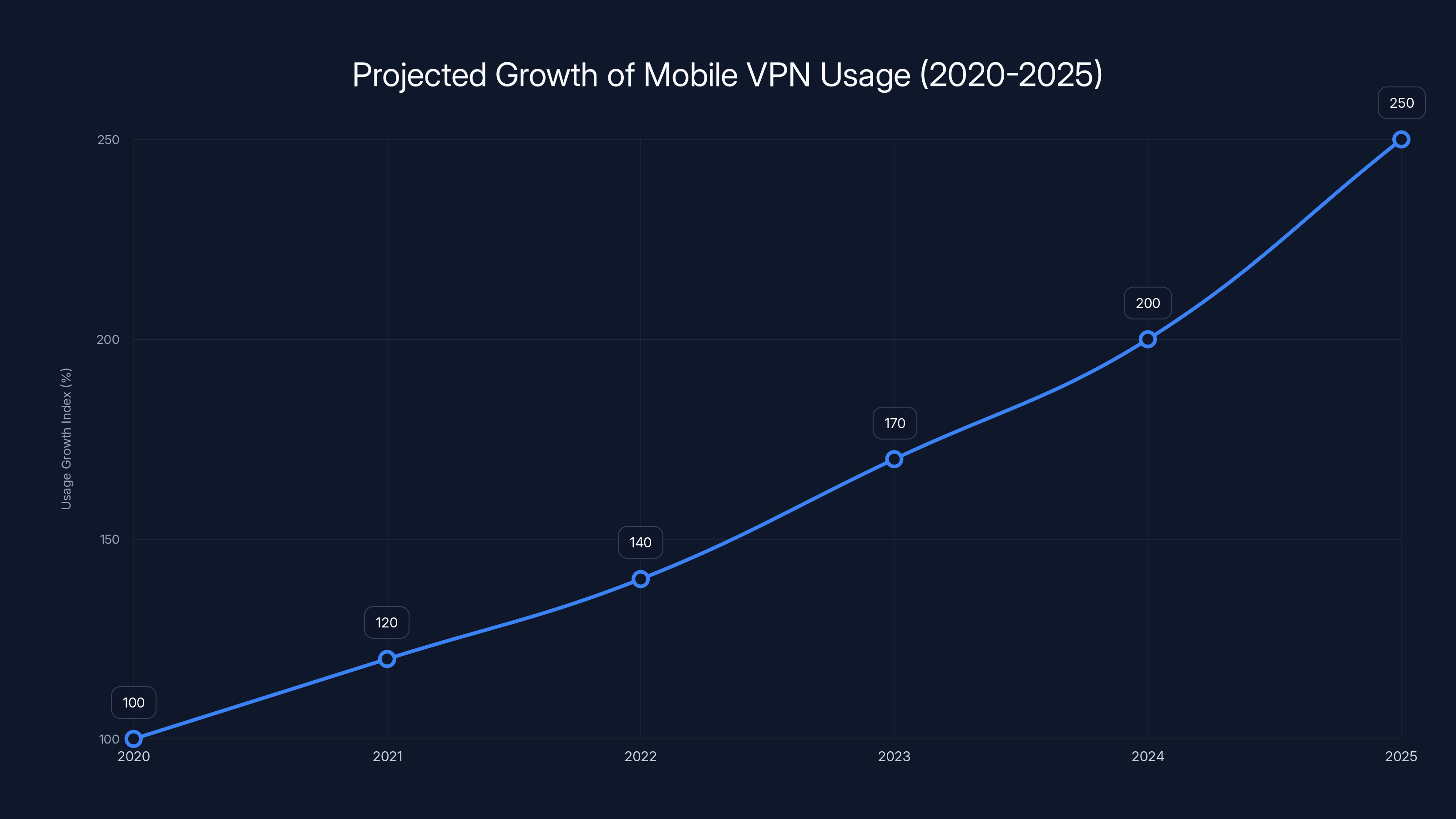
Mobile VPN usage is projected to grow by 150% from 2020 to 2025, driven by increased smartphone adoption and mobile internet usage. Estimated data.
Introduction
The digital landscape is evolving rapidly, and with it, the threats to our online privacy and security. VPNs have become a staple in the toolkit of the privacy-conscious, promising anonymity and security. However, as Tech Radar's research reveals, many providers are falling short of these promises, leaving users exposed to potential risks.

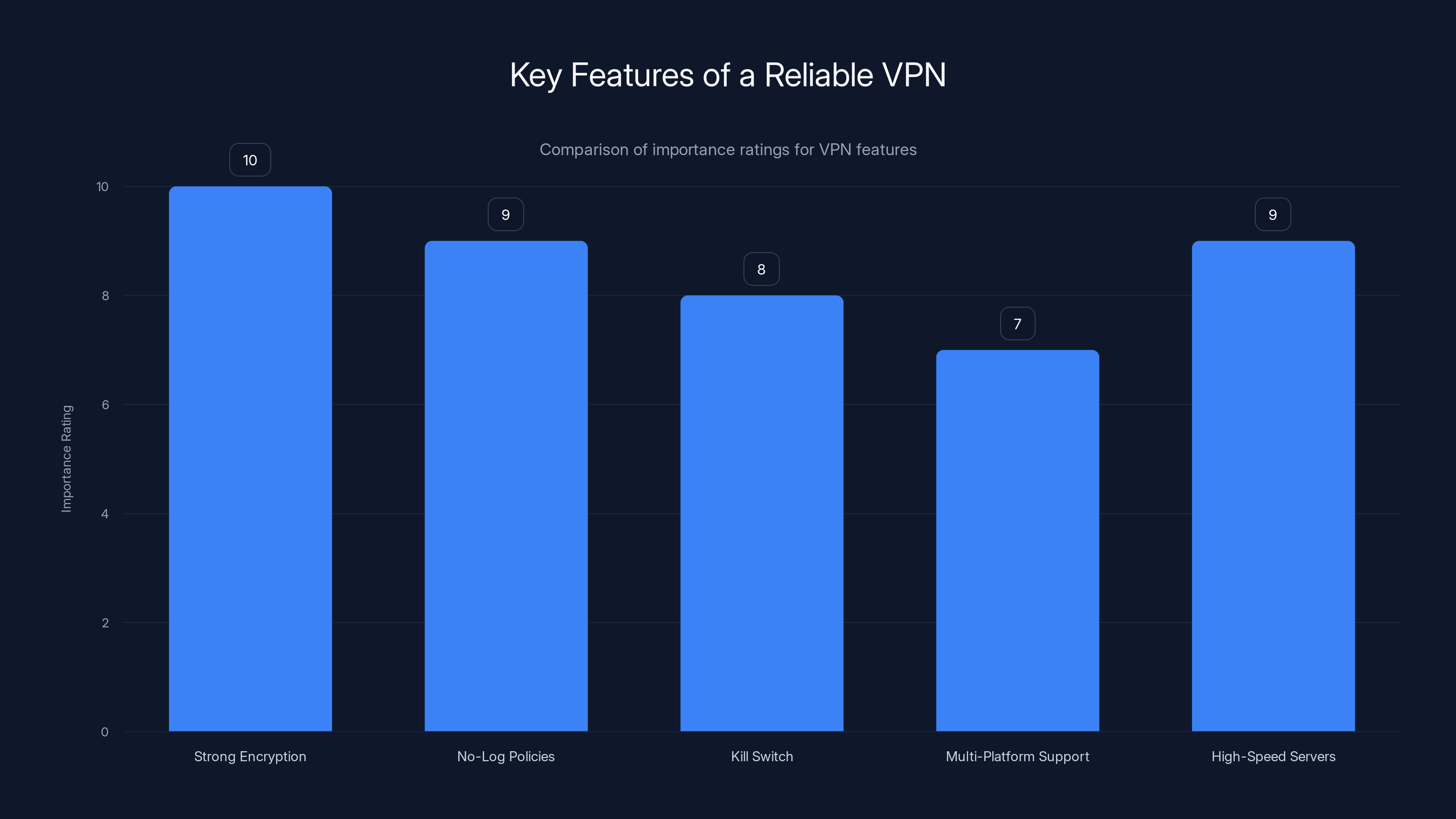
Strong encryption and high-speed servers are rated as the most important features for a reliable VPN, highlighting the need for security and performance.
Understanding the VPN Market
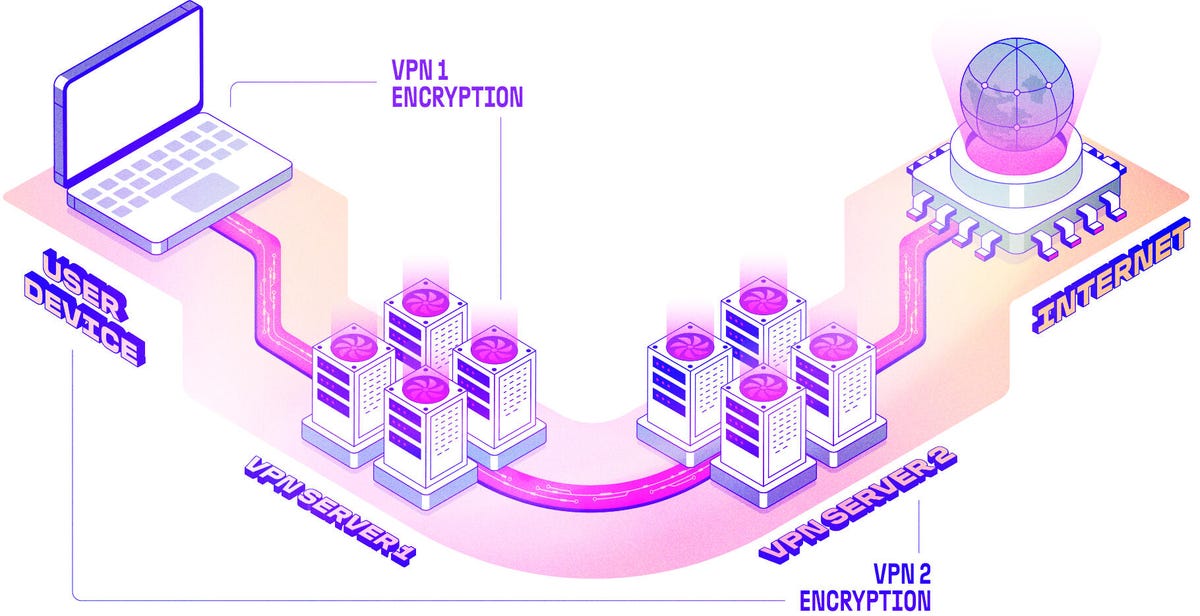
To grasp the full scope of the issue, it's essential to understand what a VPN does. At its core, a VPN encrypts your internet connection, making it appear as though you're accessing the web from a different location. This encryption is supposed to shield your data from prying eyes.
Key Features of a Reliable VPN
- Strong Encryption Protocols: AES-256 is the standard for secure encryption.
- No-Log Policies: Ensures that user data is not stored by the provider.
- Kill Switch: Disconnects the internet if the VPN connection drops unexpectedly.
- Multi-Platform Support: Compatibility with various devices, from smartphones to desktops.
- High-Speed Servers: Essential for an uninterrupted browsing experience.
The Pitfalls of Current VPN Offerings
Despite these essential features, many VPN providers fail to deliver on their promises. Let's dive into the common pitfalls plaguing the industry:
Inadequate Encryption Standards
While AES-256 encryption is the gold standard, not all VPNs implement it. Some rely on outdated protocols like PPTP, which are vulnerable to modern hacking techniques.
Solution: Always choose VPNs that explicitly state their use of AES-256 encryption and the Open VPN protocol, known for its security and reliability.
Transparency and Trust Issues
VPN providers often claim to have a no-log policy, but without independent audits, these claims are hard to verify. Trust is crucial, yet many providers operate in jurisdictions with weak privacy laws, casting doubt on their data policies.
Solution: Opt for VPNs that have undergone third-party audits and are based in countries with strong privacy protection laws.
Limited User Education
Many users do not fully understand how VPNs work or their limitations. This lack of knowledge can lead to misuse or over-reliance on the technology for security.
Solution: VPN providers should offer comprehensive guides and tutorials to educate users on best practices and potential vulnerabilities.
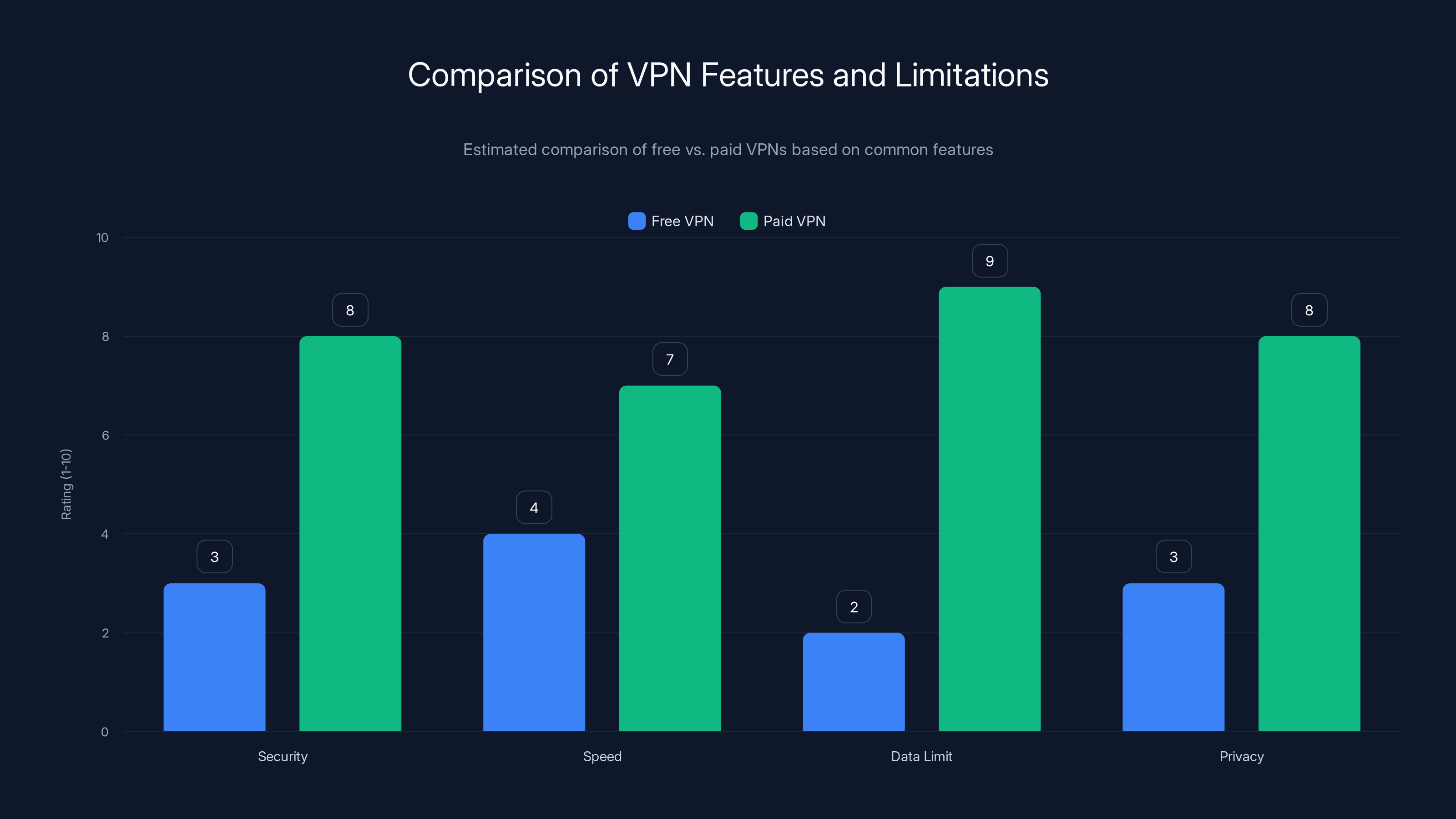
Paid VPNs generally offer better security, speed, and privacy compared to free VPNs, which often have limitations. Estimated data.
Best Practices for VPN Users
To maximize the benefits of a VPN, users need to adopt best practices that enhance their online security:
- Regularly Update VPN Software: Ensure you have the latest security patches.
- Use Strong, Unique Passwords: For your VPN account, to prevent unauthorized access.
- Enable Multi-Factor Authentication: Adds an extra layer of security to your account.
- Choose Servers Wisely: Select locations that offer the best balance of speed and privacy.
- Be Aware of DNS Leaks: Use tools to check for leaks that could expose your activity.

Future Trends in the VPN Industry
The future of VPNs is promising, with several trends poised to redefine the industry:
AI-Driven Security Enhancements
Artificial Intelligence is set to revolutionize VPNs by automating threat detection and response, making them more adaptive to emerging threats. According to PCMag, AI can analyze patterns in network traffic to identify potential security breaches in real-time.
Integration with IoT Devices
As the Internet of Things (IoT) expands, VPNs will need to secure a growing number of devices, from smart home gadgets to wearable tech.
Challenge: Ensuring seamless integration without compromising speed or security.
Increased Focus on Mobile Security
With mobile internet usage outpacing desktop, VPN providers are developing mobile-specific features to cater to this shift. CNET highlights the importance of mobile VPNs in securing data on the go.
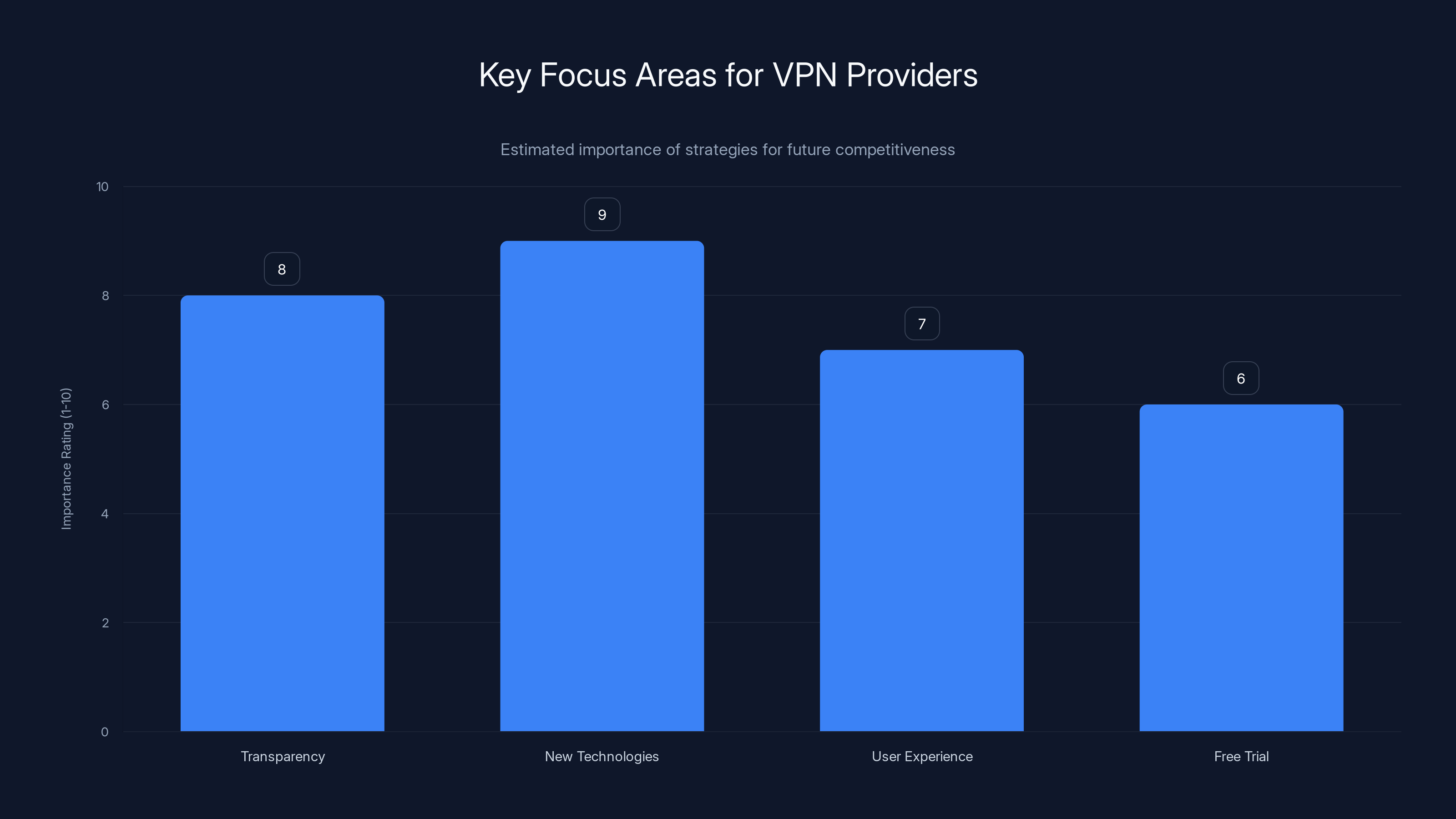
Innovating with new technologies and enhancing transparency are crucial for VPN providers to remain competitive. Estimated data based on industry trends.
Practical Implementation Guides
For those new to VPNs, getting started can seem daunting. Here's a step-by-step guide to setting up a VPN on various devices:
Setting Up a VPN on Windows
- Choose a VPN Provider: Research and select one that meets your needs.
- Download the Software: Visit the provider's website to download the Windows app.
- Install and Launch: Follow the installation instructions and open the app.
- Log In: Use your credentials to log in to the VPN service.
- Connect to a Server: Choose a server location and connect.
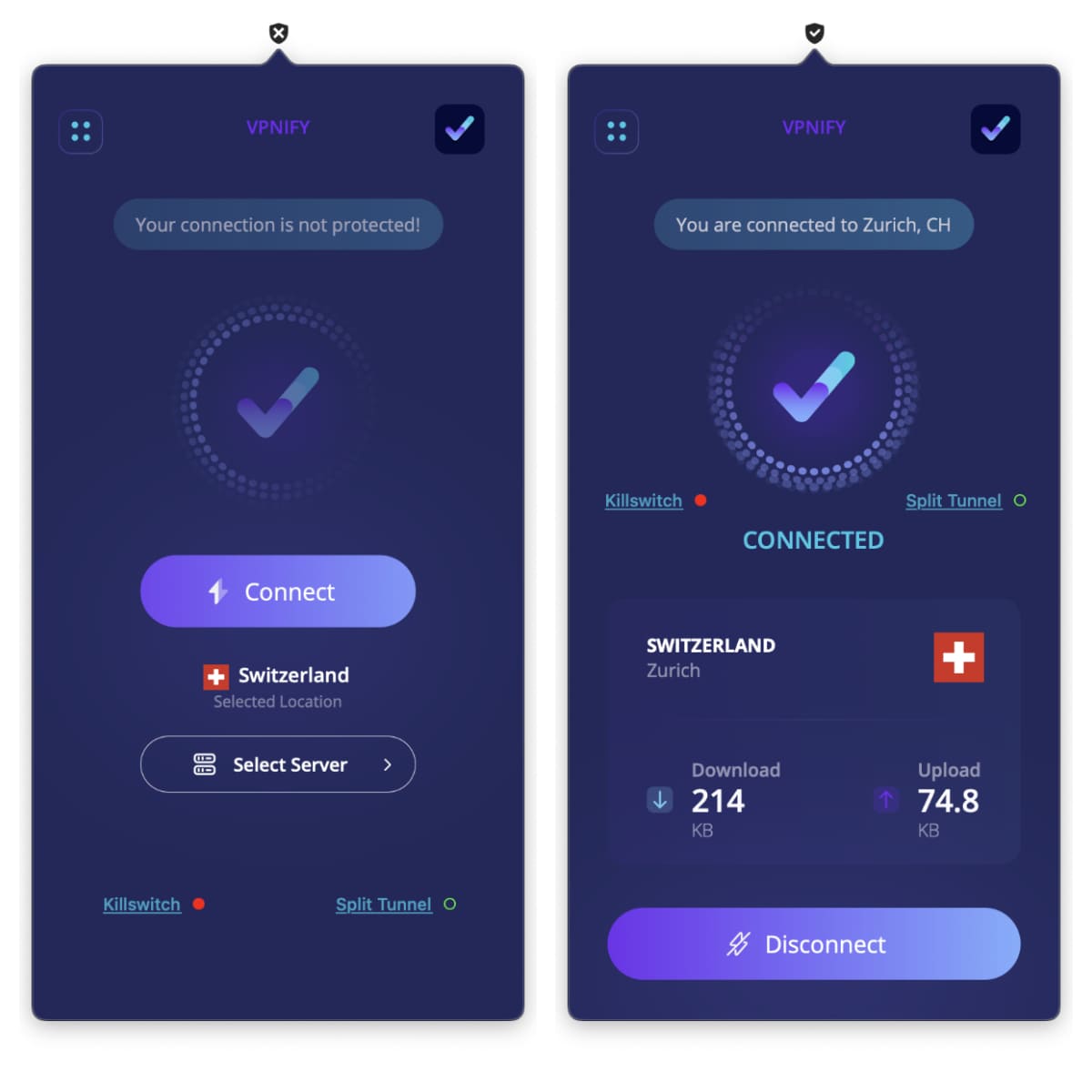
Configuring a VPN on a Smartphone
- Access the App Store: Search for your chosen VPN provider.
- Download and Install: Install the app on your device.
- Open the App: Log in using your account details.
- Select a Server: Tap to connect to your preferred location.
- Verify the Connection: Ensure your IP address has changed.

Common VPN Misconceptions
Despite their growing popularity, VPNs are often misunderstood. Let's debunk some common myths:
Myth 1: VPNs Make You Completely Anonymous
While VPNs can hide your IP address, they do not make you invisible. Websites can still track you using cookies and other methods.
Reality: Use VPNs alongside other privacy tools for maximum anonymity.
Myth 2: All VPNs Are the Same
VPNs vary significantly in terms of features, performance, and security. Some offer advanced security protocols, while others prioritize speed.
Myth 3: Free VPNs Are Just as Good as Paid Ones
Free VPNs often come with limitations, such as slower speeds, data caps, and questionable privacy practices. Tech Radar emphasizes the limitations of free VPN services.
Recommendation: Invest in a reputable paid VPN for comprehensive protection.
The Role of VPNs in Business Security
Businesses increasingly rely on VPNs to secure remote work and protect sensitive data. Here's how VPNs can benefit corporate environments:
Secure Remote Access
VPNs enable employees to access company resources securely from anywhere, reducing the risk of data breaches in remote work setups.
Cost Savings
By using VPNs, businesses can reduce the need for expensive dedicated network infrastructure while maintaining secure connections.
Enhanced Collaboration
VPNs facilitate secure communication and collaboration across geographically dispersed teams, boosting productivity.

Future Recommendations for VPN Providers
To stay competitive and address the challenges highlighted by Tech Radar, VPN providers should consider these strategies:
Enhance Transparency
Providers should prioritize transparency by undergoing regular third-party audits and clearly communicating their data policies.
Innovate with New Technologies
Adopting AI and blockchain technologies can enhance security measures, offering users greater protection against evolving threats.
Focus on User Experience
A user-friendly interface, coupled with robust customer support, can significantly improve user satisfaction and retention.
Conclusion
The VPN industry is at a crossroads, with significant portions unable to meet the growing demands of cybersecurity. As users become more savvy and threats evolve, VPN providers must innovate and educate to retain trust and relevance. By addressing the shortcomings identified by Tech Radar, the industry can better equip itself to handle the responsibilities of safeguarding user data and privacy.
FAQ
What is a VPN?
A Virtual Private Network (VPN) is a service that encrypts your internet connection, masking your IP address to enhance privacy and security.
How does a VPN work?
A VPN routes your internet traffic through an encrypted tunnel to a remote server, making it appear as if you're accessing the web from that server's location.
What are the benefits of using a VPN?
Benefits include enhanced privacy, access to geo-restricted content, secure data transfer, and protection against cyber threats.
Are free VPNs safe to use?
Free VPNs often come with limitations and potential privacy risks. It's generally recommended to use a reputable paid VPN for better security.
Can a VPN be used on multiple devices?
Yes, most VPN services offer multi-device support, allowing you to protect several devices under a single subscription.
What should I look for in a VPN provider?
Key factors include strong encryption, a no-log policy, server locations, speed, and reliable customer support.
How can I check if my VPN is working?
You can use online tools to verify your IP address and ensure it matches the VPN server location you've selected.
What is a kill switch in a VPN?
A kill switch is a feature that automatically disconnects your internet if the VPN connection drops, protecting your data from exposure.
Why is encryption important in a VPN?
Encryption ensures that your data is unreadable to unauthorized parties, protecting your privacy and sensitive information.
How can businesses benefit from using VPNs?
Businesses can secure remote work environments, reduce costs, and enhance collaboration through safe, encrypted connections.
Key Takeaways
- Many VPNs lack robust encryption, exposing users to risks.
- Transparency issues hinder trust in the VPN industry.
- User education on VPN capabilities is often inadequate.
- AI-driven security enhancements are the future of VPNs.
- Businesses can leverage VPNs for secure remote access.
- Free VPNs often come with limitations and risks.
- Encryption is crucial for protecting user data.
- VPN providers need to innovate to stay competitive.
Related Articles
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- How to Stream F1 2026 from Anywhere with the Best VPNs
- The Trump Phone: A No-Show at the World's Biggest Mobile Expo [2025]
- COPPA 2.0: A Fresh Leap Towards Online Privacy for Children and Teens [2025]
- CrowdStrike's Best Quarter Ever: The Future of Cybersecurity and Market Demands [2025]
- Navigating the World of Live Sports Streaming with a VPN: Three Frustrations You Might Face [2025]
![The VPN Industry's Unpreparedness: A Deep Dive into TechRadar's Findings [2025]](https://tryrunable.com/blog/the-vpn-industry-s-unpreparedness-a-deep-dive-into-techradar/image-1-1772816713252.jpg)



