Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
Last month, the cybersecurity community was abuzz when researchers uncovered a critical flaw in the IPVanish VPN app for Mac. This discovery sent shockwaves through technology forums and raised significant concerns about user privacy and data security.
In this comprehensive guide, we're diving deep into the technical details of this flaw, exploring its implications, and providing actionable insights for Mac users to safeguard their information.
TL; DR
- Critical Security Flaw: The vulnerability in IPVanish's Mac app could expose user data.
- Technical Details: Incorrect permissions and poor encryption practices were identified.
- Immediate Actions: Users should update to the latest version and consider additional security measures.
- Long-term Solutions: Implementing best practices in VPN usage enhances overall security.
- Future Trends: Increased scrutiny on VPN services is likely, pushing for more robust security standards.

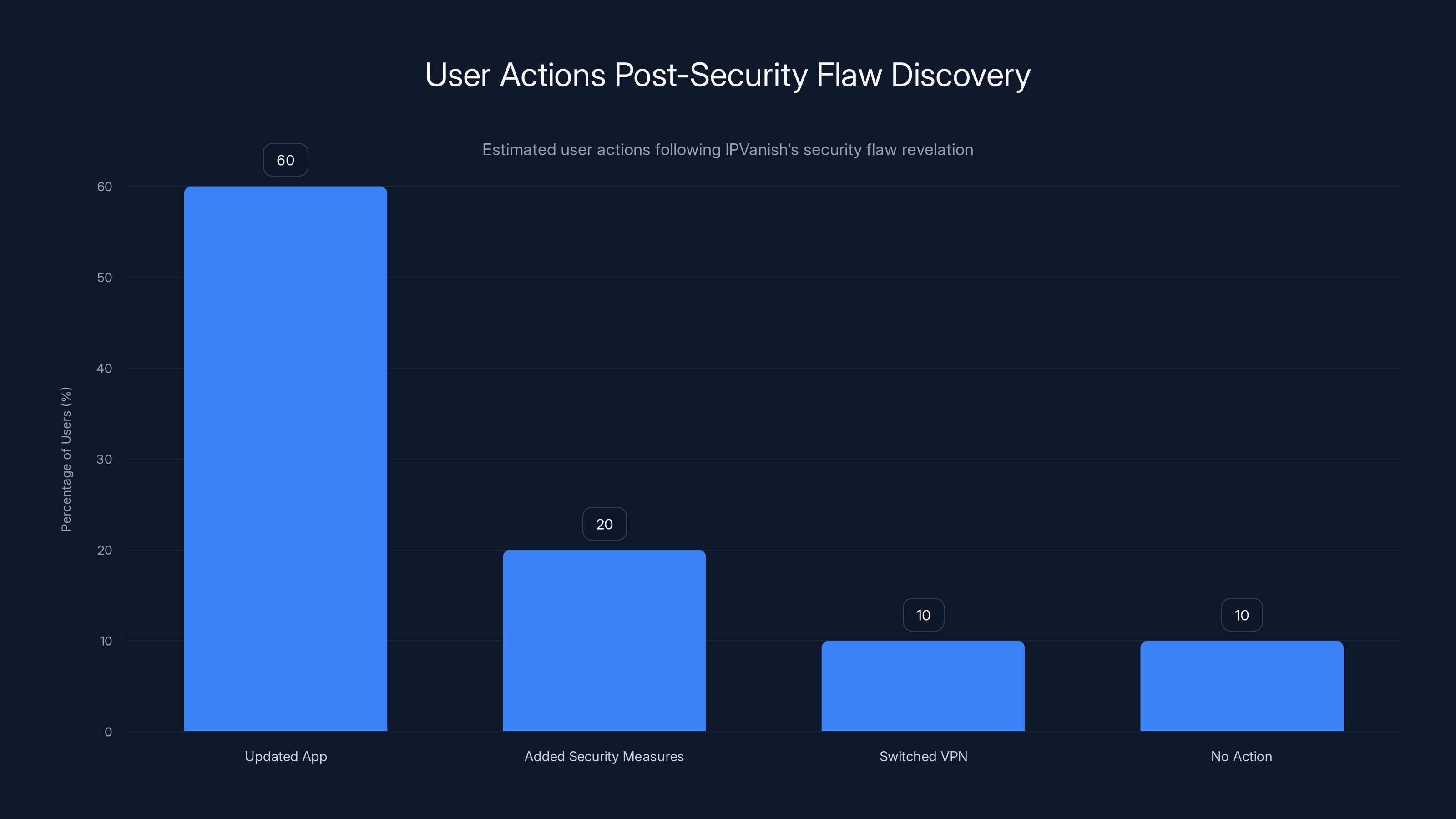
Estimated data shows that 60% of users updated their app, while 20% added extra security measures. A smaller portion switched VPNs or took no action.
What Happened?
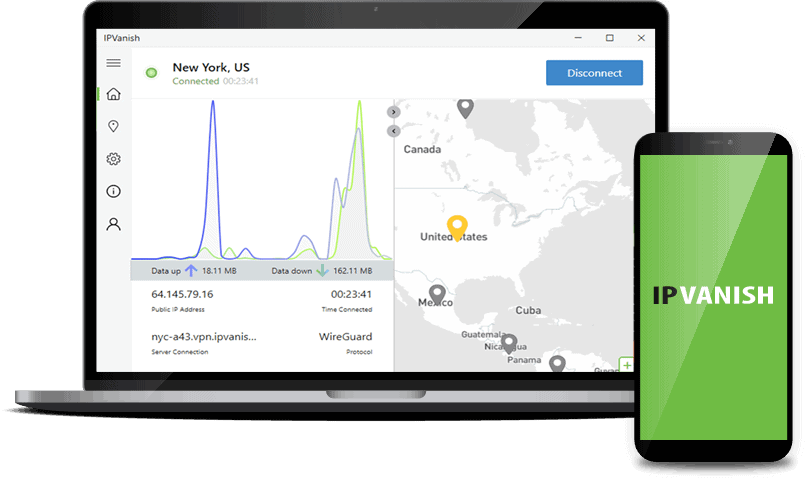
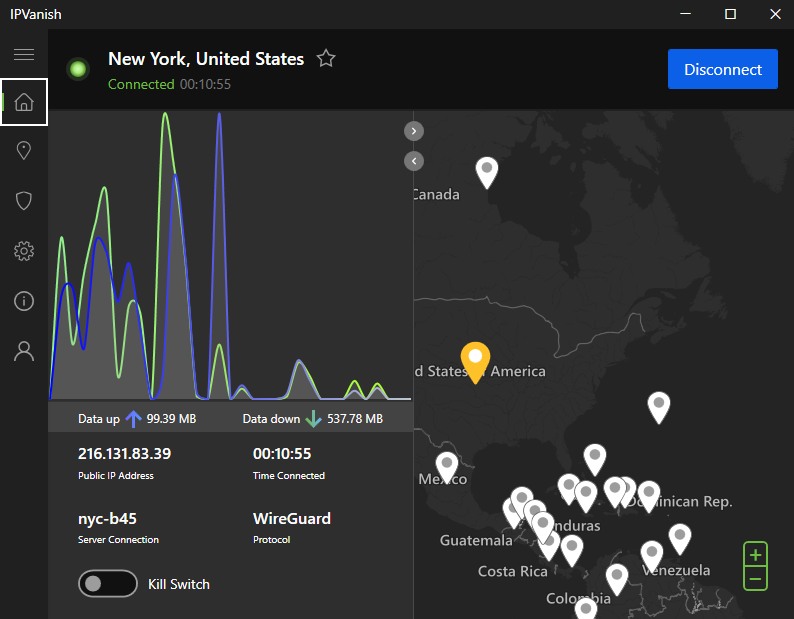
The flaw discovered in IPVanish's Mac VPN app relates to improper handling of user permissions and encryption keys. This issue potentially allows unauthorized access to sensitive data transmitted through the VPN, compromising user privacy, as detailed in CyberPress.
Technical Breakdown
The flaw was found in the way the application handles encryption keys. When a VPN app fails to secure these keys properly, it opens the door for attackers to intercept and decrypt data.
- Incorrect Permissions: The app had permissions set too broadly, allowing potential exploits.
- Weak Encryption: Outdated encryption algorithms were employed, reducing data security, as noted by TechRadar.
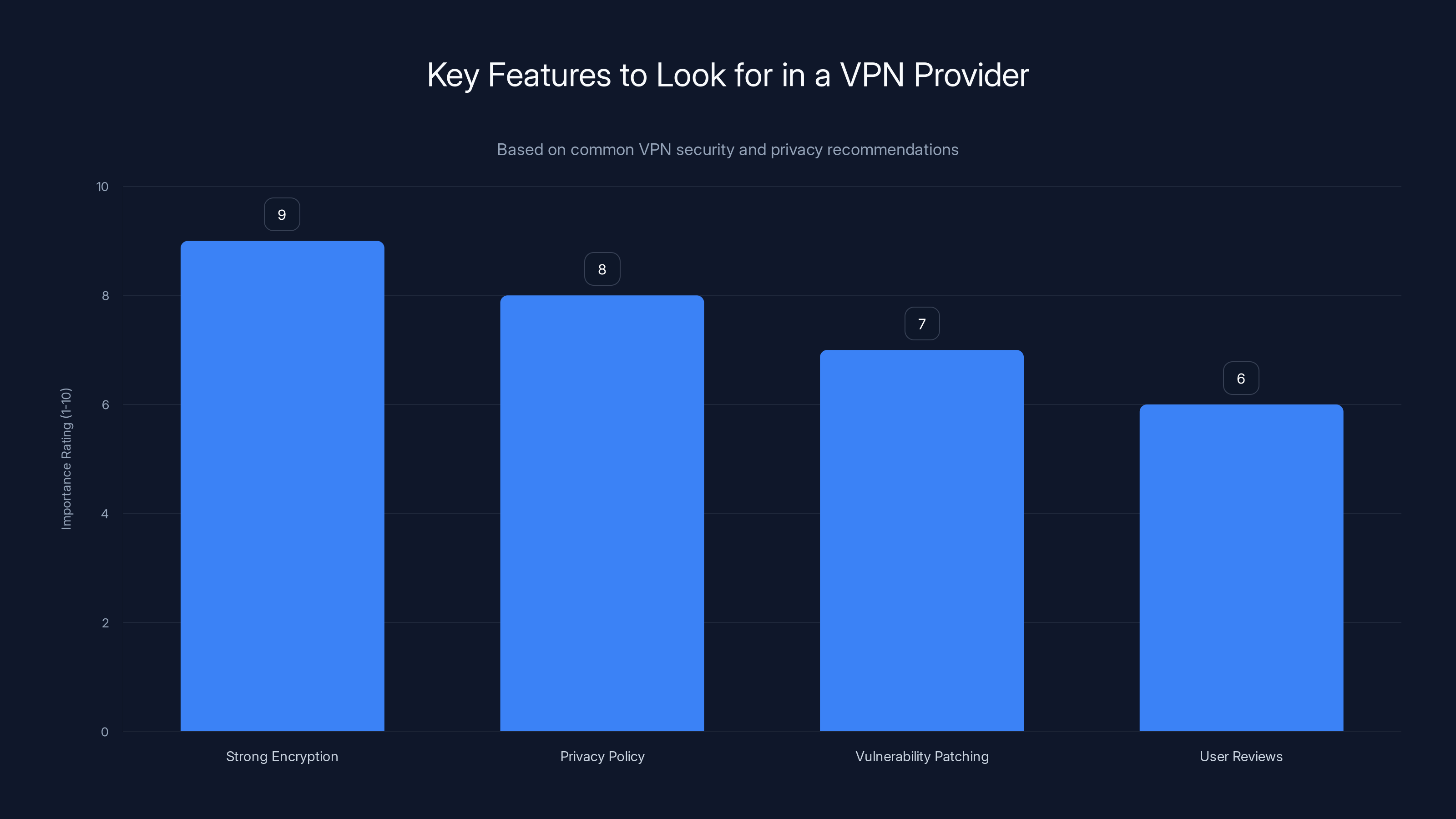
Strong encryption is the most critical feature when choosing a VPN, followed by a clear privacy policy and a history of prompt vulnerability patching. (Estimated data)
How Does This Impact You?
For the average user, this flaw means that any sensitive information sent through IPVanish could be at risk. This includes passwords, personal messages, and other confidential data, as highlighted by PCMag.
Best Practices for VPN Security
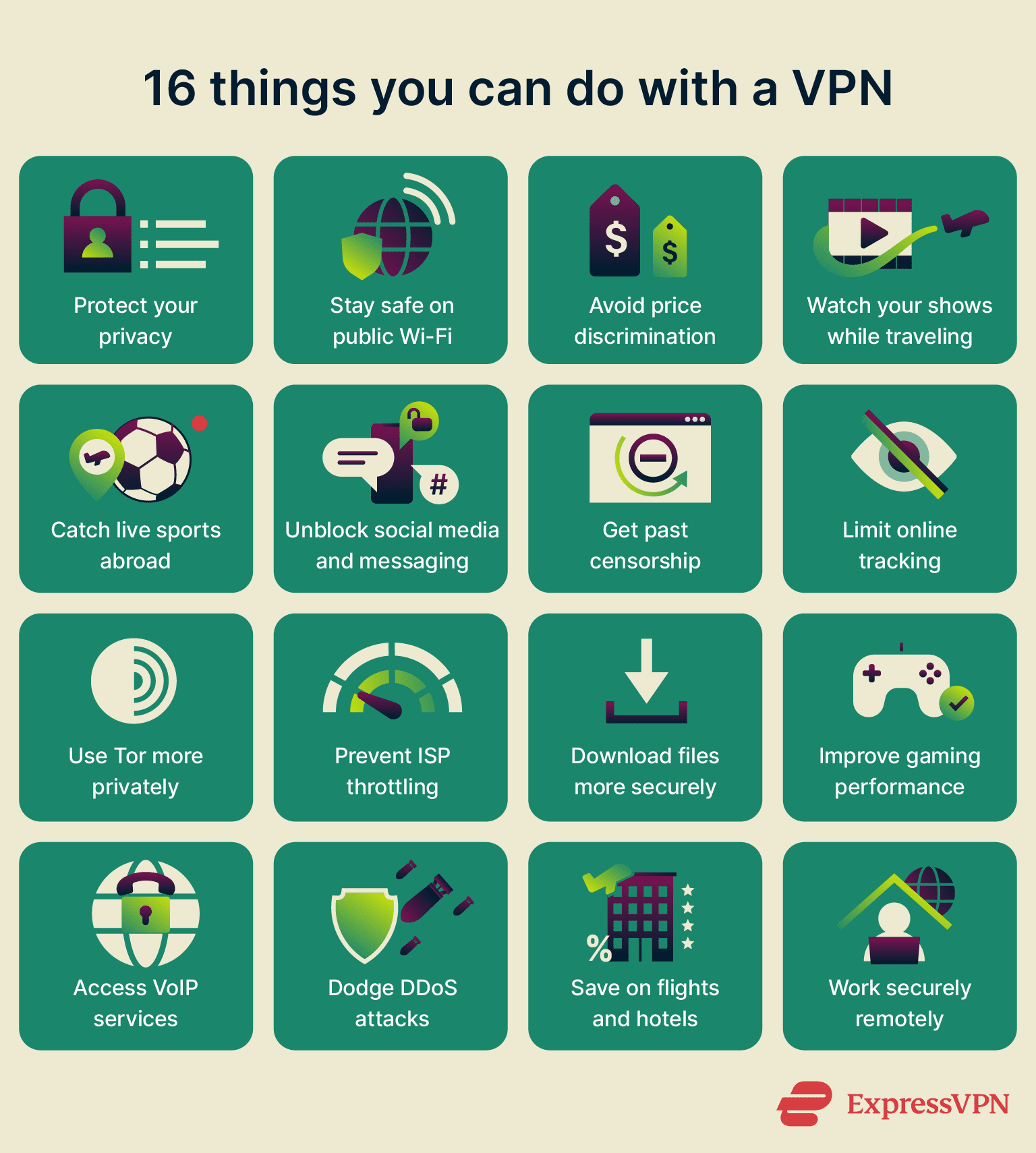
To mitigate risks, here are some best practices for securing your VPN usage:
- Regular Updates: Always keep your VPN software up to date to benefit from the latest security patches.
- Strong Encryption: Choose VPNs that use modern encryption standards like AES-256, as recommended by TechRadar.
- Secure Passwords: Use strong, unique passwords for your VPN accounts and change them regularly.
- Two-Factor Authentication: Enable 2FA for an added layer of security.
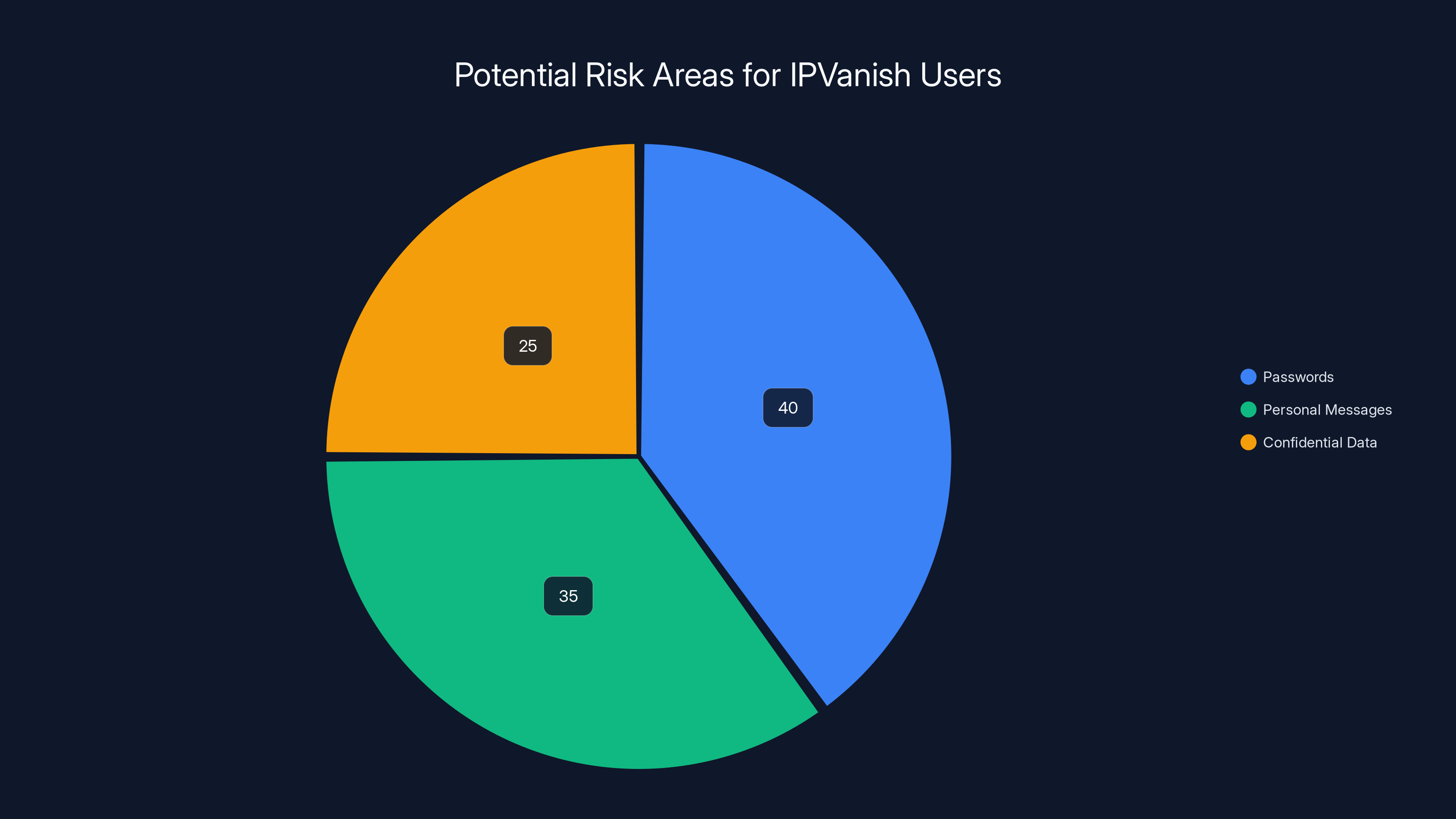
Estimated data shows that passwords (40%) are the most at risk, followed by personal messages (35%) and other confidential data (25%) due to the flaw in IPVanish.
Implementation Guide
Implementing robust security practices involves a few key steps:
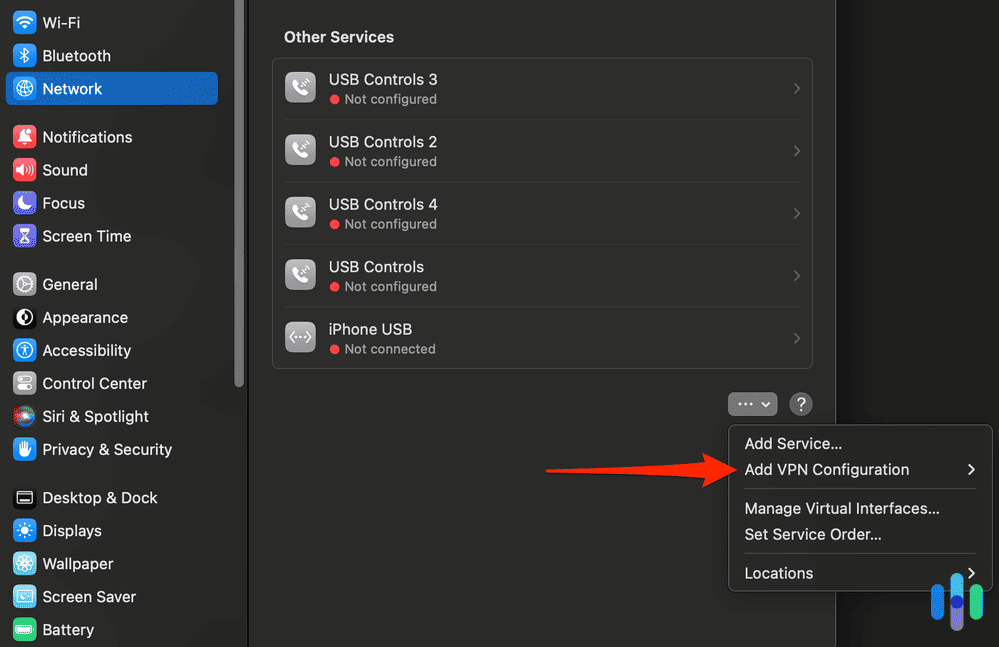
Step 1: Update Your VPN
Ensure that your IPVanish app is updated to the latest version. This typically involves:
- Opening the app
- Navigating to the settings or help menu
- Selecting 'Check for Updates'
Step 2: Use a Firewall
Configure a firewall on your Mac to monitor outgoing and incoming traffic. This can prevent unauthorized access attempts.
bash# Example of a simple firewall rule
sudo pfctl -e
sudo pfctl -f /etc/pf.conf
Step 3: Monitor Network Activity
Regularly check your network activity for any unusual behavior. Tools like Little Snitch can help monitor connections.
Common Pitfalls and Solutions
Users often overlook the importance of network security. Here are some pitfalls and their solutions:
- Ignoring Updates: Set automatic updates for your software to avoid missing critical patches.
- Using Public Wi-Fi Without Protection: Always use a VPN on public networks.
- Neglecting to Monitor Logs: Regularly review your VPN logs for any suspicious activity.

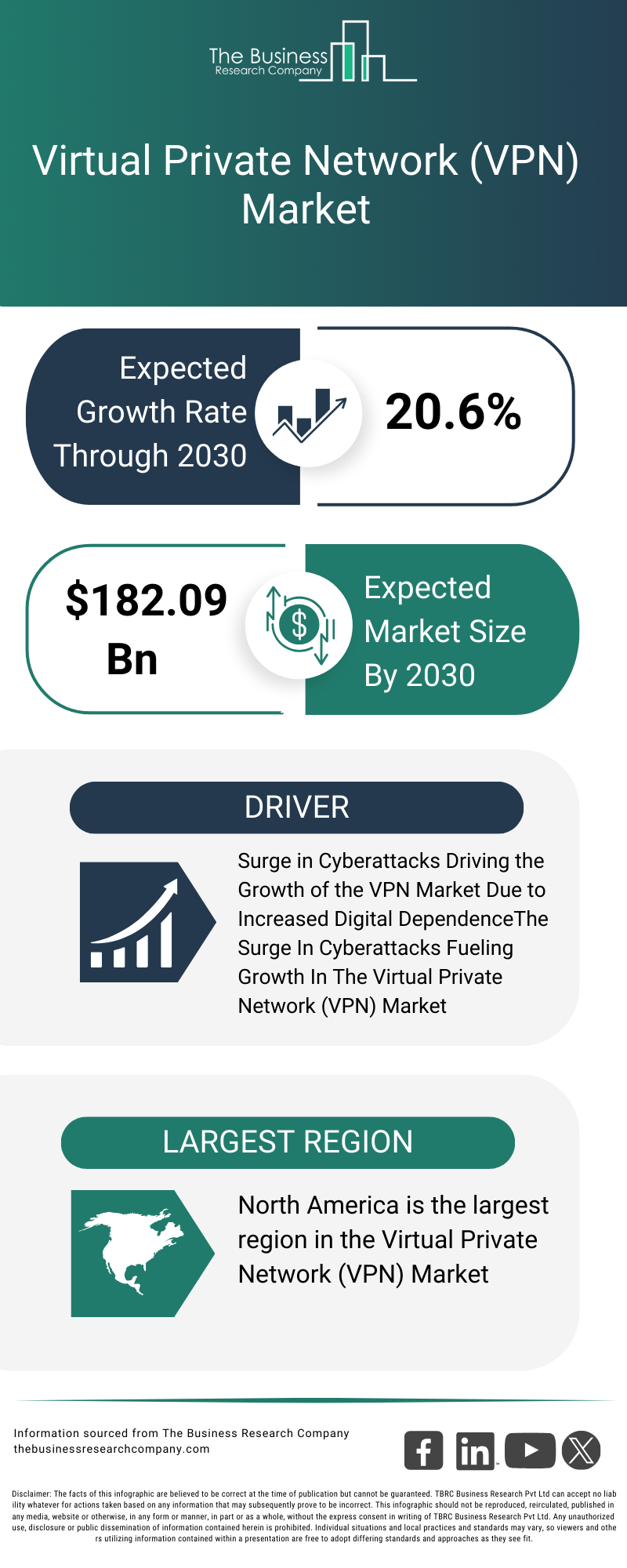
Future Trends in VPN Security
As cyber threats evolve, so too will VPN security measures. Expect to see:
- Enhanced Encryption Algorithms: Future VPNs will likely adopt even stronger encryption standards.
- AI-Powered Threat Detection: Artificial intelligence will play a bigger role in identifying and mitigating threats.
- Greater Transparency: VPN providers will be pushed towards more transparency regarding their security practices, as discussed in CyberNews.
Recommendations for VPN Users
- Research Your VPN Provider: Look into their security practices and past vulnerabilities.
- Consider Multi-VPN Configurations: Use multiple VPNs to add an extra layer of security.
- Stay Informed: Keep abreast of the latest cybersecurity news and updates, as suggested by CNET.

Conclusion
The discovery of the flaw in IPVanish's Mac VPN app serves as a crucial reminder of the importance of cybersecurity vigilance. By staying informed and adopting best practices, users can protect their data and maintain their privacy.

FAQ
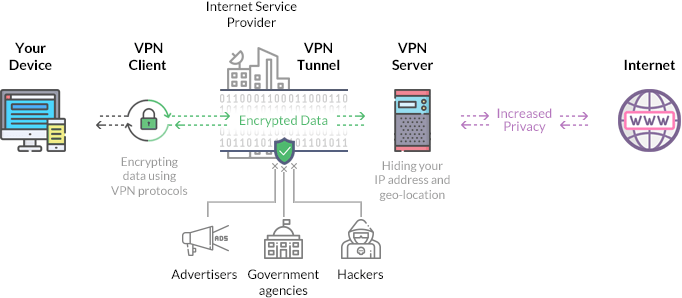
What is a VPN?
A VPN, or Virtual Private Network, encrypts your internet traffic and disguises your online identity, making it harder for third parties to track your activities.
How does the IPVanish flaw affect users?
The flaw could potentially allow unauthorized access to user data, exposing sensitive information to attackers.
What can I do to protect myself?
Update your VPN software, enable strong encryption, and consider additional security measures like firewalls and network monitoring.
Are all VPNs vulnerable?
While no software is immune to vulnerabilities, choosing a VPN with a strong security track record reduces the risk, as noted by Mashable.
How often should I update my VPN?
Check for updates at least monthly, or enable automatic updates to ensure you have the latest security patches.
Can I use other security tools with my VPN?
Yes, using firewalls, antivirus software, and network monitoring tools can enhance your security.
What should I look for in a VPN provider?
Focus on providers that offer strong encryption, a clear privacy policy, and a history of prompt vulnerability patching.
Why is encryption important in a VPN?
Encryption ensures that your data is not readable by unauthorized parties, protecting your privacy and security.
Key Takeaways
- IPVanish's Mac VPN app had a critical security flaw impacting data privacy.
- The flaw involved weak encryption and incorrect permission settings.
- Users must update their VPN software to mitigate risks.
- Implementing best security practices can enhance data protection.
- Future VPNs will likely adopt stronger encryption standards.
- AI will play a larger role in threat detection for cybersecurity.
- Transparency from VPN providers will be increasingly important.
- Regular monitoring and updates are critical for maintaining security.
Related Articles
- The Fall of LeakBase: Inside the Seizure of a Major Data Leak Forum [2025]
- The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
- Navigating the World of Live Sports Streaming with a VPN: Three Frustrations You Might Face [2025]
- An In-Depth Look at Nothing Headphones: A Comprehensive Review [2025]
- Building an Open-Source Global Threat Map: Insights from a Music Streaming CEO [2025]
- Decoding Life: How Open Source AI Models Are Revolutionizing Genomics [2025]
![Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]](https://tryrunable.com/blog/understanding-the-ipvanish-vpn-flaw-what-it-means-for-mac-us/image-1-1772712269005.jpg)



