Understanding the Espionage Ecosystem Threat [2025]
Cybersecurity threats have evolved far beyond the rudimentary phishing scams and basic malware attacks of yesteryear. Today, espionage ecosystems represent one of the most complex and pervasive threats to global cybersecurity. These are not just isolated incidents of hacking but an intricate web of state-sponsored cyber espionage activities, involving multiple actors and sophisticated tactics aimed at infiltrating and exploiting sensitive information from governments, corporations, and individuals.
TL; DR
- Espionage ecosystems: State-sponsored networks using sophisticated tactics for cyber infiltration.
- Key threat actors: Nation-states and advanced persistent threats (APTs).
- Common techniques: Social engineering, supply chain attacks, and zero-day exploits.
- Mitigation strategies: Robust threat intelligence, multi-layered security, and employee training.
- Future trends: Increased AI use in espionage, targeting of IoT and critical infrastructure.
- Bottom Line: Proactively adapting cybersecurity measures is essential to counter espionage threats.

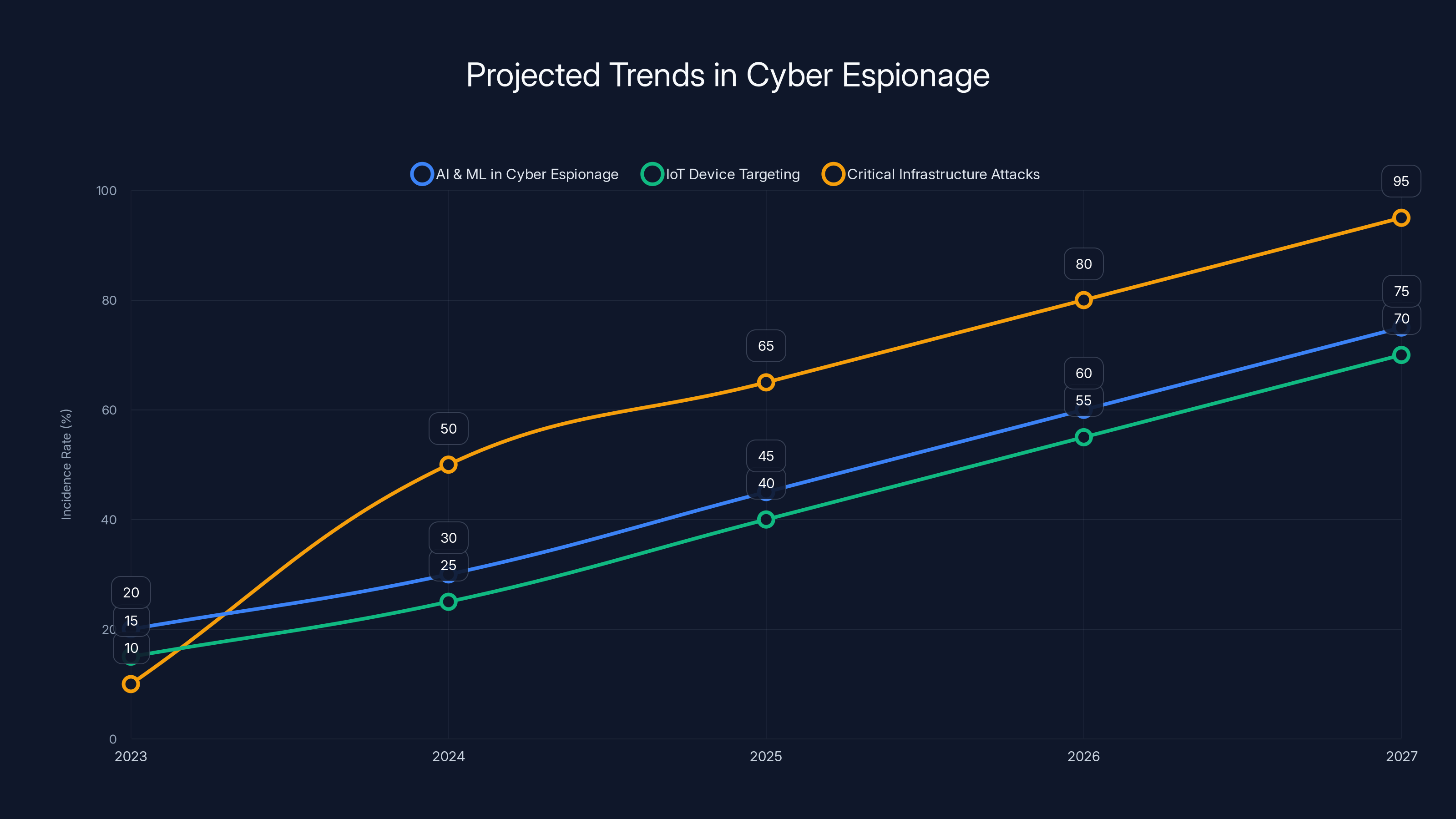
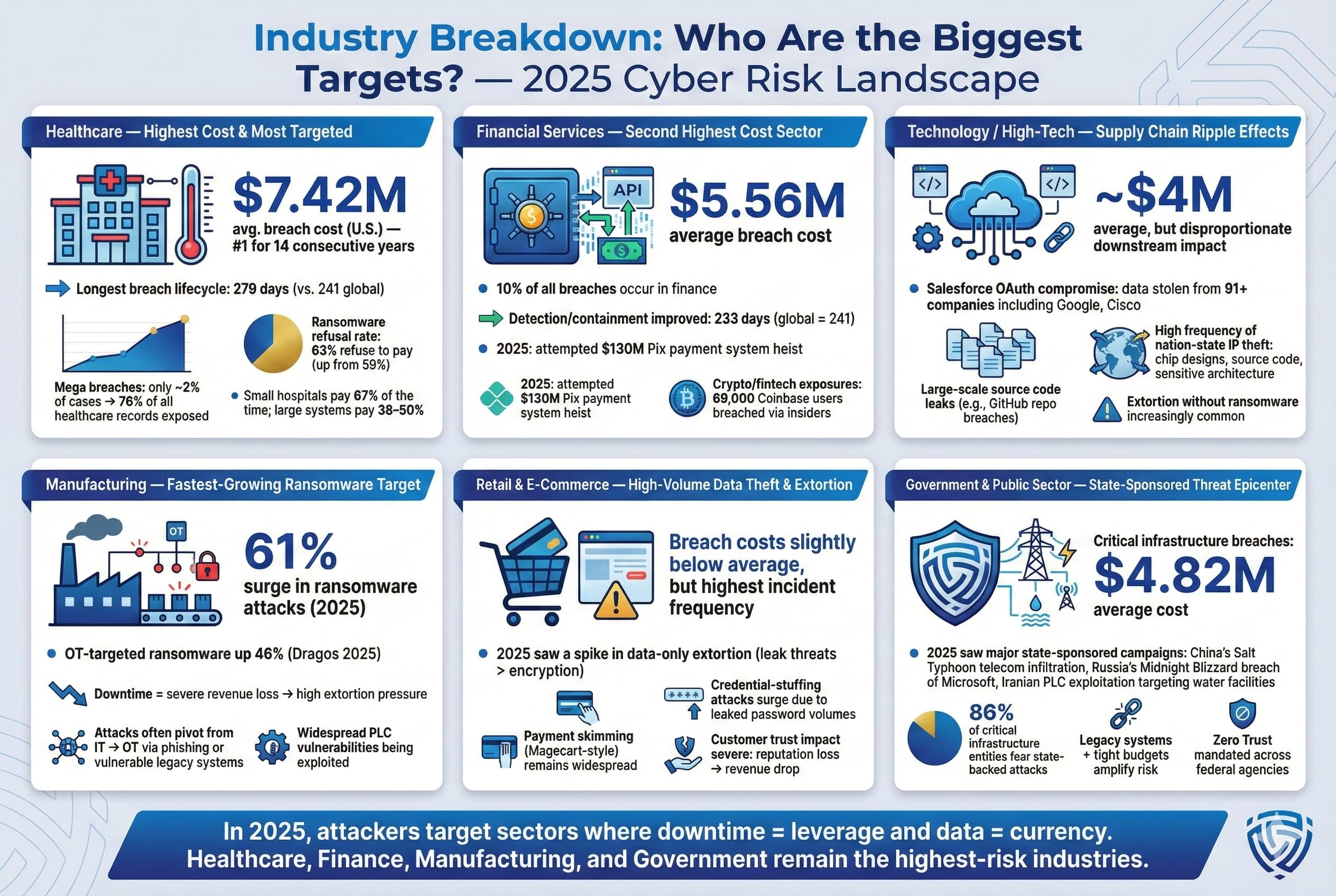
Estimated data shows a significant rise in cyber espionage activities, with critical infrastructure attacks projected to increase sharply by 2027.
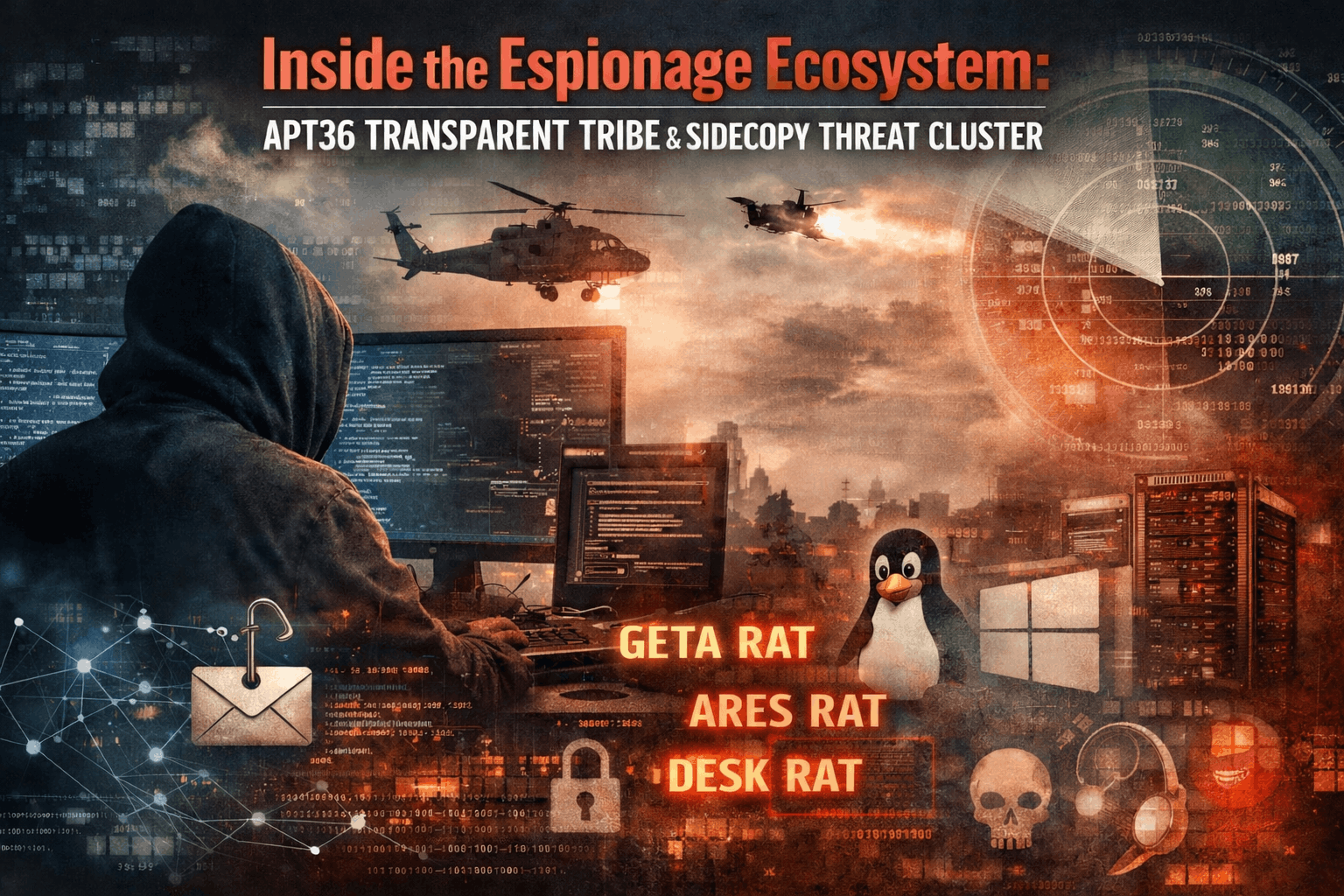
The Anatomy of an Espionage Ecosystem
What is an Espionage Ecosystem?
An espionage ecosystem is a complex network of cyber actors, often backed by nation-states, that collaborate to conduct espionage activities. Unlike traditional cyber threats, these ecosystems are characterized by their organizational structure, scalability, and persistence.
Key Players in the Ecosystem
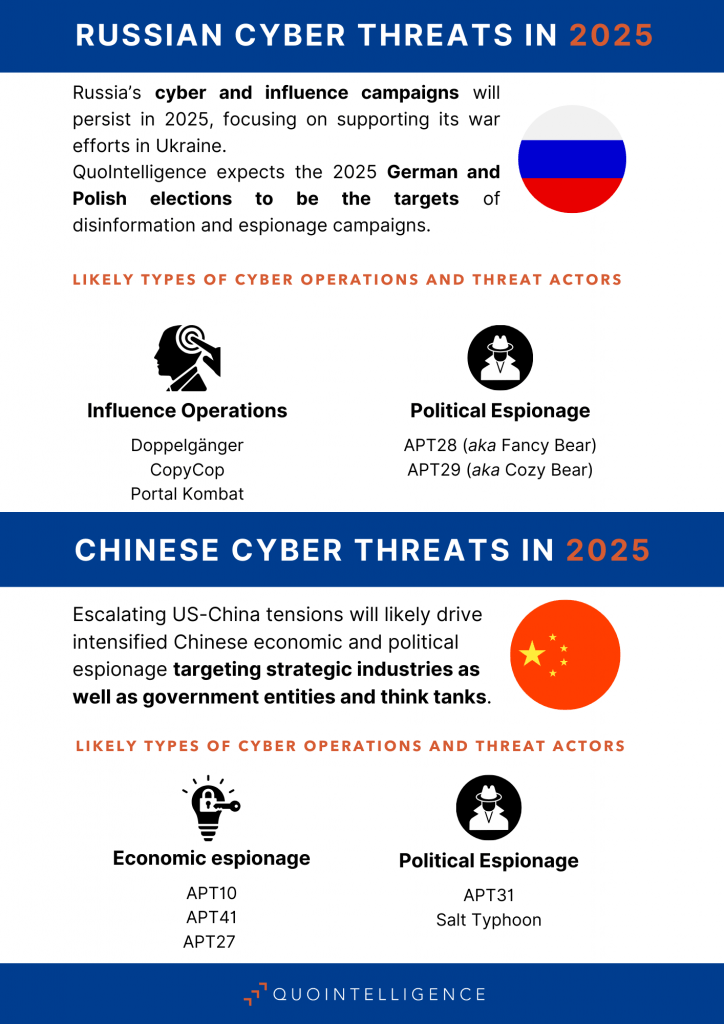
- Nation-States: Countries like China, Russia, and North Korea are often implicated in cyber espionage activities, using cyber tools to gain geopolitical advantages.
- Advanced Persistent Threats (APTs): Groups such as APT28 and APT29 are known for their sophisticated, long-term cyber espionage campaigns.
- Cyber Mercenaries: These are hackers for hire, often used by states to conduct specific operations without direct attribution.
Techniques and Tactics
Social Engineering
Social engineering remains a powerful tool in the espionage arsenal. Hackers exploit human psychology to gain access to sensitive systems and data. Phishing is the most common form, where attackers masquerade as trusted entities to procure credentials or sensitive information.
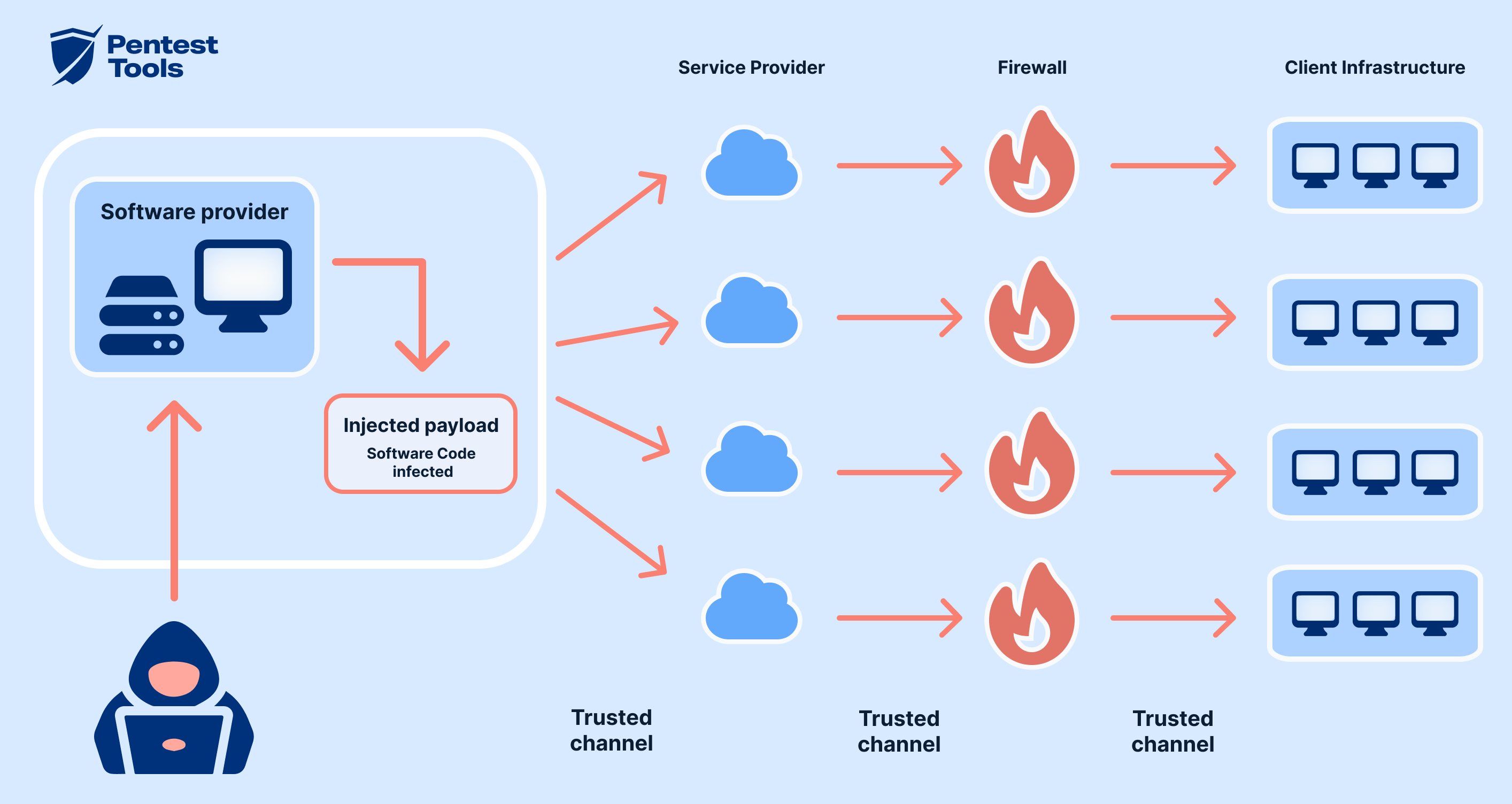
Supply Chain Attacks
Supply chain attacks involve infiltrating a less secure element of the supply chain to eventually target the primary victim. This approach was infamously used in the Solar Winds attack, affecting numerous U.S. government agencies and corporations.
Zero-Day Exploits
Zero-day exploits take advantage of software vulnerabilities unknown to the vendor. These are particularly dangerous as they can be used to breach systems without detection.
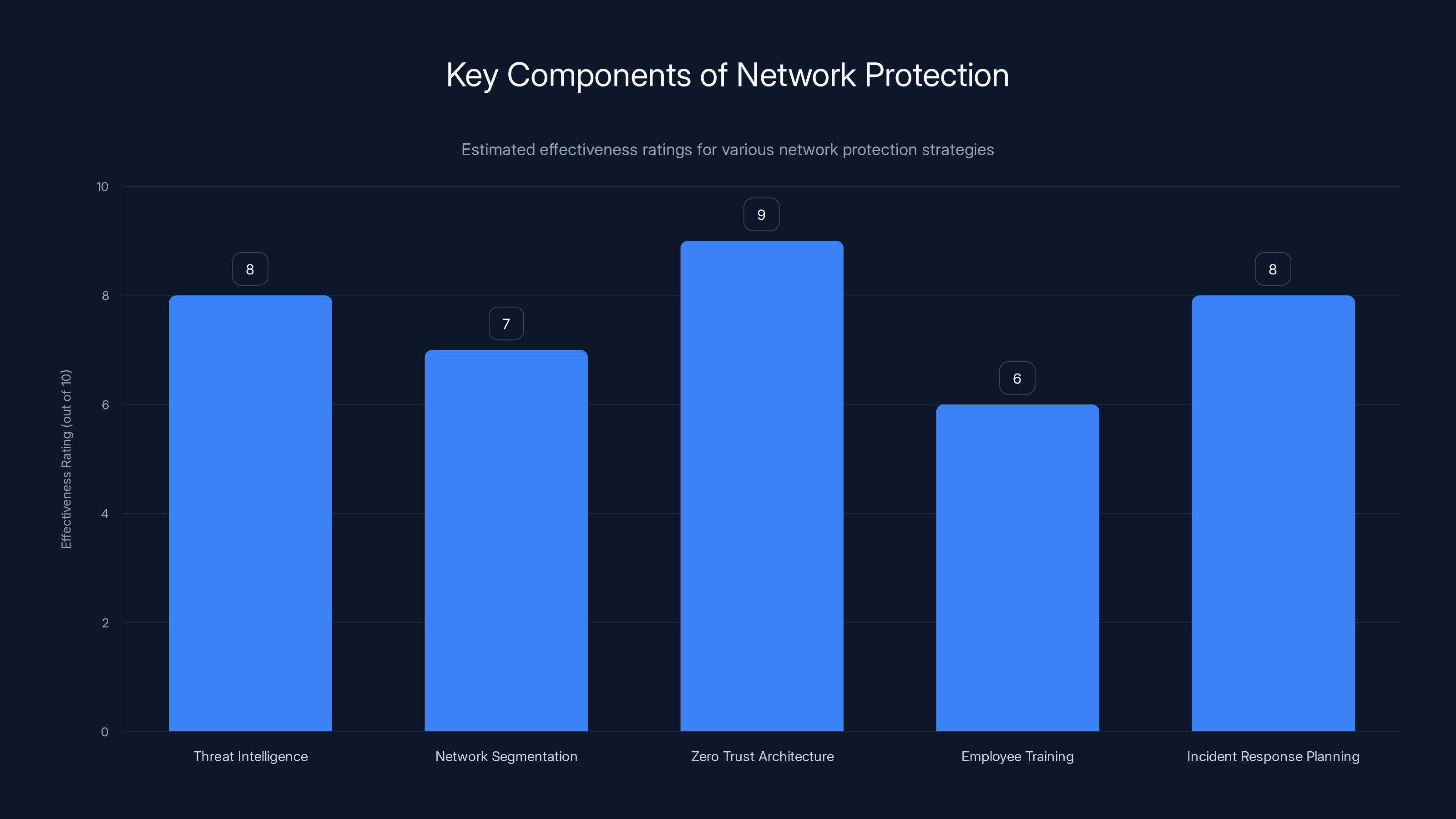
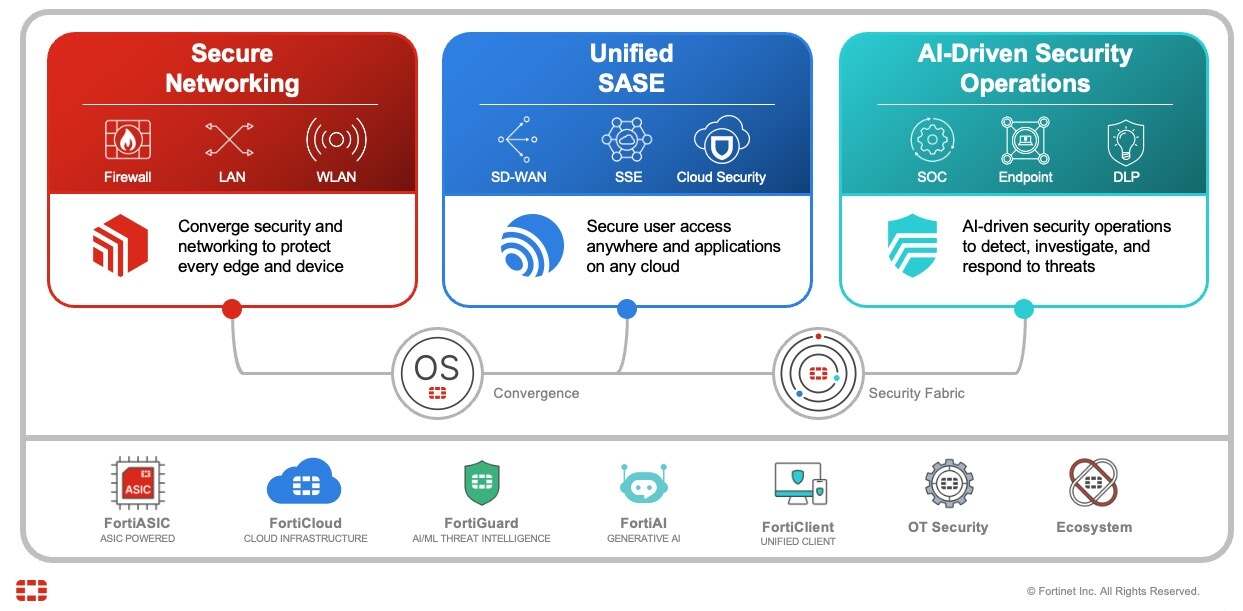
Zero Trust Architecture is rated highest in effectiveness, emphasizing its importance in modern network security strategies. (Estimated data)
Protecting Your Network
Building a Multi-Layered Defense
-
Threat Intelligence: Utilize real-time threat intelligence to stay ahead of potential threats. Platforms like Runable can automate the detection of unusual patterns and anomalies in data.
-
Network Segmentation: Divide your network into segments to contain breaches and prevent lateral movement by attackers.
-
Zero Trust Architecture: Adopt a zero-trust model, where no entity inside or outside your network is trusted by default.
Employee Training
Human error remains a significant vulnerability. Regular training sessions on cybersecurity awareness can reduce the risk of successful social engineering attacks.
Incident Response Planning
Develop a comprehensive incident response plan. Regularly update and test this plan to ensure swift action in the event of a breach.

Common Pitfalls and Solutions
Overreliance on Technology
While technology is crucial, overreliance can be a pitfall. Solution: Complement technological solutions with robust human oversight and analysis.
Ignoring Insider Threats
Espionage ecosystems often exploit insiders. Solution: Implement stringent access controls and continuous monitoring of user activities.
Inadequate Patch Management
Failure to promptly apply patches can leave vulnerabilities open. Solution: Automate patch management processes to ensure all systems are up to date.
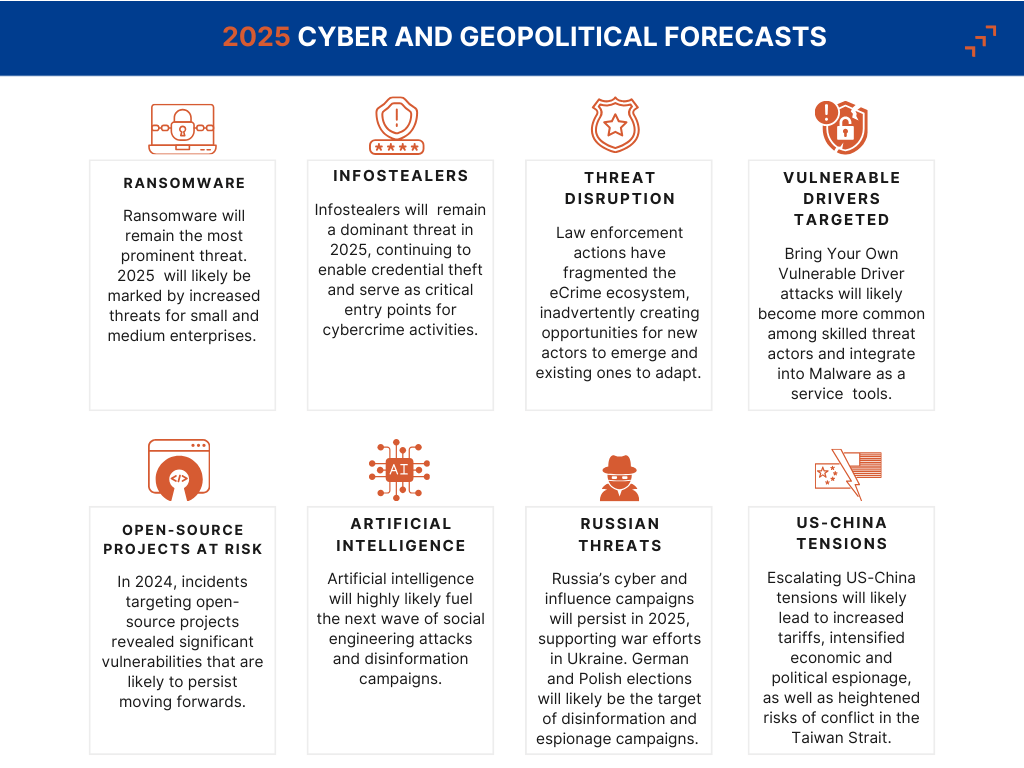
Future Trends in Cyber Espionage
Artificial Intelligence and Machine Learning
AI and ML are becoming integral to both attack and defense strategies. Attackers are using AI to develop more sophisticated phishing and social engineering tactics, while defenders use it to improve threat detection and response times.
Targeting of IoT Devices
As IoT devices proliferate, they become attractive targets due to often lax security measures. This could lead to attacks on critical infrastructure through compromised IoT networks.
Increased Focus on Critical Infrastructure
Nation-state actors are increasingly focusing on critical infrastructure, such as power grids and water supplies, as potential targets for cyber espionage and sabotage.

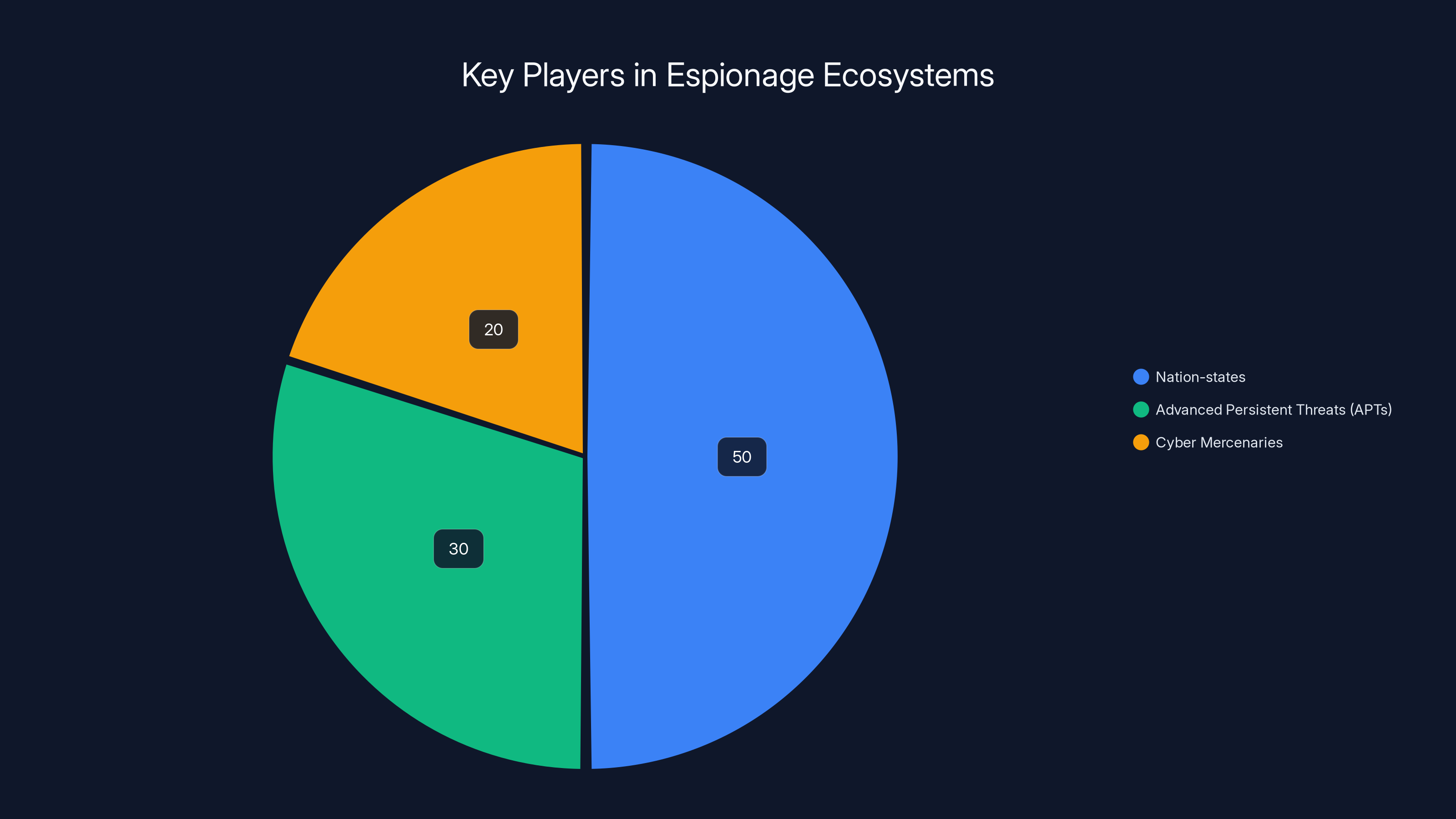
Nation-states hold the largest influence in espionage ecosystems, followed by APTs and cyber mercenaries. (Estimated data)
Best Practices for Organizations
Regular Security Audits
Conduct regular security audits to identify and mitigate vulnerabilities in your systems.
Multi-Factor Authentication (MFA)
Implement MFA to add an extra layer of security against unauthorized access.
Data Encryption
Encrypt sensitive data both in transit and at rest to protect it from unauthorized access.
Collaboration with Law Enforcement
Work with law enforcement and cybersecurity agencies to stay informed about the latest threats and trends.
Case Studies
The Solar Winds Hack
This attack illustrated the power of supply chain infiltration. Attackers inserted malware into Solar Winds' software updates, affecting thousands of clients, including multiple U.S. government agencies.
Key Takeaways:
- Importance of supply chain security
- Need for rapid detection and response capabilities
The OPM Data Breach
In 2015, the U.S. Office of Personnel Management suffered a massive breach, exposing the sensitive data of over 21 million individuals. This was attributed to a lack of encryption and outdated systems.
Key Takeaways:
- Necessity of encryption
- Regular system updates and patching

Recommendations for the Future
Proactive Threat Hunting
Engage in proactive threat hunting to identify potential threats before they can cause harm. This involves actively searching for indicators of compromise in your network.
Continuous Improvement of Security Protocols
Cybersecurity is not a set-and-forget task. Regularly update and improve security protocols to combat evolving threats.
Investment in Cybersecurity Talent
Invest in training and retaining skilled cybersecurity professionals to manage and defend against espionage threats effectively.
Conclusion
The espionage ecosystem threat is a stark reminder of the complex and evolving landscape of cybersecurity threats. As nation-states and cybercriminals continue to refine their tactics, it is imperative for organizations to stay vigilant and proactive in their defense strategies. By implementing robust security measures, fostering a culture of cybersecurity awareness, and staying informed about the latest threats and trends, organizations can protect themselves from the ever-present danger of cyber espionage.
FAQ
What is an espionage ecosystem?
An espionage ecosystem is a network of cyber actors, often state-sponsored, that collaborates to conduct espionage activities aimed at infiltrating and exploiting sensitive information.
How do espionage ecosystems operate?
They utilize tactics such as social engineering, supply chain attacks, and zero-day exploits to gain unauthorized access to systems and data.
What are the key players in an espionage ecosystem?
Key players include nation-states, advanced persistent threats (APTs), and cyber mercenaries.
How can organizations protect themselves from espionage threats?
By implementing multi-layered security defenses, conducting regular security audits, and training employees on cybersecurity best practices.
What role does AI play in cyber espionage?
AI is used by attackers to develop sophisticated tactics and by defenders to improve threat detection and response capabilities.
Why is supply chain security important?
Supply chain attacks can compromise less secure elements to eventually target the primary victim, making supply chain security crucial in defense strategies.
Key Takeaways
- Espionage ecosystems involve state-sponsored cyber actors using sophisticated tactics.
- Nation-states, APTs, and cyber mercenaries are key players in these ecosystems.
- Common tactics include social engineering, supply chain attacks, and zero-day exploits.
- Organizations must implement multi-layered defenses and train staff on security awareness.
- AI and ML are increasingly used in both attack and defense strategies.
- Future threats include targeting IoT devices and critical infrastructure.
- Continuous improvement and proactive threat hunting are essential for protection.
Related Articles
- Understanding and Mitigating the VENOM Phishing Threat Targeting Executives [2025]
- The Cybersecurity Boom: Addressing the Privacy Skills Shortage [2025]
- The Global Skills Gap in Modern Cyber Conflict [2025]
- Quantum Computing's Looming Threat to Bitcoin Encryption [2025]
- Beware: How Hackers Exploit LinkedIn's Job Alerts to Steal Your Login Details [2025]
- Understanding the Strategic Significance of OpenAI’s Stargate Data Center in Abu Dhabi [2025]
![Understanding the Espionage Ecosystem Threat [2025]](https://tryrunable.com/blog/understanding-the-espionage-ecosystem-threat-2025/image-1-1775558040984.jpg)



