Cybercriminals Target Vulnerable Sectors as Crypto Fraud Escalates [2025]
In recent years, cybercriminals have shown an alarming tendency to target some of the most vulnerable sectors: schools and hospitals. The FBI's 2025 Internet Crime Report highlights an unsettling rise in cyber-enabled fraud, with over $17.6 billion stolen, and the trend shows no signs of abating. This comprehensive guide delves into the nuances of these cyber threats, offering practical insights and strategies for protection.
TL; DR
- Cybercrime Surge: Schools and hospitals are prime targets due to outdated systems.
- Crypto Fraud Spike: Cryptocurrency scams have led to billions in losses.
- Technical Safeguards: Implementing robust cybersecurity frameworks is essential.
- Awareness and Training: Educating staff on cyber threats is crucial.
- Future Trends: AI-driven defenses will be pivotal in combating these threats.

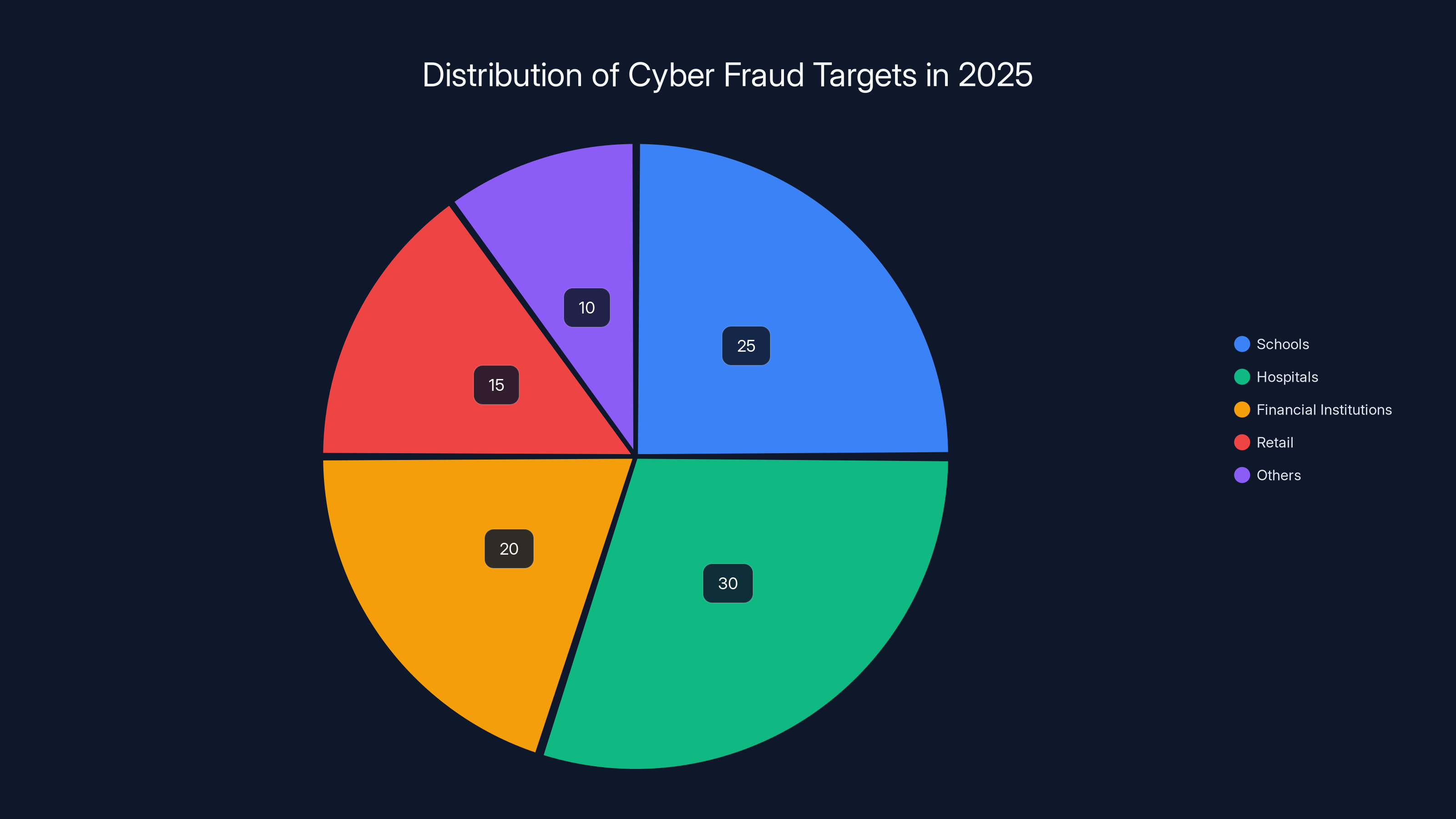
In 2025, schools and hospitals were the most targeted sectors for cyber fraud, accounting for 55% of the total attacks. Estimated data.
Understanding the Cyber Threat Landscape
The digital world has opened up a Pandora's box of possibilities for cybercriminals. They are no longer just targeting financial institutions or corporations but are increasingly setting their sights on schools and hospitals. These entities often lack the robust cybersecurity frameworks needed to fend off such sophisticated attacks.
Why Schools and Hospitals?
Schools and hospitals are particularly enticing targets for cybercriminals for several reasons:
- Outdated Technology: Many educational and healthcare institutions operate on outdated systems that are more vulnerable to breaches. For example, the Kettering Health ransomware attack highlighted the vulnerabilities in healthcare systems.
- Valuable Data: These sectors handle sensitive personal data, making them lucrative targets for identity theft and ransomware attacks.
- Limited Cybersecurity Budgets: Unlike large corporations, schools and hospitals often have limited budgets for cybersecurity, making them easier targets.
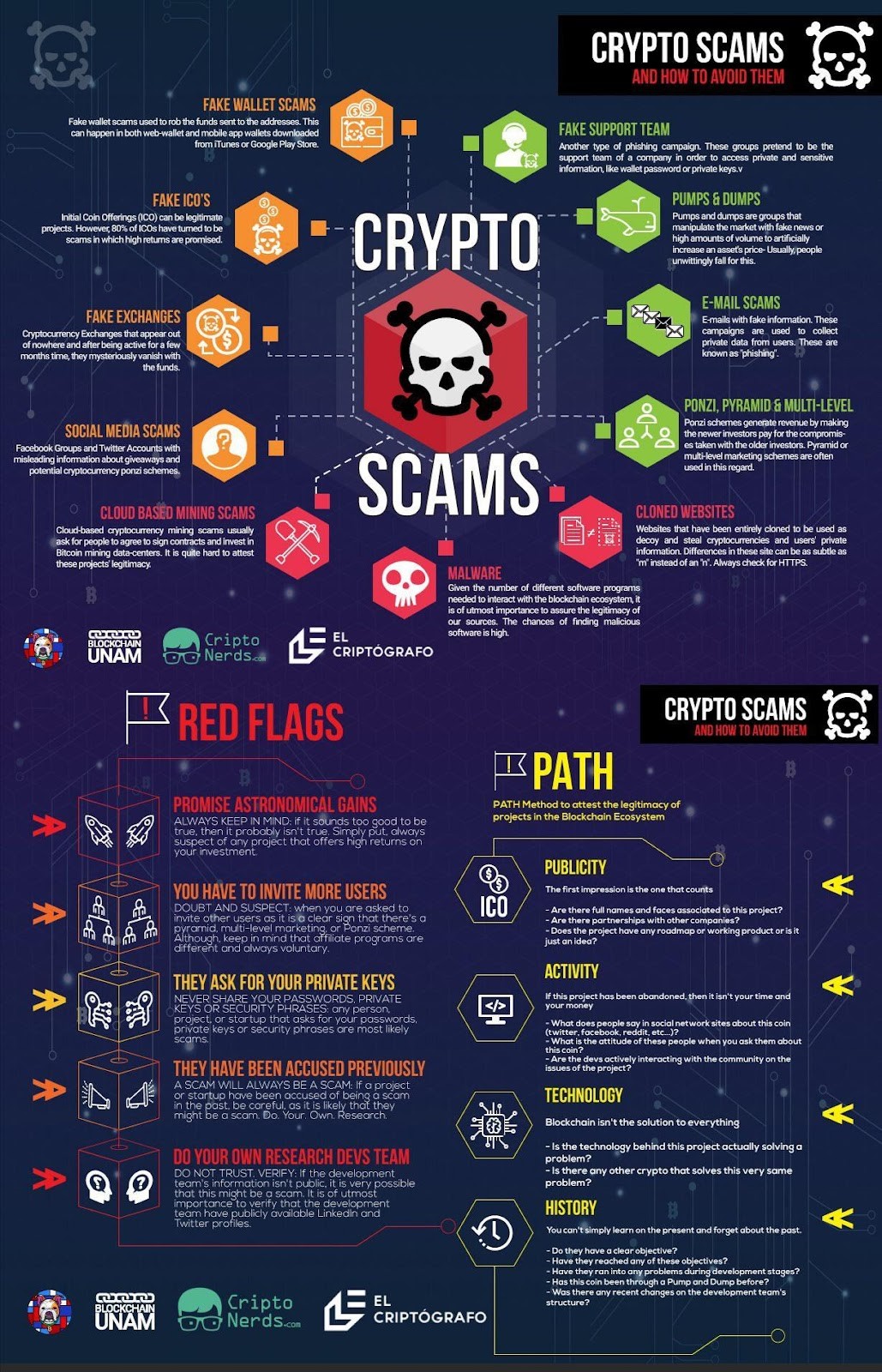
The Rise of Crypto Fraud
Cryptocurrency has seen a meteoric rise in popularity, but with it comes an increase in crypto-related fraud. The decentralized and often anonymous nature of cryptocurrencies makes it an attractive avenue for scammers.
Common Crypto Fraud Schemes
- Investment Scams: Fraudsters promise high returns on crypto investments, only to disappear with the funds. The Maryland Attorney General has issued warnings about such scams on social media platforms.
- Phishing Attacks: Hackers use fake emails and websites to steal cryptocurrency wallet credentials.
- Ponzi Schemes: New investors are paid returns with the capital of newer investors, eventually collapsing when new investments dry up.
QUICK TIP: Always verify the legitimacy of a cryptocurrency investment platform by checking for regulatory compliance and user reviews.
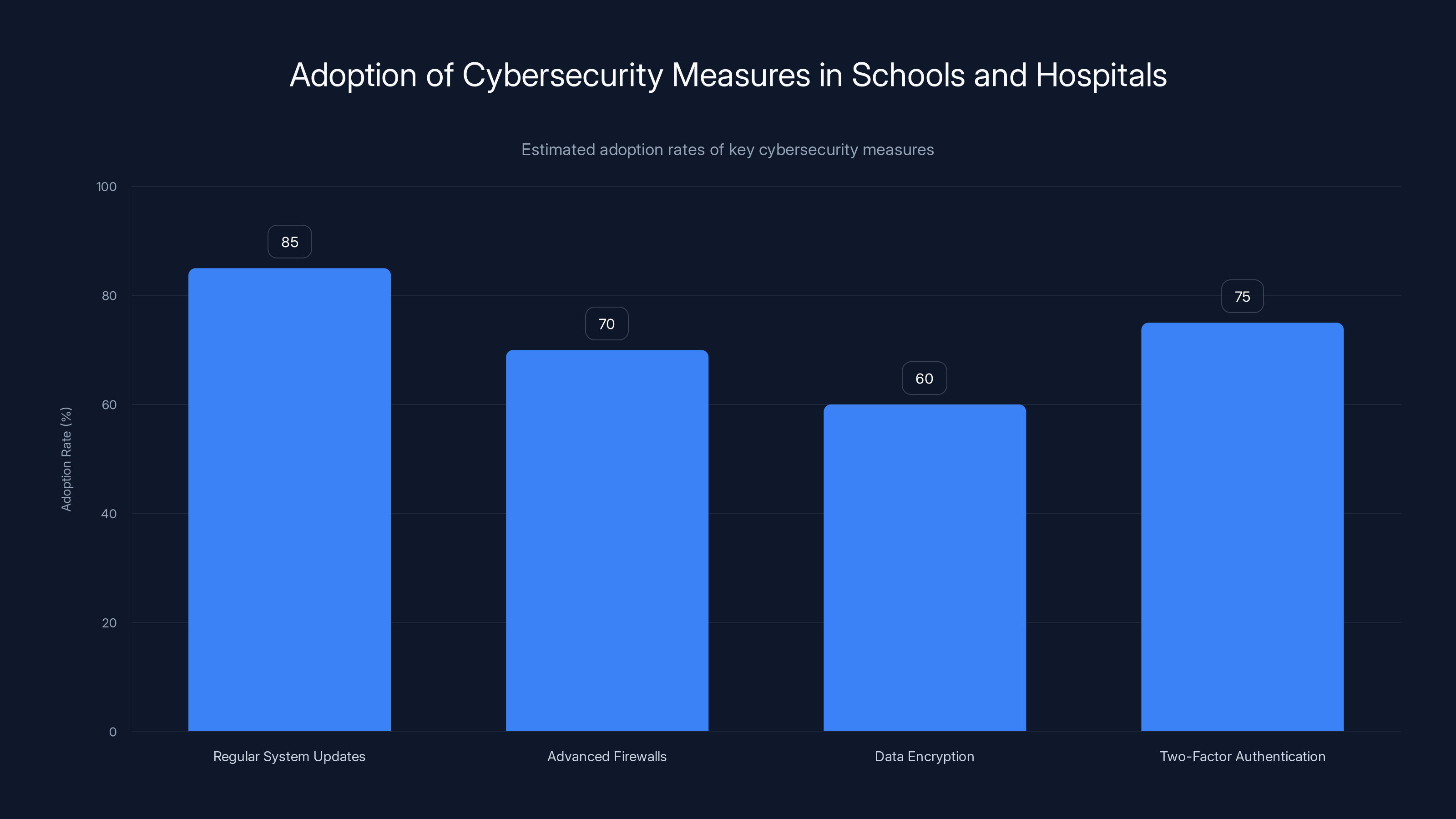
Schools and hospitals are increasingly adopting cybersecurity measures, with regular system updates leading at an estimated 85% adoption rate. Estimated data.
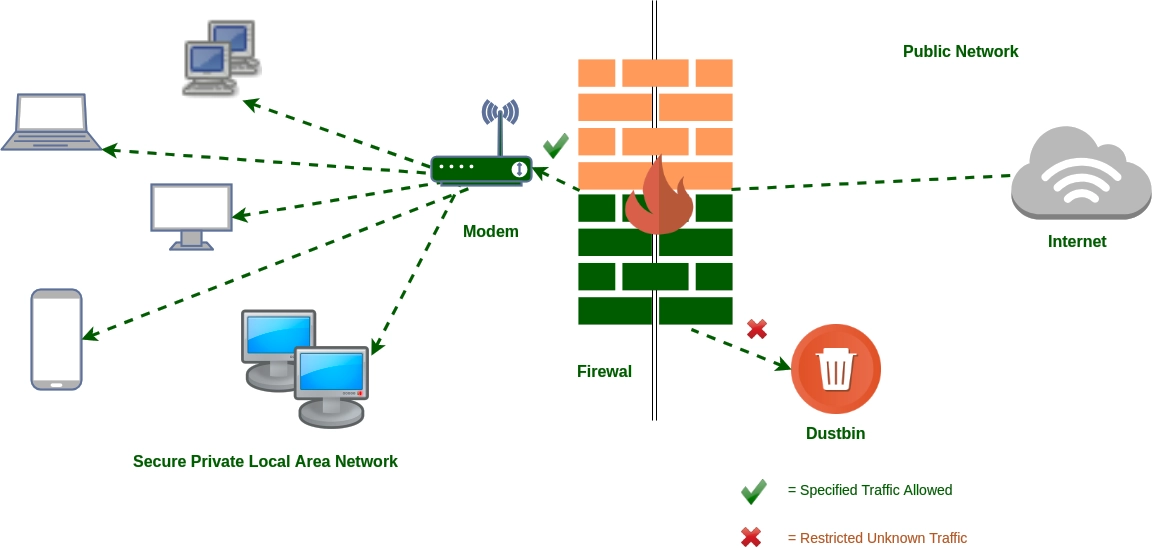
Implementing Technical Safeguards
To combat the growing threat of cybercrime, schools and hospitals need to implement robust cybersecurity measures. Here are some best practices:
- Regular System Updates: Ensure all software and systems are up-to-date to protect against known vulnerabilities.
- Advanced Firewalls: Use next-gen firewalls that offer intrusion prevention and threat detection.
- Data Encryption: Encrypt sensitive data both in transit and at rest.
- Two-Factor Authentication (2FA): Require 2FA for accessing critical systems and data.

Awareness and Training
Human error remains one of the biggest cybersecurity risks. Training staff to recognize and respond to cyber threats can significantly reduce this risk.
Key Training Areas
- Phishing Recognition: Teach employees to identify suspicious emails and links.
- Password Management: Encourage the use of strong, unique passwords and password managers.
- Incident Response: Develop and practice a response plan for potential cyber incidents.
QUICK TIP: Conduct regular phishing simulations to test and reinforce employees' ability to recognize phishing attempts.

Future Trends in Cybersecurity
As cyber threats continue to evolve, so too must our defenses. Here are some trends to watch:
- AI-Driven Cybersecurity: Artificial intelligence can help detect and respond to threats faster than traditional methods. The Information Technology and Innovation Foundation emphasizes the role of AI in enhancing cybersecurity.
- Zero Trust Architecture: This model requires verification for every access attempt, minimizing the risk of unauthorized access.
- Blockchain for Security: Utilizing blockchain technology for securing transactions and data integrity.

Developing a cybersecurity strategy is rated as the most critical step, followed closely by conducting a risk assessment. Estimated data.
Common Pitfalls and Solutions
While implementing cybersecurity measures, institutions often fall into common pitfalls. Here’s how to avoid them:
- Pitfall: Over-reliance on a single security solution. Solution: Implement a multi-layered security approach.
- Pitfall: Neglecting cybersecurity after initial implementation. Solution: Schedule regular security audits and updates.
DID YOU KNOW: Over 60% of small businesses close within six months of a cyber attack due to the financial and reputational damage.

Practical Implementation Guides
To effectively implement cybersecurity measures, consider the following step-by-step guide:
- Conduct a Risk Assessment: Identify key assets and potential threats.
- Develop a Cybersecurity Strategy: Create a comprehensive plan covering all aspects of cybersecurity.
- Implement Security Controls: Deploy technical and organizational measures to mitigate identified risks.
- Monitor and Review: Continuously monitor systems for suspicious activity and review cybersecurity policies regularly.
Case Study: A School's Journey to Cybersecurity
In 2024, Springfield High School fell victim to a ransomware attack that encrypted their entire student record system. With no backup in place, they were forced to pay a hefty ransom. Learning from this, they implemented a robust cybersecurity framework, including regular backups and employee training.
Results
- No further incidents: Their system has remained secure thanks to regular updates and training.
- Improved Response Time: Their incident response plan ensures quick action in case of any suspicious activity.

Recommendations for the Future
To stay ahead of cybercriminals, schools and hospitals should:
- Invest in Cybersecurity: Allocate a significant portion of the budget to cybersecurity measures.
- Collaborate with Experts: Partner with cybersecurity firms for expert guidance and support.
- Stay Informed: Keep abreast of the latest cyber threats and best practices through continuous learning.
QUICK TIP: Join cybersecurity forums and networks to share knowledge and experiences with other professionals.
Conclusion
Cybercrime is an ever-evolving threat that requires constant vigilance and adaptation. By implementing robust cybersecurity measures, training staff, and staying informed, schools and hospitals can protect themselves from becoming the next victim of cybercriminals. With the rise of crypto fraud, being proactive is not just a recommendation—it’s a necessity.
FAQ
What makes schools and hospitals attractive targets for cybercriminals?
Schools and hospitals are often targeted due to their outdated technology, valuable data, and limited cybersecurity budgets. These factors make them easier targets for cybercriminals.
How can institutions protect themselves from crypto fraud?
Institutions can protect themselves by verifying the legitimacy of cryptocurrency investment platforms, educating staff on crypto scams, and implementing robust security measures.
What are the benefits of implementing a multi-layered security approach?
A multi-layered security approach provides comprehensive protection by addressing different types of threats at various points of entry, reducing the risk of a successful cyber attack.
How does AI-driven cybersecurity enhance protection?
AI-driven cybersecurity can detect and respond to threats faster and more accurately than traditional methods, thanks to its ability to analyze large amounts of data quickly and identify patterns indicative of cyber threats.
Why is regular cybersecurity training important?
Regular training helps staff recognize and respond to cyber threats more effectively, reducing the risk of human error, which is a common entry point for cyber attacks.
What role does blockchain play in cybersecurity?
Blockchain technology can enhance cybersecurity by providing secure, tamper-proof transactions and data integrity, making it harder for cybercriminals to alter data.
Key Takeaways
- Cybercrime against schools and hospitals is rising due to outdated systems.
- Crypto fraud has resulted in billions in losses, requiring new security measures.
- Implementing advanced firewalls and encryption is essential for protection.
- Regular staff training can significantly reduce the risk of cyber attacks.
- AI and blockchain are emerging as key technologies in cybersecurity.
- A multi-layered security approach offers comprehensive protection.
- Staying informed about the latest threats is crucial for maintaining security.
Related Articles
- The Global Skills Gap in Modern Cyber Conflict [2025]
- Quantum Computing's Looming Threat to Bitcoin Encryption [2025]
- Your Marketing Stack is an Attack Surface — Is Security Watching? [2025]
- Iranian Hackers: Cold War Tactics and Digital Deceptions [2025]
- Europe's Sovereignty Ambitions Require Smarter Infrastructure [2025]
- Understanding the Espionage Ecosystem Threat [2025]
![Cybercriminals Target Vulnerable Sectors as Crypto Fraud Escalates [2025]](https://tryrunable.com/blog/cybercriminals-target-vulnerable-sectors-as-crypto-fraud-esc/image-1-1775579796018.jpg)



