Understanding and Mitigating the VENOM Phishing Threat Targeting Executives [2025]
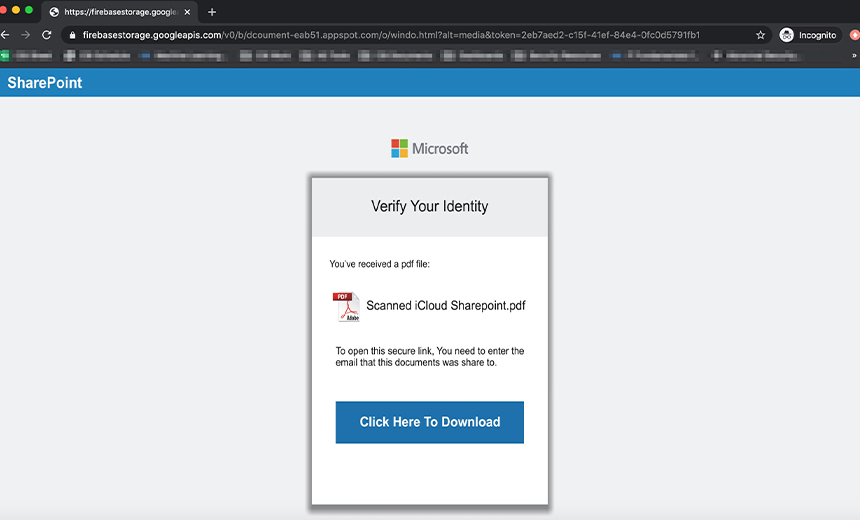
Last month, a well-known tech firm's CFO received an email that looked like a routine Share Point notification. It was personalized, right down to the executive's name, and seemed innocuous enough. But here's the catch: it wasn't a real notification. It was part of a devious phishing scheme known as VENOM that targets business executives with precision, as detailed in TechRadar's report.
TL; DR
- Targeted Phishing: The VENOM campaign uses highly personalized emails to exploit executive trust.
- Advanced Techniques: Attackers employ Unicode QR codes to bypass traditional security filters, a method highlighted by InfoSecurity Magazine.
- Credential Theft: The primary goal is to steal login credentials from high-level executives.
- Risk Mitigation: Comprehensive security training and advanced filtering systems can mitigate risks.
- Future-Proofing: Emerging AI-driven security tools are crucial in adapting to evolving threats, as noted by TechNewsWorld.
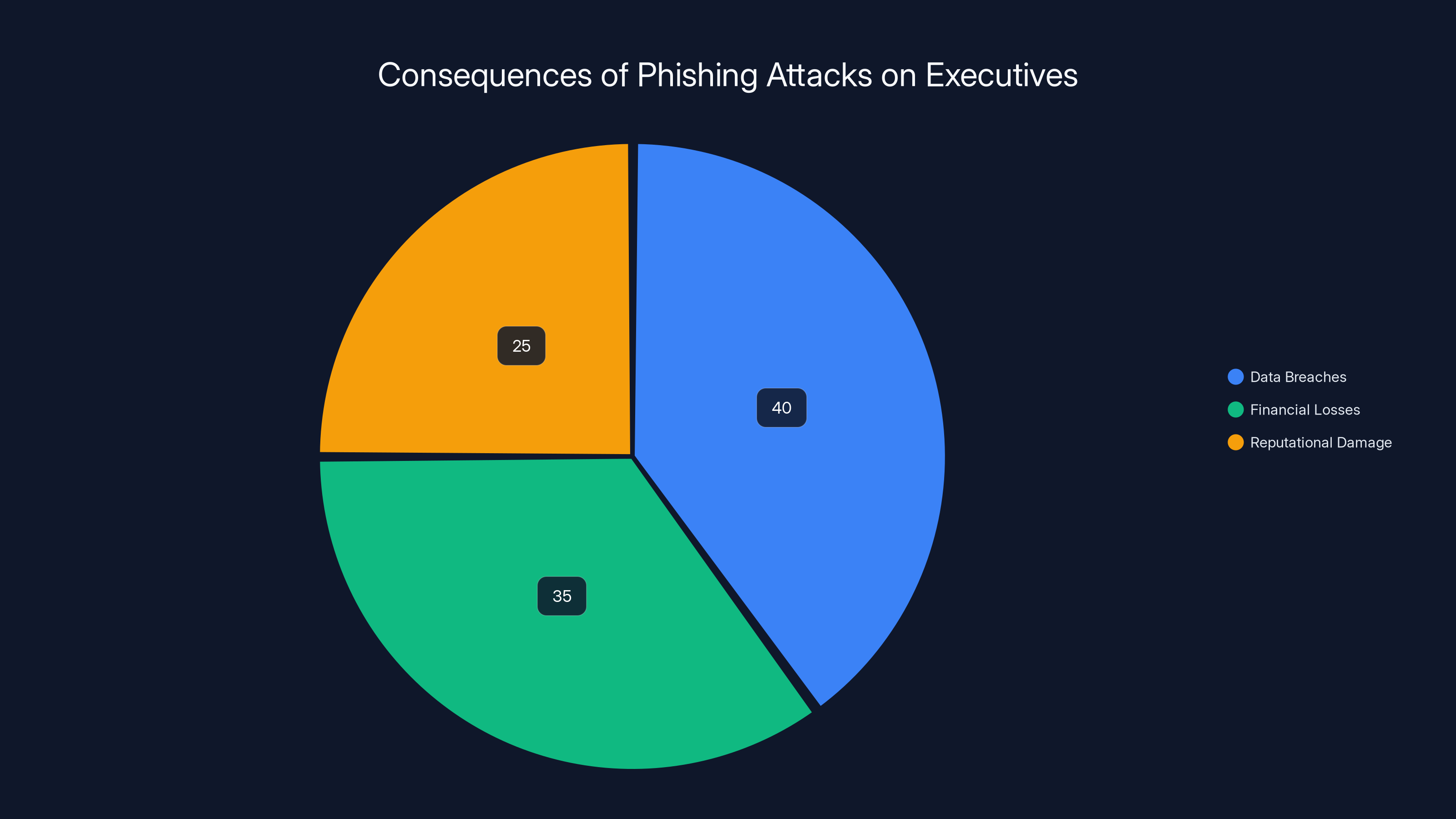
Phishing attacks on executives can lead to data breaches (40%), financial losses (35%), and reputational damage (25%). Estimated data based on typical outcomes.
The Rise of Targeted Phishing Campaigns
Phishing has been around since the early days of the internet. However, these attacks have evolved significantly in recent years. The VENOM phishing kit represents a new breed of targeted attacks that exploit personal data to ensnare victims. Unlike traditional phishing, which casts a wide net, VENOM specifically targets C-suite executives, making these attacks both sophisticated and potentially damaging, as reported by InfoSecurity Magazine.
What Makes VENOM Different?
The VENOM phishing campaign stands out due to its high degree of personalization. Attackers gather personal information about their targets, such as name, position, and even recent activities or interests, to craft convincing emails. These emails mimic legitimate business communications, such as Share Point notifications, to lower the target's guard.
Key Features of VENOM Phishing:
- Personalized Content: Emails are tailored to the recipient's name and position.
- Mimicry of Legitimate Services: Often disguised as notifications from platforms like Share Point.
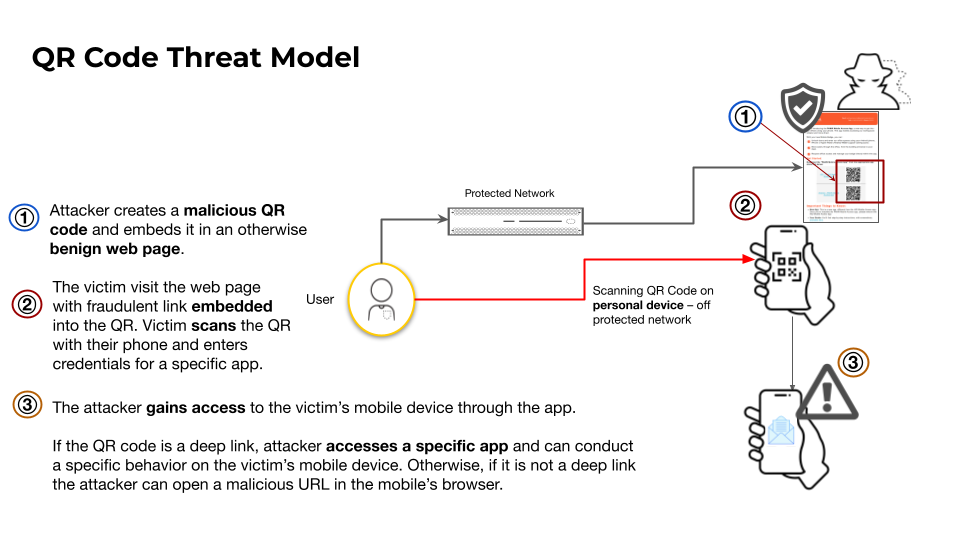
- Use of Unicode QR Codes: Helps bypass traditional email security filters.
- Credential Harvesting: Main objective is to steal login credentials.

AI integration is estimated to be the most effective strategy against phishing, with a 90% effectiveness rating. Estimated data.
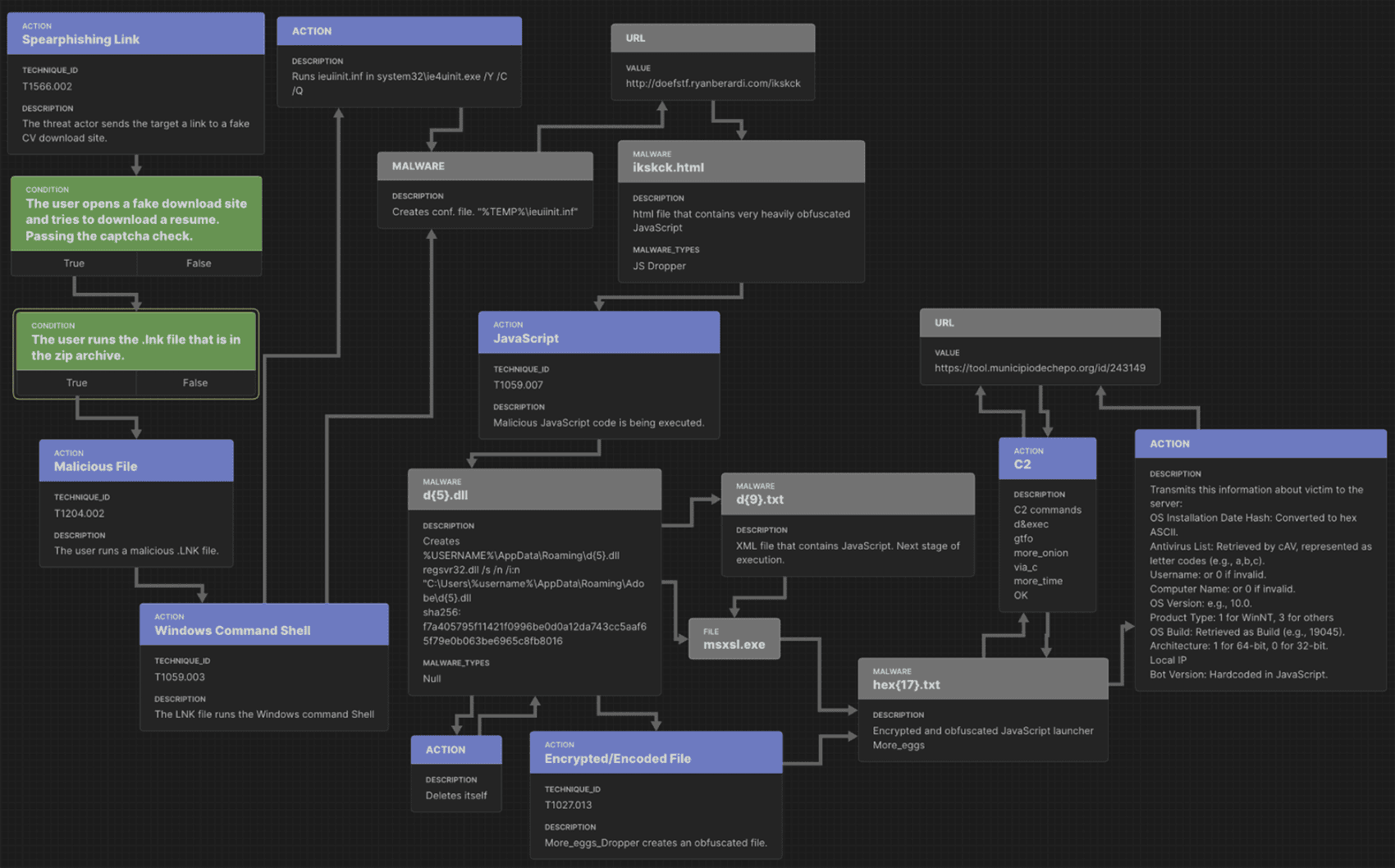
Technical Breakdown of VENOM Phishing
Understanding how VENOM phishing operates is crucial for developing effective countermeasures. Let's delve into the technical aspects of this campaign.
Email Crafting and Delivery
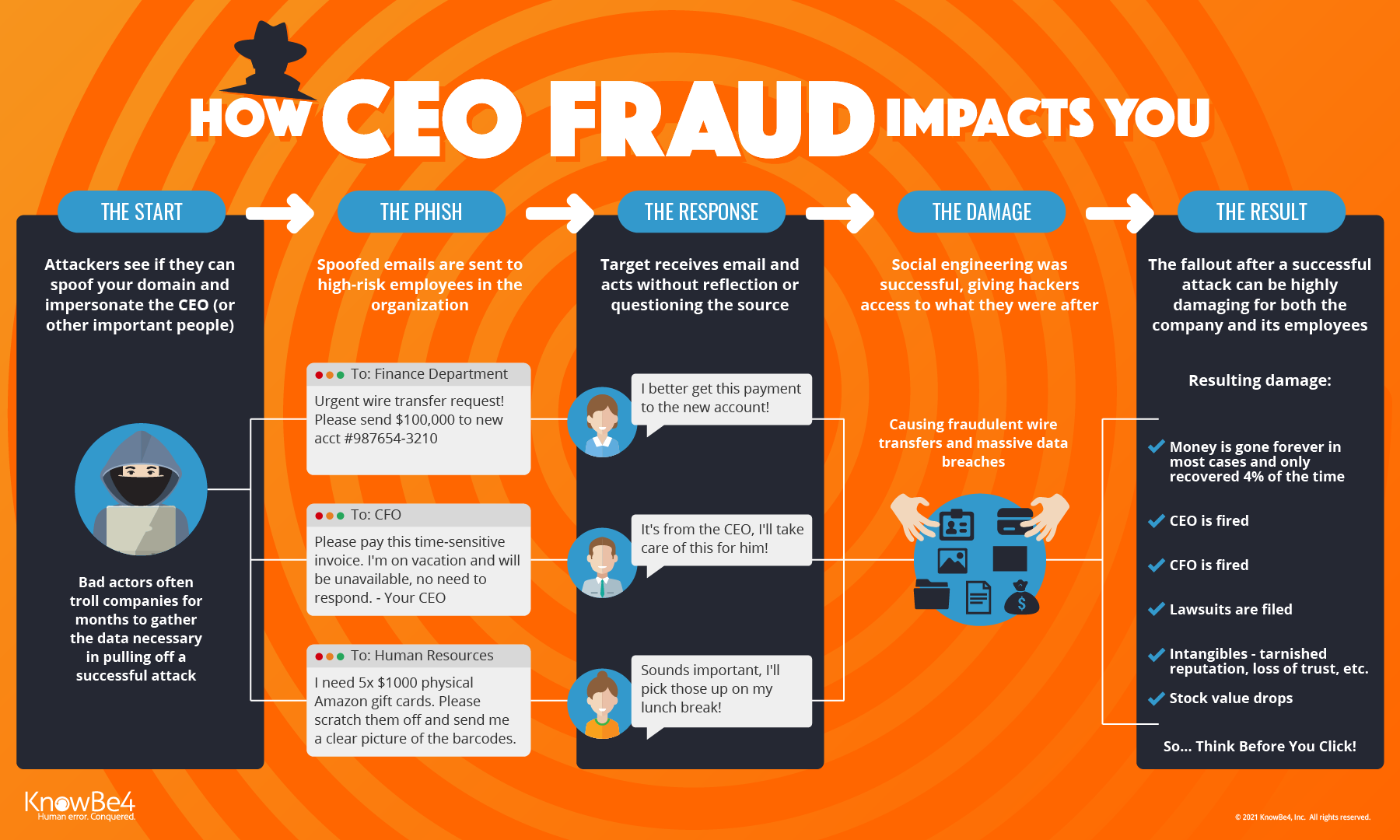
The first step in the VENOM campaign is crafting convincing emails. Attackers use social engineering techniques to collect information about their targets. This data is then used to create emails that appear to come from legitimate sources.
- Social Engineering: Attackers might scour social media, company websites, and public records to gather information.
- Email Spoofing: Using techniques to make emails appear as though they are sent from trusted domains.
- Advanced Phishing Kits: Tools like VENOM automate the process of creating and sending these targeted emails.
Bypassing Security Filters
Traditional security filters often rely on detecting suspicious links or attachments. However, VENOM uses Unicode QR codes cleverly embedded in emails, which are less likely to be flagged by standard security measures.
- Unicode QR Codes: These are visually similar to regular text but can encode malicious URLs.
- Dynamic Content: Some emails include dynamic content that changes after delivery, making it harder to detect.

The Impact on Business Executives
Phishing attacks targeting executives can have devastating effects on organizations. When high-level credentials are compromised, attackers can gain access to sensitive data, financial information, and strategic plans, as highlighted by TechRadar.
Case Study: The Aftermath of a Successful VENOM Attack
Consider a scenario where an executive's credentials are stolen through a VENOM phishing attack:
- Data Breaches: Attackers access confidential company data, leading to potential data breaches.
- Financial Losses: Unauthorized transactions or financial fraud can occur.
- Reputational Damage: Publicized breaches can damage the company's reputation and lead to loss of customer trust.
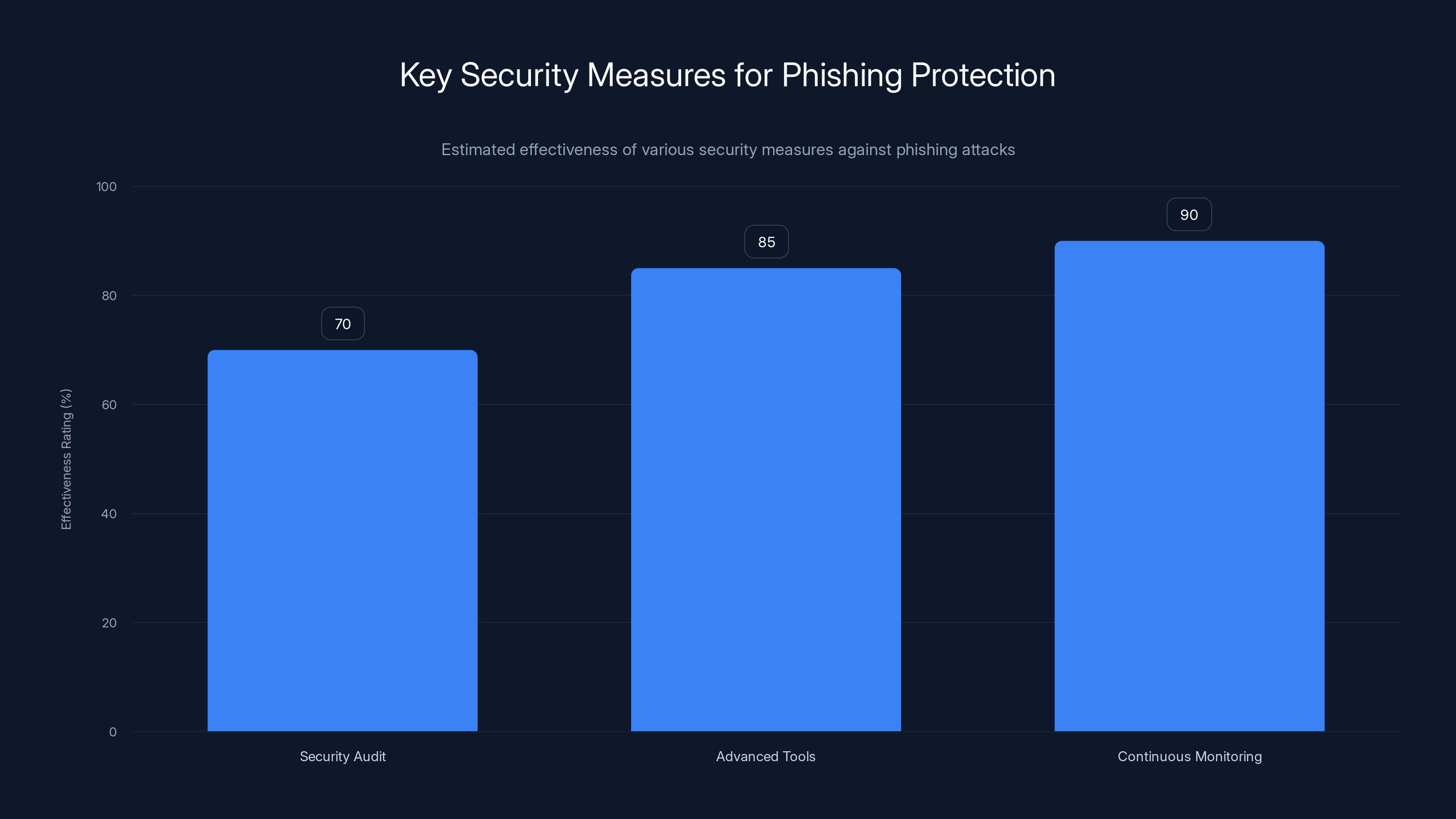
Continuous monitoring and updates are estimated to be the most effective measure against phishing attacks, with a 90% effectiveness rating. Estimated data.
Strategies for Mitigating Phishing Risks
To combat the evolving threat landscape, organizations need to adopt a multi-layered security approach.
Security Awareness and Training
Educating employees, especially executives, about phishing risks is crucial. Regular training sessions can help recognize phishing attempts and understand the potential consequences, as suggested by KnowBe4.
- Phishing Simulations: Conduct regular phishing drills to test response capabilities.
- Security Workshops: Organize sessions focused on recognizing phishing indicators and safe browsing practices.
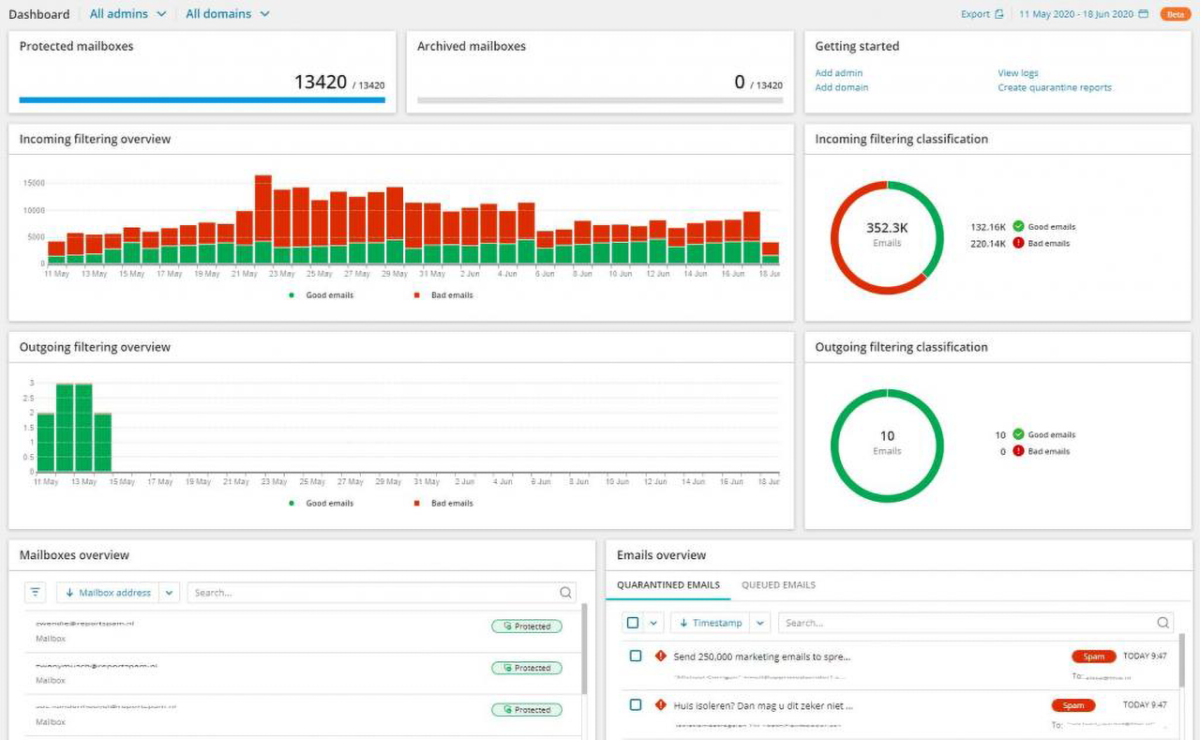
Advanced Email Filtering and Monitoring
Implementing advanced email filtering systems can help detect and block phishing attempts before they reach inboxes.
- AI-Powered Filters: Use machine learning algorithms to identify and quarantine suspicious emails.
- Real-Time Monitoring: Continuously monitor email traffic for signs of phishing activity.
Implementation Guide: Protecting Your Organization
Implementing robust security measures requires a strategic approach. Here's a step-by-step guide to bolster your organization's defenses against phishing attacks.
Step 1: Conduct a Security Audit
Begin by assessing your current security posture. Identify vulnerabilities in your email systems, employee training programs, and data protection protocols.
- Review Security Policies: Ensure policies are up-to-date and comprehensive.
- Assess Technological Infrastructure: Evaluate existing email filtering and monitoring systems.
- Identify High-Risk Individuals: Focus on executives and others with access to sensitive information.
Step 2: Deploy Advanced Security Tools
Utilize cutting-edge security tools designed to detect and prevent phishing attacks.
- AI-Driven Security Tools: Leverage AI to enhance threat detection capabilities.
- Multi-Factor Authentication (MFA): Implement MFA for all critical accounts.
- Network Segmentation: Limit access to sensitive data based on user roles.
Step 3: Continuous Monitoring and Updates
Maintaining a proactive security stance requires continuous monitoring and updates.
- Regular Software Updates: Ensure all security software is up-to-date.
- Threat Intelligence Feeds: Subscribe to feeds that provide real-time threat updates.
- Incident Response Plan: Develop and regularly update a response plan for potential breaches.

AI threat detection is rated highest in effectiveness for phishing defense, followed closely by advanced filtering and blockchain security. Estimated data.
Common Pitfalls and How to Avoid Them
Security measures are only effective when properly implemented. Here are some common pitfalls organizations face and how to avoid them.
Inadequate Training
Issue: Employees and executives may not receive sufficient training to recognize phishing attempts.
Solution: Schedule regular training sessions and keep content updated with the latest phishing tactics.
Overreliance on Technology
Issue: Solely relying on technological solutions without human oversight can lead to gaps in security.
Solution: Combine technology with human analysis to evaluate threats comprehensively.
Ignoring Insider Threats
Issue: Focusing solely on external threats while neglecting internal risks.
Solution: Implement access controls and monitor insider activities to detect suspicious behavior.
Future Trends in Phishing and Security
As technology evolves, so do phishing tactics. Staying ahead of these trends is essential for maintaining robust security.
AI-Driven Phishing Attacks
Attackers are increasingly using AI to craft more convincing phishing emails, making detection more challenging, as discussed in TechNewsWorld.
- AI-Powered Personalization: Emails that adapt content based on recipient behaviors and preferences.
- Deepfake Technology: Use of deepfake audio or video to impersonate company executives.
Blockchain for Security
Blockchain technology offers promising solutions for enhancing security and authenticity.
- Decentralized Identity Verification: Using blockchain to verify user identities and credentials.
- Secure Communication Channels: Blockchain-based messaging platforms for secure communications.
Enhanced Detection Tools
Future security tools will leverage AI and big data to predict and prevent phishing attempts.
- Predictive Analytics: Analyzing patterns to forecast potential phishing tactics.
- Behavioral Analysis: Monitoring user behavior to detect anomalies indicative of phishing.
Summary and Recommendations
The VENOM phishing campaign highlights the evolving threat landscape faced by modern organizations. By understanding the tactics and techniques used in these attacks, businesses can better prepare and protect themselves.
Key Takeaways
- Proactive Defense: Regular training and advanced filtering are critical.
- Continuous Monitoring: Stay updated with the latest threat intelligence.
- AI Integration: Utilize AI for both offensive and defensive security measures.
- Blockchain Potential: Consider blockchain for enhancing security and authentication.
- Vigilance Required: Always verify email sources and links before clicking.
Use Case: Automate your threat intelligence feeds and reports with Runable's AI-powered solutions.
Try Runable For FreeBy adopting these strategies, organizations can build a resilient defense against the sophisticated threats posed by campaigns like VENOM.
FAQ
What is the VENOM phishing campaign?
The VENOM phishing campaign is a sophisticated cyber threat targeting business executives with highly personalized phishing emails designed to steal credentials.
How does VENOM phishing work?
VENOM phishing uses personalized emails, often disguised as legitimate notifications, to trick executives into sharing sensitive information. It employs techniques like Unicode QR codes to bypass security filters.
What are the benefits of advanced email filtering?
Advanced email filtering can detect and block phishing emails before they reach inboxes, reducing the risk of credential theft and data breaches.
How can organizations protect against phishing attacks?
Organizations can protect against phishing by implementing regular training, using advanced security tools, and adopting a proactive security strategy that includes continuous monitoring.
What role does AI play in phishing defense?
AI enhances phishing defense by improving threat detection capabilities and enabling predictive analytics to foresee and mitigate potential threats.
What are the future trends in phishing attacks?
Future trends include AI-driven phishing attacks, increased use of deepfake technology, and the implementation of blockchain for secure communications and identity verification.
How can blockchain improve security?
Blockchain can improve security by providing decentralized identity verification, ensuring data authenticity, and creating secure communication channels.
What should executives do if they suspect a phishing attempt?
Executives should immediately report suspected phishing attempts to their IT department, avoid clicking on any links or downloading attachments, and follow company protocols for handling such incidents.
Related Articles
- Exposing the Cracks: Syria’s Digital Security Challenges in the Modern Era [2025]
- Inside Europe's Major Data Breach: Hacking Gangs, Vulnerabilities, and Future Safeguards [2025]
- Your Marketing Stack is an Attack Surface — Is Security Watching? [2025]
- Iranian Hackers: Cold War Tactics and Digital Deceptions [2025]
- Hackers Are Posting the Claude Code Leak With Bonus Malware | WIRED
- The Alarming Surge in UK Cybercrime: Outpacing Police Staffing [2025]
![Understanding and Mitigating the VENOM Phishing Threat Targeting Executives [2025]](https://tryrunable.com/blog/understanding-and-mitigating-the-venom-phishing-threat-targe/image-1-1775486094160.jpg)



