Inside Europe's Major Data Breach: Hacking Gangs, Vulnerabilities, and Future Safeguards [2025]
Introduction
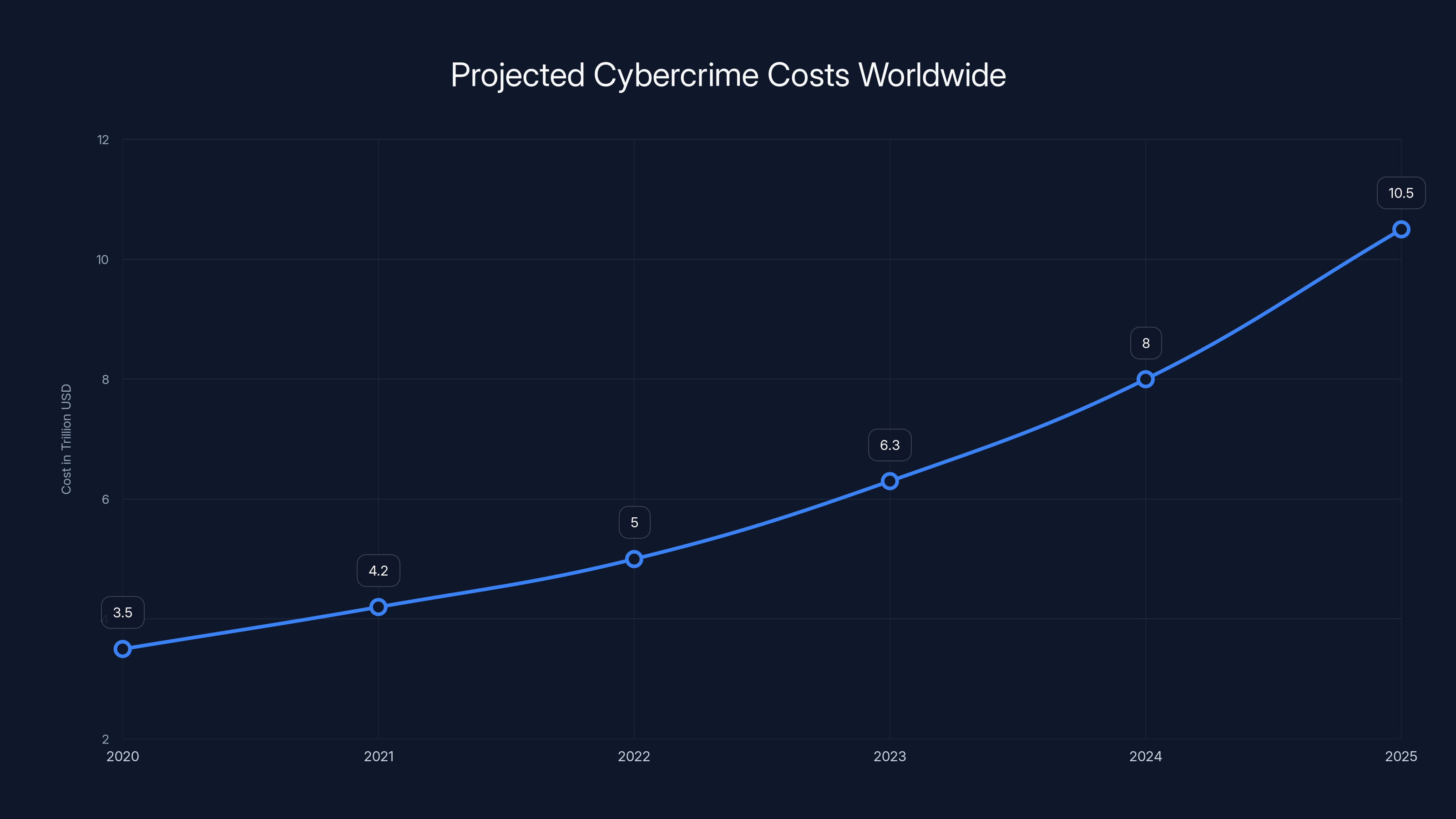
In recent developments, the European Union’s cybersecurity landscape was shaken by a significant data breach that underscored the vulnerabilities within its digital infrastructure. The breach, attributed to a cybercriminal group known as Team PCP, exposed critical data from the EU's executive body, the European Commission. This incident not only highlights the evolving tactics of hacking collectives but also serves as a wake-up call for organizations worldwide to bolster their cybersecurity measures.
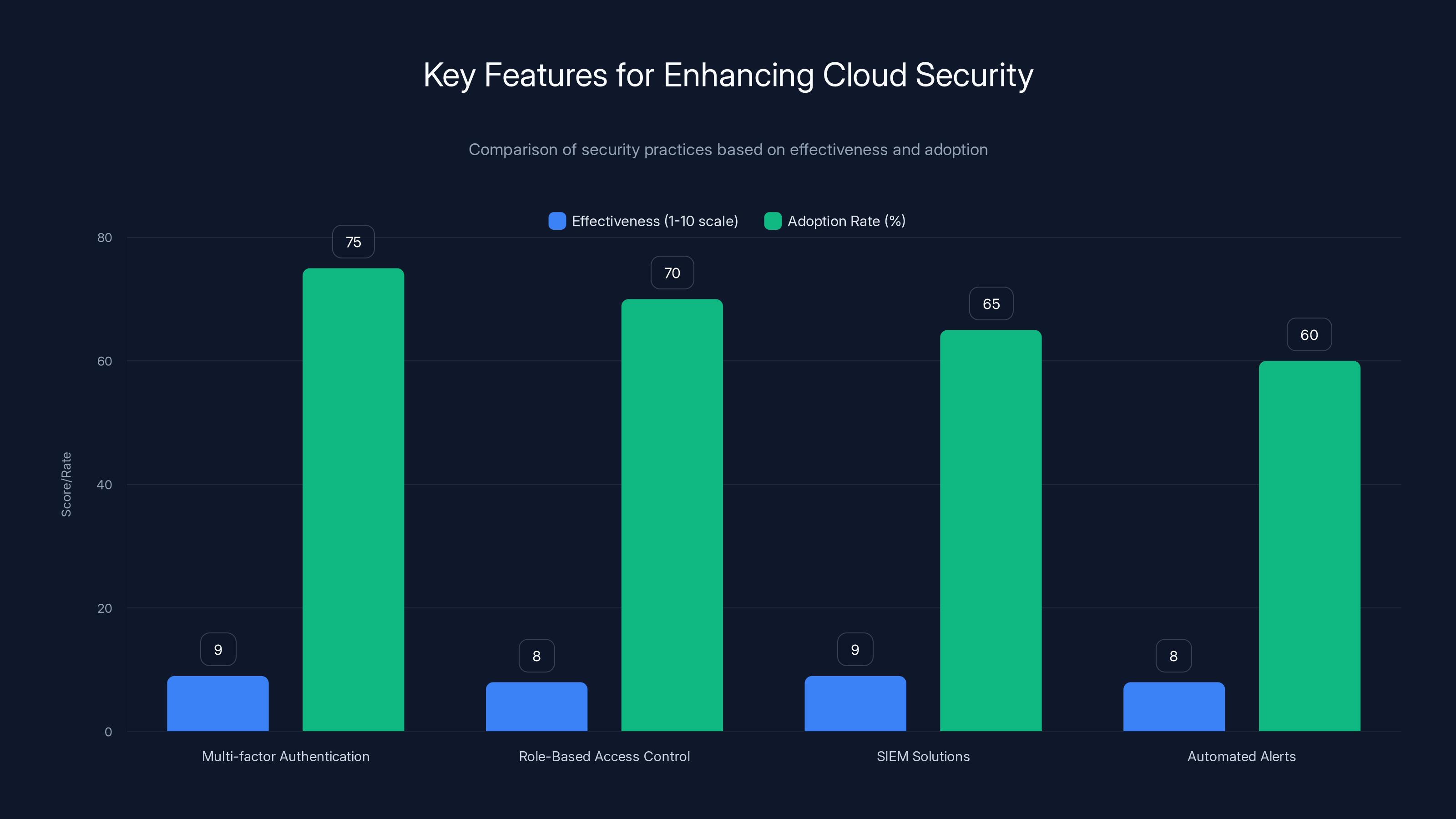
Multi-factor Authentication and SIEM solutions are highly effective in enhancing cloud security. However, their adoption rates vary, with MFA being the most widely adopted. (Estimated data)
TL; DR
- Massive Data Breach: Hackers stole 92GB of data from the EU's cloud infrastructure.
- Hacking Gangs Involved: Team PCP executed the breach, while Shiny Hunters leaked the data.
- Vulnerabilities Exposed: Weaknesses in cloud security and incident response were highlighted.
- Impact: Over 29 EU entities affected, with potential global implications.
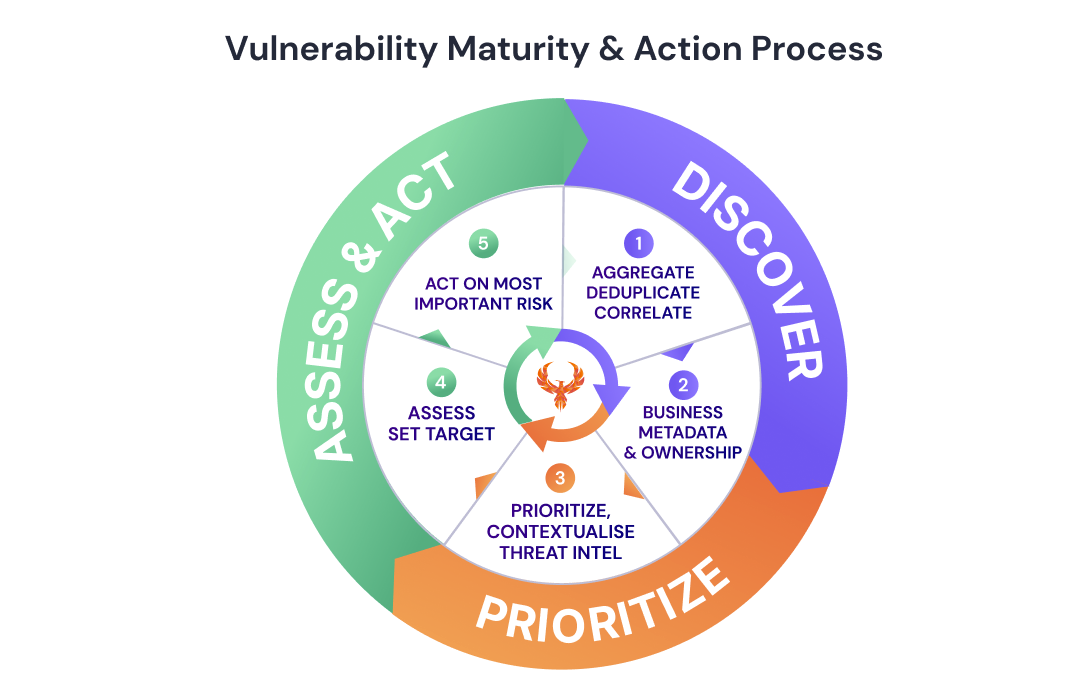
- Future Safeguards: Emphasis on enhanced cloud security and proactive threat intelligence.
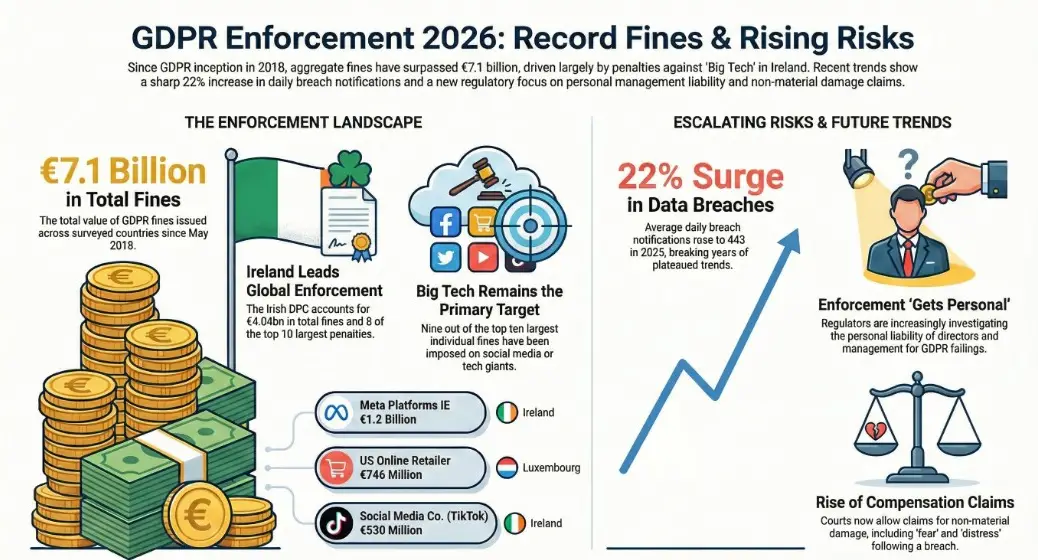
Cybercrime costs are projected to rise significantly, reaching $10.5 trillion by 2025, emphasizing the need for enhanced cybersecurity measures. Estimated data.
Understanding the Breach
The Attack Vector
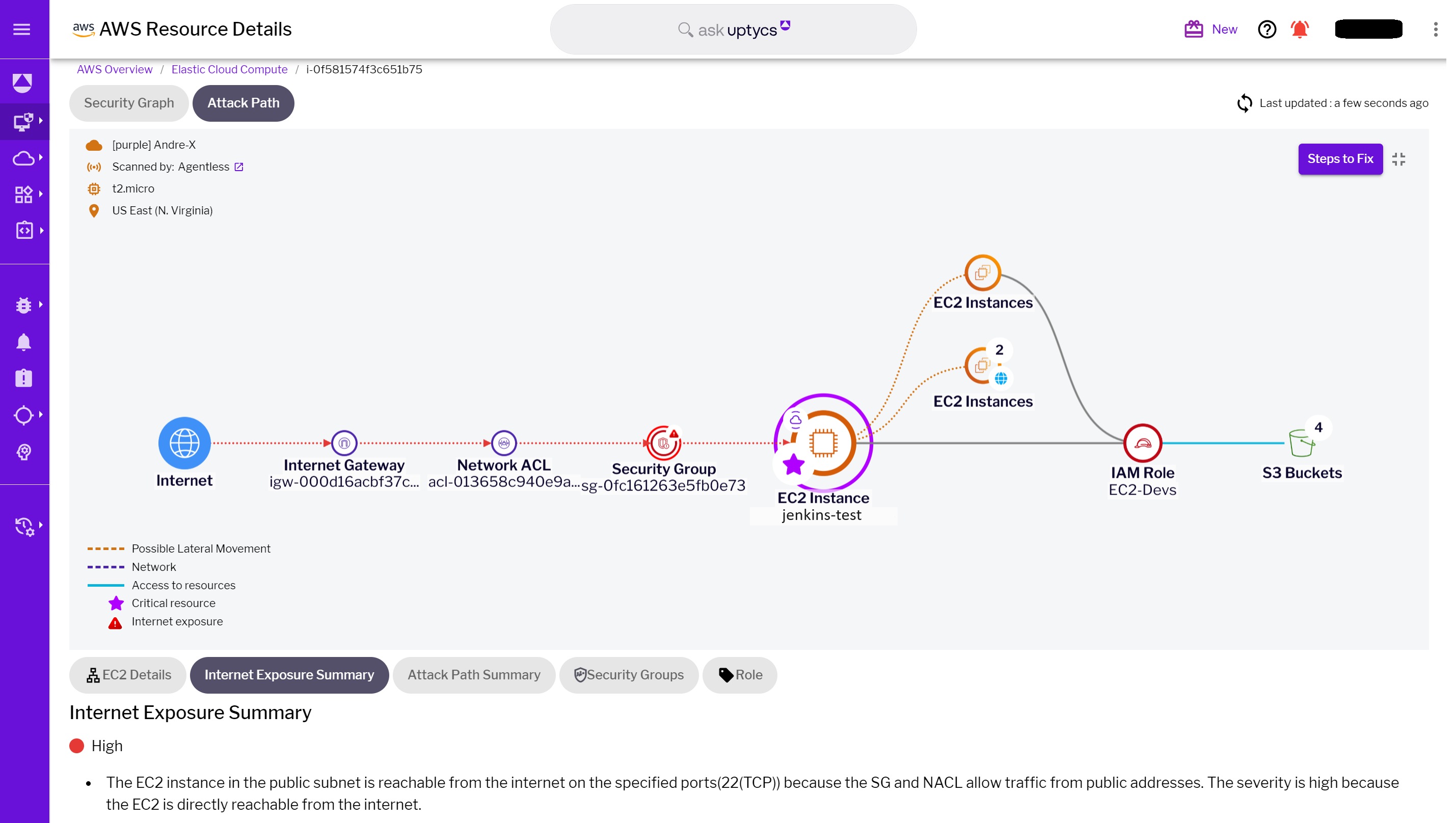
The breach predominantly targeted the EU’s cloud infrastructure, specifically utilizing vulnerabilities within an Amazon Web Services (AWS) account. This incident brings into focus the critical importance of securing cloud environments, which are increasingly becoming targets for sophisticated cyberattacks.
Data Compromised
The attackers managed to extract around 92 gigabytes of compressed data, which included sensitive personal information, such as names, email addresses, and the contents of emails. This breach not only jeopardizes individual privacy but also poses significant risks to organizational confidentiality and integrity.
The Role of Hacking Gangs
Team PCP, a notorious cybercriminal group, orchestrated the initial breach, exploiting specific vulnerabilities within the cloud infrastructure. Following this, the data was leaked online by another group known as Shiny Hunters, highlighting the interconnected nature of cybercriminal activities.
Technical Analysis of the Breach
Cloud Vulnerabilities
Cloud platforms, while offering unparalleled scalability and flexibility, are not immune to cyber threats. The breach at the EU underscores several key vulnerabilities:
- Misconfigured Permissions: Often, cloud resources are left with overly permissive access controls, making them easy targets for attackers.
- Inadequate Monitoring: Without proper monitoring, unauthorized access can go undetected until significant damage is done.
python# Example of a basic AWS IAM policy that could prevent unauthorized access
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "s 3: List Bucket",
"Resource": "arn: aws: s 3::: example-bucket",
"Condition": {
"Ip Address": {
"aws: Source Ip": "203.0.113.0/24"
}
}
}
]
}
Exploited Weaknesses
Cyber attackers frequently exploit weaknesses in cloud configurations and incident response protocols. In this case, inadequate incident response allowed the breach to escalate, leading to a significant data leak.
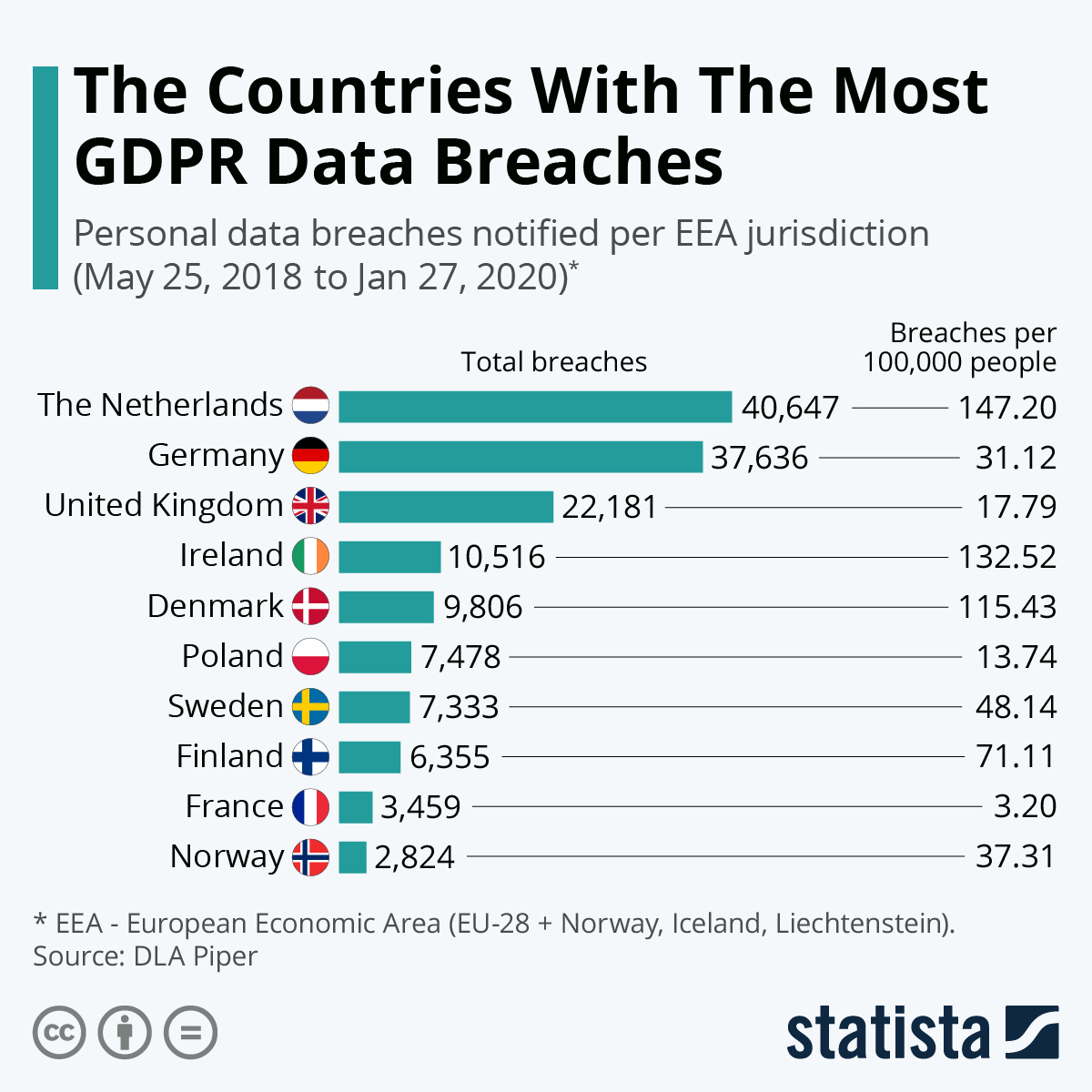
Impact on EU Entities
The ramifications of the breach are extensive, affecting at least 29 EU entities. These include potential leaks of sensitive internal communications and personal data, which can have cascading effects on political, economic, and social fronts.
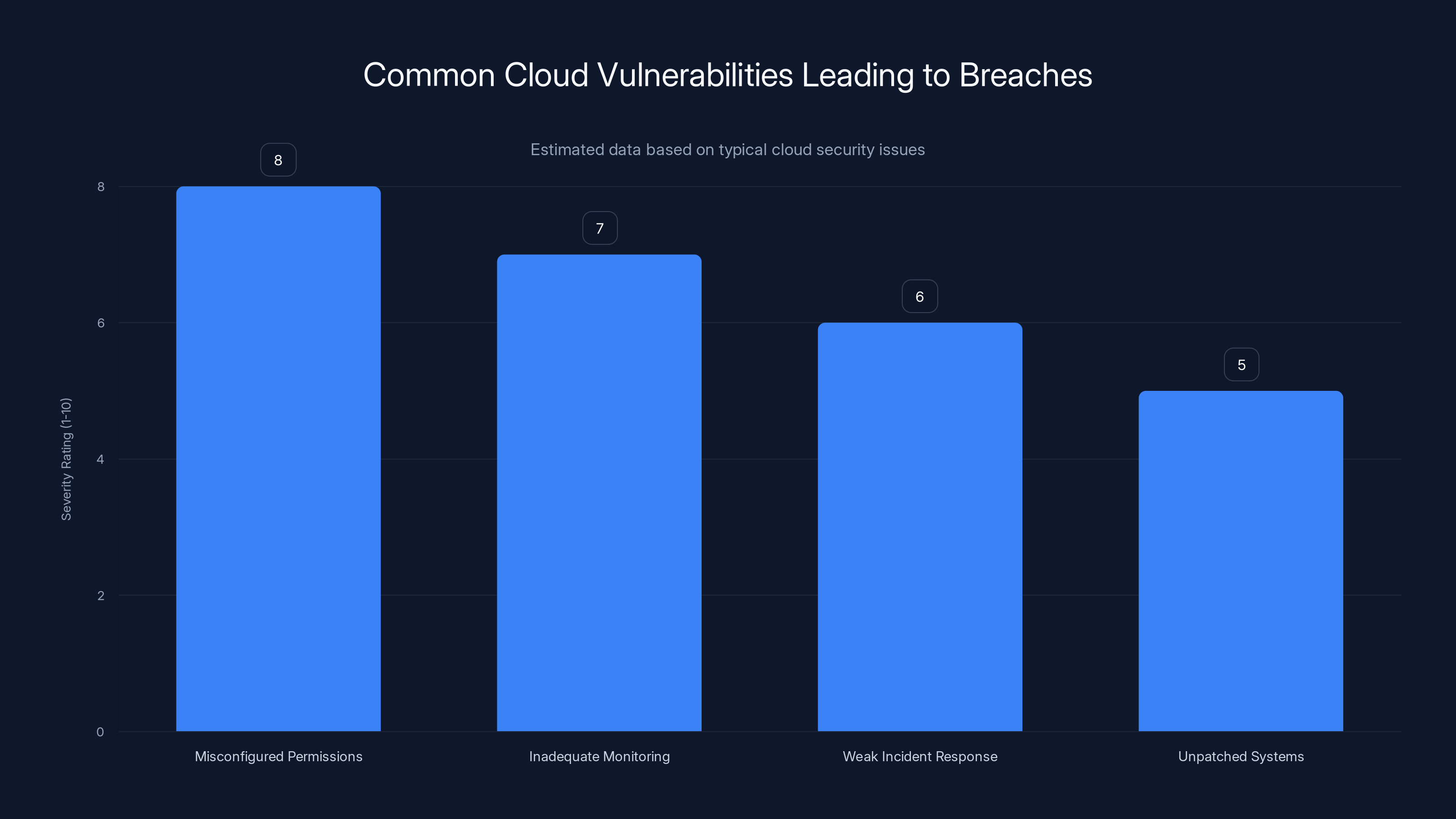
Misconfigured permissions and inadequate monitoring are the most severe vulnerabilities, often leading to significant breaches. Estimated data based on common security assessments.
Common Pitfalls in Cloud Security
Overlooked Security Best Practices
Organizations often neglect basic security principles, such as regular updates and patches, leading to vulnerabilities that cybercriminals can exploit. Additionally, the complexity of cloud security configurations can result in accidental exposure of sensitive data.
Insufficient Backup and Recovery
A robust backup and recovery strategy is critical to minimize the impact of data breaches. However, many organizations lack comprehensive plans or fail to test their effectiveness regularly.

Best Practices for Enhancing Cloud Security
Implementing Strong Access Controls
Access controls should be configured to follow the principle of least privilege, ensuring that users only have access to the resources necessary for their roles.
- Multi-factor Authentication (MFA): Enforce MFA for all accounts to add an extra layer of security.
- Role-Based Access Control (RBAC): Use RBAC to define permissions based on user roles, limiting unnecessary access.
Continuous Monitoring and Threat Detection
Real-time monitoring and threat detection are vital in identifying and mitigating security incidents before they escalate.
- Security Information and Event Management (SIEM): Implement SIEM solutions to collect and analyze security data across your infrastructure.
- Automated Alerts: Set up automated alerts for suspicious activities, enabling rapid response to potential threats.
shell# Example of a Cloud Watch alarm for unauthorized login attempts
aws cloudwatch put-metric-alarm --alarm-name Unauthorized Login Attempts \
--metric-name Failed Login Attempts --namespace AWS/IAM \
--statistic Sum --period 300 --threshold 5 \
--comparison-operator Greater Than Or Equal To Threshold \
--evaluation-periods 1

The Future of Cybersecurity in the EU
Proactive Threat Intelligence
Leveraging threat intelligence can help organizations anticipate and counteract cyber threats more effectively. By understanding the tactics, techniques, and procedures (TTPs) of threat actors, organizations can develop more robust security postures.
Strengthening Policy and Collaboration
The EU must enhance its cybersecurity policies and foster collaboration among member states to build a unified defense against cyber threats. Initiatives like cross-border threat sharing and coordinated incident response can significantly improve collective security.
Conclusion
The data breach affecting the European Commission serves as a stark reminder of the vulnerabilities that exist within our digital infrastructure. By understanding the tactics of hacking gangs and implementing robust security measures, organizations can better protect themselves against future threats. As cybercriminals continue to evolve, so too must our defenses, ensuring a secure digital future for all.
FAQ
What was the scope of the EU data breach?
The breach involved around 92 gigabytes of data, including personal and sensitive information, affecting at least 29 EU entities.
Who were the groups involved in the breach?
The cybercriminal group Team PCP orchestrated the breach, with the data later leaked by Shiny Hunters.
How can organizations improve their cloud security?
Implementing strong access controls, continuous monitoring, and robust incident response strategies are crucial for enhancing cloud security.
What are the future trends in cybersecurity?
The focus will be on proactive threat intelligence, policy strengthening, and cross-border collaboration to counteract evolving cyber threats.
Why is cloud security critical?
Cloud environments are increasingly targeted by cybercriminals due to their expansive use and potential vulnerabilities, making robust security essential.
How does threat intelligence help in cybersecurity?
Threat intelligence provides insights into threat actor behaviors, enabling organizations to anticipate and mitigate potential cyber threats effectively.

Key Takeaways
- Massive data breach impacted 29+ EU entities.
- TeamPCP and ShinyHunters involved in the breach.
- Exposed vulnerabilities in EU's cloud security.
- Emphasis on proactive threat intelligence needed.
- Future cybersecurity trends focus on policy and collaboration.
- Importance of strong access controls and monitoring.
Related Articles
- Unraveling the EU Cyberattack: A Deep Dive into the Breach and Its Implications [2025]
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- Duc Money Transfer Site Data Breach: A Comprehensive Guide [2025]
- Laughing RAT: The New Malware Threat in 2025
- Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
- The Hidden Dangers of AI: What If Your AI Agent Is Working Against You? [2025]
![Inside Europe's Major Data Breach: Hacking Gangs, Vulnerabilities, and Future Safeguards [2025]](https://tryrunable.com/blog/inside-europe-s-major-data-breach-hacking-gangs-vulnerabilit/image-1-1775232264347.jpg)



