Understanding Computer Vulnerabilities to TEMPEST Attacks [2025]
Computers are leaking more than just data through malware and tracking. They leak information through physics. The movements of hard drives, keystrokes, and even electric charges emit radio waves, sound, and vibrations—information that can be intercepted and decoded by those with the right skills and equipment. This method, known as TEMPEST, has been a concern since the mid-20th century, identified as a potential vulnerability by the NSA.
TL; DR
- TEMPEST Attacks: These involve intercepting electromagnetic leaks from devices to access sensitive data.
- Historical Context: First identified in the 1940s, TEMPEST has been a longstanding security concern.
- Current Threats: With advancements in technology, these attacks are becoming more feasible.
- Defense Mechanisms: Shielding and other countermeasures are crucial for protection.
- Legislative Action: U.S. lawmakers are pushing for investigations into these vulnerabilities.

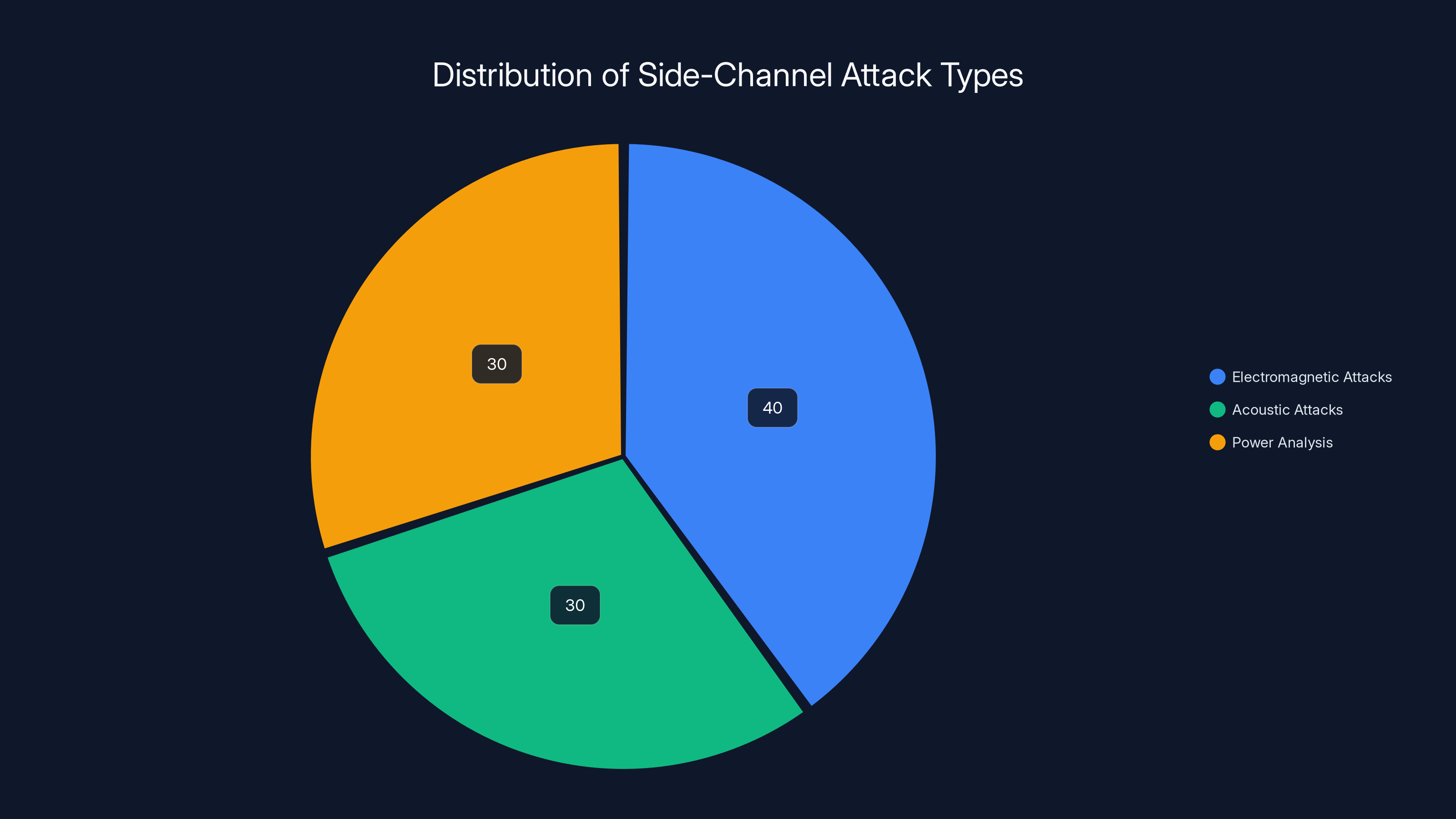
Electromagnetic attacks are estimated to be the most common type of side-channel attack, accounting for 40% of occurrences. Estimated data.
The Historical Context of TEMPEST
The Origins of TEMPEST
Back in the 1940s, Bell Labs discovered that their encryption machines for the military emitted signals detectable from afar. This discovery led to the realization that electromagnetic emissions could be exploited to retrieve sensitive information.
Early Government Responses
The U.S. government, recognizing the potential threat, began to develop countermeasures. This included the creation of Sensitive Compartmented Information Facilities (SCIFs) where sensitive information could be accessed securely, shielded from potential eavesdropping.
Evolution Over Decades
Since its discovery, TEMPEST has evolved, with various methods developed to intercept these emissions. These techniques are collectively referred to as side-channel attacks.
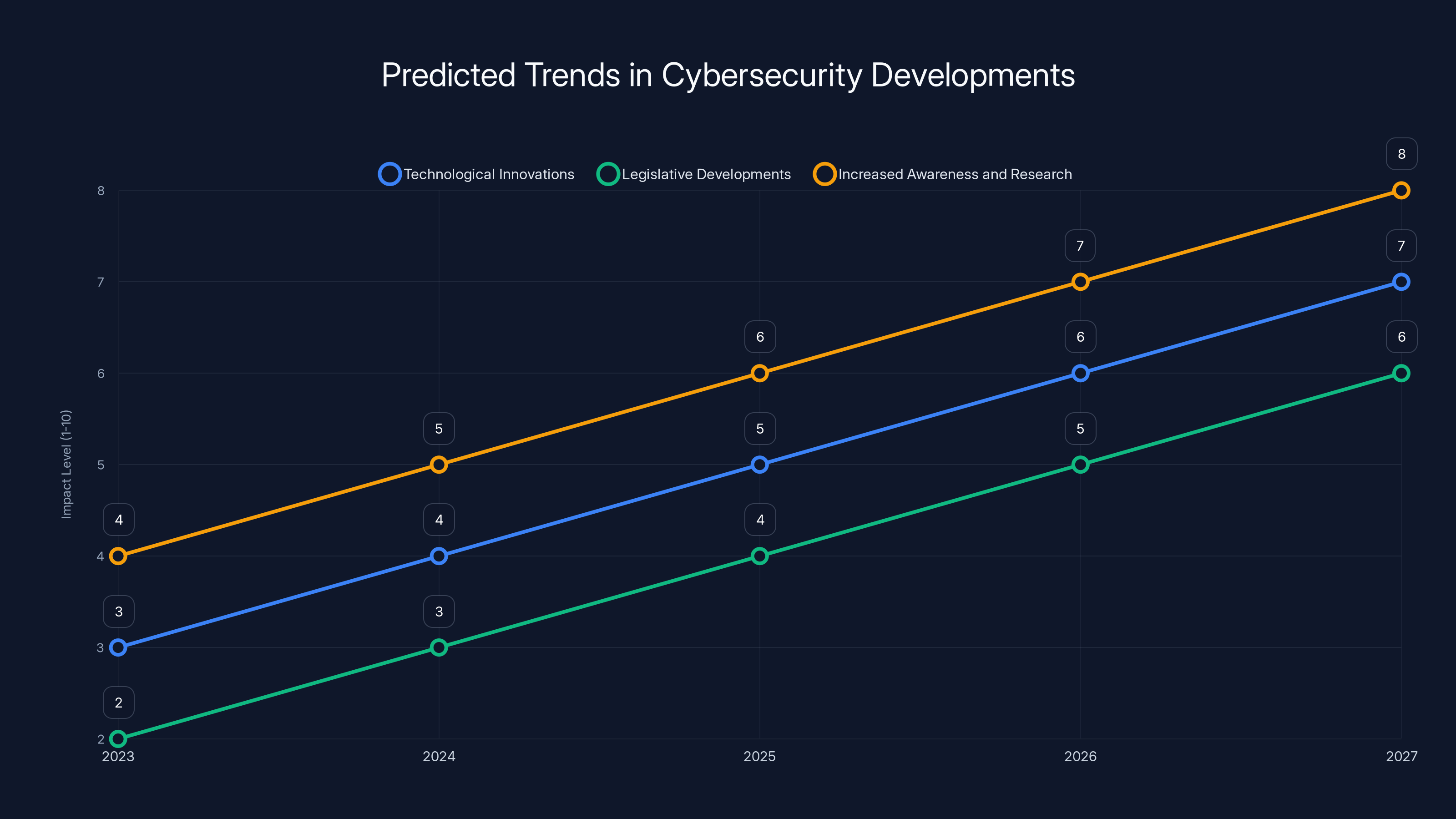
Estimated data suggests a steady increase in technological innovations, legislative developments, and awareness in cybersecurity over the next five years.
Understanding Side-Channel Attacks
What Are Side-Channel Attacks?
Side-channel attacks exploit indirect information leakage, such as electromagnetic emissions, to gain unauthorized access to data. Unlike traditional attacks, they do not rely on software or network vulnerabilities.
Types of Side-Channel Attacks
- Electromagnetic Attacks: These focus on capturing emissions from electronic devices.
- Acoustic Attacks: These involve analyzing the sounds produced by devices to extract data.
- Power Analysis: This examines the power consumption patterns of a device to infer information.
Real-World Examples
In 2015, researchers from Tel Aviv University demonstrated how electromagnetic emanations from a computer's processor could be captured using a simple device costing less than $300.

The Modern Threat Landscape
Technological Advancements
With the rise of Internet of Things (IoT) devices, the surface area for potential attacks has expanded. Modern devices emit a variety of signals that can potentially be intercepted.
Current Vulnerabilities
Despite advancements in cybersecurity, many consumer devices remain vulnerable to these types of attacks. The lack of built-in countermeasures in consumer electronics is a significant concern.
Legislative Concerns
Recently, U.S. lawmakers have called for investigations into the vulnerabilities of consumer electronics to TEMPEST-style attacks. They argue that manufacturers should be required to implement protective measures.

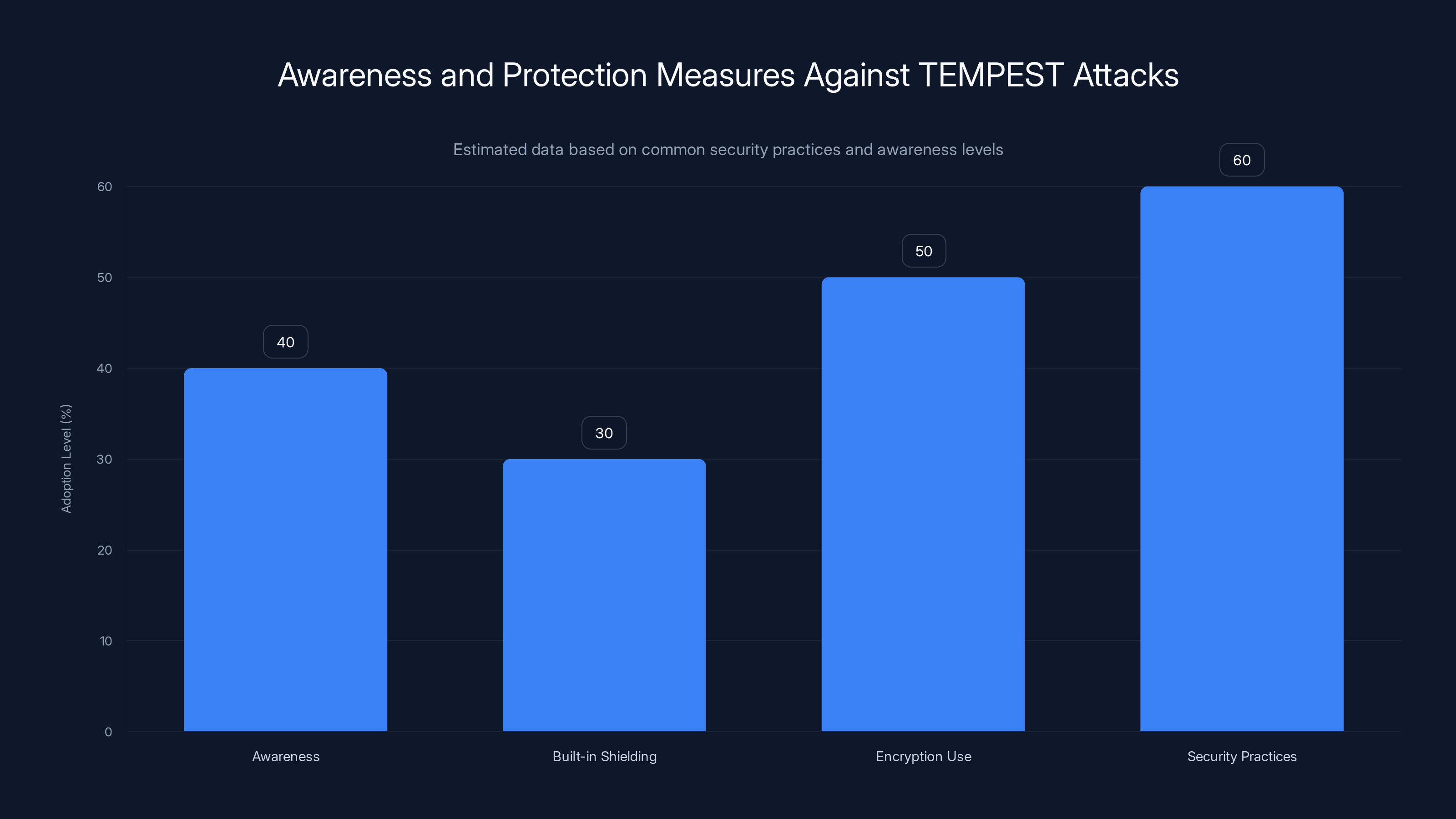
Estimated data suggests that while awareness of TEMPEST attacks is moderate, the adoption of protective measures like encryption and security practices is higher.
Defending Against Side-Channel Attacks
Shielding and Isolation
One of the primary defenses against TEMPEST attacks is physical shielding. This involves enclosing devices in materials that block electromagnetic emissions.
Encryption and Signal Obfuscation
Advanced encryption techniques can help protect data even if physical emissions are intercepted. Signal obfuscation methods are also being researched to further secure devices.
Policy and Compliance
Governments and organizations are urged to adopt stricter security policies and compliance standards to ensure that devices are protected against side-channel attacks.

Future Directions and Predictions
Technological Innovations
As technology evolves, so do the methods of attack and defense. Emerging technologies like quantum computing could offer new ways to secure devices against side-channel attacks.
Legislative Developments
We can expect more legislative actions aimed at improving the security of consumer electronics. Lawmakers are likely to push for mandatory security standards.
Increased Awareness and Research
As awareness grows, more research will be conducted to understand and mitigate these vulnerabilities. This is crucial for staying ahead of potential threats.
Conclusion
The threat of TEMPEST and side-channel attacks is real, and it's imperative that both consumers and manufacturers take action. By understanding these vulnerabilities and implementing effective countermeasures, we can better protect sensitive information from being compromised.
FAQ
What are TEMPEST attacks?
TEMPEST attacks involve intercepting electromagnetic emissions from electronic devices to access sensitive data. They exploit the physical properties of devices, rather than software vulnerabilities.
How do side-channel attacks work?
Side-channel attacks work by capturing indirect information leakage, such as electromagnetic emissions or power consumption, to gain unauthorized access to data.
What are the benefits of understanding TEMPEST?
Understanding TEMPEST allows individuals and organizations to implement effective security measures, thus protecting sensitive information from potential eavesdropping.
How can individuals protect themselves from these attacks?
Individuals can protect themselves by using devices with built-in shielding, employing encryption, and following security best practices.
Are there any legal requirements for manufacturers regarding TEMPEST?
Currently, there are limited legal requirements, but U.S. lawmakers are pushing for investigations and potential legislation to mandate protective measures in consumer electronics.
Key Takeaways
- TEMPEST attacks exploit electromagnetic emissions to access data.
- Side-channel attacks are evolving with technology.
- Shielding and encryption are critical defenses.
- Legislative action is likely to increase in response to these vulnerabilities.
- Awareness and research are crucial for future security.
Related Articles
- A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals | WIRED
- How Palantir, Microsoft, Amazon, and Google Power Trump’s Immigration Crackdown | WIRED
- The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]
- Digital Warfare: The Role of Cyber Operations in Modern Conflicts [2025]
- How Google's Accelerated Chrome Release Cycle Impacts Developers and Users [2025]
- The Sub-$500 PC Market: Thriving Against All Odds [2025]
![Understanding Computer Vulnerabilities to TEMPEST Attacks [2025]](https://tryrunable.com/blog/understanding-computer-vulnerabilities-to-tempest-attacks-20/image-1-1772627649737.jpg)



