Digital Warfare: The Role of Cyber Operations in Modern Conflicts [2025]
In today's interconnected world, the battlefield has expanded beyond the physical realm. Cyber operations have become a crucial component of modern warfare, offering unprecedented capabilities in intelligence gathering, psychological operations, and support for kinetic strikes. This article delves into how cyber operations are reshaping conflicts, using the recent war against Iran as a case study.
TL; DR
- Cyber operations are integral to modern warfare, supporting both intelligence and kinetic operations.
- Hacked infrastructure, like traffic cams and TVs, provides real-time intelligence and psychological impact.
- Coordinated cyber attacks can disrupt communications, impacting both military and civilian operations.
- Cyber capabilities allow for precision strikes and reduced collateral damage.
- Future conflicts will likely see an increased reliance on cyber operations, necessitating robust cyber defenses.
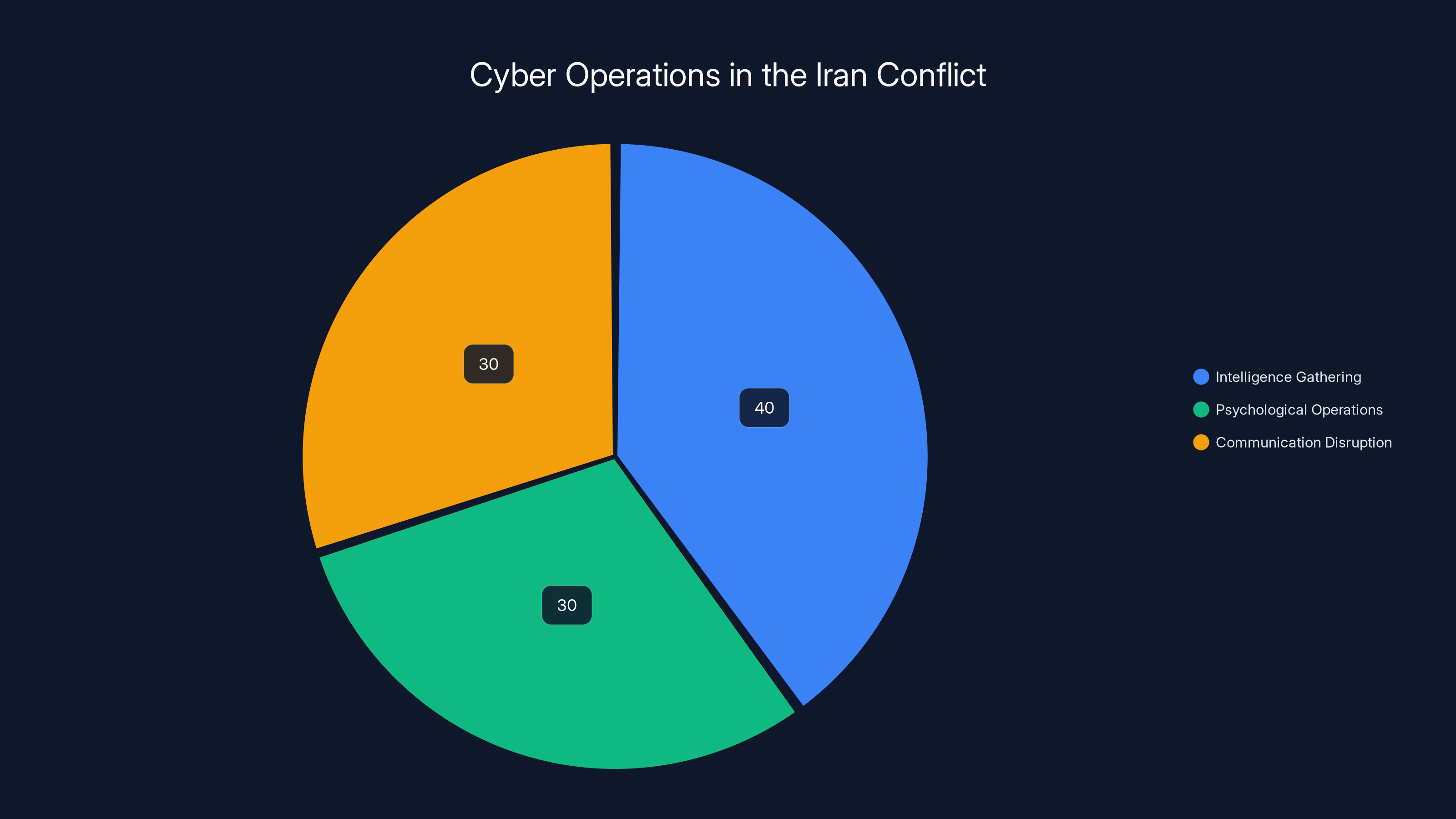
Estimated data suggests a balanced distribution of cyber operations with a slight emphasis on intelligence gathering, crucial for strategic military planning.
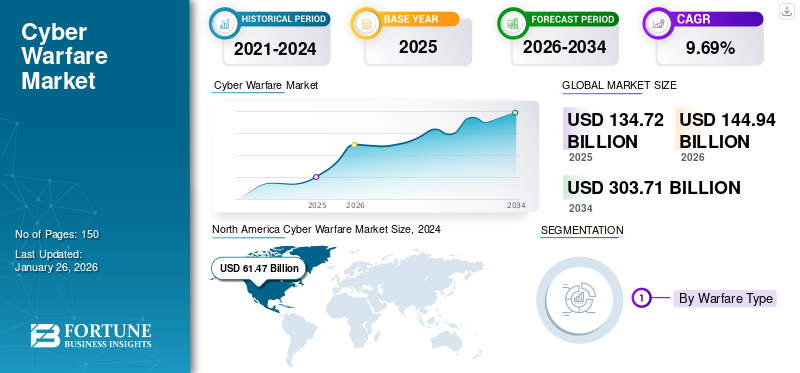
The Rise of Cyber Warfare
In recent years, cyber warfare has evolved from a theoretical concept to a practical tool of statecraft. Unlike traditional military operations, cyber warfare allows for remote engagement, minimizing risks to personnel while maximizing disruption potential.
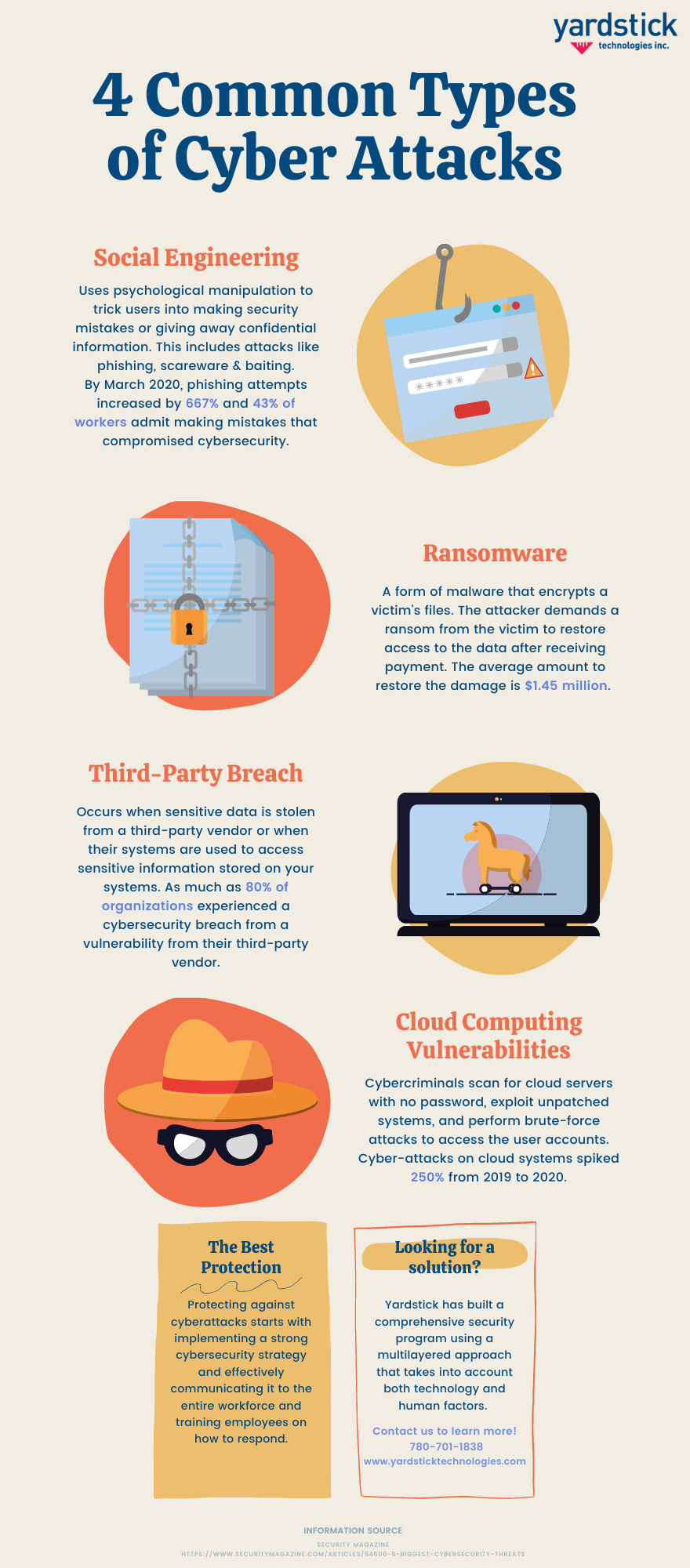
Cyber operations can be categorized into several types:
- Intelligence Gathering: Using cyber tools to collect data from adversaries' networks.
- Disruption: Temporarily or permanently disabling systems or networks.
- Deception: Feeding false information to confuse or mislead adversaries.
- Psychological Operations (Psy Ops): Influencing public perception and morale through digital means.

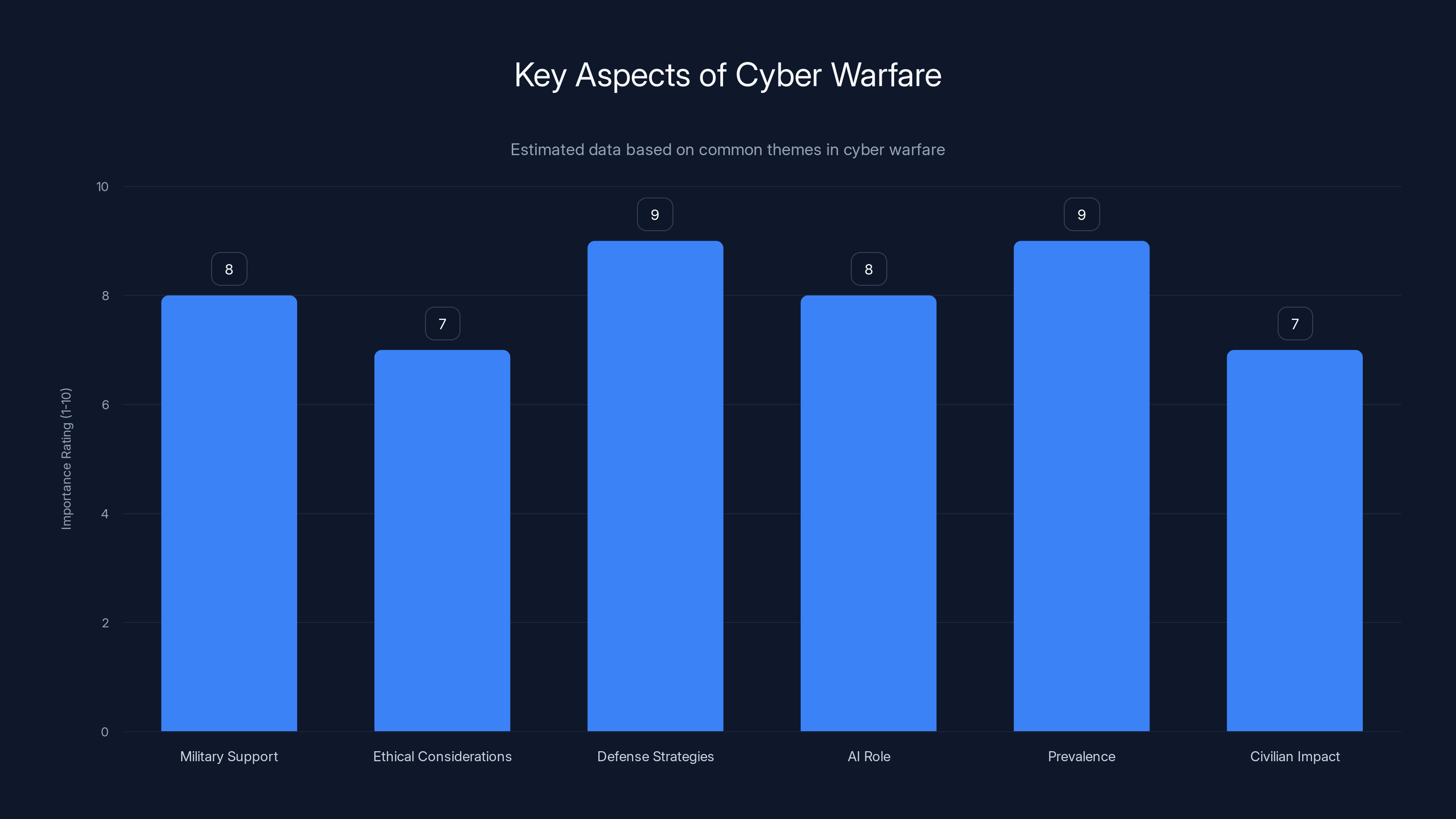
Cyber warfare's prevalence and defense strategies are rated highly in importance, reflecting their critical role in modern conflicts. (Estimated data)
Case Study: Cyber Operations in the Iran Conflict
During the recent conflict with Iran, cyber operations played a pivotal role in supporting traditional military objectives. U.S. and Israeli forces reportedly utilized cyber capabilities to disrupt Iranian communications and sensor networks, facilitating kinetic strikes with greater precision.
Intelligence Gathering
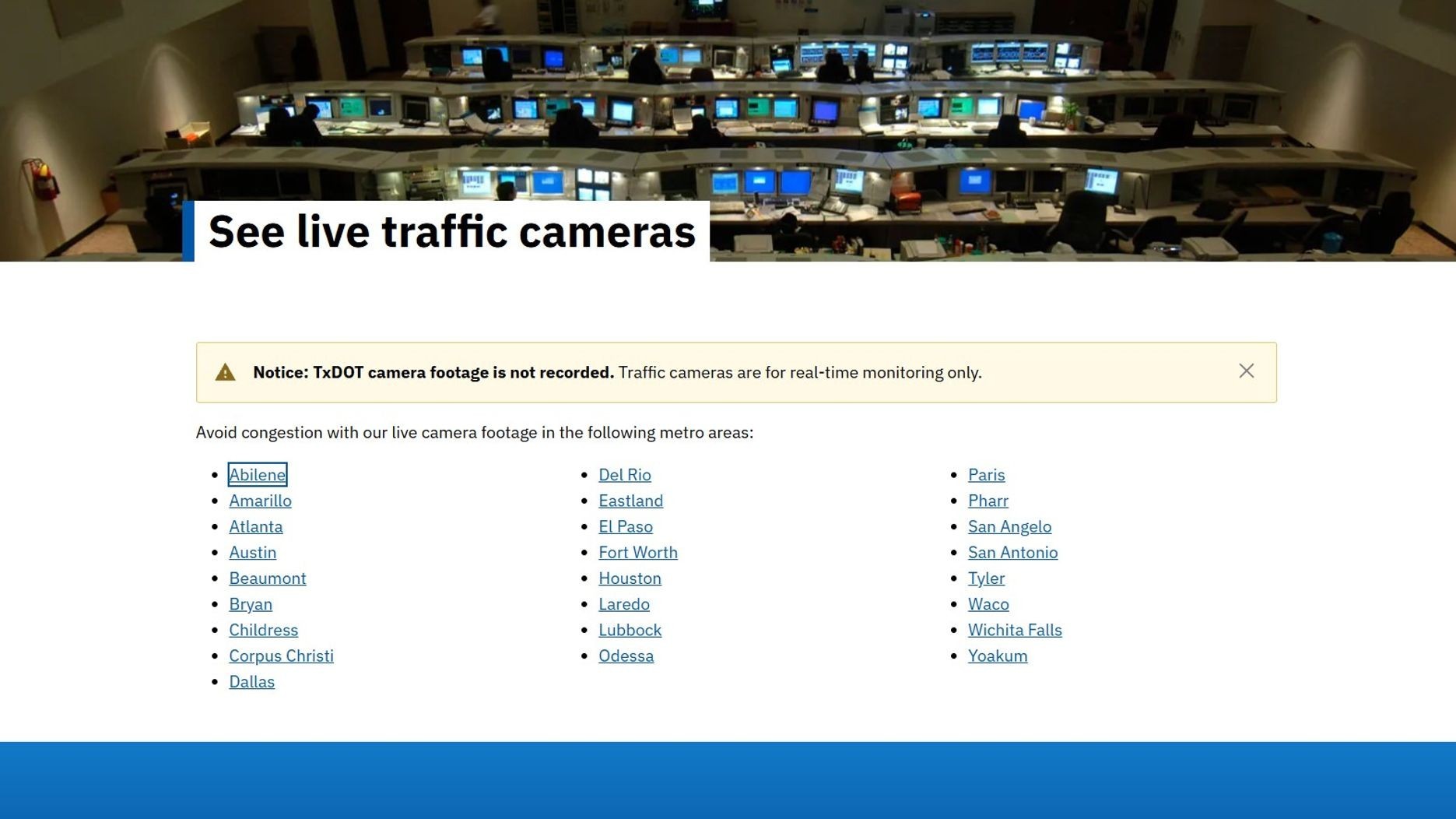
One of the primary uses of cyber operations in warfare is intelligence gathering. By hacking into Iranian infrastructure, such as traffic cameras and telecommunications networks, military forces were able to gather real-time data on troop movements and strategic positions.
Example:
Imagine a scenario where hacked traffic cameras provide continuous updates on military convoys' movements, allowing for precise timing of airstrikes. This intelligence would be invaluable in minimizing civilian casualties and ensuring mission success.
Psychological Operations
Cyber operations also play a significant role in psychological warfare. By hijacking Iranian television broadcasts, military forces were able to spread messages aimed at undermining public confidence in the Iranian government.
Real-World Use Case:
During the conflict, hacked TV stations broadcasted messages urging Iranian citizens to question their government's ability to protect them. This sowed doubt and fear, weakening morale and potentially reducing resistance to foreign intervention.
Disruption of Communications
Disrupting an adversary's communication networks can cripple their ability to coordinate effectively. In the case of Iran, cyber attacks targeted military communications, sensor arrays, and command systems, creating chaos and confusion.
Implementation Guide:
- Identify Key Nodes: Target critical communication nodes within the enemy's network.
- Develop Specialized Malware: Craft malware designed to disrupt or disable these nodes.
- Deploy Malware Simultaneously: Use coordinated attacks to maximize impact and minimize response time.
- Monitor Results: Continuously assess the disruption's effectiveness and adjust tactics as needed.

Best Practices in Cyber Warfare
While cyber operations offer significant advantages, they also come with risks and challenges. Here are some best practices to ensure successful cyber operations:
- Robust Cyber Hygiene: Maintain secure coding practices and regular security audits to protect your own systems.
- Coordinated Efforts: Synchronize cyber operations with traditional military actions for maximum impact.
- Legal and Ethical Considerations: Ensure operations comply with international law and ethical standards.
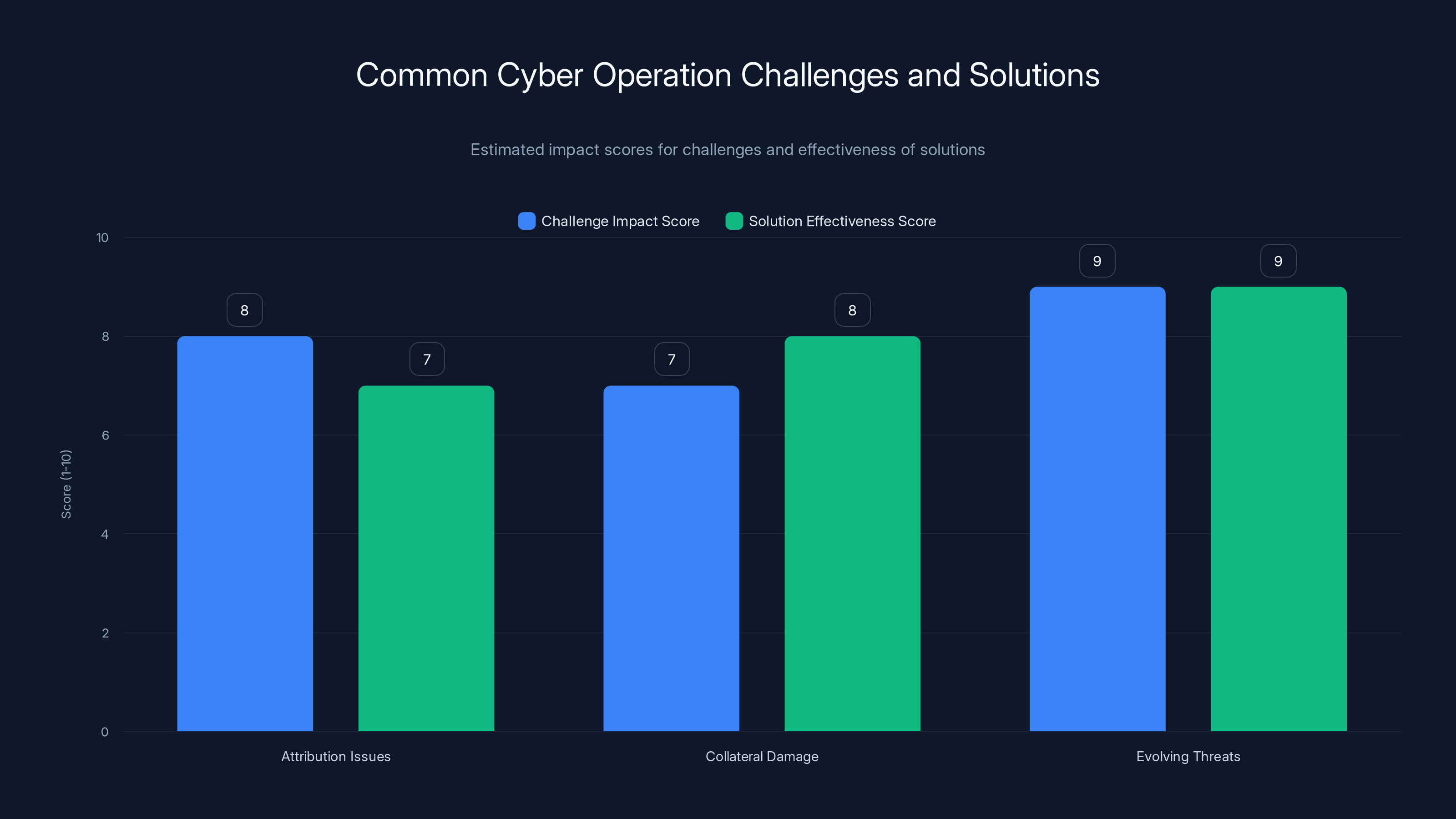
Attribution issues, collateral damage, and evolving threats are major challenges in cyber operations. Solutions like advanced threat intelligence and cross-disciplinary teams are highly effective. (Estimated data)
Common Pitfalls and Solutions
Despite their potential, cyber operations are not without pitfalls. Common challenges include:
- Attribution Issues: Determining the source of a cyber attack can be difficult, complicating political and military responses.
- Collateral Damage: Cyber operations can inadvertently affect civilian infrastructure, leading to unintended consequences.
- Rapidly Evolving Threats: The cyber landscape evolves quickly, requiring constant adaptation and innovation.
Solutions:
- Advanced Threat Intelligence: Invest in AI-powered tools to predict and identify potential cyber threats.
- Cross-Disciplinary Teams: Employ experts from various fields, including cybersecurity, military strategy, and international law, to develop comprehensive strategies.
- Continuous Training: Regularly update and train personnel on the latest cyber tactics and technologies.
Future Trends in Cyber Warfare
As technology continues to advance, so too will the capabilities of cyber operations. Future trends include:
- Increased Automation: AI and machine learning will automate many aspects of cyber warfare, increasing speed and precision.
- Integration with Io T: The proliferation of Internet of Things (Io T) devices will provide new targets and opportunities for cyber operations.
- Focus on Cyber Defense: As offensive capabilities grow, so too will the need for robust cyber defenses to protect against retaliatory attacks.

Recommendations for Policymakers
Policymakers must adapt to the realities of cyber warfare by:
- Investing in Cyber Infrastructure: Ensure that national cyber infrastructure is resilient and capable of withstanding attacks.
- International Collaboration: Work with allies to develop shared standards and protocols for cyber operations.
- Public Awareness Campaigns: Educate the public on cybersecurity best practices to reduce vulnerabilities.
Conclusion
The integration of cyber operations into modern warfare has fundamentally changed the landscape of conflict. By leveraging digital tools, states can achieve strategic objectives with precision and minimal risk to human life. However, this new paradigm also presents challenges that require careful consideration and adaptation.
Bottom Line: As cyber operations continue to evolve, nations must remain vigilant and proactive in their defense strategies to maintain security and stability.
FAQ
What is cyber warfare?
Cyber warfare involves the use of digital attacks to disrupt, damage, or destroy adversaries' networks and systems. These operations can support military objectives or serve as standalone strategies.
How do cyber operations support military objectives?
Cyber operations provide real-time intelligence, disrupt enemy communications, and conduct psychological operations to weaken adversaries' resolve and capabilities.
What are the ethical considerations of cyber warfare?
Ethical considerations include ensuring compliance with international law, minimizing collateral damage, and maintaining the integrity of civilian infrastructure.
How can nations defend against cyber attacks?
Nations can defend against cyber attacks by investing in cybersecurity infrastructure, developing rapid response teams, and engaging in international cooperation.
What role does AI play in cyber warfare?
AI enhances cyber operations by automating threat detection, enabling rapid response, and predicting potential future attacks.
Why is cyber warfare becoming more prevalent?
Cyber warfare is becoming more prevalent due to its cost-effectiveness, ability to reach targets globally, and reduced risk compared to traditional military operations.
How does cyber warfare affect civilians?
Cyber warfare can impact civilians by disrupting essential services, spreading misinformation, and potentially causing physical harm through attacks on critical infrastructure.
Key Takeaways
- Cyber operations are integral to modern warfare, offering intelligence and psychological advantages.
- Hacked infrastructure provides real-time data, aiding precision strikes and reducing collateral damage.
- Coordinated cyber attacks disrupt enemy communications, impacting military effectiveness.
- Future conflicts will see increased reliance on cyber operations, necessitating robust defenses.
- AI and machine learning will enhance cyber capabilities, automating threat detection and response.
Related Articles
- Navigating the Complexities of Modern Security: Fig Security's Revolutionary Approach [2025]
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
- The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]
- Australia's Bold Move on AI Services: Age Verification and App Store Compliance [2025]
- How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
- When AI Lies: Navigating the Complexities of Alignment Faking in Autonomous Systems [2025]
![Digital Warfare: The Role of Cyber Operations in Modern Conflicts [2025]](https://tryrunable.com/blog/digital-warfare-the-role-of-cyber-operations-in-modern-confl/image-1-1772561113068.jpg)



