Understanding Rowhammer Attacks on Nvidia GPUs and Mitigating Their Risks [2025]
Last month, a security researcher exposed a shocking vulnerability: Rowhammer attacks on Nvidia GPUs. While Rowhammer is a known threat to CPUs, its presence on GPUs marks a new era of cybersecurity risks. Imagine your state-of-the-art GPU, designed for high-performance computing, suddenly becoming a liability. Let's dive into how these attacks work, their implications, and how to defend against them.
TL; DR
- Rowhammer attacks can exploit Nvidia GPUs, compromising entire systems.
- Shared environments like cloud services are particularly vulnerable.
- Mitigation strategies include hardware upgrades and software patches.
- Future trends suggest increased focus on GPU security.
- Immediate action involves assessing current system vulnerabilities.

What is Rowhammer?
At its core, Rowhammer is an attack that exploits the physical properties of memory cells. By repeatedly accessing (or 'hammering') a row of memory cells, attackers can induce bit flips in adjacent rows. This phenomenon can lead to data corruption or unauthorized access to sensitive information.
Why GPUs?
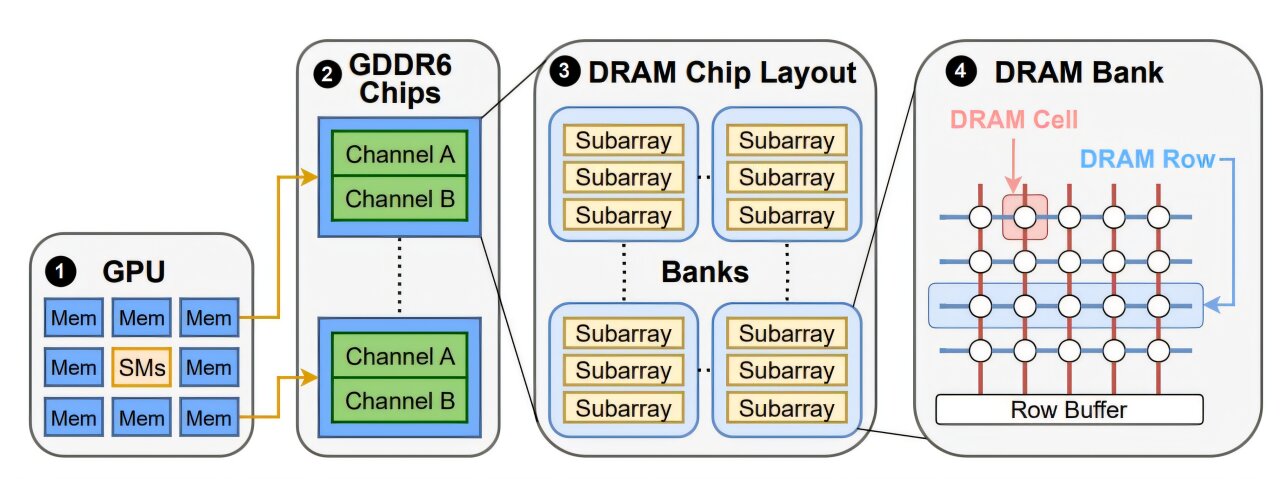
GPUs, or Graphics Processing Units, are integral to modern computing, powering everything from gaming to machine learning. Their parallel processing capabilities make them indispensable. However, this very architecture also makes them susceptible to Rowhammer attacks.
The Mechanics of Rowhammer on Nvidia GPUs
Unlike traditional CPUs, GPUs handle massive data throughput, often in shared environments like cloud services. This increases the risk of Rowhammer attacks, as multiple users can potentially exploit the same hardware.
Attack Vectors
Rowhammer attacks on GPUs typically involve:
- High-frequency memory access: Exploiting the rapid data processing capabilities of GPUs.
- Shared memory spaces: Taking advantage of shared GPU resources in cloud environments.
- Lack of isolation: GPUs often lack the same level of isolation as CPUs, making them more vulnerable.
Real-World Impact
Consider a cloud service hosting numerous virtual machines on shared GPUs. An attacker could use a Rowhammer attack to access data from another virtual machine, leading to potential data breaches.
Case Study
In one instance, a research team demonstrated how a Rowhammer attack could manipulate GPU memory to alter machine learning models, leading to incorrect outputs and potential data theft.
Mitigation Strategies
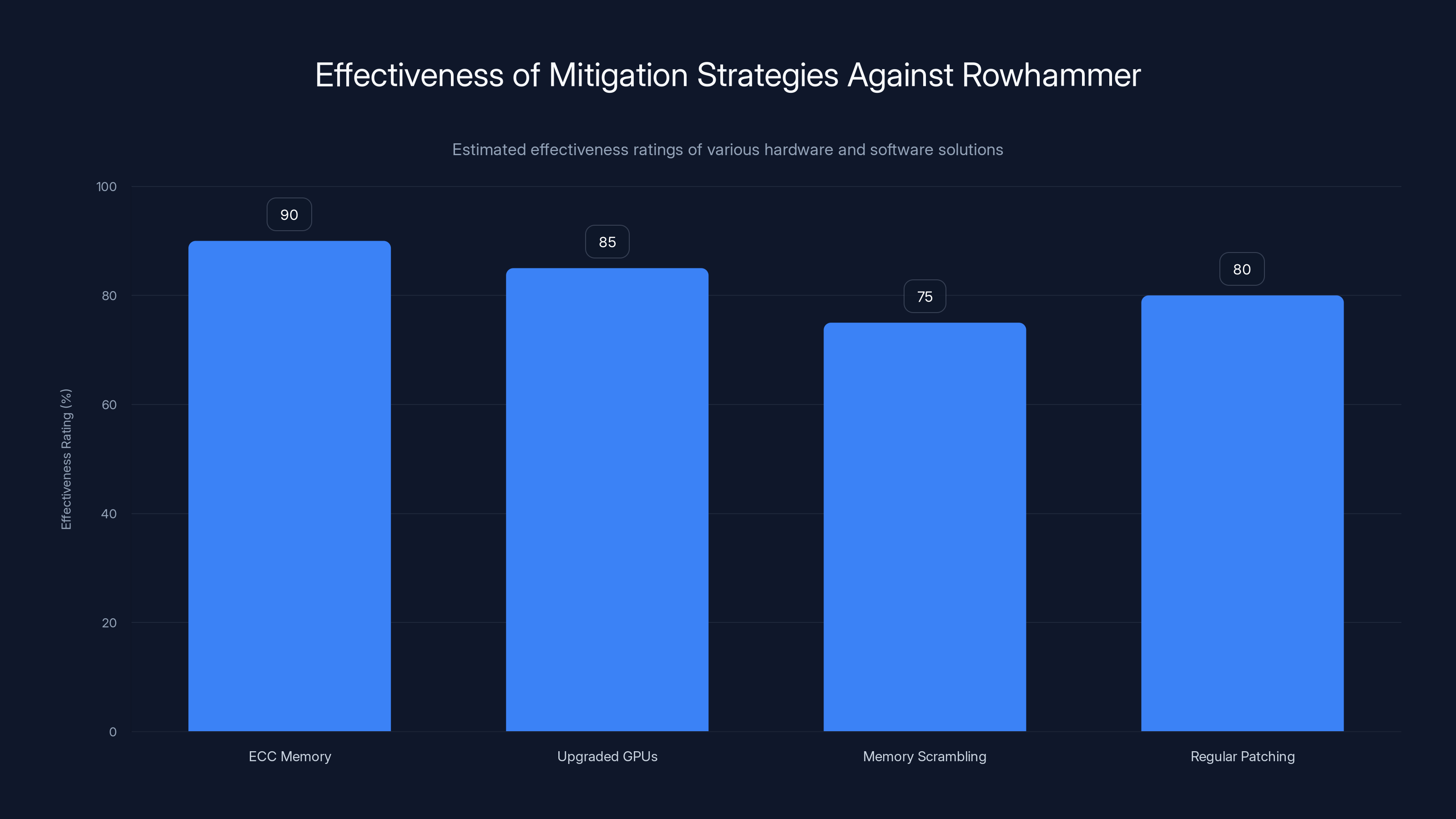
Hardware Solutions
- ECC Memory: Error-Correcting Code (ECC) memory can detect and correct bit flips, providing a robust defense against Rowhammer attacks.
- Upgraded GPUs: Next-gen GPUs with built-in defenses against Rowhammer should be prioritized.
Software Solutions
- Memory Scrambling: Implementing techniques that randomize memory access patterns can reduce the effectiveness of Rowhammer attacks.
- Regular Patching: Keeping GPU drivers and firmware updated to address known vulnerabilities.

Best Practices for Shared Environments
- Resource Isolation: Ensure proper isolation between different users in a shared environment to prevent unauthorized access.
- Monitoring and Alerts: Implement real-time monitoring to detect unusual memory access patterns indicative of Rowhammer attacks.
- Access Controls: Restrict access to GPU resources based on necessity and trust level.
Future Trends in GPU Security
The landscape of GPU security is evolving rapidly. As GPUs become more integral to AI and machine learning, the need for robust security measures will only increase.
Predictions
- Increased Research: Expect more academic and industry research focused on GPU vulnerabilities.
- Enhanced Security Features: Future GPU models will likely include advanced security features to combat Rowhammer and similar attacks.
Recommendations for Organizations
- Conduct Security Audits: Regularly assess the security posture of your GPU infrastructure.
- Invest in Training: Educate your IT staff on the risks and mitigation strategies associated with GPU vulnerabilities.
- Collaborate with Vendors: Work closely with GPU vendors like Nvidia to stay informed on the latest security updates and best practices.
Conclusion
Rowhammer attacks on Nvidia GPUs highlight a critical need for vigilance in cybersecurity practices. By understanding the mechanics of these attacks and implementing robust mitigation strategies, organizations can safeguard their systems against potential breaches.
Use Case: Enhance your cybersecurity measures with Runable's AI-powered automation tools, streamlining the process of monitoring and patching vulnerabilities.
Try Runable For Free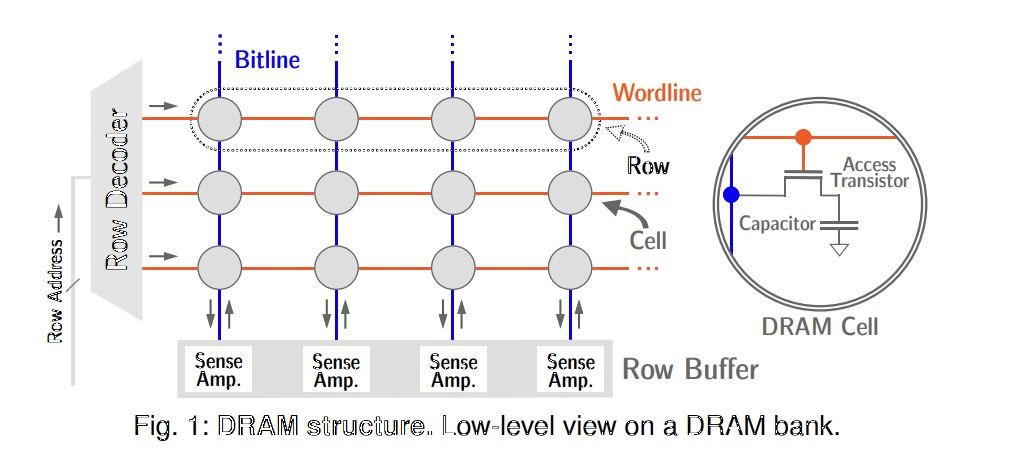
FAQ
What is a Rowhammer attack?
A Rowhammer attack exploits the physical properties of memory cells, causing bit flips by repeatedly accessing adjacent rows of memory.
How do Rowhammer attacks affect GPUs?
These attacks can lead to unauthorized data access and system compromises, particularly in shared environments where GPUs are used for parallel processing.
What are the benefits of using ECC memory?
ECC memory can detect and correct bit errors, significantly reducing the risk of successful Rowhammer attacks on GPU systems.
How can organizations protect against Rowhammer attacks?
Implementing hardware solutions like ECC memory, regular software patching, and ensuring proper resource isolation in shared environments are effective strategies.
What future trends are expected in GPU security?
Future GPUs will likely incorporate advanced security features, and there will be increased research into vulnerabilities like Rowhammer to develop more robust defenses.
How does Runable assist in mitigating cybersecurity risks?
Runable offers AI-powered tools that automate the process of monitoring and patching vulnerabilities, enhancing overall cybersecurity measures.
The Best GPU Security Practices at a Glance
| Practice | Description | Benefit |
|---|---|---|
| ECC Memory | Use Error-Correcting Code memory | Reduces bit flip risk |
| Regular Patching | Update drivers and firmware | Addresses known vulnerabilities |
| Resource Isolation | Separate user access in shared environments | Prevents unauthorized access |
Quick Navigation:
- Runable for AI-powered automation
- Understanding Rowhammer
- Real-World Impact
- Future Trends in GPU Security
Key Takeaways
- Rowhammer attacks pose a significant threat to Nvidia GPUs, especially in shared environments.
- Implementing ECC memory and regular software patching are effective mitigation strategies.
- Organizations should prioritize security audits and staff training to enhance their cybersecurity posture.
- Future trends indicate a growing focus on developing advanced security features in GPUs.
- Runable's automation tools can streamline vulnerability monitoring and mitigation processes.
Related Articles
- Boosting Engagement on Facebook: The Power of Replying to Comments [2025]
- How IT Teams Can Focus on the Big Problems by Overcoming Minor Issues [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- How Amazon’s Smart Thermostat Can Slash Your Energy Bills [2025]
![Understanding Rowhammer Attacks on Nvidia GPUs and Mitigating Their Risks [2025]](https://tryrunable.com/blog/understanding-rowhammer-attacks-on-nvidia-gpus-and-mitigatin/image-1-1775678772721.jpg)



