Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
The recent breach of sensitive Los Angeles Police Department (LAPD) documents has once again put the spotlight on the critical importance of cybersecurity. This incident, involving the theft and online leakage of internal documents, personnel files, and sensitive investigation data, highlights vulnerabilities that can be exploited by cybercriminals. Let's delve into the details of this breach, explore its implications, and learn how to bolster defenses against such attacks.
TL; DR
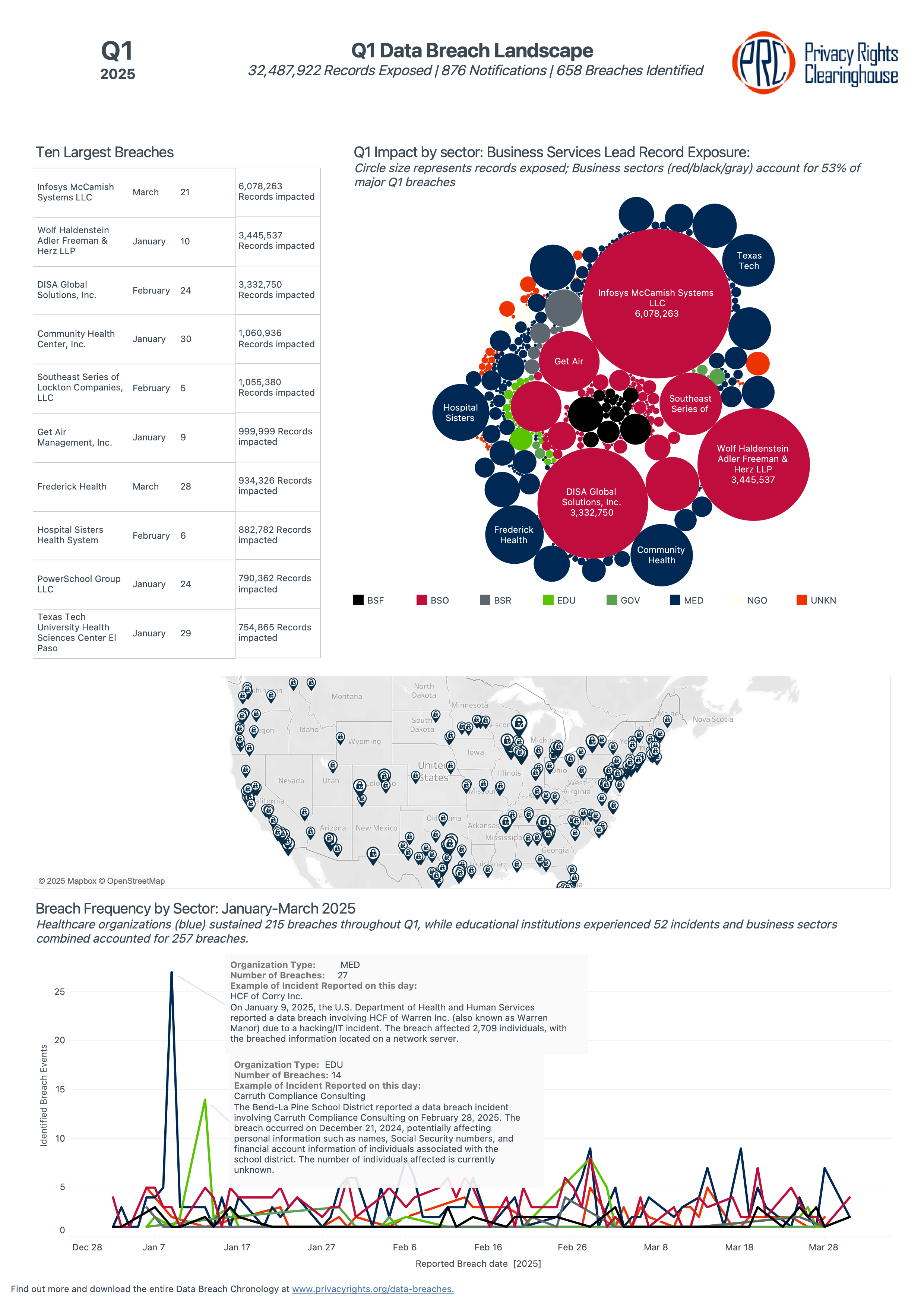
- Significant Breach: Over 20,000 LAPD documents were compromised, exposing sensitive data including personnel files and internal investigations, as reported by TechCrunch.
- Data Sensitivity: The leaked documents included unredacted criminal complaints and personal information, posing severe privacy risks, according to the Los Angeles Times.
- Cybercriminals Involved: The attack was attributed to the extortion gang World Leaks, known for pressuring victims to pay ransoms, as detailed by Security Magazine.
- Immediate Response: LAPD is investigating the breach and working with cybersecurity experts to assess the damage and prevent future attacks.
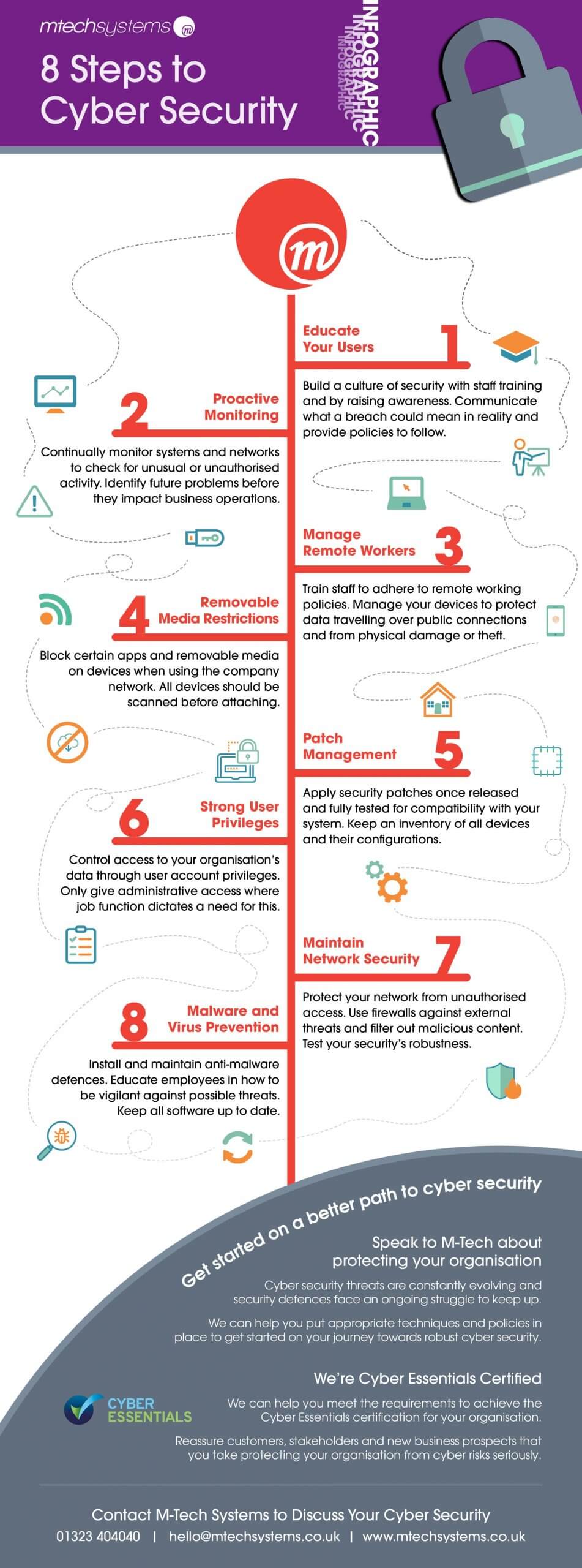
- Preventive Measures: Organizations must strengthen cybersecurity protocols, enforce strict access controls, and educate employees on best practices.
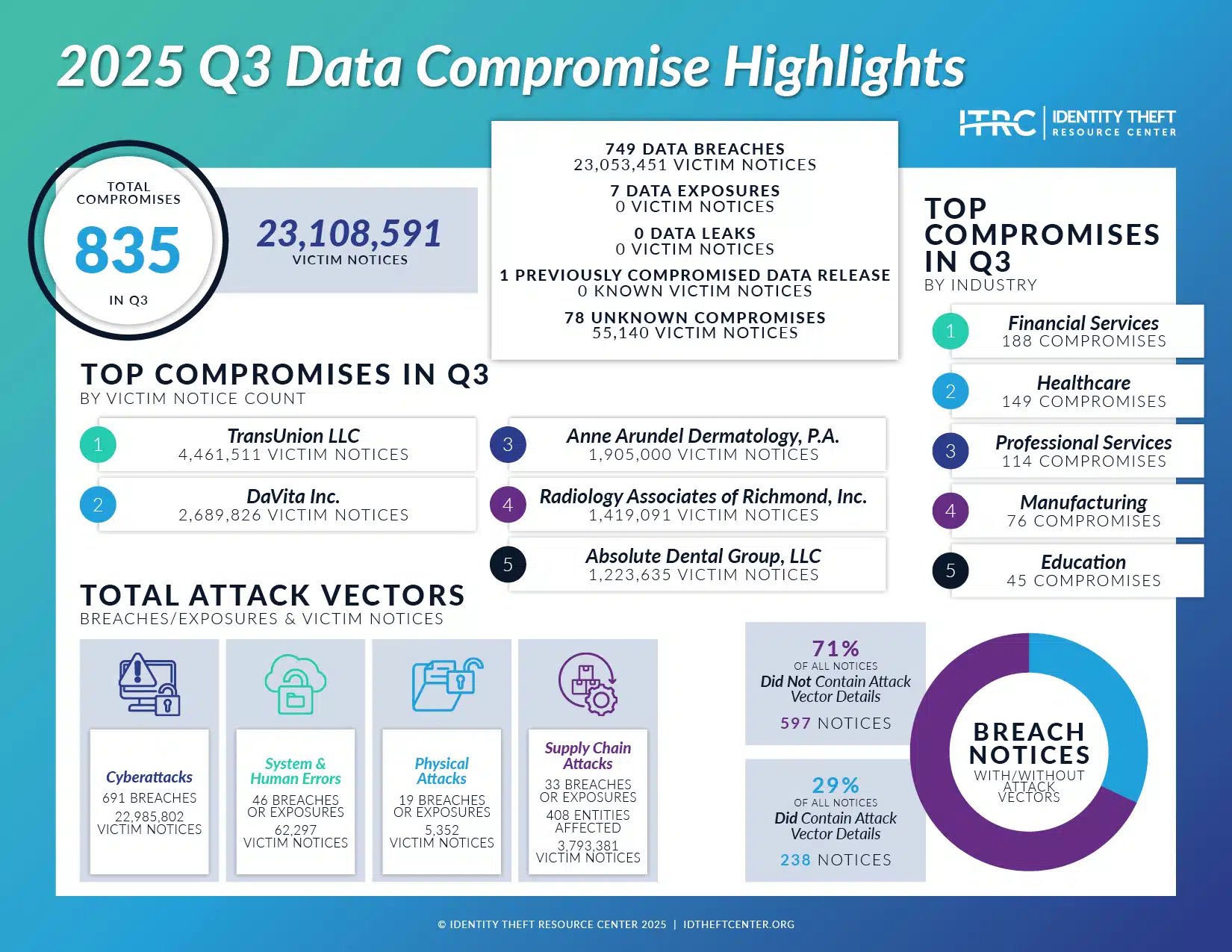
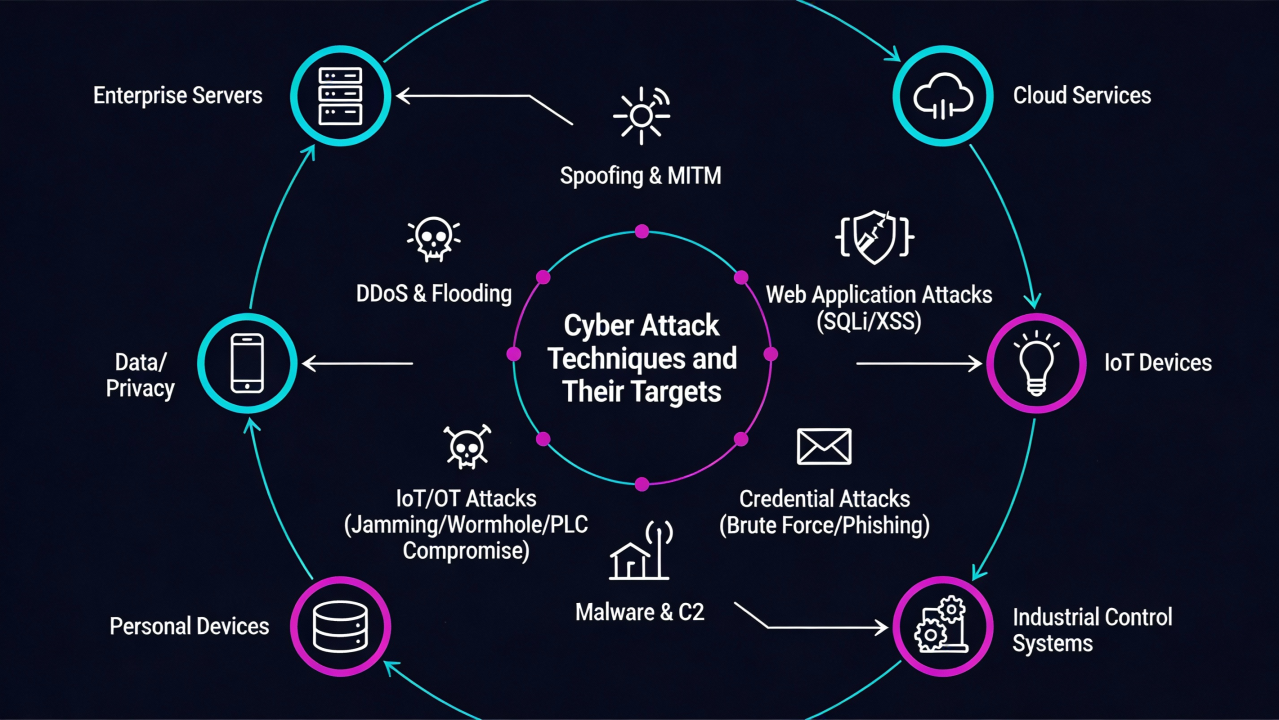
This chart estimates the effectiveness of various cyberattack techniques and defense mechanisms. Regular software updates and comprehensive monitoring are rated as highly effective defense strategies. Estimated data.
The Scale and Impact of the Breach
What Happened?
In a brazen act of cybercrime, hackers successfully infiltrated LAPD's systems, accessing and leaking a trove of confidential documents. This data breach exposed thousands of sensitive files, including officer personnel records, internal affairs investigations, and criminal complaints. Such exposure not only compromises the safety and privacy of individuals involved but also undermines public trust in law enforcement agencies, as noted by TechCrunch.
The Actors Behind the Breach
The extortion gang known as World Leaks is believed to be responsible for this breach. Known for their ruthless tactics, World Leaks specializes in stealing sensitive data and demanding ransoms from their victims. By publicizing these breaches on their website, they aim to coerce organizations into paying substantial sums to prevent further leaks, as reported by Security Magazine.
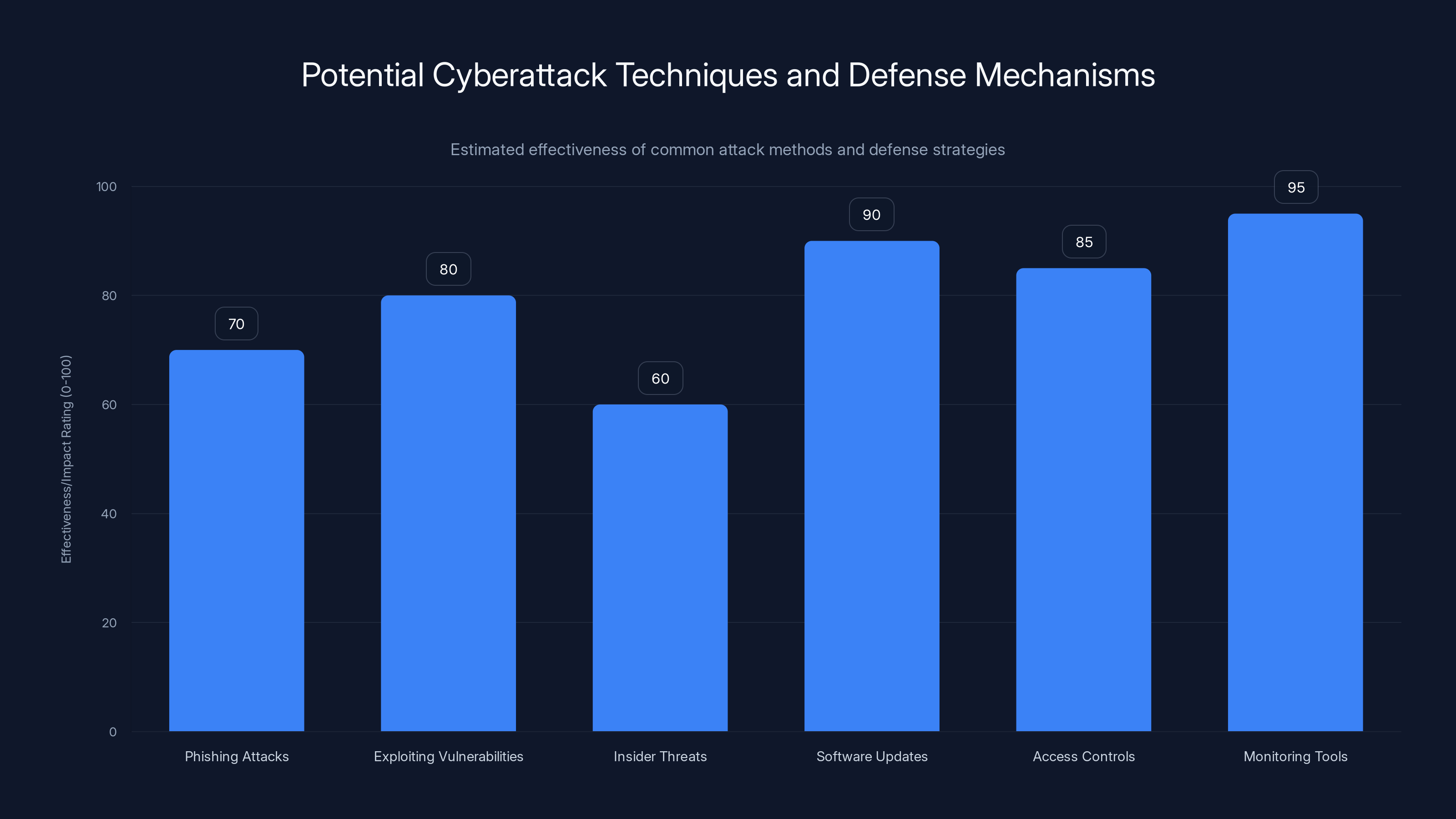
Implementing strong cybersecurity practices can significantly reduce security breaches, with data encryption and two-factor authentication being the most effective. (Estimated data)
Analyzing the Technical Aspects
How Did the Breach Occur?
The precise methods used by World Leaks to infiltrate LAPD's systems remain unclear, but several common techniques could have been employed:
- Phishing Attacks: By tricking users into revealing login credentials or installing malware, as highlighted by Microsoft.
- Exploiting Vulnerabilities: Taking advantage of outdated software or unpatched security flaws.
- Insider Threats: Leveraging the access of disgruntled or negligent employees.
Defense Mechanisms: What Could Have Been Done?
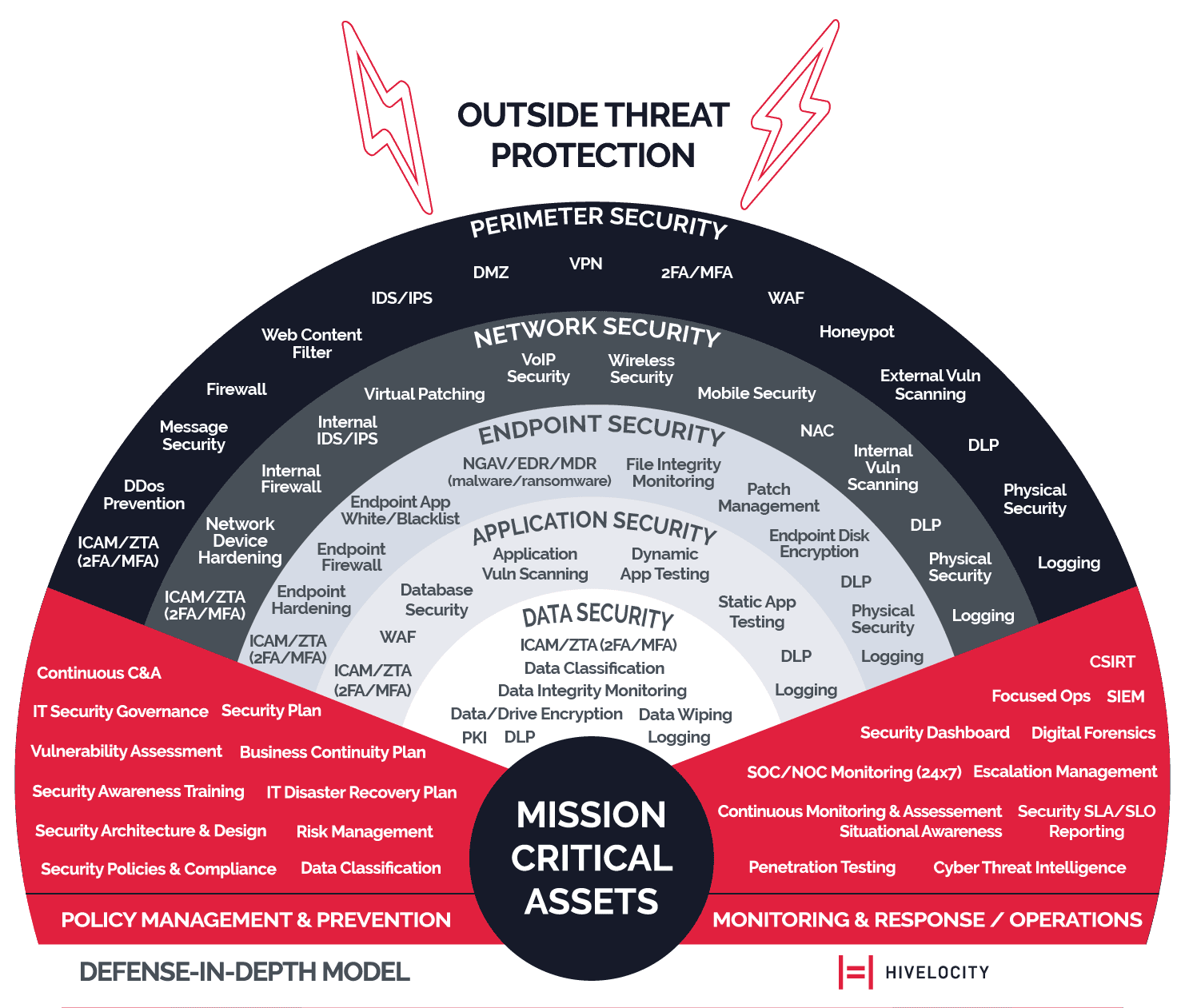
To safeguard against such breaches, organizations must adopt a multi-layered cybersecurity strategy:
- Regular Software Updates: Ensuring all systems are up-to-date with the latest security patches.
- Robust Access Controls: Limiting access to sensitive data based on the principle of least privilege.
- Comprehensive Monitoring: Implementing advanced monitoring tools to detect and respond to suspicious activities.
Best Practices for Cybersecurity
Implementing Strong Password Policies
Passwords remain a critical line of defense. Organizations should enforce policies that require:
- Complex Passwords: A mix of uppercase, lowercase, numbers, and symbols.
- Regular Changes: Mandatory password updates every 60-90 days.
- Two-Factor Authentication (2FA): Adding an extra layer of security, as recommended by Cybersecurity Insiders.
Educating Employees
Human error is often the weakest link in cybersecurity. Regular training sessions can:
- Raise Awareness: Educate employees on recognizing phishing attempts and other threats.
- Promote Best Practices: Encourage safe online behavior and the importance of data privacy.
Data Encryption
Encrypting sensitive data both at rest and in transit protects it from unauthorized access. Organizations should use strong encryption algorithms and manage encryption keys securely, as advised by HIPAA Journal.

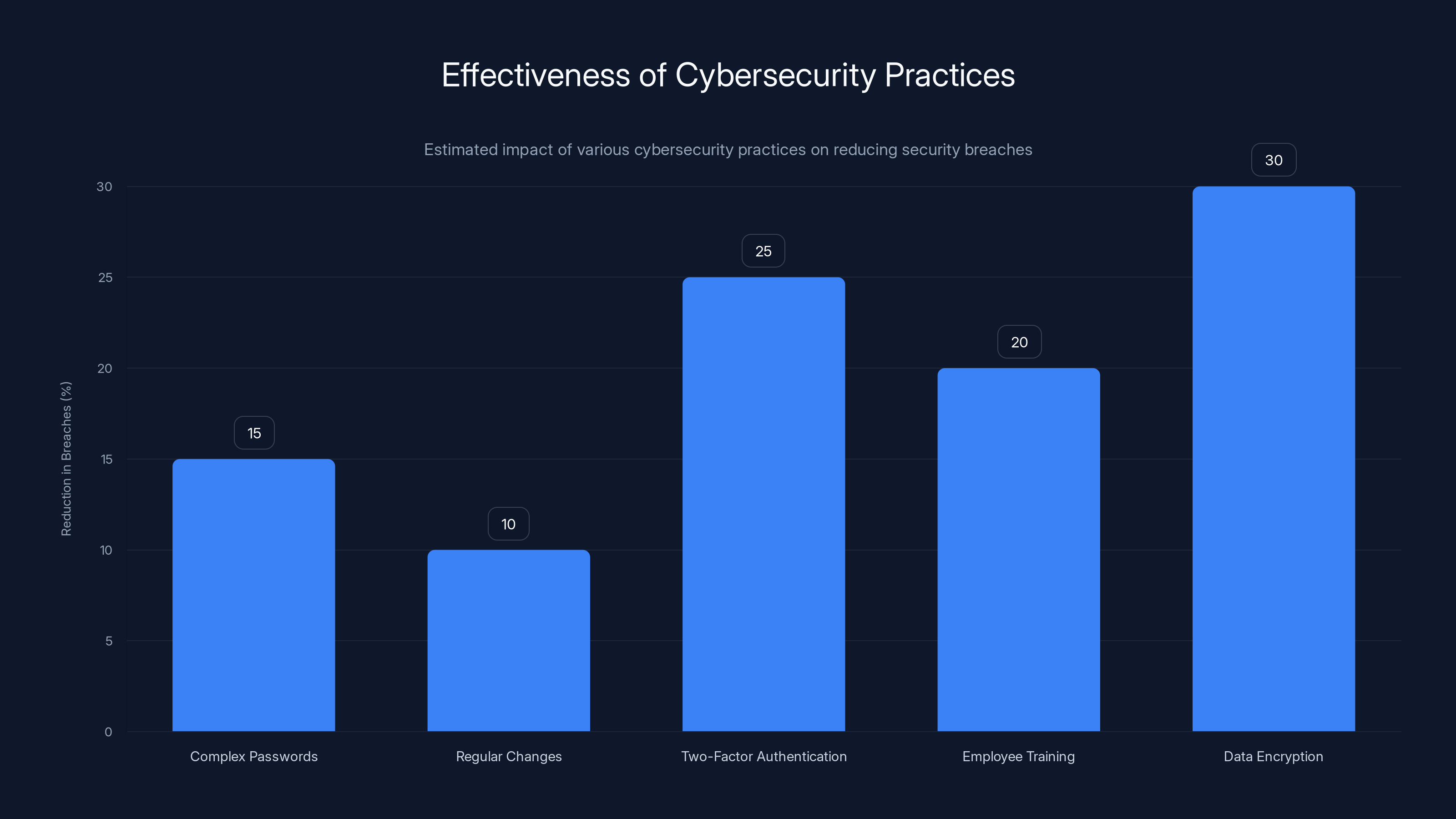
Investing in cybersecurity training and engaging with experts are rated highly effective strategies for organizations. Estimated data.
Common Pitfalls and Solutions
Overlooking Insider Threats
While external threats get significant attention, insider threats can be equally damaging. Solutions include:
- User Activity Monitoring: Tracking and analyzing user behavior for anomalies.
- Access Reviews: Regular audits to ensure only necessary personnel have access to sensitive data.
Neglecting Backup Protocols
Data backups are crucial for recovery post-breach. Best practices include:
- Regular Backups: Automated backups of critical data at regular intervals.
- Offsite Storage: Storing backups in secure, offsite locations.
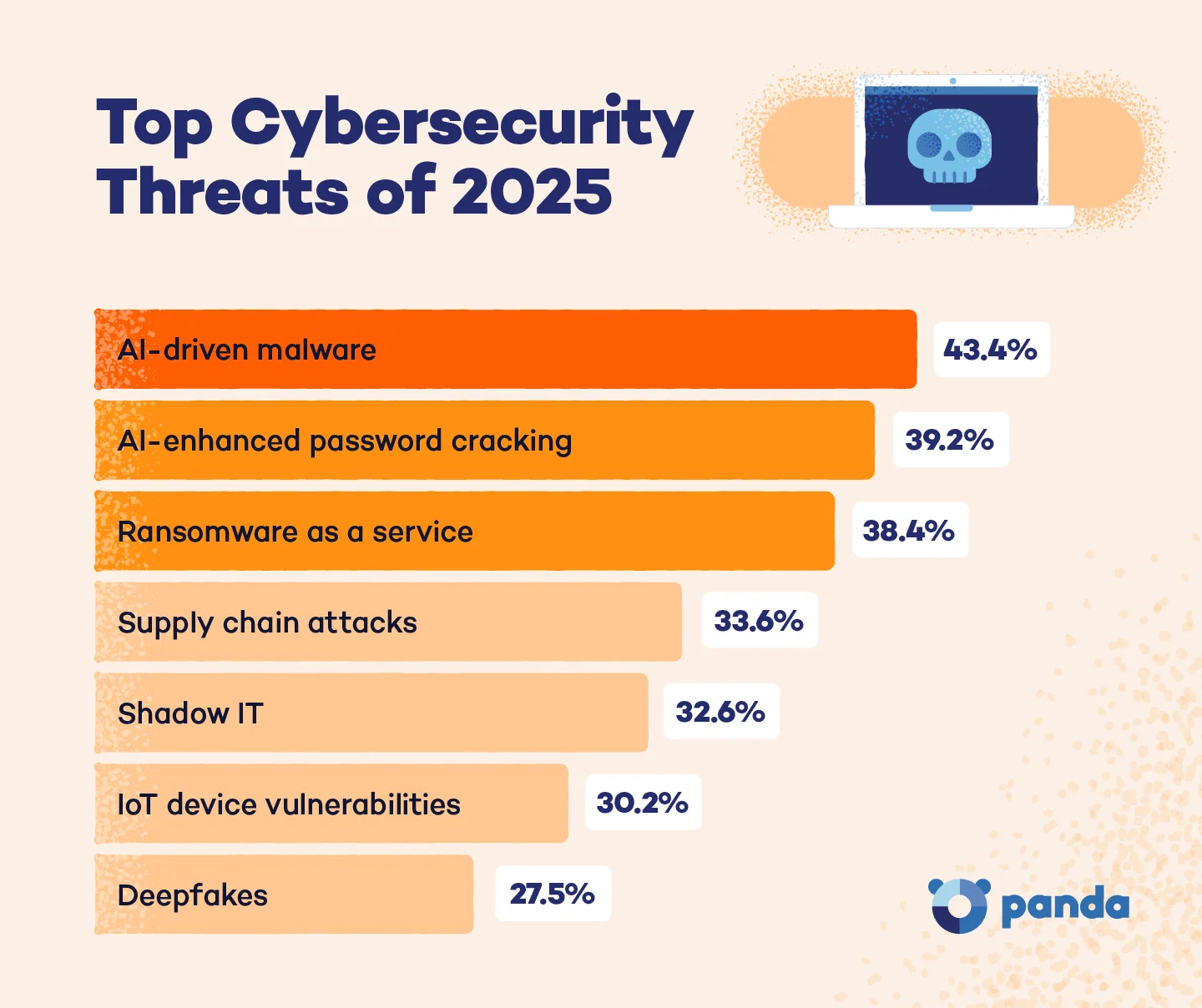
Future Trends in Cybersecurity
AI and Machine Learning
AI-driven cybersecurity tools are becoming increasingly sophisticated, capable of predicting and mitigating threats in real-time. These technologies can:
- Analyze Patterns: Detect anomalies and predict potential breaches.
- Automate Responses: Implement instant defense mechanisms against detected threats, as explored by Vocal Media.
Zero Trust Architecture
Adopting a Zero Trust approach means assuming that threats could be internal or external. Key principles include:
- Never Trust, Always Verify: Continuous authentication and authorization for all users and devices.
- Microsegmentation: Dividing networks into smaller segments for granular access control, as discussed by Mayer Brown.
Recommendations for Organizations
- Conduct Regular Security Audits: Identify and address vulnerabilities before they can be exploited.
- Invest in Cybersecurity Training: A well-informed workforce is the first line of defense against cyber threats.
- Adopt Multi-Factor Authentication: Protect sensitive accounts with additional security layers.
- Develop Incident Response Plans: Having a clear plan in place can mitigate damage during a breach.
- Engage with Cybersecurity Experts: Collaborate with specialists to strengthen defenses and stay ahead of emerging threats, as suggested by Tech Times.
Conclusion
The LAPD data breach serves as a stark reminder of the evolving cyber threat landscape. As attackers become more sophisticated, organizations must respond by enhancing their cybersecurity posture. By implementing best practices, educating employees, and embracing new technologies, we can better protect sensitive data and maintain public trust, as emphasized by Governor Ferguson's recent initiatives.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals gain access to confidential information, often with malicious intent.
How can organizations prevent data breaches?
By implementing strong cybersecurity measures such as regular software updates, robust access controls, and employee training.
What are the consequences of a data breach?
Breaches can lead to financial losses, reputational damage, legal penalties, and compromised personal data.
Why is employee training important in cybersecurity?
Educated employees are less likely to fall victim to phishing attacks and other social engineering tactics.
How does encryption help in data security?
Encryption protects data by making it unreadable without the proper decryption key, safeguarding it from unauthorized access.
What role does AI play in cybersecurity?
AI enhances cybersecurity by analyzing vast amounts of data to detect threats, predict breaches, and automate responses.

Key Takeaways
- Over 20,000 LAPD documents were compromised in a data breach.
- The breach exposed sensitive information, including personnel files.
- World Leaks, an extortion gang, is linked to the attack.
- Organizations should adopt multi-layered cybersecurity strategies.
- AI and Zero Trust architectures are emerging trends in cybersecurity.
- Regular employee training is crucial for preventing data breaches.
- Data encryption and multi-factor authentication enhance security.
- Incident response plans are vital for mitigating breach impacts.
Related Articles
- Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]
- Navigating Encryption Challenges: VeraCrypt's Developer Faces Microsoft Account Lock [2025]
- US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
- Stolen Session Cookies: The Hidden Threat to Account Security [2025]
- Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
- 5 Key Insights from Samsara's Reacceleration to $1.9 Billion in ARR [2025]
![Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]](https://tryrunable.com/blog/understanding-the-lapd-data-breach-lessons-in-cybersecurity-/image-1-1775664400084.jpg)



