Understanding the Air Snitch Attack: Wi-Fi Encryption Risks and Mitigation [2025]
Wi-Fi has become an indispensable part of modern life. With more than 48 billion Wi-Fi-enabled devices shipped since its debut in the late 1990s, it's hard to imagine a world without wireless connectivity. Yet, the convenience of Wi-Fi comes with its own set of vulnerabilities. The latest threat, known as the Air Snitch attack, has exposed significant weaknesses in Wi-Fi encryption, putting both personal and enterprise networks at risk.
TL; DR
- Air Snitch: A new attack that exploits vulnerabilities in Wi-Fi encryption.
- Impact: Affects homes, offices, and enterprises, compromising data security.
- Mitigation: Regular updates, strong passwords, and network segmentation are key.
- Future Trends: Enhanced security protocols and AI-driven threat detection.
- Bottom Line: Proactive security measures are crucial to protect against Air Snitch.
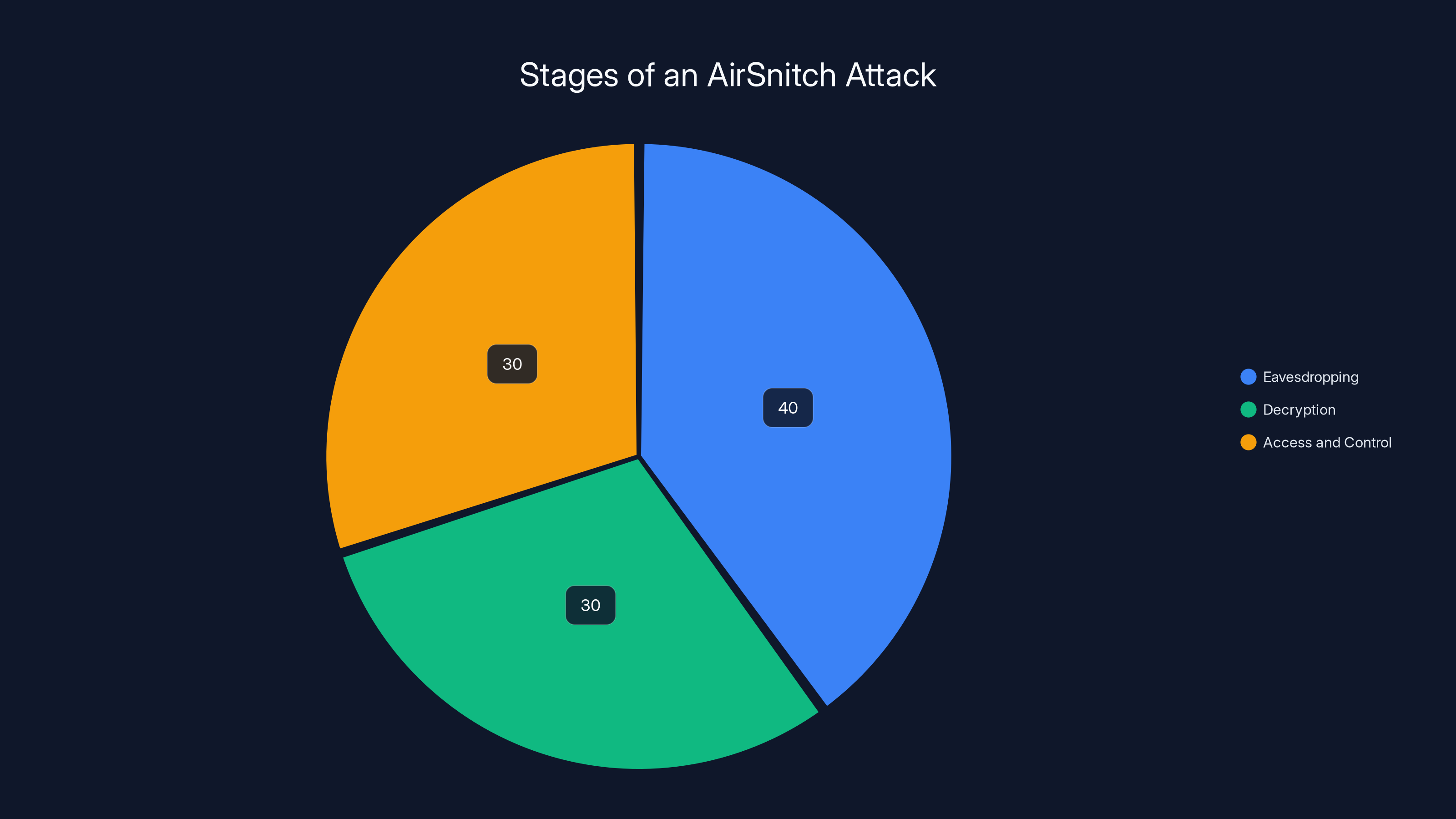
Estimated data shows that eavesdropping takes the most time in an AirSnitch attack, followed by decryption and access/control.
The Rise of Air Snitch: What Is It?
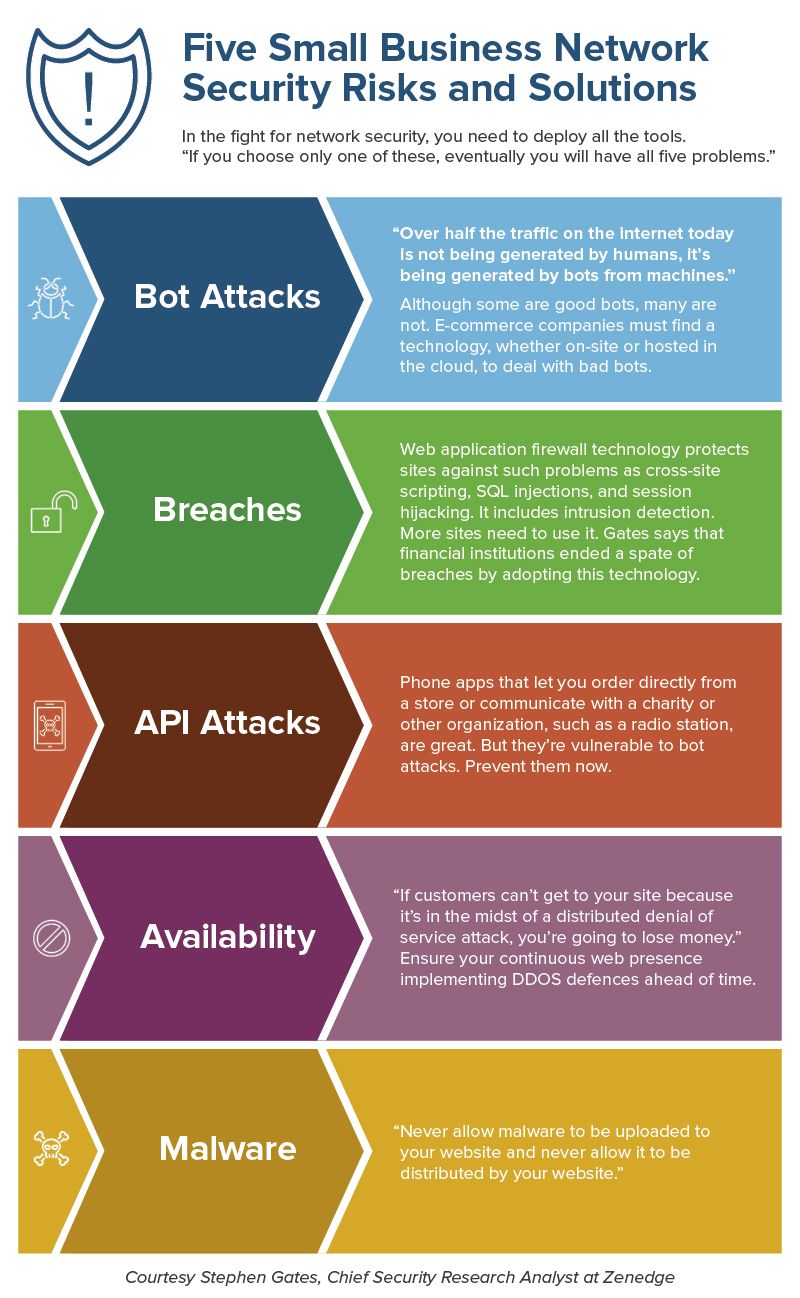
Air Snitch is a sophisticated attack that targets the encryption protocols used in Wi-Fi networks. By exploiting weaknesses in these protocols, hackers are able to intercept and decrypt data transmitted over wireless networks. This not only compromises sensitive information but also allows unauthorized access to network resources.
How Air Snitch Works
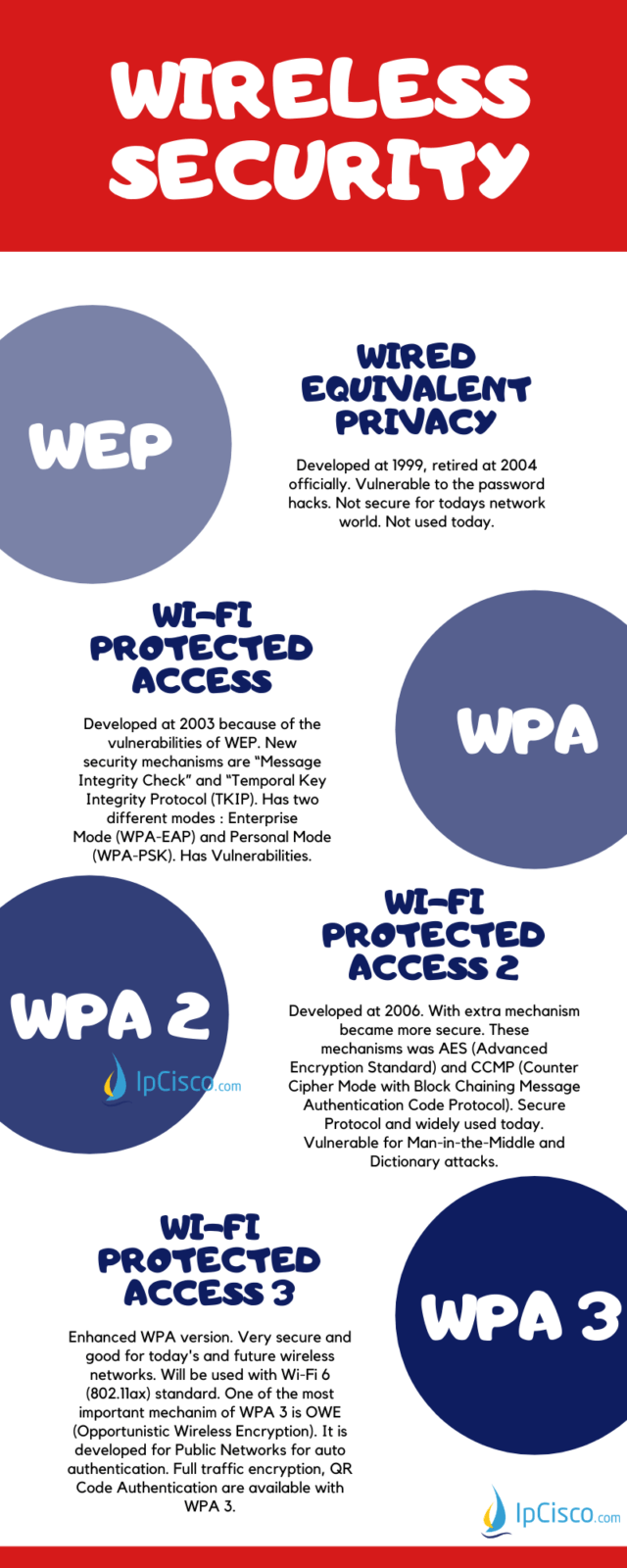
At its core, Air Snitch takes advantage of flaws in the Wi-Fi Protected Access (WPA) protocols. These protocols, designed to secure wireless networks, have been the standard for Wi-Fi encryption for years. However, like any technology, they are not without their vulnerabilities.
Key Steps in the Air Snitch Attack:
- Eavesdropping: Attackers use specially designed software to capture packets of data being transmitted over the network.
- Decryption: By exploiting weaknesses in the encryption algorithm, attackers can decrypt the captured data, gaining access to sensitive information.
- Access and Control: Once inside the network, attackers can manipulate network settings, access connected devices, and intercept data.
Real-World Examples
Consider a corporate office where employees use Wi-Fi to access company resources. An attacker using Air Snitch could potentially intercept emails, access confidential documents, and even manipulate network configurations to further exploit the company's IT infrastructure.

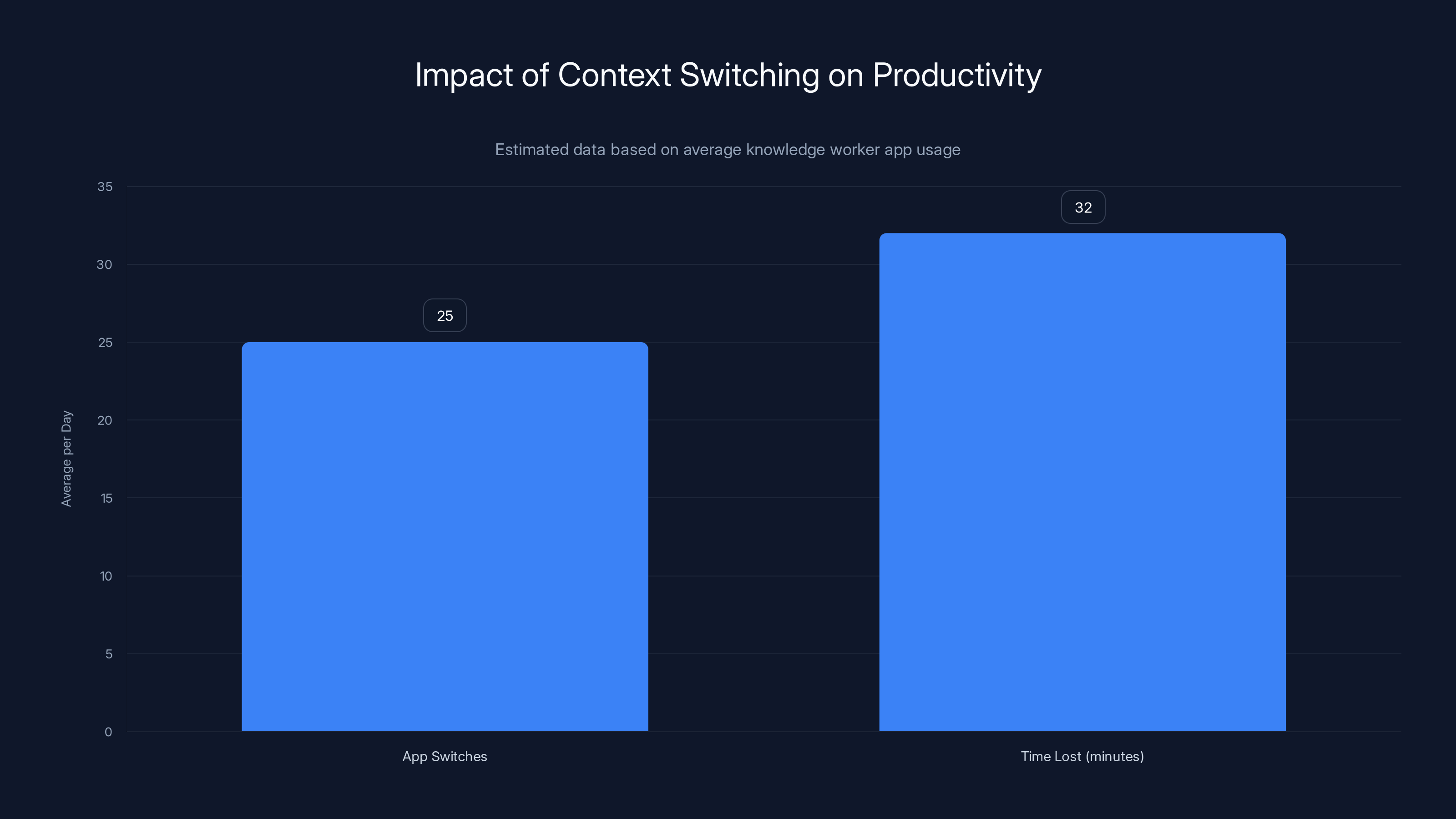
Knowledge workers switch between apps 25 times daily, losing an estimated 32 minutes to context switching. Estimated data.
The Impact of Air Snitch on Different Sectors
Air Snitch poses a significant threat across various sectors, from personal home networks to large enterprises. Let's explore how this attack affects different environments.
Home Networks
In a home setting, Wi-Fi networks are often less secure due to default settings and weak passwords. Air Snitch can easily exploit these weaknesses, allowing attackers to access personal data such as financial information and private communications, as detailed in a comprehensive guide on Wi-Fi network vulnerabilities.
Office Networks
For businesses, the implications are even more serious. Air Snitch can lead to data breaches, financial losses, and reputational damage. Companies with sensitive client data, such as law firms or financial institutions, are particularly vulnerable, as highlighted in a report on data breach prevention.
Enterprise Networks
Larger enterprises have more robust security measures in place, but the complexity of their networks can also present opportunities for attackers. Air Snitch can exploit misconfigured settings and outdated security protocols to gain unauthorized access, as discussed in a study by UCR computer scientists.
Technical Details and Best Practices
Understanding the technical aspects of Air Snitch is crucial for developing effective countermeasures. Here's a deeper dive into the attack mechanics and how you can protect your network.
Encryption Protocols
Wi-Fi networks rely on encryption protocols like WPA2 and WPA3 to secure data. While WPA3 offers improved security, many networks still use WPA2, which is more vulnerable to attacks like Air Snitch, as noted in a recent study on encryption vulnerabilities.
Best Practices for Encryption:
- Upgrade to WPA3: If your devices support it, switch to WPA3 for enhanced security.
- Regular Updates: Keep your router firmware and network devices updated to protect against known vulnerabilities.
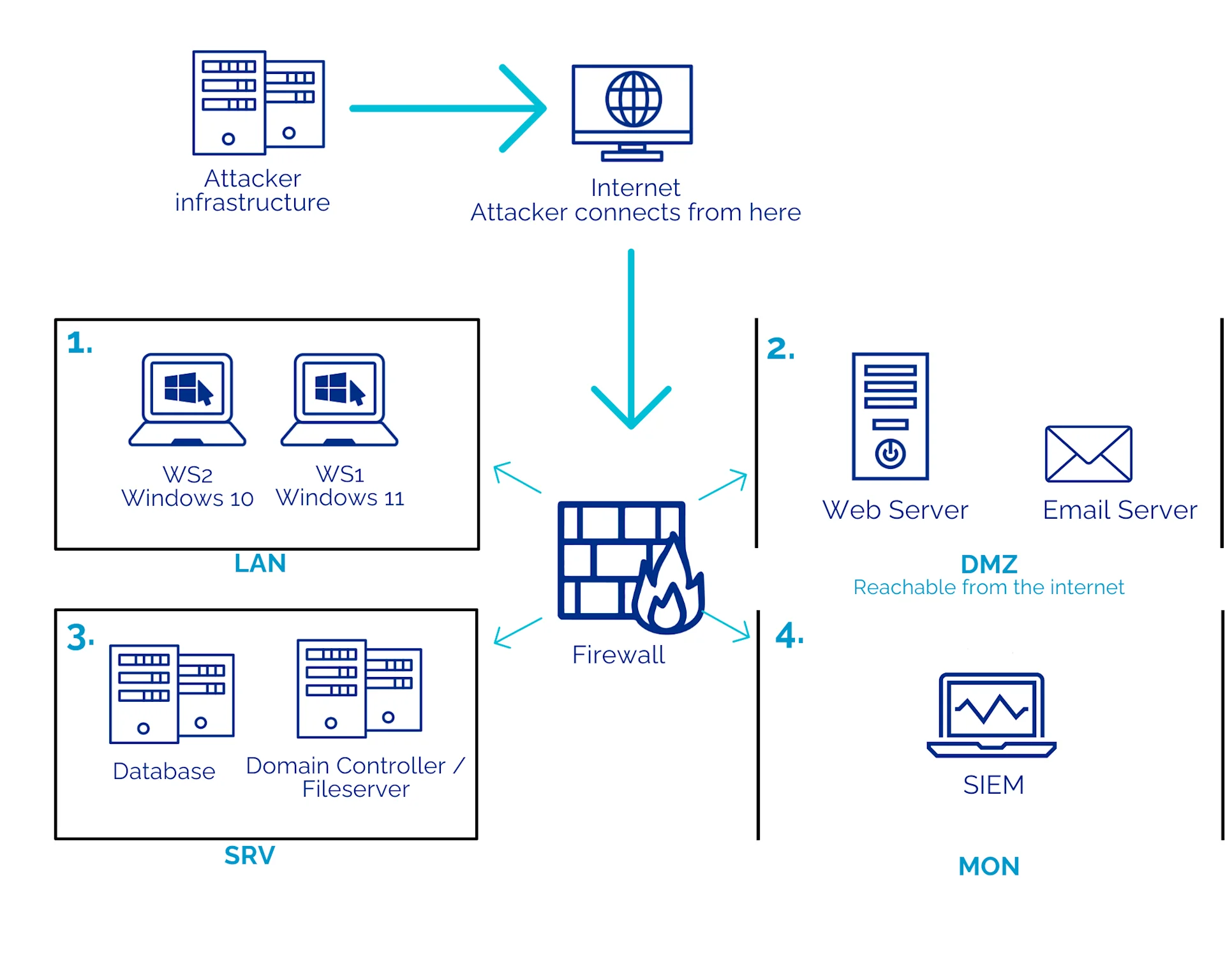
Network Segmentation
Network segmentation involves dividing your network into smaller, isolated segments. This limits the potential damage an attacker can cause by restricting their access to specific parts of the network.
Implementation Guide:
- Identify Critical Assets: Determine which devices and data are most important to protect.
- Create Segments: Use VLANs (Virtual Local Area Networks) to isolate critical assets from the rest of the network.
- Access Control: Implement strict access controls and monitor traffic between segments.
Strong Passwords and Multi-Factor Authentication
Weak passwords are a common entry point for attackers. Implementing strong password policies and multi-factor authentication (MFA) can significantly reduce the risk of unauthorized access, as advised by Anthropic's security guidelines.
Password Best Practices:
- Complexity: Use a combination of letters, numbers, and symbols.
- Length: Aim for at least 12 characters.
- Rotation: Change passwords regularly and avoid reusing them.
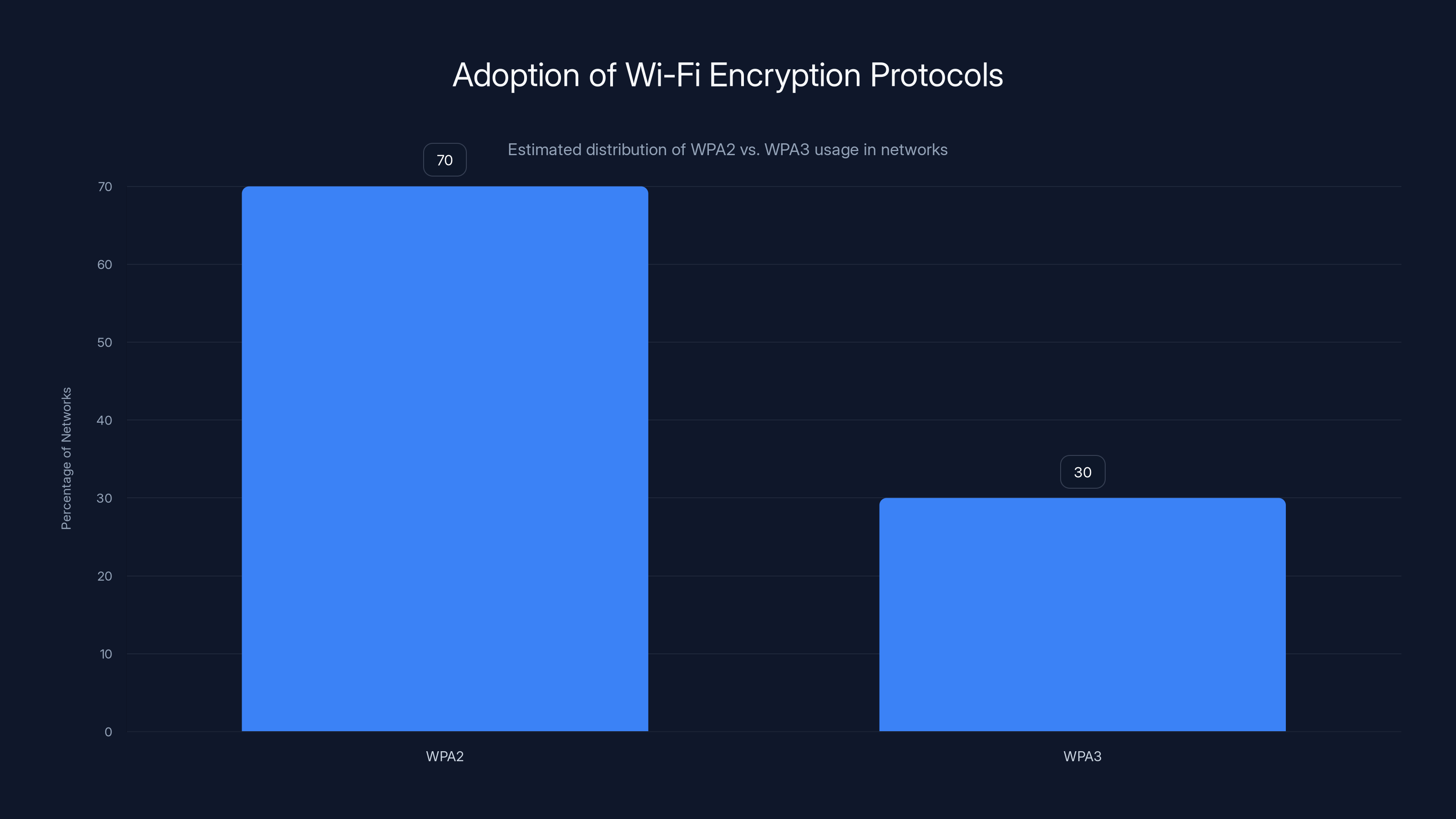
Estimated data shows that 70% of networks still use WPA2, highlighting the need for upgrading to WPA3 for better security.
Common Pitfalls and Solutions
Even with the best intentions, network security can fall short due to common pitfalls. Here are some challenges and how to overcome them.
Overlooking Firmware Updates
Many users neglect to update their router firmware, leaving their networks vulnerable to known exploits. Set up automatic updates or schedule regular manual checks to ensure your network is protected, as recommended in the Cybercrime Report.
Inadequate Monitoring
Without proper monitoring, it's difficult to detect and respond to attacks in real-time. Implement network monitoring tools to track activity and receive alerts for suspicious behavior.
Poor Configuration
Misconfigured networks are an easy target for attackers. Regularly review your network settings and consult with security experts to ensure optimal configuration, as suggested by the Frontier of Knowledge Award-winning encryption algorithm.
Future Trends and Recommendations
As technology evolves, so do the threats to network security. Here are some trends and recommendations for staying ahead of potential attacks like Air Snitch.
Enhanced Security Protocols
The development of new security protocols will be crucial in mitigating future threats. Keep an eye on industry standards and adopt new protocols as they become available, as emphasized in the Wi-Fi chipset market outlook.
AI-Driven Threat Detection
Artificial intelligence is playing an increasingly important role in cybersecurity. AI-driven tools can analyze network traffic patterns and identify anomalies that may indicate an attack, providing an additional layer of security.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities and ensure compliance with industry standards. Consider working with third-party security firms for an unbiased assessment.
Conclusion: Safeguarding Your Wi-Fi Network
The Air Snitch attack highlights the importance of proactive network security measures. By understanding the risks and implementing best practices, you can protect your network from potential threats. Stay informed about the latest developments in Wi-Fi security and be prepared to adapt as new challenges arise.

FAQ
What is the Air Snitch attack?
Air Snitch is a new attack that exploits vulnerabilities in Wi-Fi encryption protocols, allowing attackers to intercept and decrypt data transmitted over wireless networks.
How does Air Snitch affect home networks?
In home networks, Air Snitch can exploit weak passwords and default settings to access personal data such as financial information and private communications.
What measures can businesses take to protect against Air Snitch?
Businesses should implement strong encryption protocols, regularly update firmware, and use network segmentation to limit access to critical assets.
Are all Wi-Fi networks vulnerable to Air Snitch?
While all Wi-Fi networks using outdated encryption protocols are at risk, networks using the latest protocols like WPA3 have enhanced security measures in place.
How can regular users secure their Wi-Fi networks?
Users can secure their networks by using strong passwords, enabling multi-factor authentication, and regularly updating their router firmware.
What role does AI play in detecting Wi-Fi attacks?
AI-driven tools can analyze network traffic patterns and identify anomalies that may indicate an attack, providing an additional layer of security.
Key Takeaways
- AirSnitch exploits vulnerabilities in Wi-Fi encryption, compromising data security.
- Regular updates, strong passwords, and network segmentation are key mitigation strategies.
- Enhanced security protocols and AI-driven threat detection are future trends.
- Proactive security measures are crucial to protect against AirSnitch.
- Businesses should implement strong encryption protocols and regularly update firmware.
- AI-driven tools can analyze network traffic patterns for anomalies.
Related Articles
- Understanding the Implications of Data Leaks: A Deep Dive into the Frivol Incident [2025]
- Mastering Phone Privacy: How NordVPN's Birthday Sale Can Upgrade Your Security to Samsung Galaxy S26 Ultra Levels [2025]
- Navigating the Complex World of Anti-Bot Systems: The OpenClaw Dilemma [2025]
- The Dark Side of AI: How a Hacker Exploited Anthropic's Claude to Breach Mexican Government Agencies [2025]
- Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]
- Navigating 1Password's Upcoming Price Hike: How to Maximize Your Subscription [2025]
![Understanding the AirSnitch Attack: Wi-Fi Encryption Risks and Mitigation [2025]](https://tryrunable.com/blog/understanding-the-airsnitch-attack-wi-fi-encryption-risks-an/image-1-1772122022242.jpg)



