Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]
Enterprise security is facing a paradigm shift. Gone are the days when regular software upgrades and patches were the main line of defense. Now, the focus is shifting towards security independence—creating robust systems that don't solely rely on vendor updates to stay secure.
TL; DR
- Security Independence: Shifts focus from reactive patching to proactive strategies.
- Automation Threats: Attackers use AI to exploit vulnerabilities faster than ever.
- Vendor Lock-In Risks: Over-reliance on vendors can slow response times.
- Proactive Measures: Emphasizes system hardening and independent verification.
- Future Trends: Increased emphasis on zero-trust architectures and decentralized security models.

AI-driven tools and zero-trust architectures are highly effective strategies, with zero-trust showing a significant reduction in breaches. Estimated data.
The Evolution of Enterprise Security
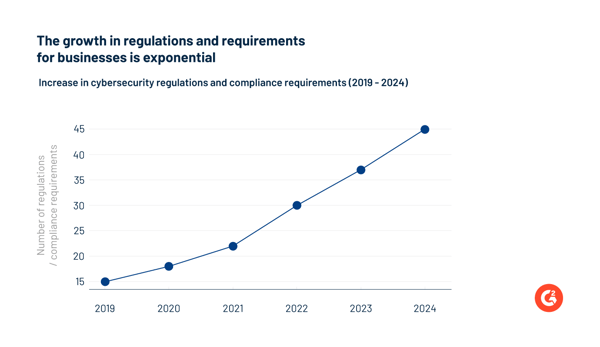
Security strategies have traditionally relied on frequent updates and patches to mitigate risks. This method, however, is reactive and often leaves systems vulnerable between patch cycles. Today, enterprises need a more dynamic approach to security that emphasizes independence from constant vendor updates.
Here's the thing: Relying solely on patching can create a false sense of security. Attackers are now leveraging AI and automated tools to exploit vulnerabilities almost immediately after they're discovered. This rapid exploitation outpaces the traditional update cycle, leaving a gap that attackers can—and do—exploit. According to The Register, native cloud security often falls short in addressing these rapid threats.

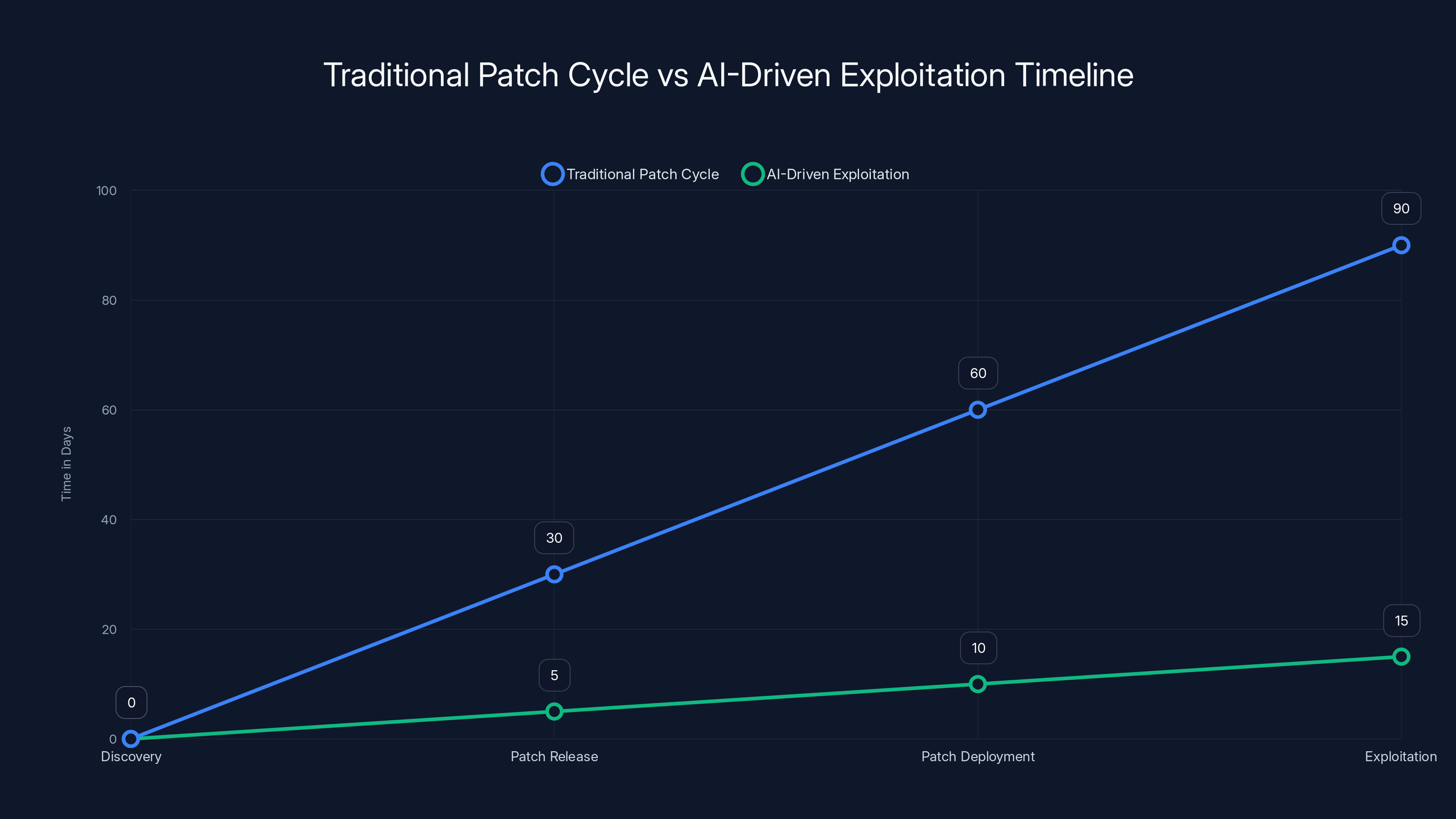
AI-driven exploitation occurs significantly faster than the traditional patch cycle, highlighting the need for more proactive security measures. Estimated data.
The Rise of Automation in Cyber Attacks
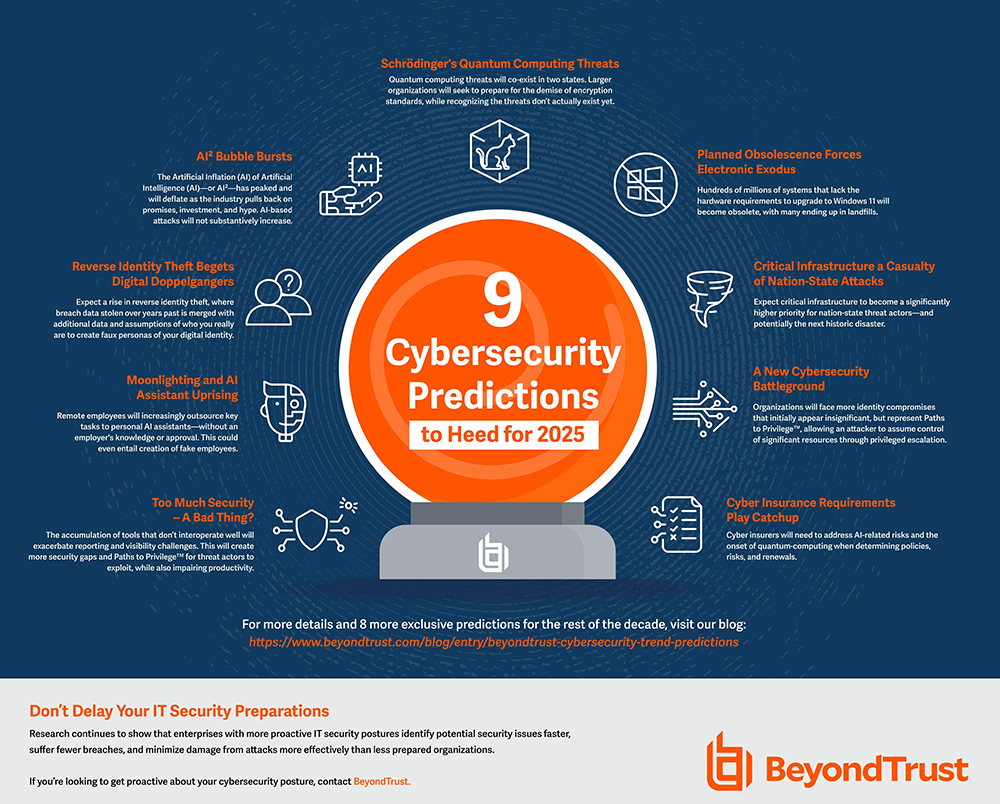
Automation has drastically changed the landscape of cyber threats. Attackers now use sophisticated AI-driven tools to scan for vulnerabilities across vast networks, making the process faster and more efficient than ever before. This shift requires enterprises to rethink their security strategies. The Hacker News highlights how AI is being used to automate these attacks at unprecedented speeds.
Understanding the Threat Landscape
Automation tools employed by attackers can:
- Identify vulnerabilities in real-time across thousands of systems.
- Exploit weaknesses using automated scripts and bots.
- Launch coordinated attacks without human intervention.

Security Independence: A New Paradigm
Security independence involves creating systems that do not solely rely on external updates to remain secure. This approach includes:
- System Hardening: Locking down systems to minimize attack surfaces.
- Independent Verification: Using third-party audits to verify security measures.
- Decentralization: Distributing security controls to prevent single points of failure.
Anthropic emphasizes the importance of independent verification in their security models.
Proactive Security Measures
- Zero-Trust Architecture: Assume that threats are already inside the network and design defenses accordingly.
- Regular Audits: Conduct frequent security audits to identify and mitigate risks.
- Behavior Monitoring: Implement systems that monitor user behavior for anomalies.
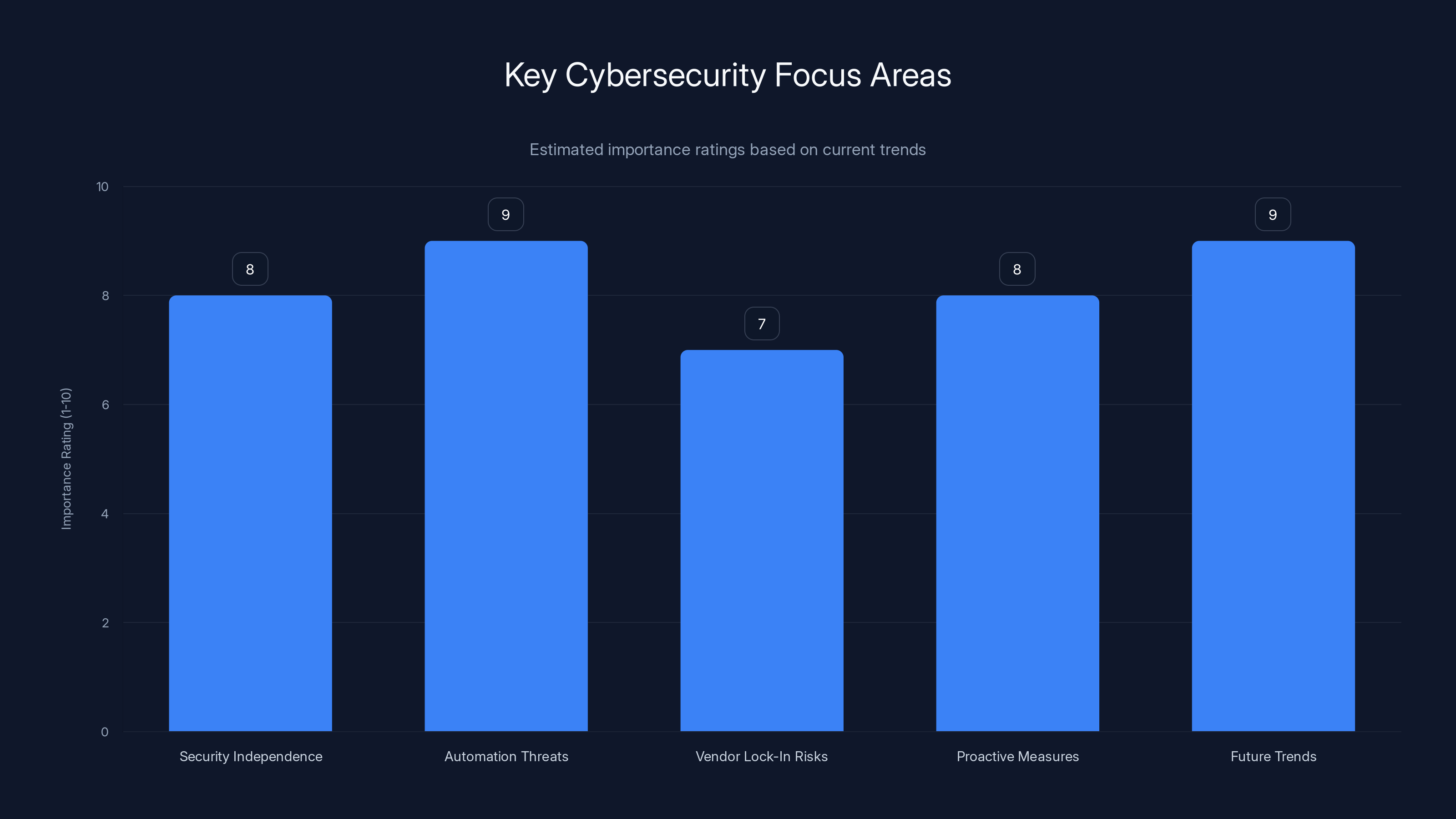
Automation threats and future trends in zero-trust architectures are rated highest in importance, reflecting the need for proactive cybersecurity strategies. Estimated data.
Shifting from Vendor-Dependent Security
Many enterprises are locked into vendor ecosystems, relying on them for patches and updates. This dependency can delay critical security responses and limit flexibility. Digital Journal discusses the risks associated with vendor lock-in and the need for more flexible systems.
Risks of Vendor Lock-In
- Delayed Patch Releases: Vendors may prioritize their own schedule over urgent security needs.
- Limited Customization: Enterprises may be unable to tailor security measures to specific threats.

Building Robust, Independent Security Systems
To build a security strategy that emphasizes independence, enterprises should:
- Invest in AI-Driven Security Tools: Use AI to predict and prevent attacks before they occur. Google Cloud's security measures demonstrate how AI can enhance cloud protection.
- Develop In-House Expertise: Train teams to handle security internally without relying solely on external vendors.
- Implement Redundancy: Ensure multiple layers of security to prevent single points of failure.

Practical Implementation Guides
Steps to Achieve Security Independence
- Assess Current Dependencies: Identify where your security relies on external vendors.
- Develop a Transition Plan: Gradually shift towards in-house management and third-party verification.
- Embrace Open Standards: Use open-source tools and standards to avoid vendor lock-in.
- Foster a Security Culture: Encourage a company-wide focus on security, from the C-suite to individual contributors.
Common Pitfalls and Solutions
Pitfall #1: Over-Reliance on Automation
Solution: Balance automation with human oversight to ensure nuanced, context-aware responses. BitSight emphasizes the importance of balancing automation with manual oversight.
Pitfall #2: Neglecting Regular Audits
Solution: Schedule frequent security audits and act on findings promptly to mitigate risks.
Pitfall #3: Inadequate Training
Solution: Invest in ongoing training to keep your team updated on the latest security practices.
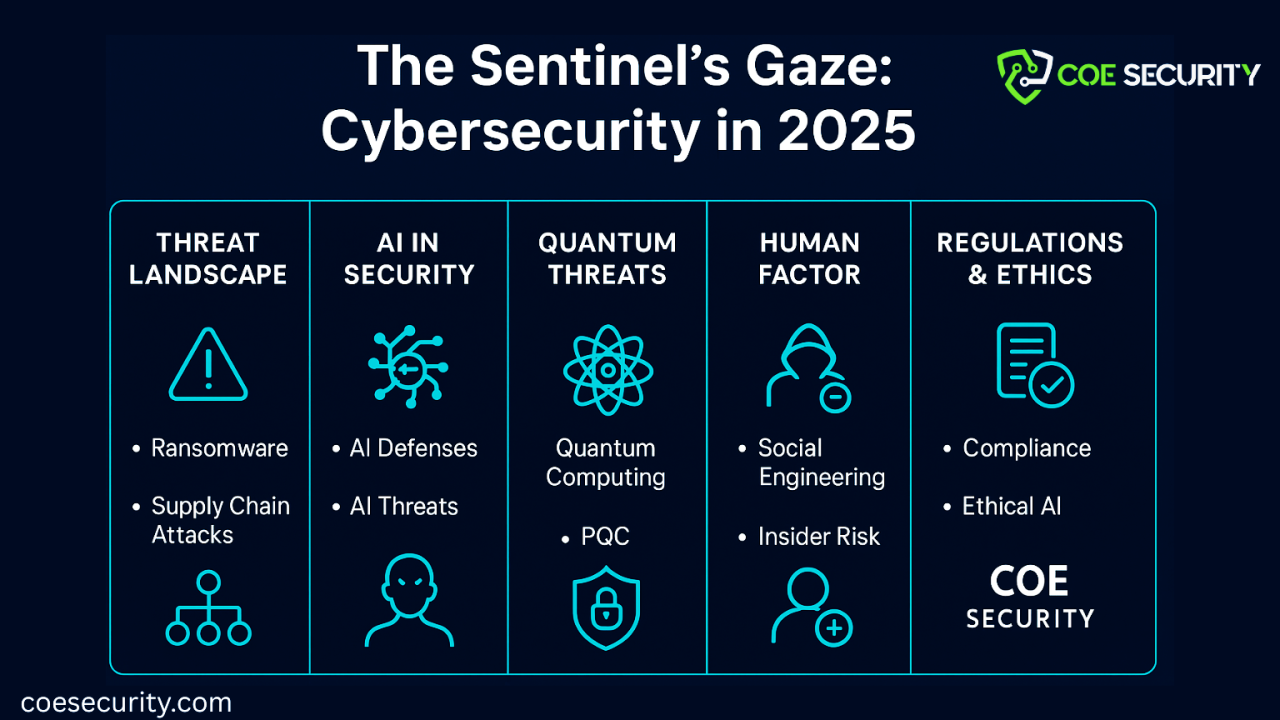
Future Trends in Enterprise Security
The future of enterprise security will likely see increased adoption of:
- Zero-Trust Models: More organizations will implement zero-trust architectures.
- Decentralized Security: Security measures spread across multiple nodes to prevent centralized failures.
- AI Integration: Enhanced AI tools for predictive threat modeling and real-time response. PYMNTS discusses the role of AI in future security strategies.
Recommendations for CIOs
CIOs should focus on the following strategies to ensure robust, independent security:
- Prioritize Training: Ensure all staff are trained in security best practices.
- Adopt Flexible Solutions: Choose security solutions that offer customization and scalability.
- Engage in Continuous Learning: Stay informed about the latest threats and defenses.

Conclusion
Enterprise security is no longer just about keeping up with the latest patches. It's about building a comprehensive strategy that emphasizes independence, agility, and proactive measures. By focusing on these aspects, enterprises can better protect themselves against the fast-evolving cyber threat landscape. Runable offers tools that can help automate security audits to detect vulnerabilities before they become breaches.
Use Case: Automating security audits to detect vulnerabilities before they become breaches.
Try Runable For Free
Key Takeaways
- Security independence reduces reliance on vendor patches.
- AI and automation have accelerated threat exploitation.
- Zero-trust architectures enhance security resilience.
- Decentralized security prevents single points of failure.
- Proactive measures outperform reactive patching.
Related Articles
- US Diplomatic Efforts Against Foreign Data Sovereignty Laws [2025]
- Mastering Video Editing with Adobe Firefly's Quick Cut [2025]
- Jira's AI Agents: Revolutionizing Workflows by Integrating Humans and Machines [2025]
- 1Password Pricing Update: What Users Need to Know [2025]
- OpenAI's Legal Victory: Navigating the Complexities of Trade Secret Lawsuits in AI [2025]
- Navigating 1Password's Upcoming Price Hike: How to Maximize Your Subscription [2025]
FAQ
What is Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]?
Enterprise security is facing a paradigm shift
What does tl; dr mean?
Gone are the days when regular software upgrades and patches were the main line of defense
Why is Why Enterprise Security Now Depends on Independence, Not Upgrades [2025] important in 2025?
Now, the focus is shifting towards security independence—creating robust systems that don't solely rely on vendor updates to stay secure
How can I get started with Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]?
- Security Independence: Shifts focus from reactive patching to proactive strategies
What are the key benefits of Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]?
- Automation Threats: Attackers use AI to exploit vulnerabilities faster than ever
What challenges should I expect?
- Vendor Lock-In Risks: Over-reliance on vendors can slow response times
![Why Enterprise Security Now Depends on Independence, Not Upgrades [2025]](https://tryrunable.com/blog/why-enterprise-security-now-depends-on-independence-not-upgr/image-1-1772033667939.jpg)



